Если этот параметр включен, пароли должны соответствовать следующим критериям:
- Не содержать имя учетной записи пользователя или части полного имени пользователя, длина которых превышает два последовательных символа.
- Длина должна быть не менее шести символов.
- Содержат символы из трех из следующих четырех категорий: английские заглавные буквы (от A до Z).
7 февраля. 2020 г.
Как отключить пароль, который должен соответствовать требованиям сложности в Windows 10?
Метод 1 — используйте редактор политики
- Нажмите клавиши Windows и R и откройте новое окно «Выполнить».
- Затем введите gpedit. msc или secpol. msc. Нажмите Enter, чтобы запустить редактор групповой политики.
- Перейдите в Настройки безопасности.
- Затем выберите Политика паролей.
- Пароль поиска должен соответствовать требованиям сложности.
- Отключите этот параметр.
4 колода 2020 г.
Какова минимальная длина пароля по умолчанию в политике паролей Windows?
Лучшие практики. Установите Минимальную длину пароля как минимум на 8. Если количество символов установлено на 0, пароль не требуется. В большинстве сред рекомендуется восьмизначный пароль, потому что он достаточно длинный, чтобы обеспечить адекватную безопасность, и достаточно короткий, чтобы пользователи могли легко его запомнить.
Как включить пароль, который должен соответствовать требованиям сложности?
Откройте консоль управления групповой политикой (Пуск / Выполнить / GPMC. MSC), откройте домен, щелкните правой кнопкой мыши и отредактируйте «Политику домена по умолчанию». Затем откройте «Конфигурация компьютера», «Настройки Windows», «Настройки безопасности», «Политики учетной записи» и измените настройку требований к сложности пароля.
Что мне делать, если я забыл пароль Windows 10?
Сброс пароля локальной учетной записи Windows 10
- Выберите ссылку «Сбросить пароль» на экране входа. Если вместо этого вы используете PIN-код, см. Раздел Проблемы при входе с помощью PIN-кода. Если вы используете рабочее устройство, подключенное к сети, вы можете не увидеть возможность сбросить пароль или PIN-код. …
- Ответьте на ваши контрольные вопросы.
- Введите новый пароль.
- Войдите в систему, как обычно, с новым паролем.
Какой хороший пароль Microsoft?
Надежный пароль: не менее 12 символов, но лучше 14 или более. Комбинация прописных букв, строчных букв, цифр и символов. Ни слова, которое можно найти в словаре.
Что такое сложность пароля?
Теоретически основное преимущество правил сложности паролей состоит в том, что они заставляют использовать уникальные пароли, которые труднее взломать. Чем больше требований вы предъявляете, тем больше возможных комбинаций букв, цифр и символов. … В этом суть взлома паролей.
Какие пароли или PIN-коды более безопасны?
«Не структура PIN-кода (длина, сложность) делает его лучше пароля, а то, как он работает», — заявляет Microsoft. Теоретически, поскольку PIN-коды привязаны к устройству, они считаются более безопасными.
Каковы требования к надежному паролю?
ХАРАКТЕРИСТИКИ СИЛЬНЫХ ПАРОЛЕЙ
- Не менее 8 символов — чем больше символов, тем лучше.
- Смесь как прописных, так и строчных букв.
- Смесь букв и цифр.
- Включение хотя бы одного специального символа, например! @ #? ]
Как узнать сложность пароля Windows?
Правила сложности пароля Windows
- Пароль не должен содержать имя учетной записи пользователя или более двух последовательных символов от полного имени пользователя.
- Пароль должен состоять из шести или более символов.
- Пароль должен содержать символы из трех из следующих четырех категорий: символы верхнего регистра AZ (латинский алфавит)
Какова минимальная длина пароля?
Общие рекомендации, отстаиваемые сторонниками безопасности программных систем, включают: Используйте пароль не менее 20 символов, если это разрешено. Включите буквы в нижнем и верхнем регистре, цифры и символы, если это разрешено.
Где политика паролей домена по умолчанию?
Политика паролей учетных записей пользователей домена настраивается в политике домена по умолчанию. Политики паролей находятся в следующем разделе GPO: Конфигурация компьютера-> Политики-> Настройки Windows-> Настройки безопасности -> Политики учетных записей -> Политика паролей; Дважды щелкните параметр политики, чтобы изменить его.
Как обеспечить усложнение пароля?
Если вы хотите, чтобы пароль пользователя соответствовал правилам сложности пароля, найдите и дважды щелкните политику «Пароль должен соответствовать требованиям сложности». Вышеупомянутое действие откроет окно настройки сложности пароля. Установите переключатель «Включено» и нажмите кнопку «ОК», чтобы сохранить изменения.
Пароль должен соответствовать требованиям сложности
Английские символы в верхнем регистре (от A до Z) Английские символы в нижнем регистре (от a до z) Базовые 10 цифр (от 0 до 9) Неалфавитные символы (например,!, $, #,%)
Какие символы можно использовать для паролей?
Пароли должны содержать три из четырех типов символов:
- Заглавные буквы: AZ.
- Строчные буквы: аз.
- Цифры: 0-9.
- Символы: ~ `! @ # $% ^ & * () _- + = {[}] |:; ”'<,>.? /
Как составить надежный пароль
Статья обновлена: 15 апреля 2019
ID: 3730
Создавайте надежные пароли и храните их в безопасном месте
Kaspersky Password Manager — менеджер паролей для компьютера и мобильных устройств. Подскажет, если вы используете ненадежные или дублирующиеся пароли, поможет сегенерировать надежный пароль для новой учетной записи. Позволяет безопасно хранить пароли и автоматически заполнять формы авторизации на сайтах.
Мы рекомендуем использовать надежные пароли, чтобы защитить личные данные и конфиденциальную информацию. Не создавайте учетные записи без паролей.
Обязательные требования к надежному паролю
- Пароль должен содержать не менее 8 символов.
Если у вас Windows, убедитесь, что в настройках операционной системы установлена минимальная длина пароля не менее 8 символов. Инструкция ниже. - Пароль должен содержать заглавные и строчные буквы, цифры, пробелы и специальные символы.
Например: oNQZnz$Hx2.
Пароль не должен содержать
- Личную информацию, которую легко узнать. Например: имя, фамилию или дату рождения.
- Очевидные и простые слова, фразы, устойчивые выражения и наборы символов, которые легко подобрать. Например: password, parol, abcd, qwerty или asdfg, 1234567.
Способы генерации пароля
- Придумайте алгоритм для составления паролей.
Например, возьмите за основу любимое стихотворение или изречение. Запишите его строчными и заглавными латинскими буквами и замените некоторые из них похожими цифрами или символами: I_p0Mn|O_4y9n0e Mg№vEn|E (Я помню чудное мгновенье). - Воспользуйтесь генератором паролей.
С помощью программы Kaspersky Password Manager вы можете генерировать сложные пароли, проверять их надежность и безопасно хранить. Вы также можете установить в браузере расширение Kaspersky Password Manager для автоматического заполнения полей ввода данных на сайтах.
Как часто менять пароль
Мы рекомендуем менять пароль каждые 3 месяца.
Защита пароля
- Никому не сообщайте и не отправляйте свои пароли.
- Не оставляйте в доступном месте пароли, записанные на бумаге.
- Используйте менеджер паролей или встроенное в браузер хранилище паролей.
- Используйте разные пароли для ваших учетных записей. Если вы будете использовать одинаковые пароли, а злоумышленник узнает пароль от одной учетной записи, он сможет получить доступ ко всем остальным.
Как проверить или изменить минимальную длину пароля в Windows
Вам помогла эта страница?
Вы должны иметь надежный пароль для защиты ваших данных онлайн, и защиты вашей операционной системы. Я бы рекомендовал использовать пароли длиной в 10 знаков, с использованием специальных символов, прописными и строчными буквами, а также цифрами, это сделает ваш пароль более надежным.
Но какая максимальная длина пароля разрешена в Windows 10?
Максимальная длина пароля в Windows 10, ограничена 127 символами. Таким образом, самый длинный пароль, который может быть использован для интерактивного входа в систему на компьютере под управлением Windows 10, составляет 127 символов. Технически, длина паролей может быть 127 знаков максимум, значит, что в качестве пароля для входа в систему вы можете легко использовать фразы, которые легко запомните и это будет вполне надежный пароль.
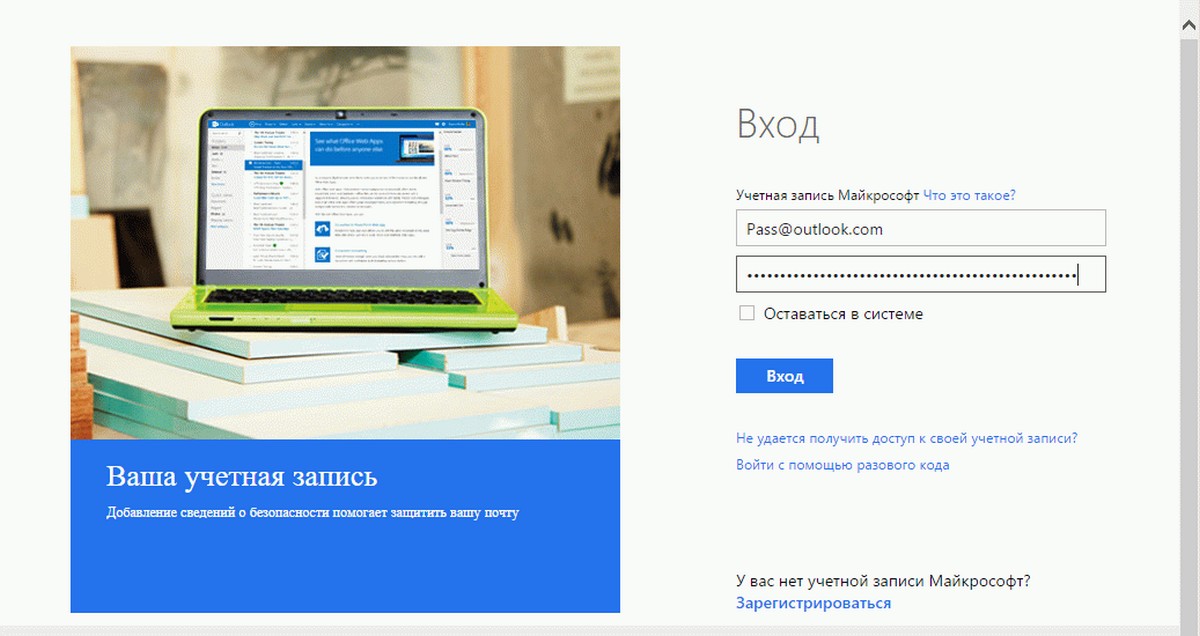
Например, если вы используете учетную запись Microsoft в Windows 10, вы не можете ввести 127 символов. Это потому, что учетные записи Microsoft (Live, Outlook, Hotmail и т.д.) имеют максимальный предел в 16 символов. Таким образом, даже несмотря на то, Windows 10 позволяет использовать 127 символов, вы вынуждены использовать пароль длинной максимум в 16 символов.
Yahoo и Google в этом случае лучше, и позволит использовать пароль в 32 и 200 символов соответственно.
Если вы в своем аккаунте Microsoft введете длинный пароль, вы увидите следующее сообщение об ошибке:
Пароли для учетной записи Microsoft может содержать 16 символов. Если вы используете пароль, который имеет более чем 16 символов, введите только первые 16.
Это не означает, что ваш пароль был сокращен, Windows Live ID пароли всегда были ограничены 16 символами и все остальные символы пароля будут проигнорированы.
Чтобы избежать этого сообщения об ошибке в будущем, вам нужно вводить только первые 16 символов вашего пароля, сообщает Microsoft.
Минимальное количество символов, используемых для входа в Windows, и учетную запись Microsoft равно 8, и может включать в себя все типы специальных символов (за исключением пробела). Вы также можете использовать ALT + Numpad для создания специальных символов и Windows 10 с радостью примет их.
Вход и Диалоговое окно ввода пароля.
Ввод логина и пароля в Windows 10, ограничен текстовым полем, которое может отображать только 32 символа. Но поскольку технический предел равен 127 символам, вы можете продолжать набирать пароль, даже если вы достигнете предела текстового поля. В текстовом поле будет отображаться только последние 32 символа, но вы можете быть уверены, что все 127 символов были записаны в диалоговом окне Входа или сброса пароля. Как упоминалось ранее, все 127 символов принимаются, хотя и не отображается в текстовом поле, в следствии ограничений.
Наложение ограничений на пароли.
Вы можете использовать редактор групповой политики или командную строку, для ограничения символов пароля — например, минимальной и максимальной длины паролей, использование специальных символов, истечение срока паролей и многое другое.
Итог.
1. При использовании 127 символов можно легко использовать в качестве надежного и легко запоминающегося пароля фразу из любимого фильма или стихотворения.
2. Если вы используете операционную систему старше Windows NT, сократите пароли до 14 символов.
Все.
I can understand that imposing a minimum length on passwords makes a lot of sense (to save users from themselves), but my bank has a requirement that passwords are between 6 and 8 characters long, and I started wondering…
- Wouldn’t this just make it easier for brute force attacks? (Bad)
- Does this imply that my password is being stored unencrypted? (Bad)
If someone with (hopefully) some good IT security professionals working for them are imposing a max password length, should I think about doing similar? What are the pros/cons of this?
asked Sep 19, 2008 at 1:49
9
Passwords are hashed to 32, 40, 128, whatever length. The only reason for a minimum length is to prevent easy to guess passwords. There is no purpose for a maximum length.
The obligatory XKCD explaining why you’re doing your user a disservice if you impose a max length:
answered Sep 19, 2008 at 1:52
epochwolfepochwolf
12.2k14 gold badges59 silver badges70 bronze badges
10
A maximum length specified on a password field should be read as a SECURITY WARNING. Any sensible, security conscious user must assume the worst and expect that this site is storing your password literally (i.e. not hashed, as explained by epochwolf).
In that that is the case:
- Avoid using this site like the plague if possible. They obviously know nothing about security.
- If you truly must use the site, make sure your password is unique — unlike any password you use elsewhere.
If you are developing a site that accepts passwords, do not put a silly password limit, unless you want to get tarred with the same brush.
[Internally, of course your code may treat only the first 256/1024/2k/4k/(whatever) bytes as «significant», in order to avoid crunching on mammoth passwords.]
answered Sep 19, 2008 at 4:51
tardatetardate
16.2k15 gold badges50 silver badges50 bronze badges
7
Allowing for completely unbounded password length has one major drawback if you accept the password from untrusted sources.
The sender could try to give you such a long password that it results in a denial of service for other people. For example, if the password is 1GB of data and you spend all your time accept it until you run out of memory. Now suppose this person sends you this password as many times as you are willing to accept. If you’re not careful about the other parameters involved this could lead to a DoS attack.
Setting the upper bound to something like 256 chars seems overly generous by today’s standards.
answered Sep 19, 2008 at 2:04
Jason DagitJason Dagit
13.5k8 gold badges33 silver badges55 bronze badges
8
First, do not assume that banks have good IT security professionals working for them. Plenty don’t.
That said, maximum password length is worthless. It often requires users to create a new password (arguments about the value of using different passwords on every site aside for the moment), which increases the likelihood they will just write them down. It also greatly increases the susceptibility to attack, by any vector from brute force to social engineering.
answered Sep 19, 2008 at 1:55
SparrSparr
7,41031 silver badges47 bronze badges
10
Setting maximum password length less than 128 characters is now discouraged by OWASP Authentication Cheat Sheet
https://www.owasp.org/index.php/Authentication_Cheat_Sheet
Citing the whole paragraph:
Longer passwords provide a greater combination of characters and consequently make it more difficult for an attacker to guess.
Minimum length of the passwords should be enforced by the application.
Passwords shorter than 10 characters are considered to be weak ([1]).
While minimum length enforcement may cause problems with memorizing passwords among some users, applications should encourage them to set passphrases (sentences or combination of words) that can be much longer than typical passwords and yet much easier to remember.Maximum password length should not be set too low, as it will prevent users from creating passphrases. Typical maximum length is 128 characters.
Passphrases shorter than 20 characters are usually considered weak if they only consist of lower case Latin characters. Every character counts!!Make sure that every character the user types in is actually included in the password. We’ve seen systems that truncate the password at a length shorter than what the user provided (e.g., truncated at 15 characters when they entered 20).
This is usually handled by setting the length of ALL password input fields to be exactly the same length as the maximum length password. This is particularly important if your max password length is short, like 20-30 characters.
ABM
1,5982 gold badges25 silver badges41 bronze badges
answered May 13, 2013 at 17:49
kravietzkravietz
10.3k2 gold badges33 silver badges27 bronze badges
3
One reason I can imagine for enforcing a maximum password length is if the frontend must interface with many legacy system backends, one of which itself enforces a maximum password length.
Another thinking process might be that if a user is forced to go with a short password they’re more likely to invent random gibberish than an easily guessed (by their friends/family) catch-phrase or nickname. This approach is of course only effective if the frontend enforces mixing numbers/letters and rejects passwords which have any dictionary words, including words written in l33t-speak.
answered Sep 19, 2008 at 2:23
mbac32768mbac32768
11.4k9 gold badges34 silver badges40 bronze badges
1
One potentially valid reason to impose some maximum password length is that the process of hashing it (due to the use of a slow hashing function such as bcrypt) takes up too much time; something that could be abused in order to execute a DOS attack against the server.
Then again, servers should be configured to automatically drop request handlers that take too long. So I doubt this would be much of a problem.
answered Sep 7, 2012 at 21:09
AardvarkSoupAardvarkSoup
1,0518 silver badges18 bronze badges
1
I think you’re very right on both bullet points. If they’re storing the passwords hashed, as they should, then password length doesn’t affect their DB schema whatsoever. Having an open-ended password length throws in one more variable that a brute-force attacker has to account for.
It’s hard to see any excuse for limiting password length, besides bad design.
answered Sep 19, 2008 at 1:54
Lucas OmanLucas Oman
15.4k2 gold badges44 silver badges45 bronze badges
The only benefit I can see to a maximum password length would be to eliminate the risk of a buffer overflow attack caused by an overly long password, but there are much better ways to handle that situation.
answered Sep 19, 2008 at 2:02
DrStalkerDrStalker
8,84116 gold badges43 silver badges47 bronze badges
1
Ignore the people saying not to validate long passwords. Owasp literally says that 128 chars should be enough. Just to give enough breath space you can give a bit more say 300, 250, 500 if you feel like it.
https://www.owasp.org/index.php/Authentication_Cheat_Sheet#Password_Length
Password Length Longer passwords provide a greater combination of
characters and consequently make it more difficult for an attacker to
guess.…
Maximum password length should not be set too low, as it will prevent
users from creating passphrases. Typical maximum length is 128
characters. Passphrases shorter than 20 characters are usually
considered weak if they only consist of lower case Latin characters.
answered Jun 17, 2018 at 9:18
CommonSenseCodeCommonSenseCode
22.6k32 gold badges127 silver badges182 bronze badges
1
My bank does this too. It used to allow any password, and I had a 20 character one. One day I changed it, and lo and behold it gave me a maximum of 8, and had cut out non-alphanumeric characters which were in my old password. Didn’t make any sense to me.
All the back-end systems at the bank worked before when I was using my 20 char password with non alpha-numerics, so legacy support can’t have been the reason. And even if it was, they should still allow you to have arbitrary passwords, and then make a hash that fits the requirements of the legacy systems. Better still, they should fix the legacy systems.
A smart card solution would not go well with me. I already have too many cards as it is… I don’t need another gimmick.
answered Sep 19, 2008 at 3:22
Vincent McNabbVincent McNabb
32.5k6 gold badges31 silver badges52 bronze badges
1
If you accept an arbitrary sized password then one assumes that it is getting truncated to a curtain length for performance reasons before it is hashed. The issue with truncation is that as your server performance increases over time you can’t easily increase the length before truncation as its hash would clearly be different. Of course you could have a transition period where both lengths are hashed and checked but this uses more resources.
answered Jul 31, 2014 at 15:40
UserUser
3195 silver badges16 bronze badges
Try not to impose any limitation unless necessary. Be warned: it might and will be necessary in a lot of different cases. Dealing with legacy systems is one of these reasons. Make sure you test the case of very long passwords well (can your system deal with 10MB long passwords?). You can run into Denial of Service (DoS) problems because the Key Defivation Functions (KDF) you will be using (usually PBKDF2, bcrypt, scrypt) will take to much time and resources. Real life example: http://arstechnica.com/security/2013/09/long-passwords-are-good-but-too-much-length-can-be-bad-for-security/
answered Mar 22, 2015 at 21:15
Marek PuchalskiMarek Puchalski
3,0021 gold badge25 silver badges34 bronze badges
Storage is cheap, why limit the password length. Even if you’re encrypting the password as opposed to just hashing it a 64 character string isn’t going to take much more than a 6 character string to encrypt.
Chances are the bank system is overlaying an older system so they were only able to allow a certain amount of space for the password.
answered Sep 19, 2008 at 1:51
LizBLizB
2,18316 silver badges17 bronze badges
2
Should there be a maximum length? This is a curious topic in IT in that, longer passwords are typically harder to remember, and therefore more likely to get written down (a BIG no-no for obvious reasons). Longer passwords also tend to get forgotten more, which while not necessarily a security risk, can lead to administrative hassles, lost productivity, etc. Admins who believe that these issues are pressing are likely to impose maximum lengths on passwords.
I personally believe on this specific issue, to each user their own. If you think you can remember a 40 character password, then all the more power to you!
Having said that though, passwords are fast becoming an outdated mode of security, Smart Cards and certificate authentication prove very difficult to impossible to brute force as you stated is an issue, and only a public key need be stored on the server end with the private key on your card/computer at all times.
answered Sep 19, 2008 at 1:59
tekiegregtekiegreg
1,6676 gold badges25 silver badges41 bronze badges
1
Longer passwords, or pass-phrases, are harder to crack simply based on length, and easier to remember than requiring a complex password.
Probably best to go for a fairly long (10+) minimum length, restricting the length useless.
answered Sep 19, 2008 at 2:00
benPearcebenPearce
37.3k14 gold badges64 silver badges96 bronze badges
Legacy systems (mentioned already) or interfacing outside vendor’s systems might necessitate the 8 character cap. It could also be a misguided attempt to save the users from themselves. Limiting it in that fashion will result in too many pssw0rd1, pssw0rd2, etc. passwords in the system.
answered Sep 19, 2008 at 3:04
One reason passwords may not be hashed is the authentication algorithm used. For example, some digest algorithms require a plaintext version of the password at the server as the authentication mechanism involves both the client and the server performing the same maths on the entered password (which generally won’t produce the same output each time as the password is combined with a randomly generated ‘nonce’, which is shared between the two machines).
Often this can be strengthened as the digest can be part computed in some cases, but not always. A better route is for the password to be stored with reversible encryption — this then means the application sources need to be protected as they’ll contain the encryption key.
Digst auth is there to allow authentication over otherwise non-encrypted channels. If using SSL or some other full-channel encryption, then there’s no need to use digest auth mechanisms, meaning passwords can be stored hashed instead (as passwords could be sent plaintext over the wire safely (for a given value of safe).
answered Mar 15, 2014 at 12:06
Chris JChris J
30.3k6 gold badges68 silver badges109 bronze badges
I found using the same characters for the first 72 bytes of a password gives a successful verification using password_hash() and password_verify() in PHP, no matter what random string comes after the first 72 bytes.
From PHP docs: https://www.php.net/manual/en/function.password-hash.php
Caution: Using the PASSWORD_BCRYPT as the algorithm, will result in the password parameter being truncated to a maximum length of 72 bytes.
answered Jun 3, 2022 at 23:14
dewddewd
4,3603 gold badges28 silver badges42 bronze badges
In .net core 6 I use HashPasswordV3 method that it use HMACSHA512 with 1000 iterations. I tested some password length and it generate a 86 characters hash.
So I set the PasswordHash field in sql server for varchar(100).
https://stackoverflow.com/a/72429730/9875486
answered Sep 8, 2022 at 13:36
M KomaeiM Komaei
5,6352 gold badges19 silver badges29 bronze badges
Just 8 char long passwords sound simply wrong. If there ought to be a limit, then atleast 20 char is better idea.
answered Sep 19, 2008 at 2:05
1
I think the only limit that should be applied is like a 2000 letter limit, or something else insainly high, but only to limit the database size if that is an issue
answered Sep 22, 2008 at 8:24
Josh HuntJosh Hunt
14k26 gold badges78 silver badges98 bronze badges
2
I can understand that imposing a minimum length on passwords makes a lot of sense (to save users from themselves), but my bank has a requirement that passwords are between 6 and 8 characters long, and I started wondering…
- Wouldn’t this just make it easier for brute force attacks? (Bad)
- Does this imply that my password is being stored unencrypted? (Bad)
If someone with (hopefully) some good IT security professionals working for them are imposing a max password length, should I think about doing similar? What are the pros/cons of this?
asked Sep 19, 2008 at 1:49
9
Passwords are hashed to 32, 40, 128, whatever length. The only reason for a minimum length is to prevent easy to guess passwords. There is no purpose for a maximum length.
The obligatory XKCD explaining why you’re doing your user a disservice if you impose a max length:
answered Sep 19, 2008 at 1:52
epochwolfepochwolf
12.2k14 gold badges59 silver badges70 bronze badges
10
A maximum length specified on a password field should be read as a SECURITY WARNING. Any sensible, security conscious user must assume the worst and expect that this site is storing your password literally (i.e. not hashed, as explained by epochwolf).
In that that is the case:
- Avoid using this site like the plague if possible. They obviously know nothing about security.
- If you truly must use the site, make sure your password is unique — unlike any password you use elsewhere.
If you are developing a site that accepts passwords, do not put a silly password limit, unless you want to get tarred with the same brush.
[Internally, of course your code may treat only the first 256/1024/2k/4k/(whatever) bytes as «significant», in order to avoid crunching on mammoth passwords.]
answered Sep 19, 2008 at 4:51
tardatetardate
16.2k15 gold badges50 silver badges50 bronze badges
7
Allowing for completely unbounded password length has one major drawback if you accept the password from untrusted sources.
The sender could try to give you such a long password that it results in a denial of service for other people. For example, if the password is 1GB of data and you spend all your time accept it until you run out of memory. Now suppose this person sends you this password as many times as you are willing to accept. If you’re not careful about the other parameters involved this could lead to a DoS attack.
Setting the upper bound to something like 256 chars seems overly generous by today’s standards.
answered Sep 19, 2008 at 2:04
Jason DagitJason Dagit
13.5k8 gold badges33 silver badges55 bronze badges
8
First, do not assume that banks have good IT security professionals working for them. Plenty don’t.
That said, maximum password length is worthless. It often requires users to create a new password (arguments about the value of using different passwords on every site aside for the moment), which increases the likelihood they will just write them down. It also greatly increases the susceptibility to attack, by any vector from brute force to social engineering.
answered Sep 19, 2008 at 1:55
SparrSparr
7,41031 silver badges47 bronze badges
10
Setting maximum password length less than 128 characters is now discouraged by OWASP Authentication Cheat Sheet
https://www.owasp.org/index.php/Authentication_Cheat_Sheet
Citing the whole paragraph:
Longer passwords provide a greater combination of characters and consequently make it more difficult for an attacker to guess.
Minimum length of the passwords should be enforced by the application.
Passwords shorter than 10 characters are considered to be weak ([1]).
While minimum length enforcement may cause problems with memorizing passwords among some users, applications should encourage them to set passphrases (sentences or combination of words) that can be much longer than typical passwords and yet much easier to remember.Maximum password length should not be set too low, as it will prevent users from creating passphrases. Typical maximum length is 128 characters.
Passphrases shorter than 20 characters are usually considered weak if they only consist of lower case Latin characters. Every character counts!!Make sure that every character the user types in is actually included in the password. We’ve seen systems that truncate the password at a length shorter than what the user provided (e.g., truncated at 15 characters when they entered 20).
This is usually handled by setting the length of ALL password input fields to be exactly the same length as the maximum length password. This is particularly important if your max password length is short, like 20-30 characters.
ABM
1,5982 gold badges25 silver badges41 bronze badges
answered May 13, 2013 at 17:49
kravietzkravietz
10.3k2 gold badges33 silver badges27 bronze badges
3
One reason I can imagine for enforcing a maximum password length is if the frontend must interface with many legacy system backends, one of which itself enforces a maximum password length.
Another thinking process might be that if a user is forced to go with a short password they’re more likely to invent random gibberish than an easily guessed (by their friends/family) catch-phrase or nickname. This approach is of course only effective if the frontend enforces mixing numbers/letters and rejects passwords which have any dictionary words, including words written in l33t-speak.
answered Sep 19, 2008 at 2:23
mbac32768mbac32768
11.4k9 gold badges34 silver badges40 bronze badges
1
One potentially valid reason to impose some maximum password length is that the process of hashing it (due to the use of a slow hashing function such as bcrypt) takes up too much time; something that could be abused in order to execute a DOS attack against the server.
Then again, servers should be configured to automatically drop request handlers that take too long. So I doubt this would be much of a problem.
answered Sep 7, 2012 at 21:09
AardvarkSoupAardvarkSoup
1,0518 silver badges18 bronze badges
1
I think you’re very right on both bullet points. If they’re storing the passwords hashed, as they should, then password length doesn’t affect their DB schema whatsoever. Having an open-ended password length throws in one more variable that a brute-force attacker has to account for.
It’s hard to see any excuse for limiting password length, besides bad design.
answered Sep 19, 2008 at 1:54
Lucas OmanLucas Oman
15.4k2 gold badges44 silver badges45 bronze badges
The only benefit I can see to a maximum password length would be to eliminate the risk of a buffer overflow attack caused by an overly long password, but there are much better ways to handle that situation.
answered Sep 19, 2008 at 2:02
DrStalkerDrStalker
8,84116 gold badges43 silver badges47 bronze badges
1
Ignore the people saying not to validate long passwords. Owasp literally says that 128 chars should be enough. Just to give enough breath space you can give a bit more say 300, 250, 500 if you feel like it.
https://www.owasp.org/index.php/Authentication_Cheat_Sheet#Password_Length
Password Length Longer passwords provide a greater combination of
characters and consequently make it more difficult for an attacker to
guess.…
Maximum password length should not be set too low, as it will prevent
users from creating passphrases. Typical maximum length is 128
characters. Passphrases shorter than 20 characters are usually
considered weak if they only consist of lower case Latin characters.
answered Jun 17, 2018 at 9:18
CommonSenseCodeCommonSenseCode
22.6k32 gold badges127 silver badges182 bronze badges
1
My bank does this too. It used to allow any password, and I had a 20 character one. One day I changed it, and lo and behold it gave me a maximum of 8, and had cut out non-alphanumeric characters which were in my old password. Didn’t make any sense to me.
All the back-end systems at the bank worked before when I was using my 20 char password with non alpha-numerics, so legacy support can’t have been the reason. And even if it was, they should still allow you to have arbitrary passwords, and then make a hash that fits the requirements of the legacy systems. Better still, they should fix the legacy systems.
A smart card solution would not go well with me. I already have too many cards as it is… I don’t need another gimmick.
answered Sep 19, 2008 at 3:22
Vincent McNabbVincent McNabb
32.5k6 gold badges31 silver badges52 bronze badges
1
If you accept an arbitrary sized password then one assumes that it is getting truncated to a curtain length for performance reasons before it is hashed. The issue with truncation is that as your server performance increases over time you can’t easily increase the length before truncation as its hash would clearly be different. Of course you could have a transition period where both lengths are hashed and checked but this uses more resources.
answered Jul 31, 2014 at 15:40
UserUser
3195 silver badges16 bronze badges
Try not to impose any limitation unless necessary. Be warned: it might and will be necessary in a lot of different cases. Dealing with legacy systems is one of these reasons. Make sure you test the case of very long passwords well (can your system deal with 10MB long passwords?). You can run into Denial of Service (DoS) problems because the Key Defivation Functions (KDF) you will be using (usually PBKDF2, bcrypt, scrypt) will take to much time and resources. Real life example: http://arstechnica.com/security/2013/09/long-passwords-are-good-but-too-much-length-can-be-bad-for-security/
answered Mar 22, 2015 at 21:15
Marek PuchalskiMarek Puchalski
3,0021 gold badge25 silver badges34 bronze badges
Storage is cheap, why limit the password length. Even if you’re encrypting the password as opposed to just hashing it a 64 character string isn’t going to take much more than a 6 character string to encrypt.
Chances are the bank system is overlaying an older system so they were only able to allow a certain amount of space for the password.
answered Sep 19, 2008 at 1:51
LizBLizB
2,18316 silver badges17 bronze badges
2
Should there be a maximum length? This is a curious topic in IT in that, longer passwords are typically harder to remember, and therefore more likely to get written down (a BIG no-no for obvious reasons). Longer passwords also tend to get forgotten more, which while not necessarily a security risk, can lead to administrative hassles, lost productivity, etc. Admins who believe that these issues are pressing are likely to impose maximum lengths on passwords.
I personally believe on this specific issue, to each user their own. If you think you can remember a 40 character password, then all the more power to you!
Having said that though, passwords are fast becoming an outdated mode of security, Smart Cards and certificate authentication prove very difficult to impossible to brute force as you stated is an issue, and only a public key need be stored on the server end with the private key on your card/computer at all times.
answered Sep 19, 2008 at 1:59
tekiegregtekiegreg
1,6676 gold badges25 silver badges41 bronze badges
1
Longer passwords, or pass-phrases, are harder to crack simply based on length, and easier to remember than requiring a complex password.
Probably best to go for a fairly long (10+) minimum length, restricting the length useless.
answered Sep 19, 2008 at 2:00
benPearcebenPearce
37.3k14 gold badges64 silver badges96 bronze badges
Legacy systems (mentioned already) or interfacing outside vendor’s systems might necessitate the 8 character cap. It could also be a misguided attempt to save the users from themselves. Limiting it in that fashion will result in too many pssw0rd1, pssw0rd2, etc. passwords in the system.
answered Sep 19, 2008 at 3:04
One reason passwords may not be hashed is the authentication algorithm used. For example, some digest algorithms require a plaintext version of the password at the server as the authentication mechanism involves both the client and the server performing the same maths on the entered password (which generally won’t produce the same output each time as the password is combined with a randomly generated ‘nonce’, which is shared between the two machines).
Often this can be strengthened as the digest can be part computed in some cases, but not always. A better route is for the password to be stored with reversible encryption — this then means the application sources need to be protected as they’ll contain the encryption key.
Digst auth is there to allow authentication over otherwise non-encrypted channels. If using SSL or some other full-channel encryption, then there’s no need to use digest auth mechanisms, meaning passwords can be stored hashed instead (as passwords could be sent plaintext over the wire safely (for a given value of safe).
answered Mar 15, 2014 at 12:06
Chris JChris J
30.3k6 gold badges68 silver badges109 bronze badges
I found using the same characters for the first 72 bytes of a password gives a successful verification using password_hash() and password_verify() in PHP, no matter what random string comes after the first 72 bytes.
From PHP docs: https://www.php.net/manual/en/function.password-hash.php
Caution: Using the PASSWORD_BCRYPT as the algorithm, will result in the password parameter being truncated to a maximum length of 72 bytes.
answered Jun 3, 2022 at 23:14
dewddewd
4,3603 gold badges28 silver badges42 bronze badges
In .net core 6 I use HashPasswordV3 method that it use HMACSHA512 with 1000 iterations. I tested some password length and it generate a 86 characters hash.
So I set the PasswordHash field in sql server for varchar(100).
https://stackoverflow.com/a/72429730/9875486
answered Sep 8, 2022 at 13:36
M KomaeiM Komaei
5,6352 gold badges19 silver badges29 bronze badges
Just 8 char long passwords sound simply wrong. If there ought to be a limit, then atleast 20 char is better idea.
answered Sep 19, 2008 at 2:05
1
I think the only limit that should be applied is like a 2000 letter limit, or something else insainly high, but only to limit the database size if that is an issue
answered Sep 22, 2008 at 8:24
Josh HuntJosh Hunt
14k26 gold badges78 silver badges98 bronze badges
2