In this post we’ll learn the steps to disable firewall in Windows Server 2012 R2. Security was always an area of concern for Microsoft Operating Systems, therefore Microsoft enhanced the security for all the new Operating Systems by enabling Firewall. It is enabled by default when you install the Windows Server 2012 R2. You would not be able to ping the computer on which firewall is enabled.
We would not recommend to disable the firewall for security reason but if you are using hardware firewall at organizational level and don’t want Software firewall to be enabled then follow the steps given below to disable Windows firewall on 2012 R2, you can follow the same steps for Windows Server 2008, Windows 8, etc.
https://www.itingredients.com//domain-controller-vs-member-server-vs-client/
1. Click start menu and click on the icon of Server Manager.
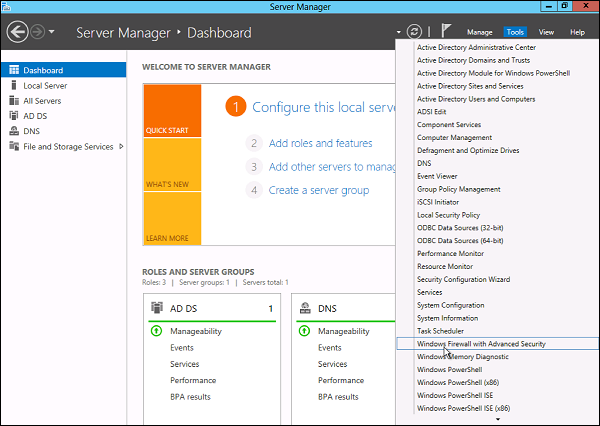
2. It opens the server manager then, click on “tools”.
https://www.itingredients.com//what-is-fsmo-roles-flexible-single-master-operations/
3. Select the option “Windows Firewall with Advanced Security” from the given options.
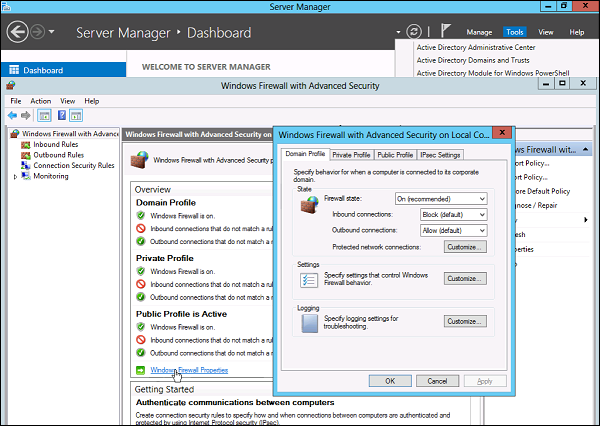
4. In Advanced Security window we can see Domain Profile, Private Profile and Public Profile, we have to disable all three of them. Click on “Windows Profile Properties”.
a) Domain Profile: It is used for the domain environment.
b) Private Profile: It is used for the network at home or at work where you know and trust the people.
c) Public Profile: It is primarily for the networks at public places e.g. airports, coffee shops, etc.
5. To disable the domain profile, drop down the firewall state and select “off”.
6. To disable the private profile, click drop-down and select “off”.
7. To disable the public profile, click drop-down and select “off”.
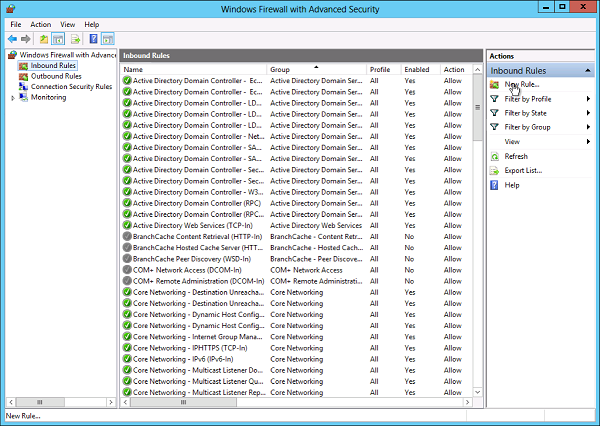
8. Here you can verify that all profiles are disabled. However, if you don’t want to disable all the profiles then you can even create inbound and outbound firewall rules. We’ll talk about those options in upcoming articles. We can even use Group Policy to apply firewall settings.
9. As we are done with the steps, now you can open a command prompt and try to ping the server and check if communication is working or not.
Hope you understood all the steps that we have listed on this article to disable Windows Server Firewall on 2012 R2. Feel free to leave your suggestions and comments in the below mentioned comment section. Besides that please confirm if you are using Hardware Firewall or Software Firewall in your Organization.
Брандмауэр Windows в режиме повышенной безопасности – это брандмауэр, который работает на Windows Server 2012 и включен по умолчанию. Настройки брандмауэра в Windows Server 2012 управляются из консоли управления Microsoft брандмауэра Windows . Чтобы настроить параметры брандмауэра, выполните следующие действия:
Шаг 1. Нажмите «Диспетчер серверов» на панели задач → Откройте меню «Инструменты» и выберите «Брандмауэр Windows в режиме повышенной безопасности».
Шаг 2. Чтобы просмотреть текущие параметры конфигурации, выберите « Свойства брандмауэра Windows» в консоли MMC. Это позволяет получить доступ к изменению настроек для каждого из трех профилей брандмауэра, а именно: настройки домена, частного и общего доступа, а также настроек IPsec.
Шаг 3 – Применение пользовательских правил, который будет включать следующие два шага –
-
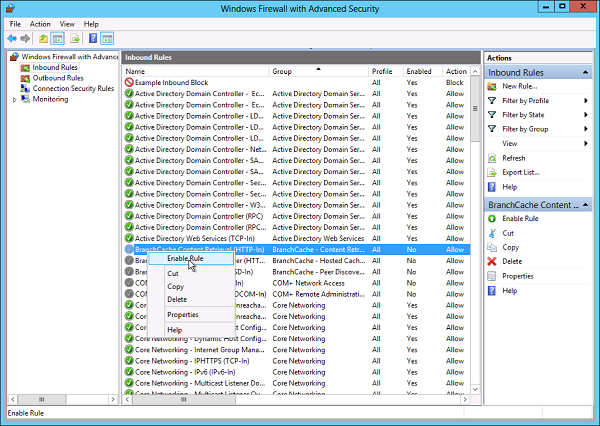
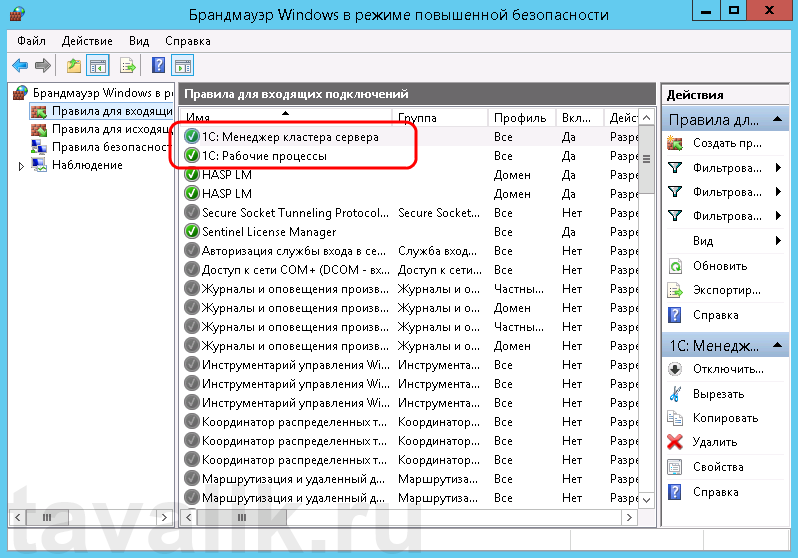
Выберите « Входящие правила» или « Исходящие правила» в разделе « Брандмауэр Windows в режиме повышенной безопасности» в левой части консоли управления. (Как вы знаете, исходящий трафик – это трафик, генерируемый сервером в Интернет, а входящий трафик – наоборот). Правила, которые в настоящее время включены, обозначены зеленым значком флажка, в то время как отключенные правила отображают серый значок флажка.
-
Правое нажатие на правило позволит вам включить / отключить.
Выберите « Входящие правила» или « Исходящие правила» в разделе « Брандмауэр Windows в режиме повышенной безопасности» в левой части консоли управления. (Как вы знаете, исходящий трафик – это трафик, генерируемый сервером в Интернет, а входящий трафик – наоборот). Правила, которые в настоящее время включены, обозначены зеленым значком флажка, в то время как отключенные правила отображают серый значок флажка.
Правое нажатие на правило позволит вам включить / отключить.
Как создать новое правило брандмауэра?
Чтобы создать новое правило брандмауэра, вы должны придерживаться следующих шагов –
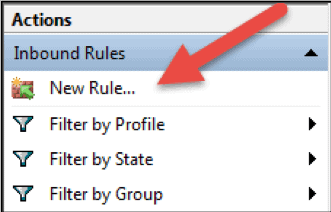
Шаг 1 – С правой стороны либо Правил входящих, либо Правил исходящих – нажмите «Новое правило».
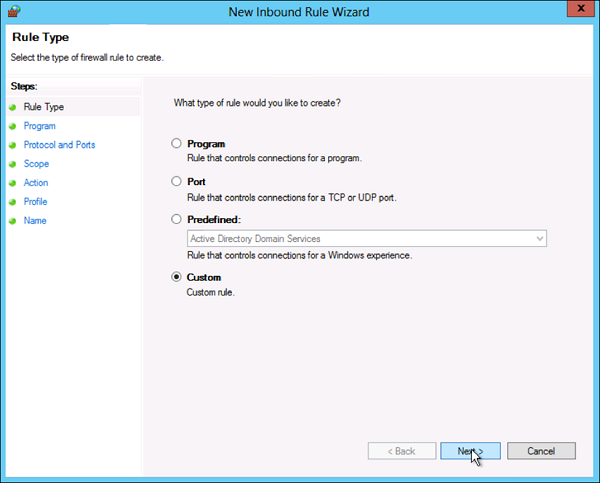
Шаг 2 – Пользовательский из радиальной кнопки Тип правила → нажмите Далее .
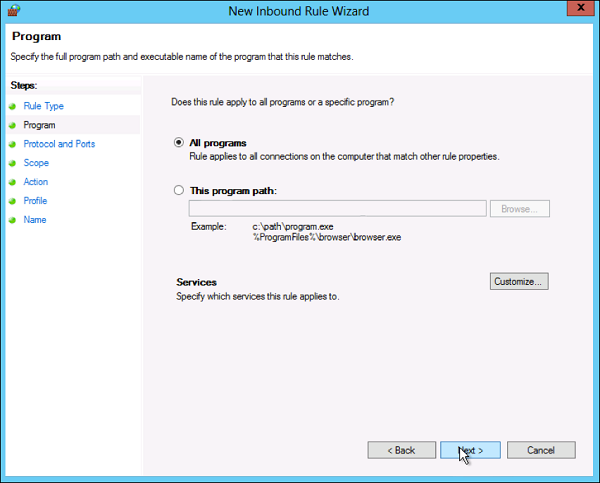
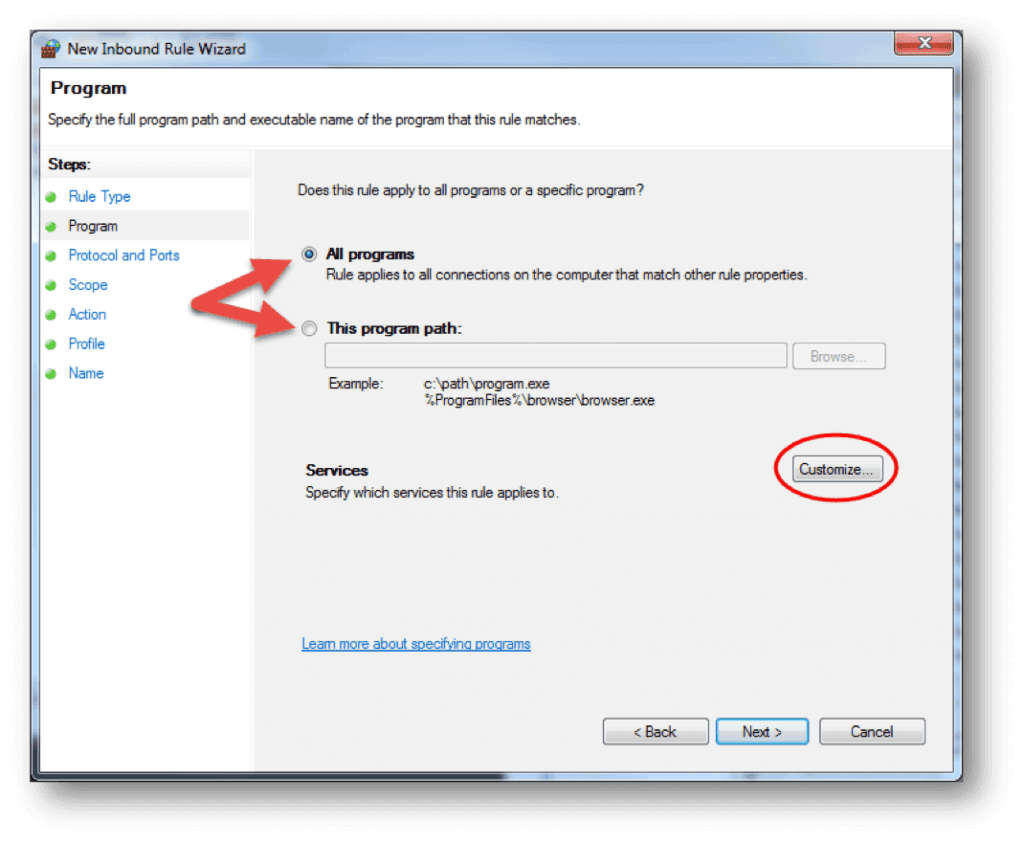
Шаг 3. Выберите ассоциацию программы для правила настраиваемого брандмауэра в качестве Все программы или путь к программе → нажмите Далее.
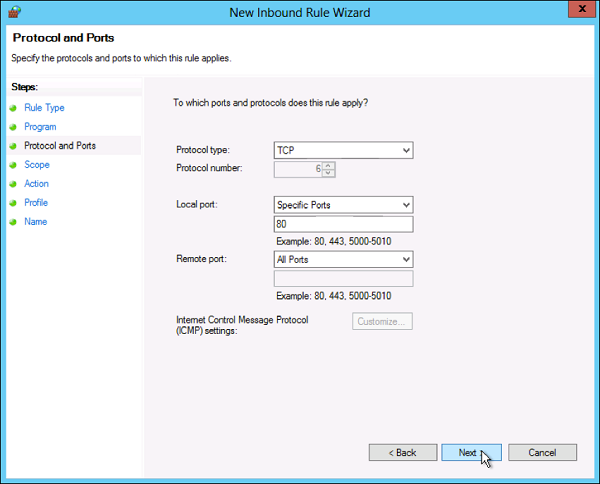
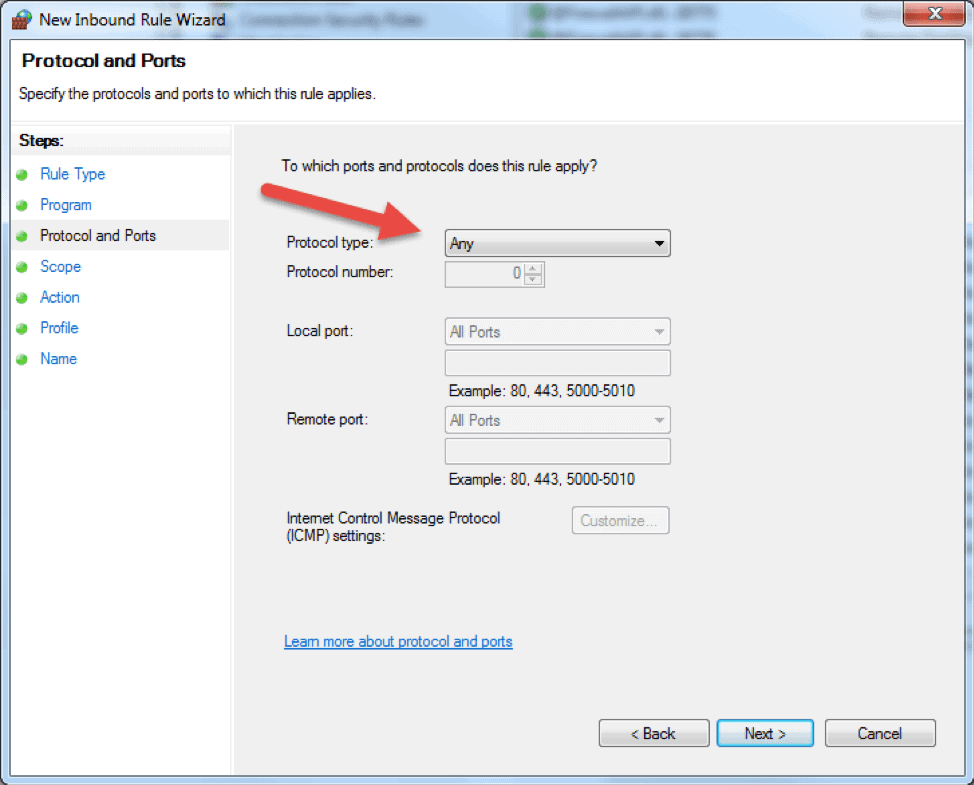
Шаг 4 – Поле типа протокола выберите тип протокола → нажмите Далее .
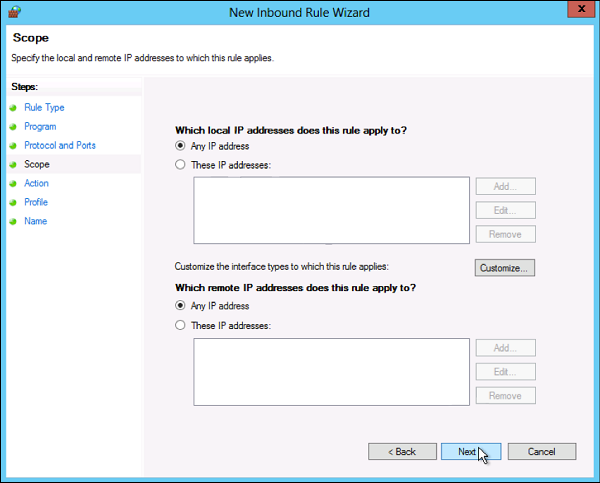
Шаг 5 – Выберите сопоставление IP-адресов для локальных и удаленных адресов → нажмите Далее .
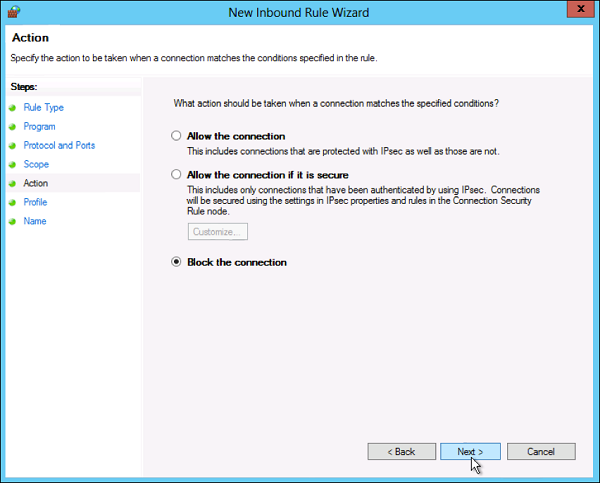
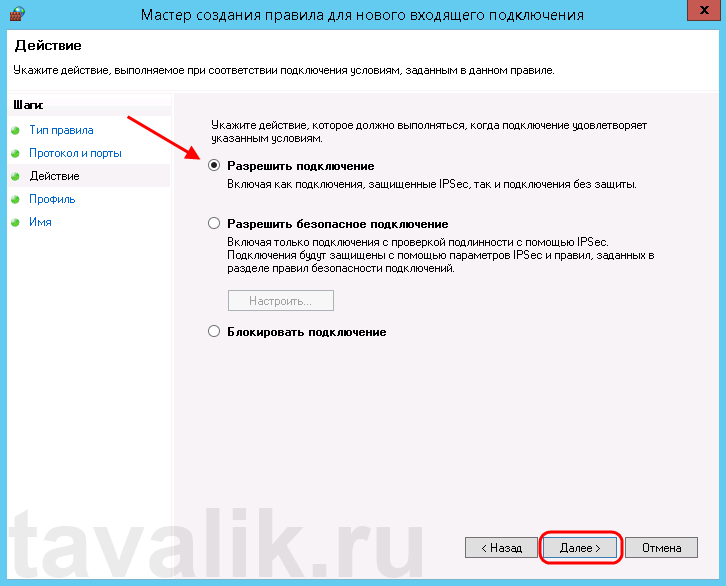
Шаг 6 – Выберите действие, которое нужно выполнить для соответствующего трафика → нажмите Далее.
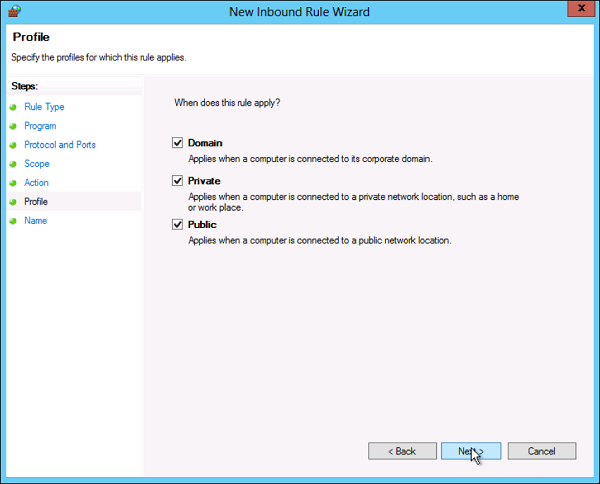
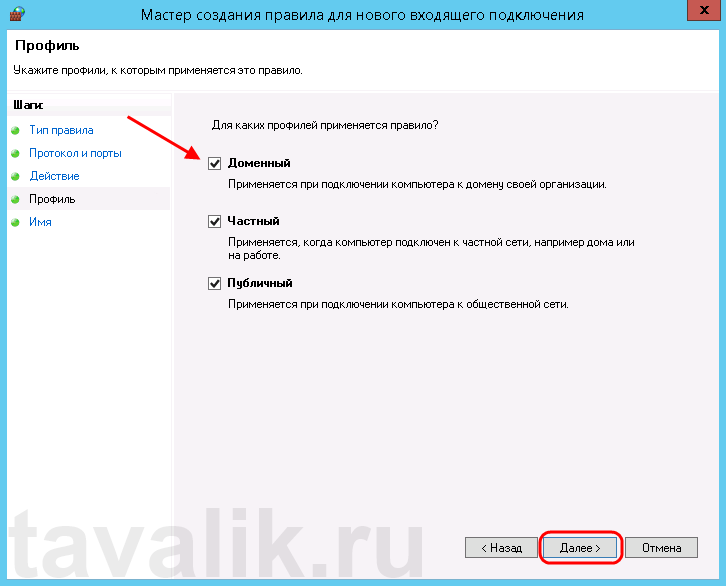
Шаг 7 – Выберите профили, связанные с пользовательским правилом → нажмите Далее .
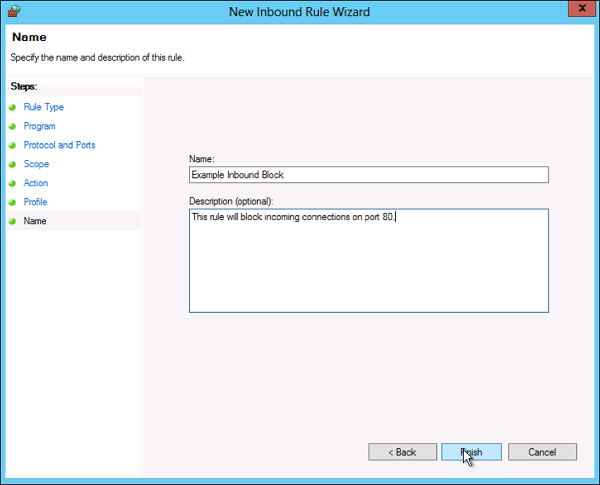
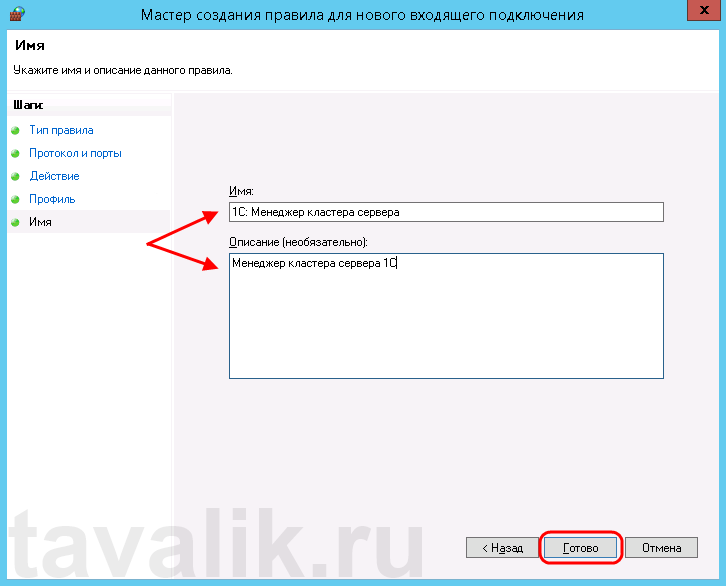
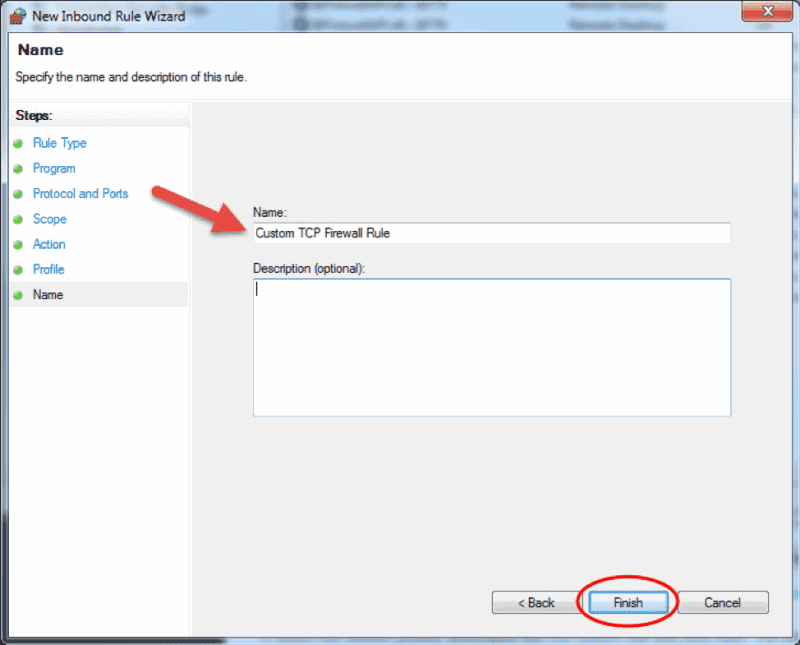
Шаг 8. Введите имя для правила брандмауэра и необязательное описание → Готово .
Шаг 9 – Правило брандмауэра можно найти на соответствующей вкладке «Правило», входящее или исходящее в зависимости от созданного типа. Чтобы отключить или удалить правило, найдите правило в MMC, щелкните его правой кнопкой мыши и выберите « Отключить правило» или « Удалить» .

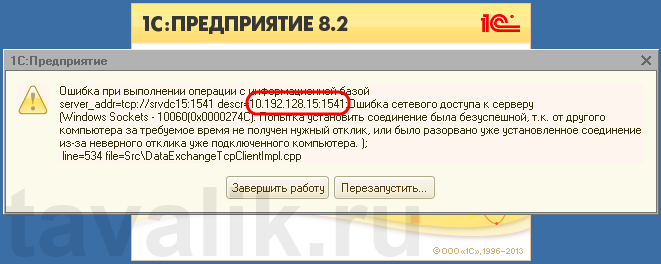
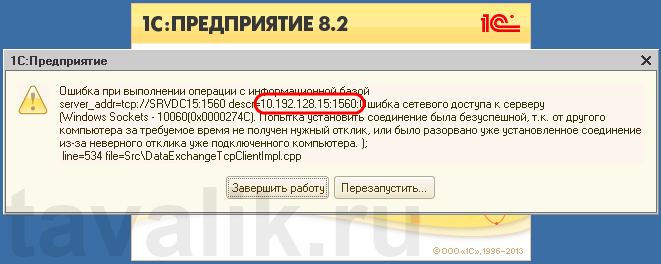
Некоторые программы и службы при работе через сетевые протоколы используют определенные порты для обмена данными. По умолчанию включенный брандмауэр Windows блокирует подобную сетевую активность. В частности, если попытаться подключиться с клиентской машины к серверу 1С:Предприятие 8.х можно натолкнуться на ошибку:
«Ошибка при выполнении операции с информационной базой (…). Ошибка сетевого доступа к серверу (…). Попытка установить соединение была безуспешной, т. к. от другого компьютера за требуемое время не получен нужный отклик, или было разорвано уже установленное соединение из-за неверного отклика уже подключенного компьютера (…) »
Данная ошибка означает, что по указанному адресу не найден сервер «1С:Предприятия», ну или на сервере закрыт порт (в данном случае порт 1541).
Для открытия порта, заходим на компьютер, где установлен сервер «1С:Предприятия» (в моем примере это компьютер с адресом 10.192.128.15 и установленной на нем операционной системой Windows Server 2012 R2).
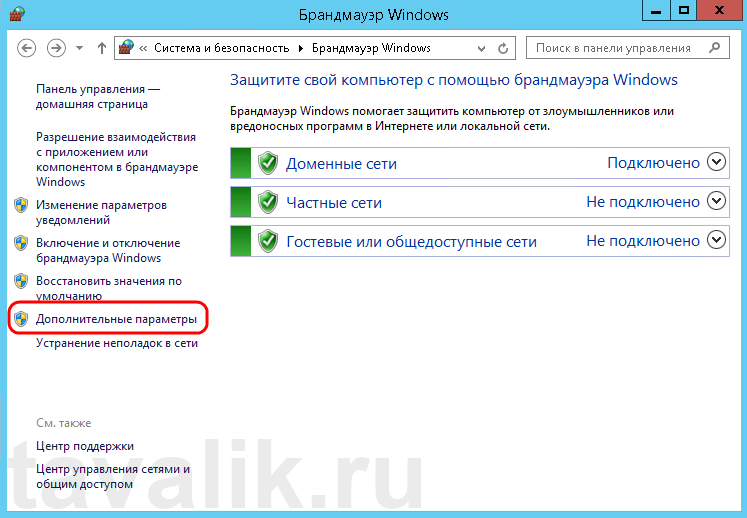
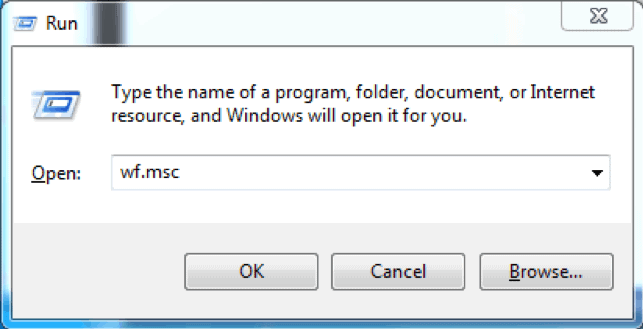
Запускаем брандмауэр Windows. Сделать это можно кликнув правой кнопкой мыши по «Пуск» (Start), затем «Панель управления» (Control Panel) — «Система и безопасность» (System and Security) — «Брандмауэр Windows» (Windows Firewall). Или же выполнив команду firewall.cpl (для этого необходимо нажать комбинацию клавиш Win + R, в окне «Отрыть» (Open) ввести имя команды и нажать «ОК» ) .
Далее нажимаем на «Дополнительные параметры» (Advanced Settings) в меню слева.
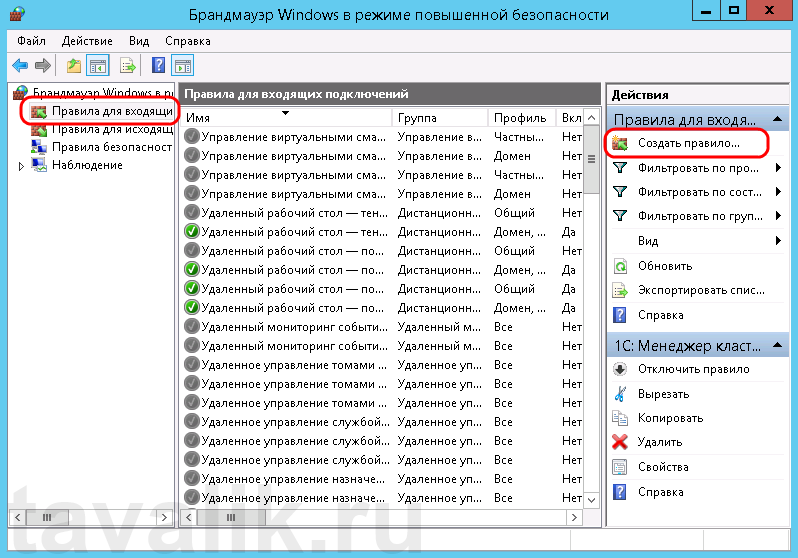
В открывшемся окне, в дереве слева откроем вкладку «Правила для входящих подключений» (Inbound Rules), а затем в меню «Действия» (Actions) выберем пункт «Создать правило…» (New Rule…).
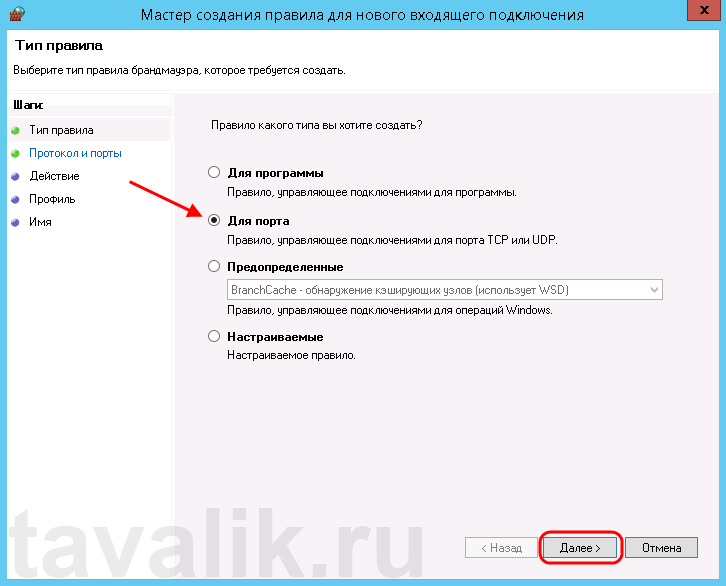
Запустится «Мастер создания правила для нового входящего подключения» (New Inbound Rule Wizard). На первой странице выберем тип правила (Rule Type) «Для порта» (Port) и нажмем «Далее» (Next).
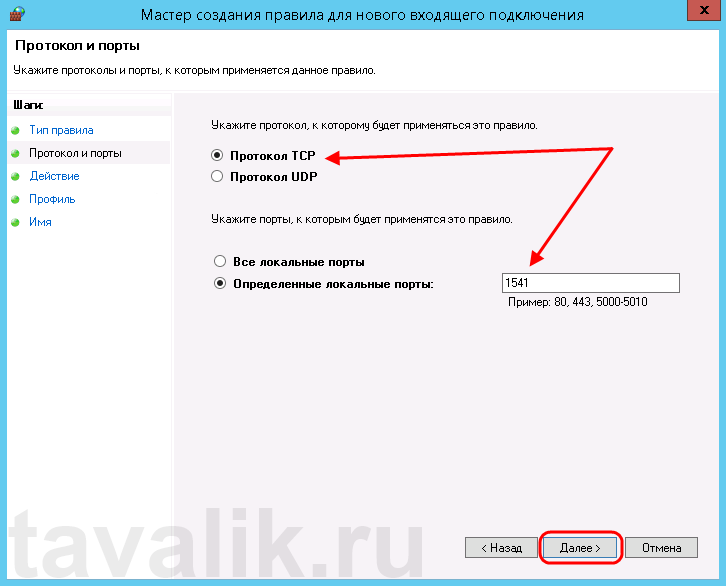
Затем необходимо указать протокол (в нашем примере это TCP) и, непосредственно, номер порта (Specific local ports), который открываем. После чего жмем «Далее» (Next).
Теперь укажем действие связанное с добавляемым правилом. Выберем «Разрешить подключение» (Allow the connection) и нажмем «Далее» (Next).
На следующей странице нужно указать, для каких профилей брандмауэра будет действовать правило. Отмечаем нужные профили галочками и жмем «Далее» (Next).
Ну и наконец, вводим имя и описание для нового правила и нажимаем «Готово» (Finish) для завершения работы мастера.
Пробуем снова подключиться к серверу «1С:Предприятия» и видим что ошибка сохранилось, но в сообщении уже другой, 1560-ый порт.
Вышеописанным способом добавим еще одно разрешающее правило, с названием «1С: Рабочие процессы» для всего диапазона портов с 1560 по 1591 (для рабочих процессов 1С), указав их через дефис на шаге «Протокол и порты» (Protocol and Ports).
Теперь, в оснастке «Брандмауэр Windows в режиме повышенной безопасности» (Windows Firewall with Advanced Security) в таблице «Правила для входящих подключений» (Inbound Rules) мы должны увидеть 2 только что созданных правила.
Ну а клиент «1С:Предприятия» должен без ошибок подключиться к серверу. Если же потребуется подключаться к этом серверу через консоль администрирования серверов «1С:Предприятия», то необходимо также открыть порт 1540.
Аналогичным образом добавляются правила для для исходящих подключений (Outbound Rules), запрещающие правила, правила для определенных программ и протоколов. Также любое правило можно изменить, открыв его свойства из данной оснастки.
Introduction
Firewalls have become an essential part of every network that has access to the Internet. Without firewalls, anyone would be able to access your network and servers and infect them with malicious software. Properly configured, a firewall can substantially decrease undesirable network communications in a local network.
The article will explain how to create a firewall rule using firewall MMC and Windows PowerShell. We are using Windows Server 2012, but the procedure applies to other versions of Windows, with slight variations.
What is a Firewall?
A firewall is a piece of hardware or software that controls the flow of data packets, and it is critical on modern computer systems. It protects private networks and devices from malicious actions coming from public networks in the same way a physical firewall prevents fire from spreading from one area to another. A firewall acts as a defense mechanism which controls network traffic according to the implemented firewall rules.
Computers behind a firewall cannot receive data until the data passes all filters. This enhances security by a large margin and reduces the risk of unauthorized access to private networks. A proper firewall configuration provides your system with a crucial layer of security and lowers the risk of successful hacking attacks. Firewalls can perform many tasks:
- Protect the data on your computer by creating a barrier that blocks any undesired incoming or outgoing traffic.
- Notify you if there are any connection requests from other computers.
- Log activity for later inspection and warn you if any application tries to connect to another computer.
How Windows Server Firewalls Work
As the name suggests, a firewall acts like a barrier between your local devices and the external network. When you send a connection request to your computer or server over the internet, a hacker can interrupt that connection and try to gain access to your private network. With a firewall in place, only the network traffic that matches firewall rules can get through.
The sets of firewall rules you define in the firewall settings review every packet for flagged information. To make the most out of your firewall, you should precisely define both inbound and outbound rules in order to avoid any unwanted connections.
For example, you can set an inbound rule defining that the data communicated through a specific port, such as TCP port 80, can pass the firewall. That means if the firewall sees a packet coming towards any other port, it will drop it and the data will not reach its intended destination.
Windows Firewall Server 2012 with Advanced Security
Windows Firewall with Advanced Security is the management console which stores all Windows Firewall configurations. Windows Firewall is a host-based firewall solution embedded with virtually all current Windows operating systems.
Windows Firewall with Advanced Security provides safer inbound and outbound network communications by enforcing rules that control traffic flow for its local machine. There are three available firewall profiles:
- Domain. It is used when a computer connects to the corporate network. It is a network where the device can detect its domain controller.
- Private. We use this profile for computers that connect to a private network, such as home or office. In private networks, the users are always behind a device and not directly exposed to the Internet.
- Public. This profile is used when a computer connects to a public network, such as libraries, airports and other public hotspots. The firewall configurations should be the most restrictive for this profile since these networks are the least secure.
The benefits of using Windows Server Firewall with Advanced Security are numerous:
- It is ready out-of-the-box. It comes preinstalled with personal Microsoft Windows operating systems as well as Server editions. It is also active by default, protecting your operating system from the very first startup.
- It does not need a special license or additional hardware. Once you obtain your copy of a Windows operating system, there are no additional costs.
- It is highly flexible. It offers many advanced functionalities and different levels of controls for the firewall services.
What is the Difference between Windows Firewall and Windows Firewall with Advanced Security?
The difference between the two is the level of functionality available to the end-user, that is, the interface itself. Both of them are the same firewall service. The Windows Firewall is easier to use and more consumer-friendly. It is located in the Control Panel and allows you to perform basic firewall configurations.
The Windows Firewall with Advanced Security offers granular control over the inbound and outbound rules, as well as the default firewall profiles. You can modify all advanced firewall configurations using the Microsoft Management Console (MMC) or Windows PowerShell.
How to Launch Windows Firewall with Advanced Security Console?
You can access the Windows Firewall with Advanced Security console in a few different ways. Whichever method you choose, it will open Windows Firewall MMC where you can make further firewall configurations for all profiles.
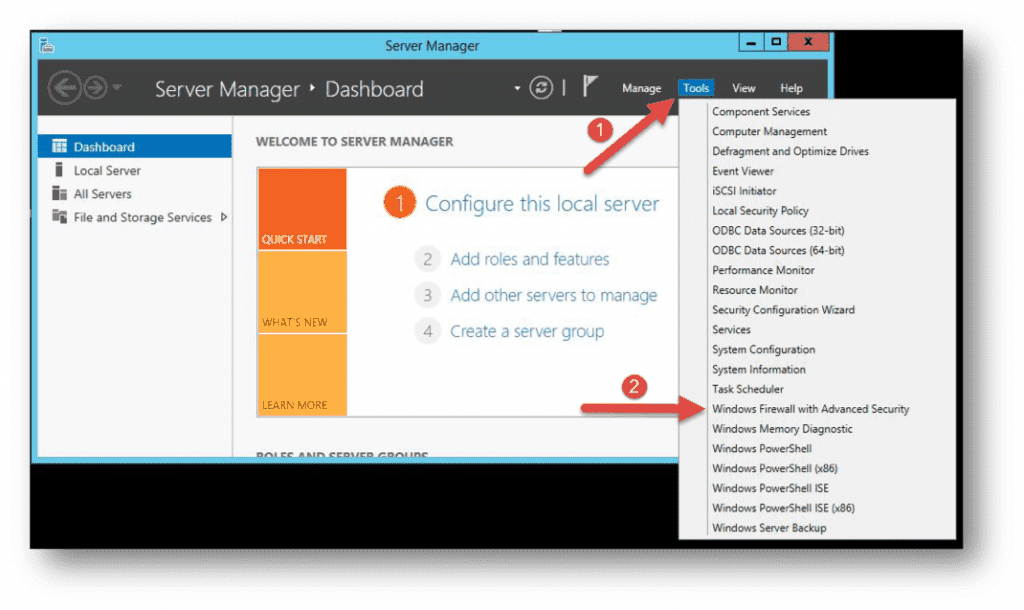
- Use the Server Manager to access the firewall MMC. Once the window opens, go to Tools on the top right side, and locate the Windows Firewall with Advanced Security option toward the bottom of the list.
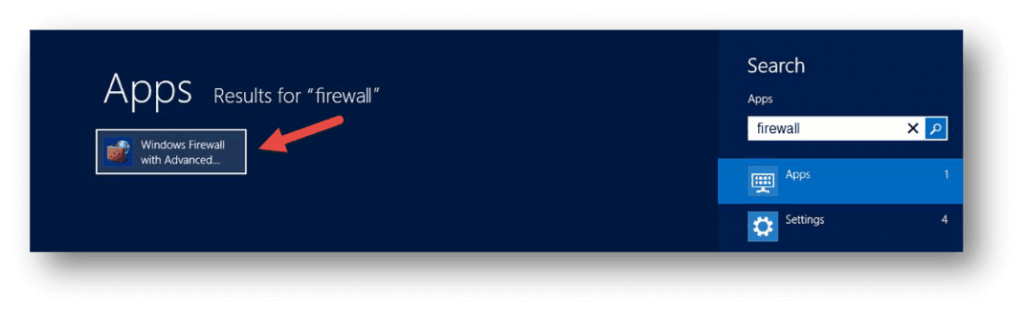
- Open the Start menu (use the Windows key on your keyboard) and type “firewall”. You should see the Windows Firewall with Advanced Security icon appear as one of the search results.
- Use the Run box to launch Windows Firewall with Advanced Security. Press Win + R keys, type in msc and hit Enter to load the console. You can also use Command Prompt or Windows PowerShell to run this command.
Now that you have the Windows Firewall with Advanced Security console open, in the middle you can see the summary of the three firewall profiles. Their default configuration is to permit the outgoing traffic and to limit incoming traffic.
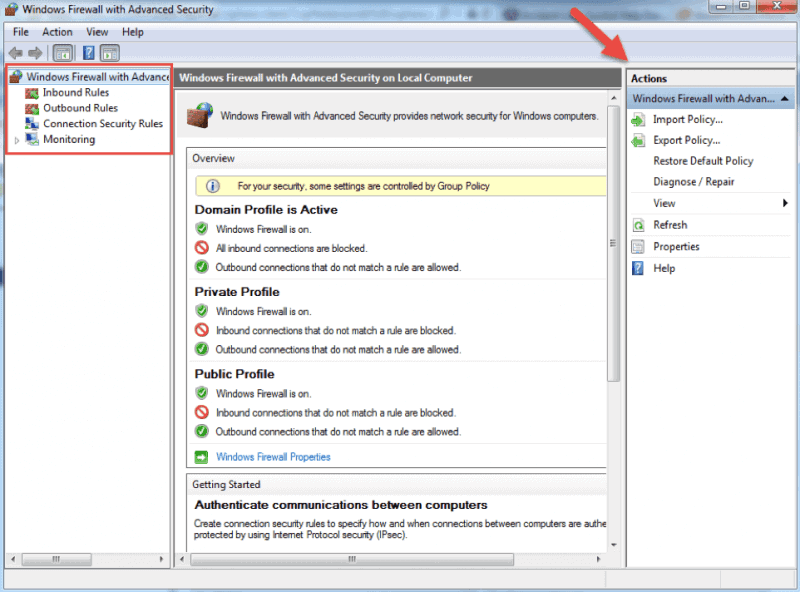
When you select an option from the menu on the left side of the window, you will see its details in the middle section. On the right side, the menu will show the available actions for the option you previously selected.
The Windows Firewall with Advanced Security console allows you to configure inbound and outbound rules, as well as the Internet Protocol security (IPSec) connections. The Monitoring tab allows you to view the active firewall rules and connection security rules for that server.
Firewall Rules
Windows firewall rules allow you to state whether to permit or block specific incoming or outgoing network connections. You can choose between multiple parameters and settings for each individual inbound or outbound rule. This includes selecting a program, a TCP or UDP port, protocol, service, or profile that a rule will apply to.
The procedure is the same when creating inbound rules and outbound rules with Windows Firewall with Advanced Security. I will list the steps for creating an inbound rule and you can follow them in the same order when you want to create an outbound rule.
How to Create Inbound Rules
Launch the Windows Firewall with Advanced Security MMC using the method you prefer. You may want to pin the shortcut to the start menu if you use the console on a regular basis.
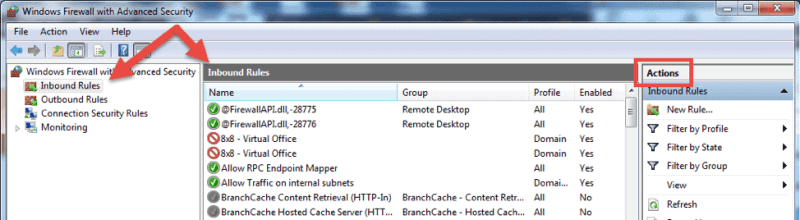
- On the home screen, select the Inbound Rules The console will show all inbound rules in the middle section and available actions in the right pane. You can filter the list by using the available choices.
- Click on New Rule… to start the New Inbound Rule Wizard.The wizard will let you choose the type of rule you want to create. You can choose one out of four types.
- This rule allows or blocks connections for a user-defined program. It allows you to select a path to an executable (*.exe) file. It does not require to insert any program-specific settings.
- A rule based on port settings allows you to permit or block a connection depending on the TCP or UDP port number it uses. You can state multiple ports to apply to this firewall rule.
- This rule contains a list of the most common Windows programs and services. You can select one to allow or block connections for it.
- Custom. This is the most flexible rule in the Wizard. It allows you to create a tailor-made rule with configurations that previous options do not provide. I will proceed with listing the steps for this rule since it covers the most settings.
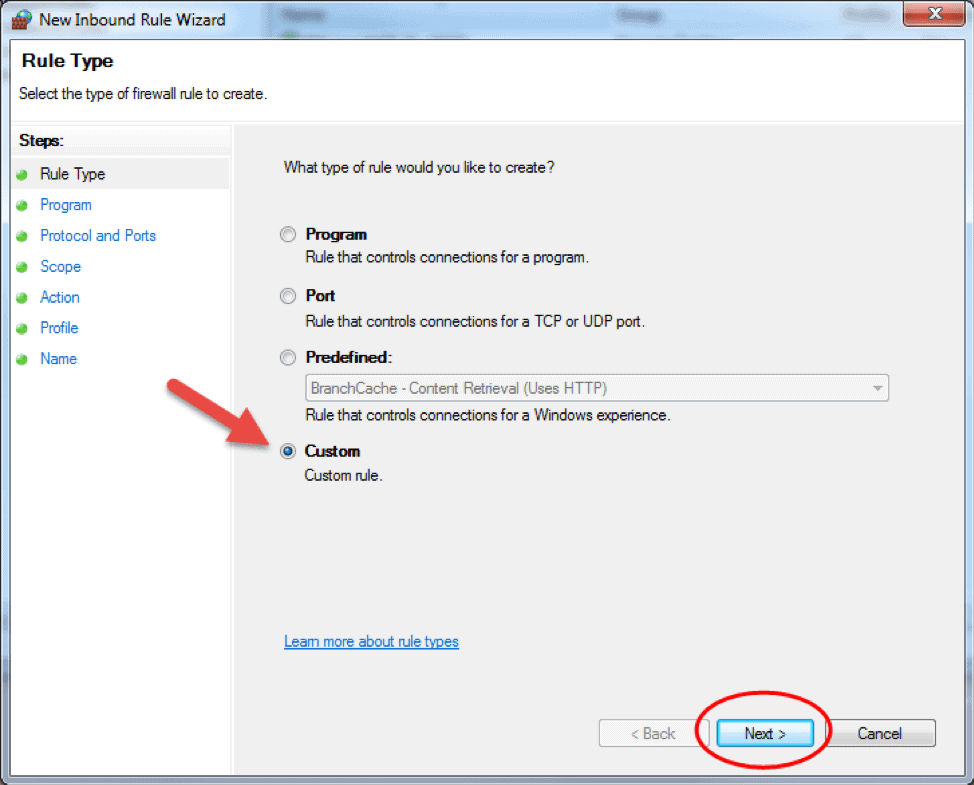
- Click on Custom and click Next to proceed.
- Choose if the rule will apply to connections for All programs or a specific program on the local machine and click Next. You can click Customize… to select additional settings for the processes of the program you selected.
- The following step will allow you to specify the protocol and port for the traffic that this firewall rule will filter. Click Next after you select a protocol type and configure the settings.
- Protocol type. Click on the bar and select the protocol from the dropdown list. You can always select Custom to manually configure the port number. If you select TCP or UDP, you will need to specify local and remote port.
- Protocol number. This field populates automatically after you select a protocol type, and you cannot change it. In order to insert your own port, select Custom in the ‘Protocol type’ dropdown menu.
- Local port. This represents the port on the local machine where you are creating this rule. This section becomes editable if you select TCP or UDP in the ‘Protocol type’ dropdown. Select one of the options from the dropdown box. Note that RPC Endpoint Mapper and RPC Dynamic Ports are available only for TCP inbound rules, and IPHTTPS is available for TCP only. Edge Traversal is available for UDP inbound rules.
- Remote port. This is the port on a remote machine that is trying to establish a connection with the local machine. This section becomes editable if you select TCP or UDP in the ‘Protocol type’ dropdown. Select one of the options from the dropdown box. Note that RPC Endpoint Mapper and RPC Dynamic Ports are available only for TCP inbound rules, and IPHTTPS is available for TCP only. Edge Traversal is available for UDP inbound rules.
- Internet Control Message Protocol (ICMP) settings. You can customize the ICMP settings if you select ICMPv4 or ICMPv6 in the ‘Protocol type’ dropdown list.
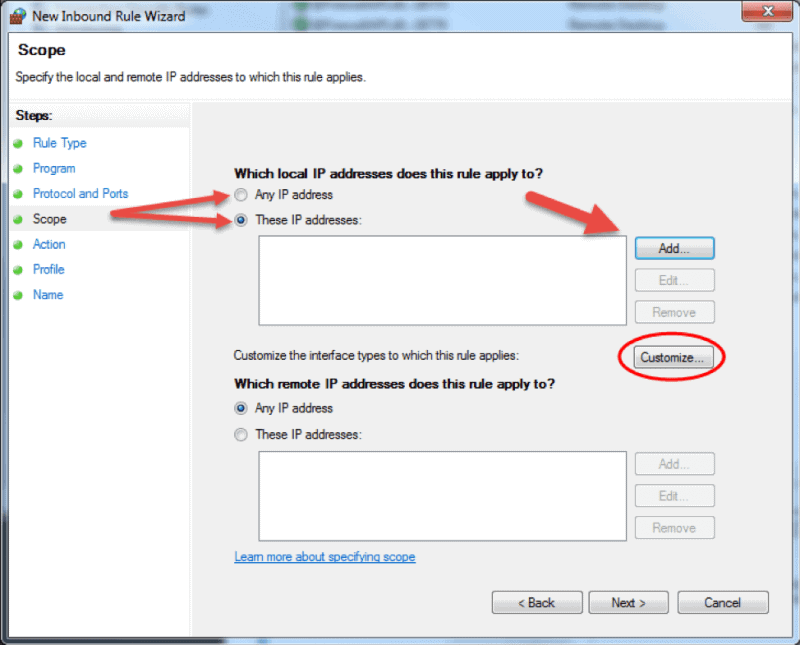
- The Scope step of the wizard allows you to input local and remote IP addresses whose network traffic applies to the current rule.
- Local. If you select ‘Any IP address’ in the local IP addresses section, then the rule applies to the traffic going through the network device that uses a local IP address. This is always the case with the machine where you are creating the rule. Select ‘These IP addresses’ to state that the rule applies to the packets with an address specified in the list. Click Add to insert the IP address to match. You can later edit or remove any of the IP addresses in the list. You can also apply this rule to a specific interface. Click Customize… and select to apply the rule to connections on all interfaces or chose one of the available interfaces listed in the box.
- Remote. If you select ‘Any IP address’ in the remote IP addresses section, then the rule applies to the traffic coming from any IP address included in the list. Select ‘These IP addresses’ to insert the remote IP addresses to which the rule applies. Click Add to specify the IP address to match. You can later edit or remove any of the IP addresses in the list.
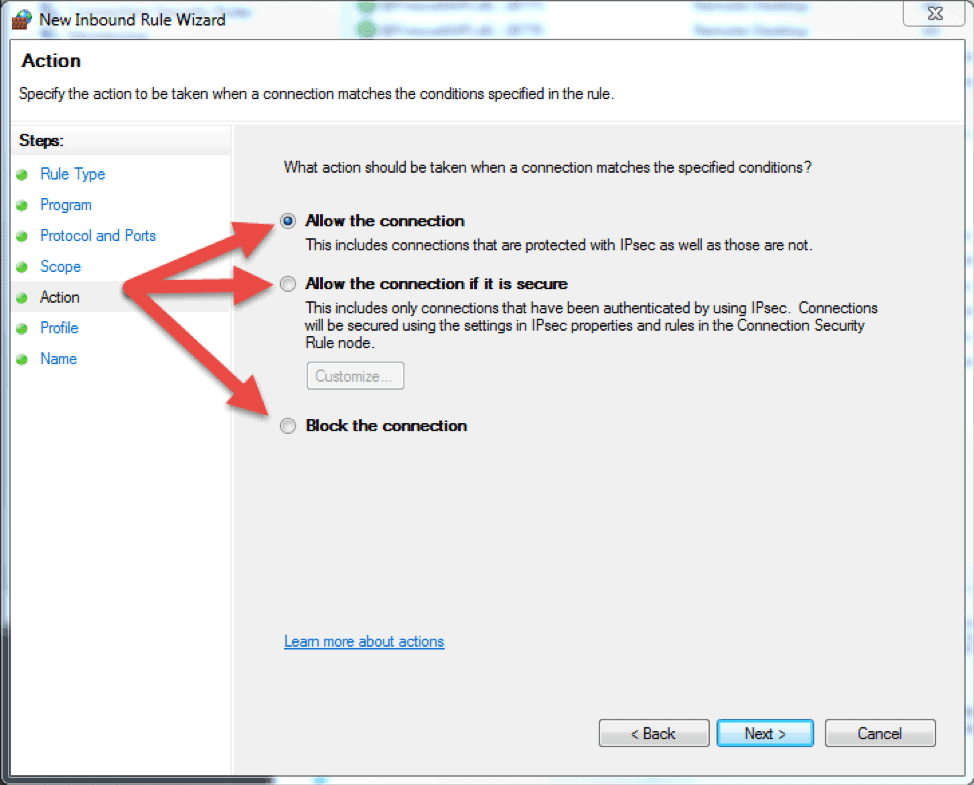
- The next step lets you chose the action the firewall takes when a connection matches the inbound rule configuration. You can select one of the three available options and then click Next to continue.
- Allow the connection. If the connection matches the inbound or the outbound rule configuration, the packets can go through the firewall.
- Allow the connection if it is secure. Select this option to allow only IPSec connections. If you chose this option, two more steps will appear in the wizard: Users and Computers. The additional steps let you chose users and computers you want to block or grant them access. Click on ‘Customize…’ to configure the authentication and integrity requirements.
- Block the connection. This option blocks all network traffic that matches the firewall rule configuration. If a similar rule with ‘allow’ action is in place, then the block action has the priority unless otherwise is stated in the other rule.
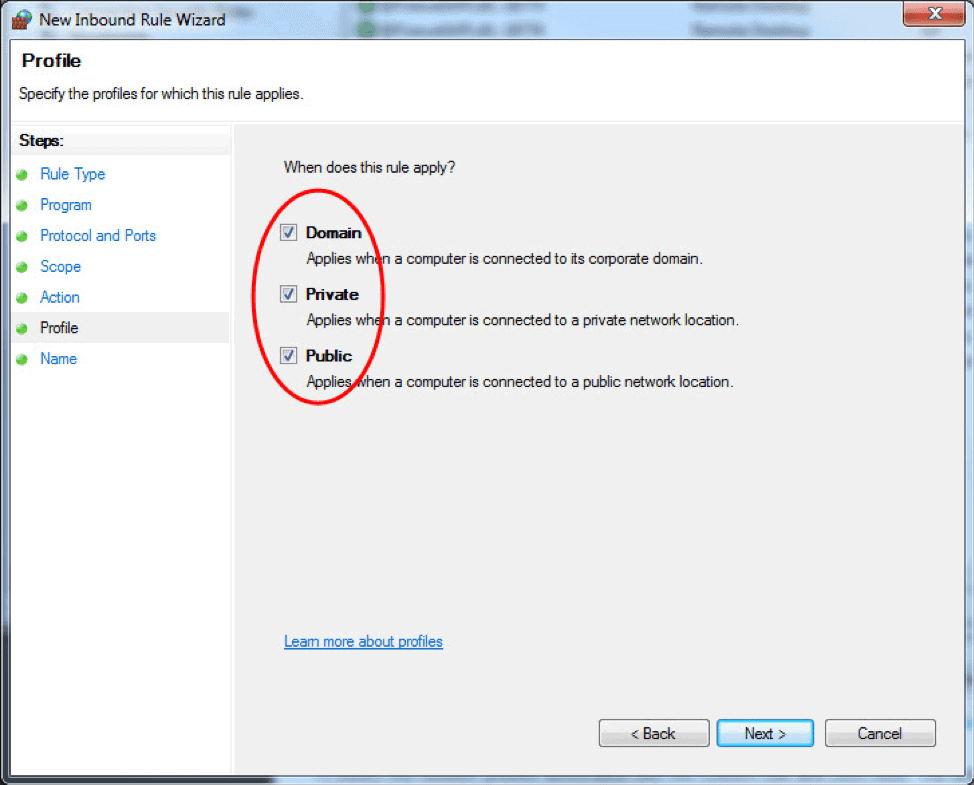
- The Profile step lets you choose the firewall profile the rule will apply to. You can leave everything selected or uncheck a profile that you do not want to include. Click Next to proceed to the final step.
- In the final step, enter the desired name and optional description for this firewall rule, and click Finish.
When you close the wizard, the rule will take effect immediately. You can find the rule in the firewall console when you click on the Inbound rules option. Enabled rules have green checkmark icon while disabled are with grey icons.
How to Edit a Firewall Rule
To edit any existing rule and make additional configuration, open the Windows Firewall with Advanced Security console and select Inbound Rules or Outbound Rules option. Locate and click a rule to see the actions specific to it in the right pane. Select Properties and another window will load where you can edit the rule settings.
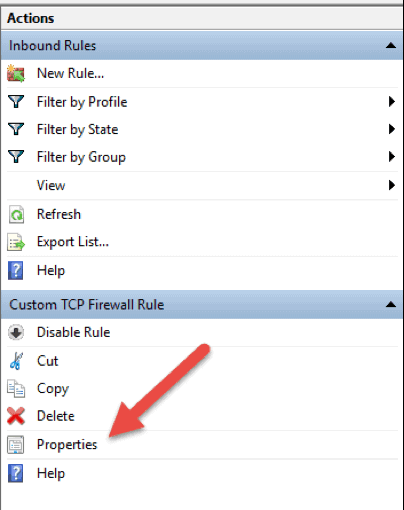
You can also disable, cut, copy, or delete the rule you selected. Make sure you highlight the correct rule to avoid changing firewall configurations for wrong rules.
Tip: you can double click a rule to directly open the Properties window.
How to Create a Firewall Rule with Windows PowerShell
1. Launch the PowerShell command line. You can do so by searching for “powershell” in the start menu, or press Win + R keys on your keyboard and type in “powershell” in the Run box.
2. Insert the following command and hit enter:
New-NetFirewallRule -DisplayName "TCP custom inbound rule" -Enabled:True -Profile Private -Direction Inbound -Action Allow -Protocol TCP -LocalPort 1234New-NetFirewallRule. This command creates a rule. It is followed by a string of parameters and their values.-DisplayName. Specifies the display name of the rule.-Enabled. Enables the rule if set to true. If you omit this parameter, it defaults to true.-Profile. Assigns the rule to the specified profile: Domain, Private, orPublic.-Direction. States if the rule applies to inbound or outbound connections. If you leave it out, it defaults to Inbound.-Action.Specify if the firewall rule will block or allow the connection. If you do not state the action, it defaults to Allow.-Protocol. Specify the protocol for the rule. In this case, we used TCP. Omitting the protocol defaults the setting to Any.-LocalPort. Insert the port where the traffic can go through on the local server. Omitting the port number defaults the setting to Any.
This is only one example of how to add a firewall rule using the Windows PowerShell command line. You can find more examples in the Microsoft PowerShell Documentation.
Conclusion
This article explains the basic functions and different types of firewall and details the steps for managing the Windows Server Firewall within the Windows Firewall with Advanced Security interface. The Windows Firewall Management Console is a powerful tool that allows for creating detailed configurations. If you carefully followed the instructions in the article, you are now able to manage the firewall on your Windows Server.