English | 中文
Configure IPsec/L2TP VPN Clients
After setting up your own VPN server, follow these steps to configure your devices. IPsec/L2TP is natively supported by Android, iOS, OS X, and Windows. There is no additional software to install. Setup should only take a few minutes. In case you are unable to connect, first check to make sure the VPN credentials were entered correctly.
- Platforms
- Windows
- OS X (macOS)
- Android
- iOS (iPhone/iPad)
- Chrome OS (Chromebook)
- Linux
- IKEv1 troubleshooting
Windows
You may also connect using IKEv2 mode (recommended).
Windows 11
- Right-click on the wireless/network icon in your system tray.
- Select Network and Internet settings, then on the page that opens, click VPN.
- Click the Add VPN button.
- Select Windows (built-in) in the VPN provider drop-down menu.
- Enter anything you like in the Connection name field.
- Enter
Your VPN Server IPin the Server name or address field. - Select L2TP/IPsec with pre-shared key in the VPN type drop-down menu.
- Enter
Your VPN IPsec PSKin the Pre-shared key field. - Enter
Your VPN Usernamein the User name field. - Enter
Your VPN Passwordin the Password field. - Check the Remember my sign-in info checkbox.
- Click Save to save the VPN connection details.
Note: This one-time registry change is required if the VPN server and/or client is behind NAT (e.g. home router).
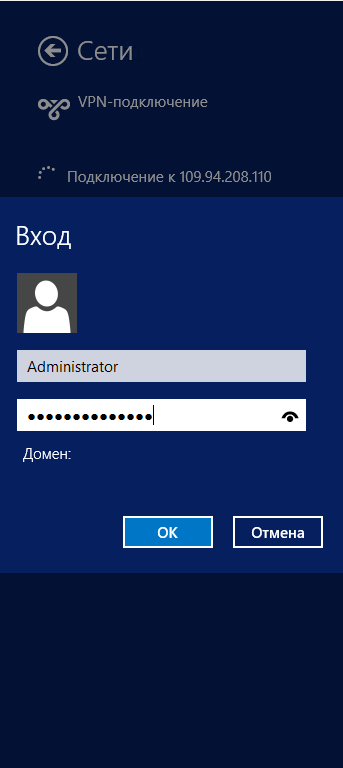
To connect to the VPN: Click the Connect button, or click on the wireless/network icon in your system tray, click VPN, then select the new VPN entry and click Connect. If prompted, enter Your VPN Username and Password, then click OK. You can verify that your traffic is being routed properly by looking up your IP address on Google. It should say «Your public IP address is Your VPN Server IP«.
If you get an error when trying to connect, see Troubleshooting.
Windows 10 and 8
- Right-click on the wireless/network icon in your system tray.
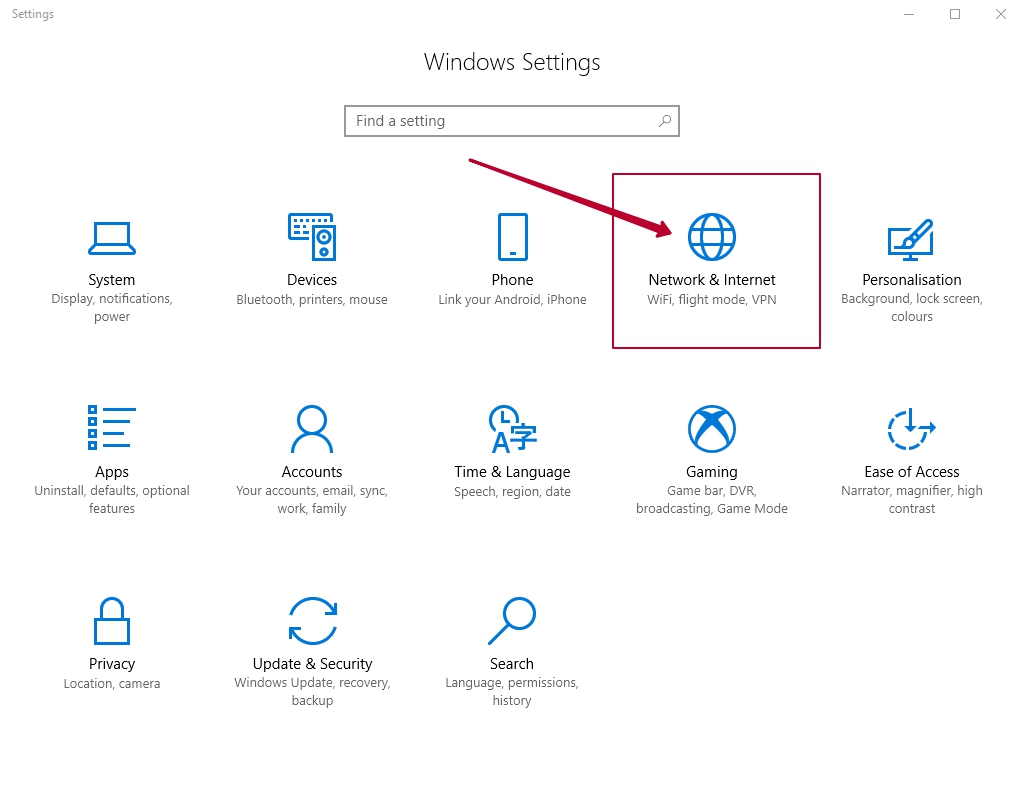
- Select Open Network & Internet settings, then on the page that opens, click Network and Sharing Center.
- Click Set up a new connection or network.
- Select Connect to a workplace and click Next.
- Click Use my Internet connection (VPN).
- Enter
Your VPN Server IPin the Internet address field. - Enter anything you like in the Destination name field, and then click Create.
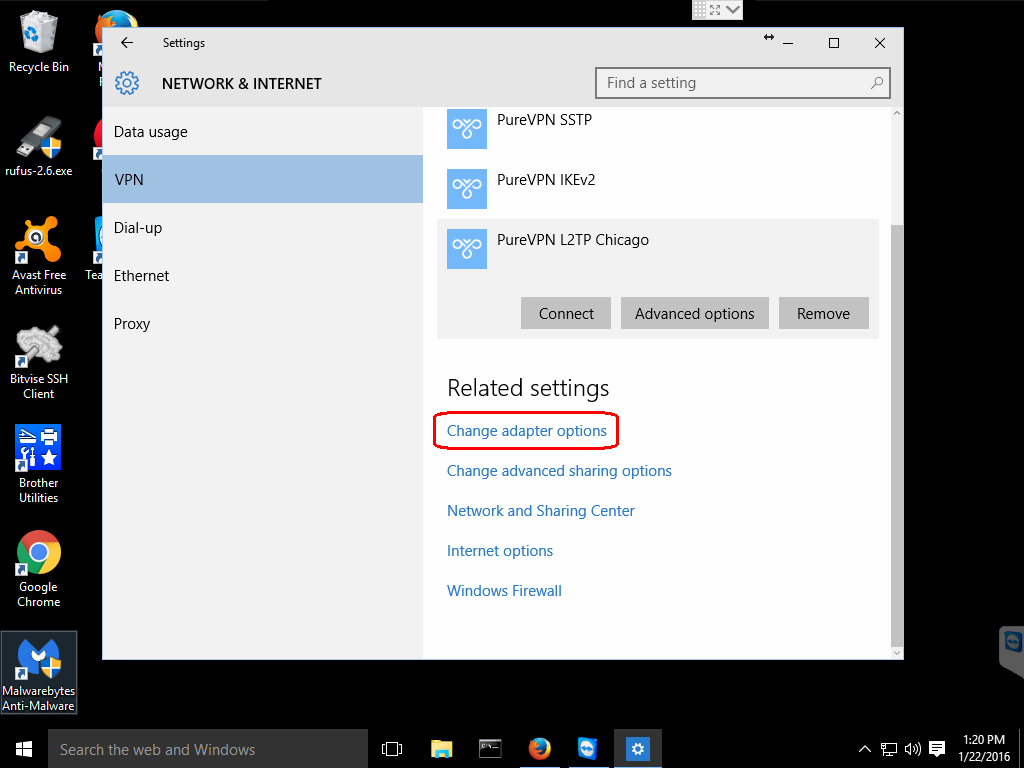
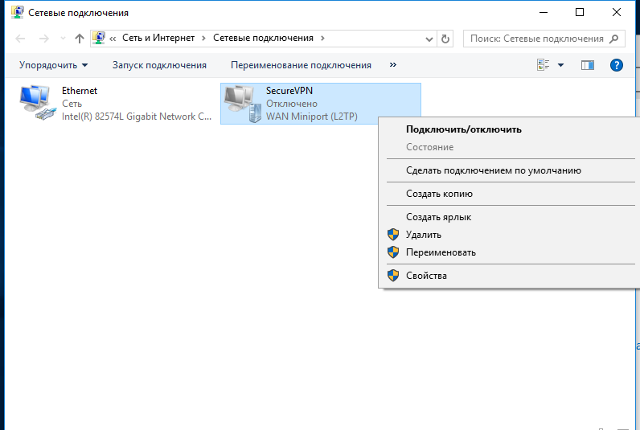
- Return to Network and Sharing Center. On the left, click Change adapter settings.
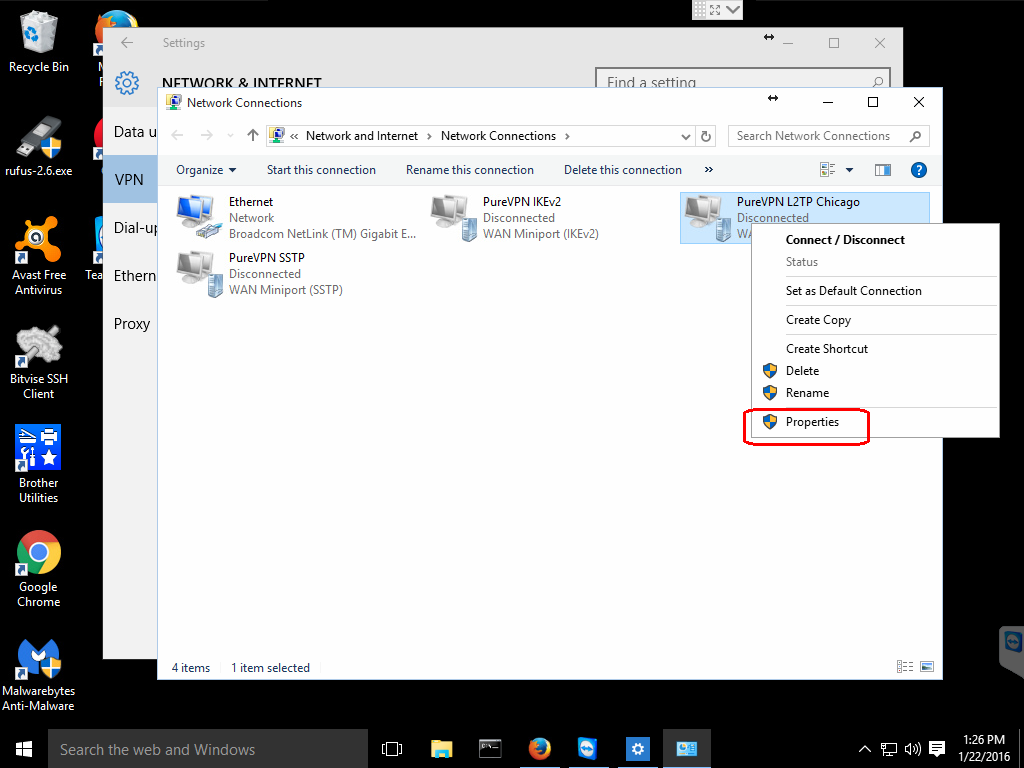
- Right-click on the new VPN entry and choose Properties.
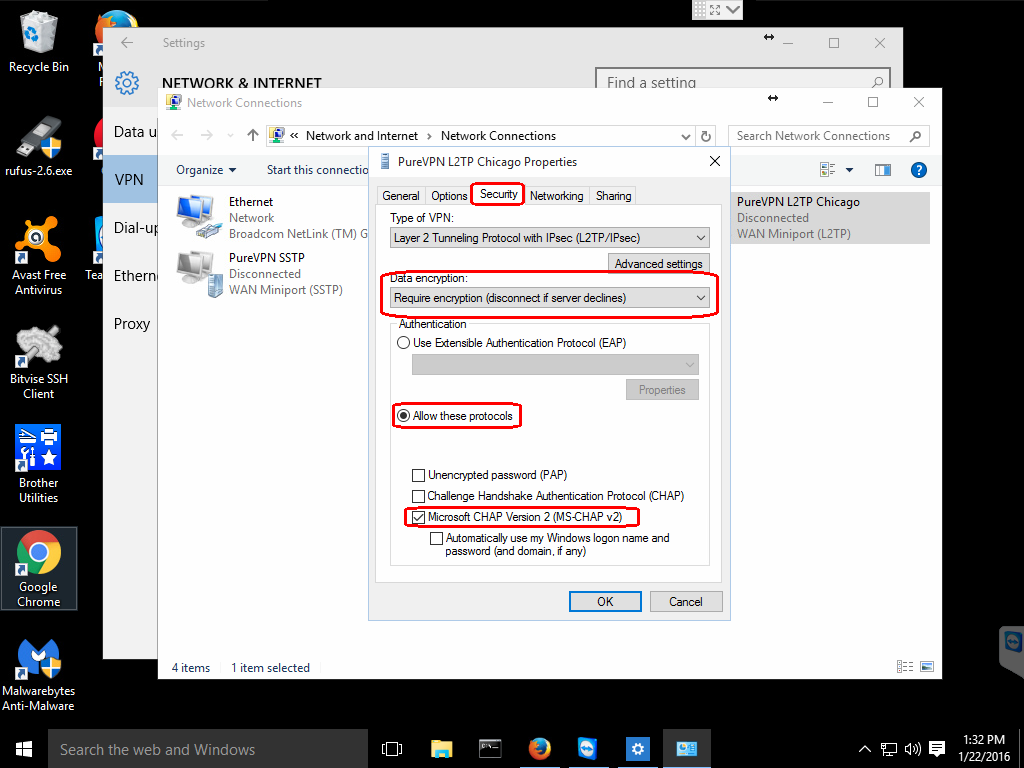
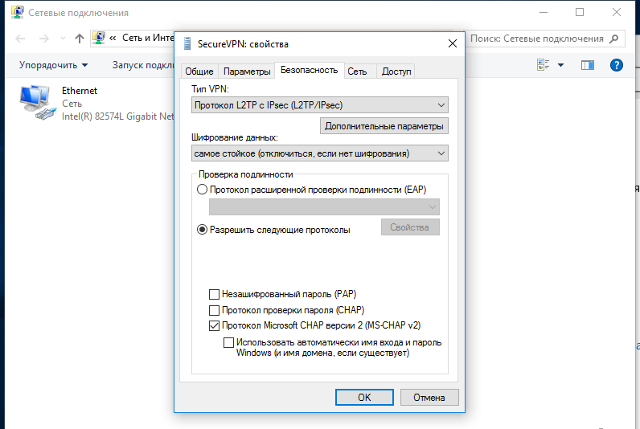
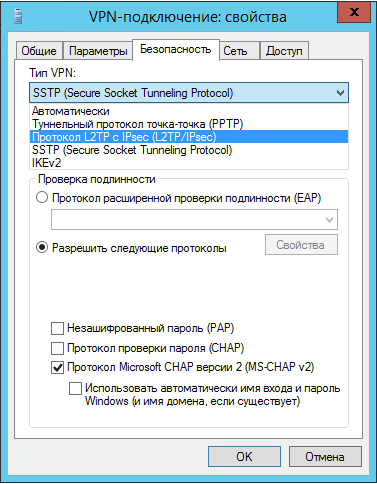
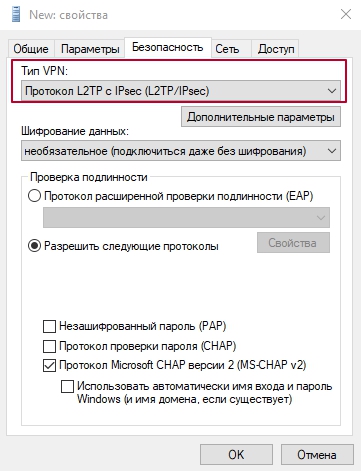
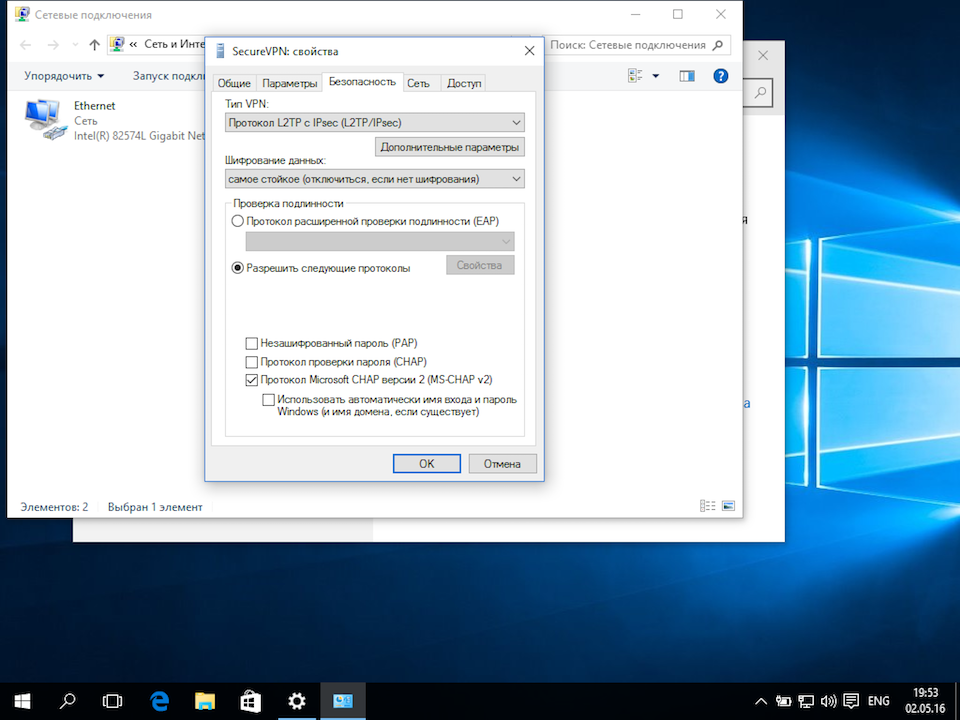
- Click the Security tab. Select «Layer 2 Tunneling Protocol with IPsec (L2TP/IPSec)» for the Type of VPN.
- Click Allow these protocols. Check the «Challenge Handshake Authentication Protocol (CHAP)» and «Microsoft CHAP Version 2 (MS-CHAP v2)» checkboxes.
- Click the Advanced settings button.
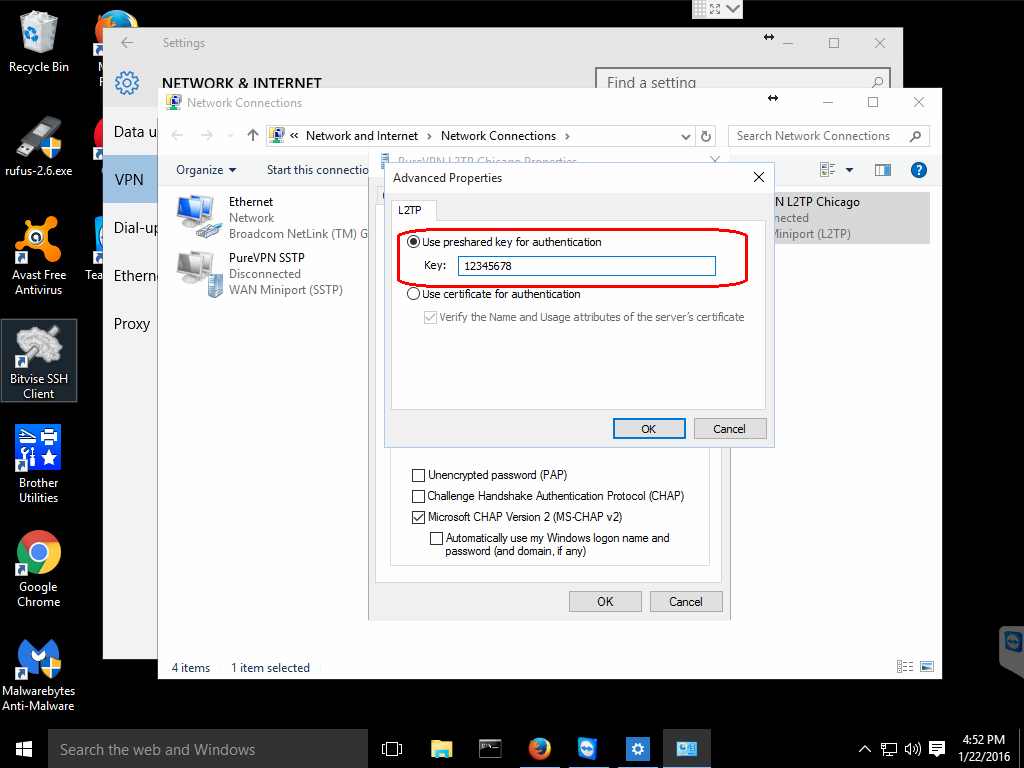
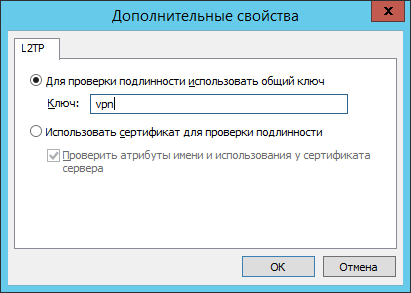
- Select Use preshared key for authentication and enter
Your VPN IPsec PSKfor the Key. - Click OK to close the Advanced settings.
- Click OK to save the VPN connection details.
Note: This one-time registry change is required if the VPN server and/or client is behind NAT (e.g. home router).
To connect to the VPN: Click on the wireless/network icon in your system tray, select the new VPN entry, and click Connect. If prompted, enter Your VPN Username and Password, then click OK. You can verify that your traffic is being routed properly by looking up your IP address on Google. It should say «Your public IP address is Your VPN Server IP«.
If you get an error when trying to connect, see Troubleshooting.
Alternatively, instead of following the steps above, you may create the VPN connection using these Windows PowerShell commands. Replace Your VPN Server IP and Your VPN IPsec PSK with your own values, enclosed in single quotes:
# Disable persistent command history Set-PSReadlineOption –HistorySaveStyle SaveNothing # Create VPN connection Add-VpnConnection -Name 'My IPsec VPN' -ServerAddress 'Your VPN Server IP' ^ -L2tpPsk 'Your VPN IPsec PSK' -TunnelType L2tp -EncryptionLevel Required ^ -AuthenticationMethod Chap,MSChapv2 -Force -RememberCredential -PassThru # Ignore the data encryption warning (data is encrypted in the IPsec tunnel)
Windows 7, Vista and XP
- Click on the Start Menu and go to the Control Panel.
- Go to the Network and Internet section.
- Click Network and Sharing Center.
- Click Set up a new connection or network.
- Select Connect to a workplace and click Next.
- Click Use my Internet connection (VPN).
- Enter
Your VPN Server IPin the Internet address field. - Enter anything you like in the Destination name field.
- Check the Don’t connect now; just set it up so I can connect later checkbox.
- Click Next.
- Enter
Your VPN Usernamein the User name field. - Enter
Your VPN Passwordin the Password field. - Check the Remember this password checkbox.
- Click Create, and then Close.
- Return to Network and Sharing Center. On the left, click Change adapter settings.
- Right-click on the new VPN entry and choose Properties.
- Click the Options tab and uncheck Include Windows logon domain.
- Click the Security tab. Select «Layer 2 Tunneling Protocol with IPsec (L2TP/IPSec)» for the Type of VPN.
- Click Allow these protocols. Check the «Challenge Handshake Authentication Protocol (CHAP)» and «Microsoft CHAP Version 2 (MS-CHAP v2)» checkboxes.
- Click the Advanced settings button.
- Select Use preshared key for authentication and enter
Your VPN IPsec PSKfor the Key. - Click OK to close the Advanced settings.
- Click OK to save the VPN connection details.
Note: This one-time registry change is required if the VPN server and/or client is behind NAT (e.g. home router).
To connect to the VPN: Click on the wireless/network icon in your system tray, select the new VPN entry, and click Connect. If prompted, enter Your VPN Username and Password, then click OK. You can verify that your traffic is being routed properly by looking up your IP address on Google. It should say «Your public IP address is Your VPN Server IP«.
If you get an error when trying to connect, see Troubleshooting.
OS X
You may also connect using IKEv2 (recommended) or IPsec/XAuth mode.
- Open System Preferences and go to the Network section.
- Click the + button in the lower-left corner of the window.
- Select VPN from the Interface drop-down menu.
- Select L2TP over IPSec from the VPN Type drop-down menu.
- Enter anything you like for the Service Name.
- Click Create.
- Enter
Your VPN Server IPfor the Server Address. - Enter
Your VPN Usernamefor the Account Name. - Click the Authentication Settings button.
- In the User Authentication section, select the Password radio button and enter
Your VPN Password. - In the Machine Authentication section, select the Shared Secret radio button and enter
Your VPN IPsec PSK. - Click OK.
- Check the Show VPN status in menu bar checkbox.
- (Important) Click the Advanced button and make sure the Send all traffic over VPN connection checkbox is checked.
- (Important) Click the TCP/IP tab, and make sure Link-local only is selected in the Configure IPv6 section.
- Click OK to close the Advanced settings, and then click Apply to save the VPN connection information.
To connect to the VPN: Use the menu bar icon, or go to the Network section of System Preferences, select the VPN and choose Connect. You can verify that your traffic is being routed properly by looking up your IP address on Google. It should say «Your public IP address is Your VPN Server IP«.
If you get an error when trying to connect, see Troubleshooting.
Android
Important: Android users should instead connect using IKEv2 mode (recommended), which is more secure. Android 12+ only supports IKEv2 mode. The native VPN client in Android uses the less secure modp1024 (DH group 2) for the IPsec/L2TP and IPsec/XAuth («Cisco IPsec») modes.
If you still want to connect using IPsec/L2TP mode, you must first edit /etc/ipsec.conf on the VPN server. Find the line ike=... and append ,aes256-sha2;modp1024,aes128-sha1;modp1024 at the end. Save the file and run sudo service ipsec restart.
Docker users: Add VPN_ENABLE_MODP1024=yes to your env file, then re-create the Docker container.
After that, follow the steps below on your Android device:
- Launch the Settings application.
- Tap «Network & internet». Or, if using Android 7 or earlier, tap More… in the Wireless & networks section.
- Tap VPN.
- Tap Add VPN Profile or the + icon at top-right of screen.
- Enter anything you like in the Name field.
- Select L2TP/IPSec PSK in the Type drop-down menu.
- Enter
Your VPN Server IPin the Server address field. - Leave the L2TP secret field blank.
- Leave the IPSec identifier field blank.
- Enter
Your VPN IPsec PSKin the IPSec pre-shared key field. - Tap Save.
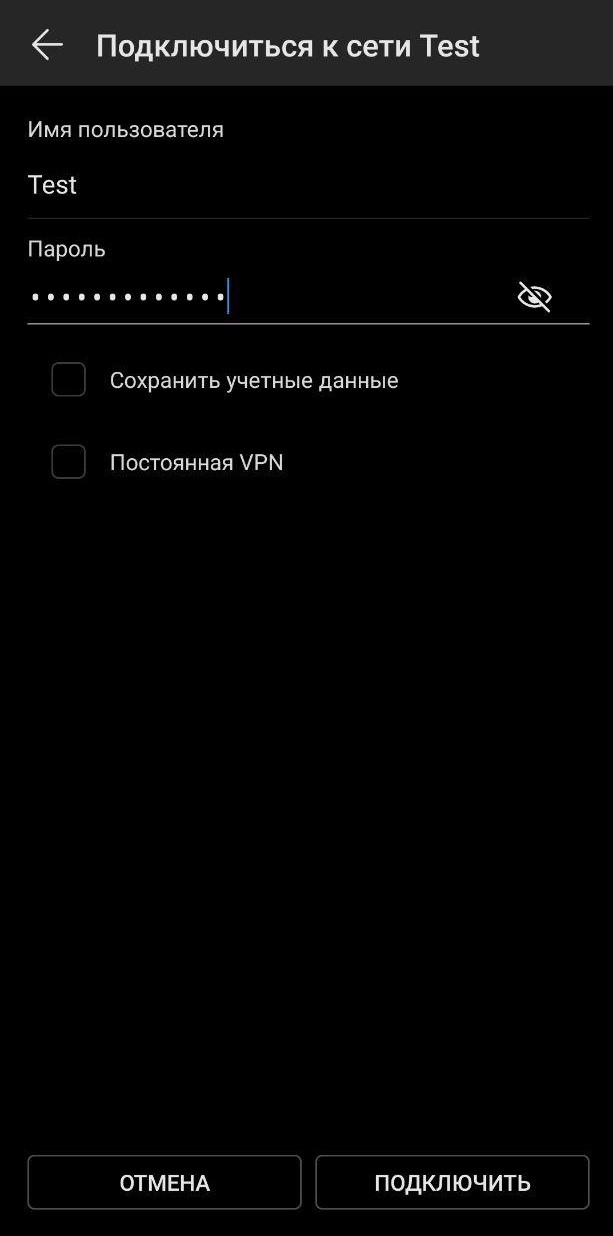
- Tap the new VPN connection.
- Enter
Your VPN Usernamein the Username field. - Enter
Your VPN Passwordin the Password field. - Check the Save account information checkbox.
- Tap Connect.
Once connected, you will see a VPN icon in the notification bar. You can verify that your traffic is being routed properly by looking up your IP address on Google. It should say «Your public IP address is Your VPN Server IP«.
If you get an error when trying to connect, see Troubleshooting.
iOS
You may also connect using IKEv2 (recommended) or IPsec/XAuth mode.
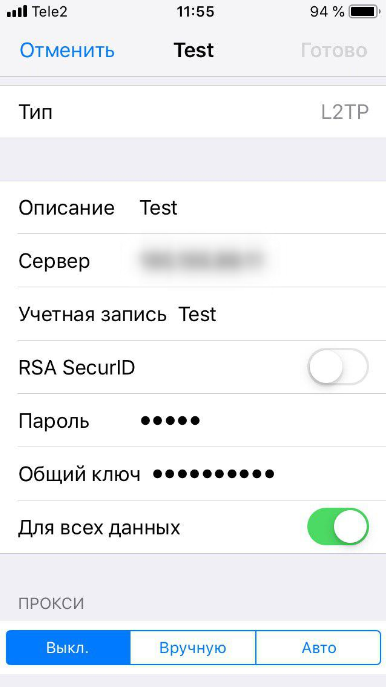
- Go to Settings -> General -> VPN.
- Tap Add VPN Configuration….
- Tap Type. Select L2TP and go back.
- Tap Description and enter anything you like.
- Tap Server and enter
Your VPN Server IP. - Tap Account and enter
Your VPN Username. - Tap Password and enter
Your VPN Password. - Tap Secret and enter
Your VPN IPsec PSK. - Make sure the Send All Traffic switch is ON.
- Tap Done.
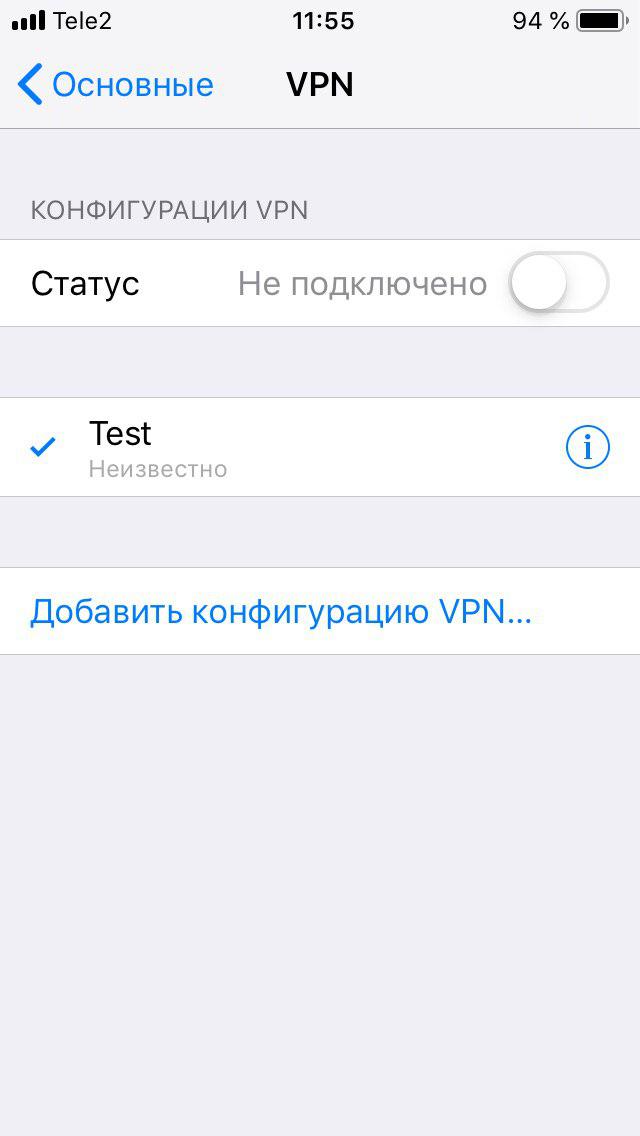
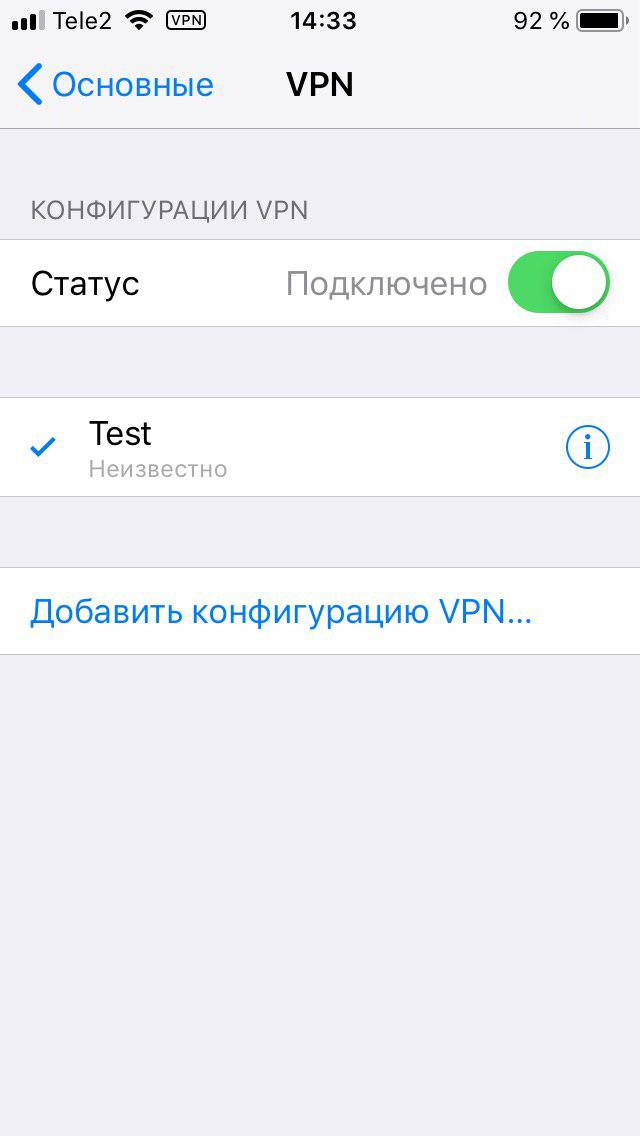
- Slide the VPN switch ON.
Once connected, you will see a VPN icon in the status bar. You can verify that your traffic is being routed properly by looking up your IP address on Google. It should say «Your public IP address is Your VPN Server IP«.
If you get an error when trying to connect, see Troubleshooting.
Chrome OS
You may also connect using IKEv2 mode (recommended).
- Go to Settings -> Network.
- Click Add connection, then click Add built-in VPN.
- Enter anything you like for the Service name.
- Select L2TP/IPsec in the Provider type drop-down menu.
- Enter
Your VPN Server IPfor the Server hostname. - Select Pre-shared key in the Authentication type drop-down menu.
- Enter
Your VPN Usernamefor the Username. - Enter
Your VPN Passwordfor the Password. - Enter
Your VPN IPsec PSKfor the Pre-shared key. - Leave other fields blank.
- Enable Save identity and password.
- Click Connect.
Once connected, you will see a VPN icon overlay on the network status icon. You can verify that your traffic is being routed properly by looking up your IP address on Google. It should say «Your public IP address is Your VPN Server IP«.
If you get an error when trying to connect, see Troubleshooting.
Linux
You may also connect using IKEv2 mode (recommended).
Ubuntu Linux
Ubuntu 18.04 (and newer) users can install the network-manager-l2tp-gnome package using apt, then configure the IPsec/L2TP VPN client using the GUI.
- Go to Settings -> Network -> VPN. Click the + button.
- Select Layer 2 Tunneling Protocol (L2TP).
- Enter anything you like in the Name field.
- Enter
Your VPN Server IPfor the Gateway. - Enter
Your VPN Usernamefor the User name. - Right-click the ? in the Password field, select Store the password only for this user.
- Enter
Your VPN Passwordfor the Password. - Leave the NT Domain field blank.
- Click the IPsec Settings… button.
- Check the Enable IPsec tunnel to L2TP host checkbox.
- Leave the Gateway ID field blank.
- Enter
Your VPN IPsec PSKfor the Pre-shared key. - Expand the Advanced section.
- Enter
aes128-sha1-modp2048for the Phase1 Algorithms. - Enter
aes128-sha1for the Phase2 Algorithms. - Click OK, then click Add to save the VPN connection information.
- Turn the VPN switch ON.
If you get an error when trying to connect, try this fix.
Once connected, you can verify that your traffic is being routed properly by looking up your IP address on Google. It should say «Your public IP address is Your VPN Server IP«.
Fedora and CentOS
Fedora 28 (and newer) and CentOS 8/7 users can connect using IPsec/XAuth mode.
Other Linux
First check here to see if the network-manager-l2tp and network-manager-l2tp-gnome packages are available for your Linux distribution. If yes, install them (select strongSwan) and follow the instructions above. Alternatively, you may configure Linux VPN clients using the command line.
Configure Linux VPN clients using the command line
Advanced users can configure Linux VPN clients using the command line. Alternatively, you may connect using IKEv2 mode (recommended), or configure using the GUI. Instructions below are inspired by the work of Peter Sanford. Commands must be run as root on your VPN client.
To set up the VPN client, first install the following packages:
# Ubuntu and Debian apt-get update apt-get install strongswan xl2tpd net-tools # Fedora yum install strongswan xl2tpd net-tools # CentOS yum install epel-release yum --enablerepo=epel install strongswan xl2tpd net-tools
Create VPN variables (replace with actual values):
VPN_SERVER_IP='your_vpn_server_ip' VPN_IPSEC_PSK='your_ipsec_pre_shared_key' VPN_USER='your_vpn_username' VPN_PASSWORD='your_vpn_password'
Configure strongSwan:
cat > /etc/ipsec.conf <<EOF # ipsec.conf - strongSwan IPsec configuration file conn myvpn auto=add keyexchange=ikev1 authby=secret type=transport left=%defaultroute leftprotoport=17/1701 rightprotoport=17/1701 right=$VPN_SERVER_IP ike=aes128-sha1-modp2048 esp=aes128-sha1 EOF cat > /etc/ipsec.secrets <<EOF : PSK "$VPN_IPSEC_PSK" EOF chmod 600 /etc/ipsec.secrets # For CentOS and Fedora ONLY mv /etc/strongswan/ipsec.conf /etc/strongswan/ipsec.conf.old 2>/dev/null mv /etc/strongswan/ipsec.secrets /etc/strongswan/ipsec.secrets.old 2>/dev/null ln -s /etc/ipsec.conf /etc/strongswan/ipsec.conf ln -s /etc/ipsec.secrets /etc/strongswan/ipsec.secrets
Configure xl2tpd:
cat > /etc/xl2tpd/xl2tpd.conf <<EOF [lac myvpn] lns = $VPN_SERVER_IP ppp debug = yes pppoptfile = /etc/ppp/options.l2tpd.client length bit = yes EOF cat > /etc/ppp/options.l2tpd.client <<EOF ipcp-accept-local ipcp-accept-remote refuse-eap require-chap noccp noauth mtu 1280 mru 1280 noipdefault defaultroute usepeerdns connect-delay 5000 name "$VPN_USER" password "$VPN_PASSWORD" EOF chmod 600 /etc/ppp/options.l2tpd.client
The VPN client setup is now complete. Follow the steps below to connect.
Note: You must repeat all steps below every time you try to connect to the VPN.
Create xl2tpd control file:
mkdir -p /var/run/xl2tpd touch /var/run/xl2tpd/l2tp-control
Restart services:
service strongswan restart
# For Ubuntu 20.04, if strongswan service not found
ipsec restart
service xl2tpd restart
Start the IPsec connection:
# Ubuntu and Debian ipsec up myvpn # CentOS and Fedora strongswan up myvpn
Start the L2TP connection:
echo "c myvpn" > /var/run/xl2tpd/l2tp-control
Run ifconfig and check the output. You should now see a new interface ppp0.
Check your existing default route:
Find this line in the output: default via X.X.X.X .... Write down this gateway IP for use in the two commands below.
Exclude your VPN server’s public IP from the new default route (replace with actual value):
route add YOUR_VPN_SERVER_PUBLIC_IP gw X.X.X.X
If your VPN client is a remote server, you must also exclude your Local PC’s public IP from the new default route, to prevent your SSH session from being disconnected (replace with actual value):
route add YOUR_LOCAL_PC_PUBLIC_IP gw X.X.X.X
Add a new default route to start routing traffic via the VPN server:
route add default dev ppp0
The VPN connection is now complete. Verify that your traffic is being routed properly:
wget -qO- http://ipv4.icanhazip.com; echo
The above command should return Your VPN Server IP.
To stop routing traffic via the VPN server:
route del default dev ppp0
To disconnect:
# Ubuntu and Debian echo "d myvpn" > /var/run/xl2tpd/l2tp-control ipsec down myvpn # CentOS and Fedora echo "d myvpn" > /var/run/xl2tpd/l2tp-control strongswan down myvpn
IKEv1 troubleshooting
Read this in other languages: English, 中文.
See also: IKEv2 troubleshooting and Advanced usage.
- Check logs and VPN status
- Windows error 809
- Windows error 789 or 691
- Windows error 628 or 766
- Windows 10 connecting
- Windows 10 upgrades
- Windows DNS leaks and IPv6
- Android MTU/MSS issues
- Android 6 and 7
- macOS send traffic over VPN
- iOS 13+ and macOS 10.15/11+
- iOS/Android sleep mode
- Debian 11/10 kernel
- Other errors
Check logs and VPN status
Commands below must be run as root (or using sudo).
First, restart services on the VPN server:
service ipsec restart service xl2tpd restart
Docker users: Run docker restart ipsec-vpn-server.
Then reboot your VPN client device, and retry the connection. If still unable to connect, try removing and recreating the VPN connection. Make sure that the VPN server address and VPN credentials are entered correctly.
For servers with an external firewall (e.g. EC2/GCE), open UDP ports 500 and 4500 for the VPN.
Check the Libreswan (IPsec) and xl2tpd logs for errors:
# Ubuntu & Debian grep pluto /var/log/auth.log grep xl2tpd /var/log/syslog # CentOS/RHEL, Rocky Linux, AlmaLinux, Oracle Linux & Amazon Linux 2 grep pluto /var/log/secure grep xl2tpd /var/log/messages # Alpine Linux grep pluto /var/log/messages grep xl2tpd /var/log/messages
Check the status of the IPsec VPN server:
Show currently established VPN connections:
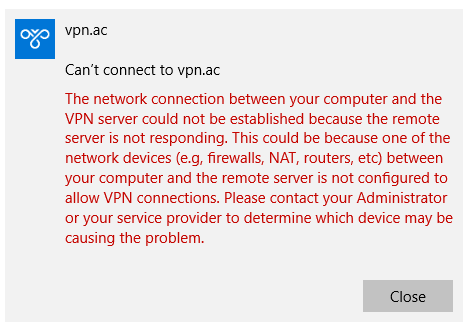
Windows error 809
Error 809: The network connection between your computer and the VPN server could not be established because the remote server is not responding. This could be because one of the network devices (e.g, firewalls, NAT, routers, etc) between your computer and the remote server is not configured to allow VPN connections. Please contact your Administrator or your service provider to determine which device may be causing the problem.
Note: The registry change below is only required if you use IPsec/L2TP mode to connect to the VPN. It is NOT required for the IKEv2 and IPsec/XAuth modes.
To fix this error, a one-time registry change is required because the VPN server and/or client is behind NAT (e.g. home router). Download and import the .reg file below, or run the following from an elevated command prompt. You must reboot your PC when finished.
-
For Windows Vista, 7, 8, 10 and 11 (download .reg file)
REG ADD HKLMSYSTEMCurrentControlSetServicesPolicyAgent /v AssumeUDPEncapsulationContextOnSendRule /t REG_DWORD /d 0x2 /f -
For Windows XP ONLY (download .reg file)
REG ADD HKLMSYSTEMCurrentControlSetServicesIPSec /v AssumeUDPEncapsulationContextOnSendRule /t REG_DWORD /d 0x2 /f
Although uncommon, some Windows systems disable IPsec encryption, causing the connection to fail. To re-enable it, run the following command and reboot your PC.
-
For Windows XP, Vista, 7, 8, 10 and 11 (download .reg file)
REG ADD HKLMSYSTEMCurrentControlSetServicesRasManParameters /v ProhibitIpSec /t REG_DWORD /d 0x0 /f
Windows error 789 or 691
Error 789: The L2TP connection attempt failed because the security layer encountered a processing error during initial negotiations with the remote computer.
Error 691: The remote connection was denied because the user name and password combination you provided is not recognized, or the selected authentication protocol is not permitted on the remote access server.
For error 789, click here for troubleshooting information. For error 691, you may try removing and recreating the VPN connection, by following the instructions in this document. Make sure that the VPN credentials are entered correctly.
Windows error 628 or 766
Error 628: The connection was terminated by the remote computer before it could be completed.
Error 766: A certificate could not be found. Connections that use the L2TP protocol over IPSec require the installation of a machine certificate, also known as a computer certificate.
To fix these errors, please follow these steps:
- Right-click on the wireless/network icon in your system tray.
- Select Open Network and Sharing Center. Or, if using Windows 10 version 1709 or newer, select Open Network & Internet settings, then on the page that opens, click Network and Sharing Center.
- On the left, click Change adapter settings. Right-click on the new VPN and choose Properties.
- Click the Security tab. Select «Layer 2 Tunneling Protocol with IPsec (L2TP/IPSec)» for Type of VPN.
- Click Allow these protocols. Check the «Challenge Handshake Authentication Protocol (CHAP)» and «Microsoft CHAP Version 2 (MS-CHAP v2)» checkboxes.
- Click the Advanced settings button.
- Select Use preshared key for authentication and enter
Your VPN IPsec PSKfor the Key. - Click OK to close the Advanced settings.
- Click OK to save the VPN connection details.
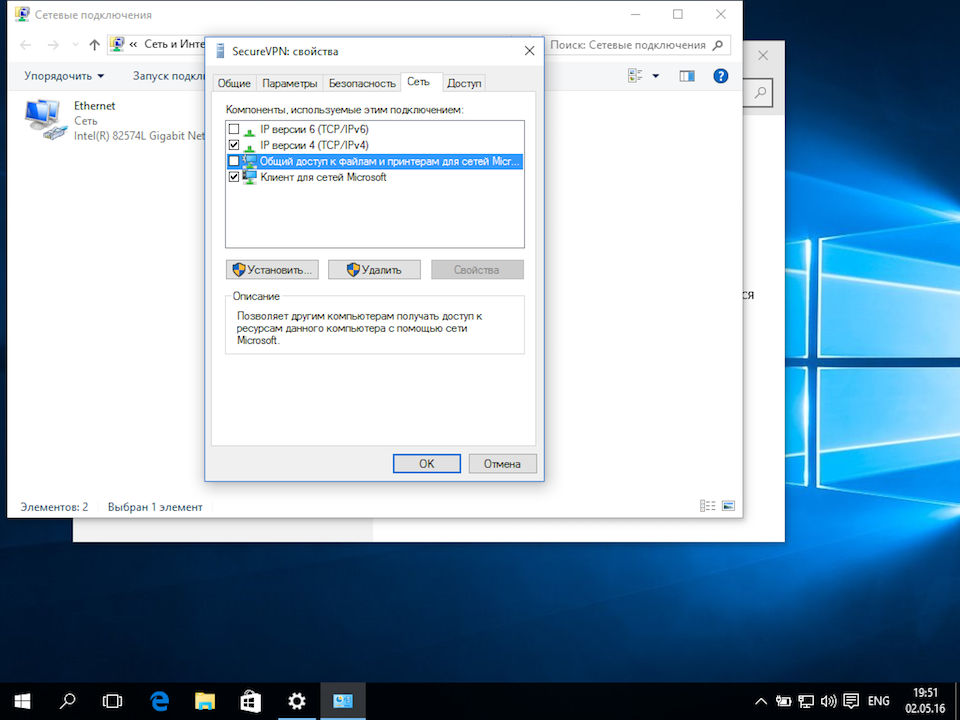
For reference, see this screenshot of the VPN connection properties dialog.
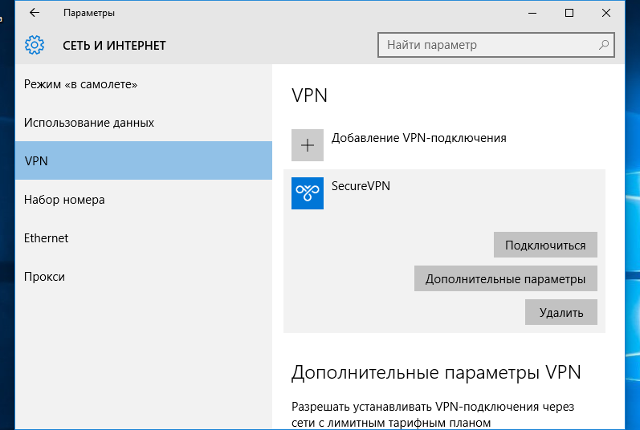
Windows 10 connecting
If using Windows 10 and the VPN is stuck on «connecting» for more than a few minutes, try these steps:
- Right-click on the wireless/network icon in your system tray.
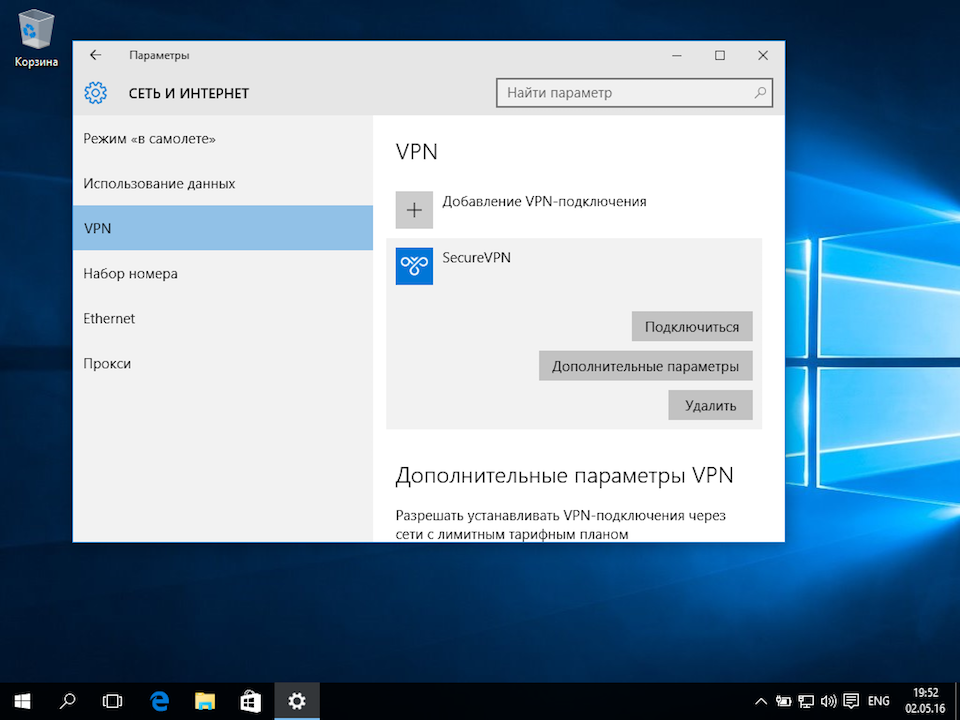
- Select Open Network & Internet settings, then on the page that opens, click VPN on the left.
- Select the new VPN entry, then click Connect. If prompted, enter
Your VPN UsernameandPassword, then click OK.
Windows 10 upgrades
After upgrading Windows 10 version (e.g. from 1709 to 1803), you may need to re-apply the fix above for Windows Error 809 and reboot.
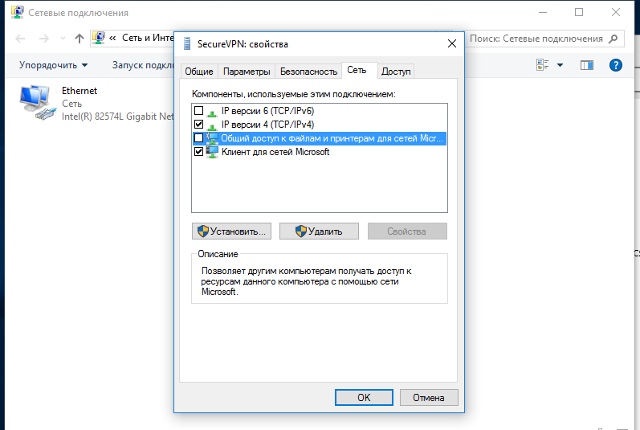
Windows DNS leaks and IPv6
Windows 8, 10 and 11 use «smart multi-homed name resolution» by default, which may cause «DNS leaks» when using the native IPsec VPN client if your DNS servers on the Internet adapter are from the local network segment. To fix, you may either disable smart multi-homed name resolution, or configure your Internet adapter to use DNS servers outside your local network (e.g. 8.8.8.8 and 8.8.4.4). When finished, clear the DNS cache and reboot your PC.
In addition, if your computer has IPv6 enabled, all IPv6 traffic (including DNS queries) will bypass the VPN. Learn how to disable IPv6 in Windows. If you need a VPN with IPv6 support, you could instead try OpenVPN.
Android MTU/MSS issues
Some Android devices have MTU/MSS issues, that they are able to connect to the VPN using IPsec/XAuth («Cisco IPsec») mode, but cannot open websites. If you encounter this problem, try running the following commands on the VPN server. If successful, you may add these commands to /etc/rc.local to persist after reboot.
iptables -t mangle -A FORWARD -m policy --pol ipsec --dir in
-p tcp -m tcp --tcp-flags SYN,RST SYN -m tcpmss --mss 1361:1536
-j TCPMSS --set-mss 1360
iptables -t mangle -A FORWARD -m policy --pol ipsec --dir out
-p tcp -m tcp --tcp-flags SYN,RST SYN -m tcpmss --mss 1361:1536
-j TCPMSS --set-mss 1360
echo 1 > /proc/sys/net/ipv4/ip_no_pmtu_disc
Docker users: Instead of running the commands above, you may apply this fix by adding VPN_ANDROID_MTU_FIX=yes to your env file, then re-create the Docker container.
Reference: [1].
Android 6 and 7
If your Android 6.x or 7.x device cannot connect, try these steps:
- Tap the «Settings» icon next to your VPN profile. Select «Show advanced options» and scroll down to the bottom. If the option «Backward compatible mode» exists (see screenshot), enable it and reconnect the VPN. If not, try the next step.
- Edit
/etc/ipsec.confon the VPN server. Find the linesha2-truncbugand toggle its value. i.e. Replacesha2-truncbug=nowithsha2-truncbug=yes, or replacesha2-truncbug=yeswithsha2-truncbug=no. Save the file and runservice ipsec restart. Then reconnect the VPN.
Docker users: You may set sha2-truncbug=yes (default is no) in /etc/ipsec.conf by adding VPN_SHA2_TRUNCBUG=yes to your env file, then re-create the Docker container.
macOS send traffic over VPN
OS X (macOS) users: If you can successfully connect using IPsec/L2TP mode, but your public IP does not show Your VPN Server IP, read the OS X section above and complete these steps. Save VPN configuration and re-connect.
- Click the Advanced button and make sure the Send all traffic over VPN connection checkbox is checked.
- Click the TCP/IP tab, and make sure Link-local only is selected in the Configure IPv6 section.
After trying the steps above, if your computer is still not sending traffic over the VPN, check the service order. From the main network preferences screen, select «set service order» in the cog drop down under the list of connections. Drag the VPN connection to the top.
iOS 13+ and macOS 10.15/11+
If your device running iOS 13+, macOS 10.15 (Catalina), macOS 11 (Big Sur) or above cannot connect, try these steps: Edit /etc/ipsec.conf on the VPN server. Find sha2-truncbug=yes and replace it with sha2-truncbug=no. Save the file and run service ipsec restart. Then reconnect the VPN.
In addition, users running macOS Big Sur 11.0 should update to version 11.1 or newer, to fix some issues with VPN connections. To check your macOS version and update, refer to this article.
iOS/Android sleep mode
To save battery, iOS devices (iPhone/iPad) will automatically disconnect Wi-Fi shortly after the screen turns off (sleep mode). As a result, the IPsec VPN disconnects. This behavior is by design and cannot be configured.
If you need the VPN to auto-reconnect when the device wakes up, you may connect using IKEv2 mode (recommended) and enable the «VPN On Demand» feature. Alternatively, you may try OpenVPN instead, which has support for options such as «Reconnect on Wakeup» and «Seamless Tunnel».
Android devices will also disconnect Wi-Fi shortly after entering sleep mode, unless the option «Keep Wi-Fi on during sleep» is enabled. This option is no longer available in Android 8 (Oreo) and newer. Alternatively, you may try enabling the «Always-on VPN» option to stay connected. Learn more here.
Debian 11/10 kernel
Debian 11 or 10 users: Run uname -r to check your server’s Linux kernel version. If it contains the word «cloud», and /dev/ppp is missing, then the kernel lacks ppp support and cannot use IPsec/L2TP mode. The VPN setup scripts try to detect this and show a warning. In this case, you may instead use IKEv2 or IPsec/XAuth mode to connect to the VPN.
To fix the issue with IPsec/L2TP mode, you may switch to the standard Linux kernel by installing e.g. the linux-image-amd64 package. Then update the default kernel in GRUB and reboot your server.
Other errors
If you encounter other errors, refer to the links below:
- http://www.tp-link.com/en/faq-1029.html
- https://documentation.meraki.com/MX-Z/Client_VPN/Troubleshooting_Client_VPN#Common_Connection_Issues
- https://stackoverflow.com/questions/25245854/windows-8-1-gets-error-720-on-connect-vpn
License
Note: This license applies to this document only.
Copyright (C) 2016-2023 Lin Song
Inspired by the work of Joshua Lund
This program is free software: you can redistribute it and/or modify it under the terms of the GNU General Public License as published by the Free Software Foundation, either version 3 of the License, or (at your option) any later version.
This program is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the GNU General Public License for more details.
L2TP/IPsec is a popular VPN protocol built-in to most modern platforms including Microsoft Windows 10. Using a built-in protocol can be a good choice as you do not have to install any extra applications or worry if they are written securely and bug free. Depending on your provider’s software they can be a little trickier to set up as you need to manually enter in your VPN configuration.
The following tutorial with plenty of screenshots will show you how to set up a L2TP/IPsec VPN on Windows 10 using the built-in capabilities of the operating system.
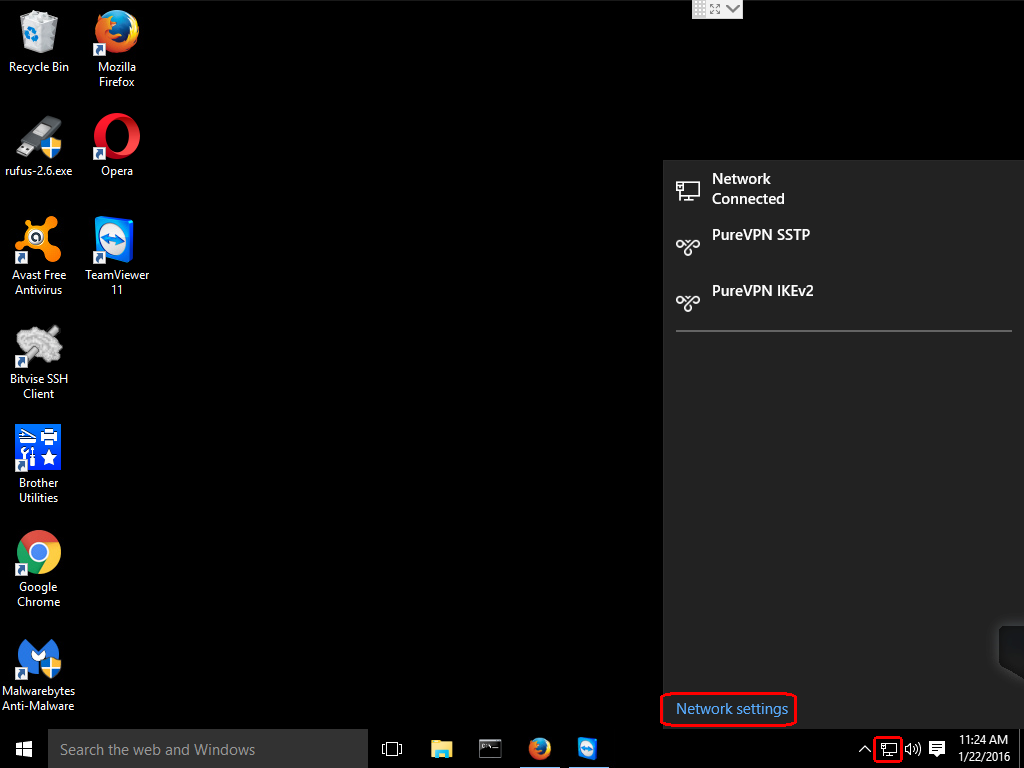
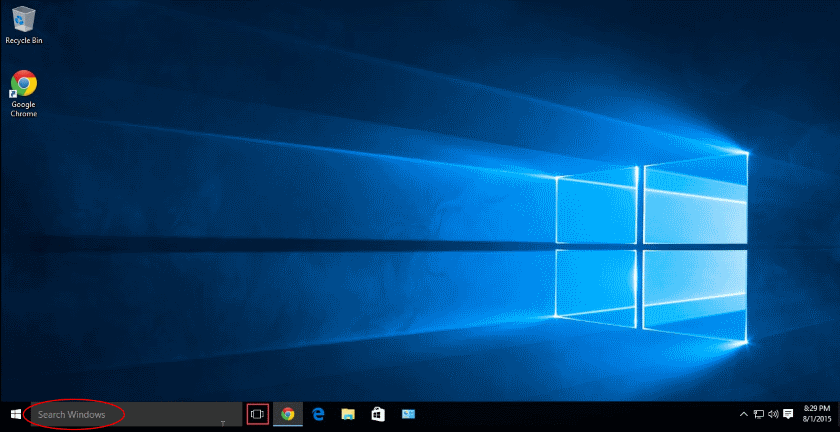
Step 1: Open Network settings
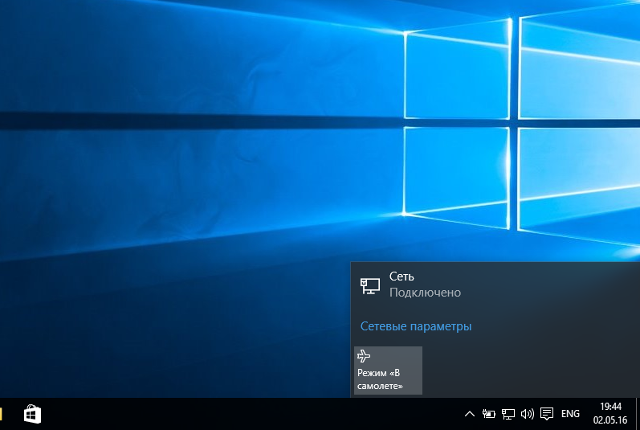
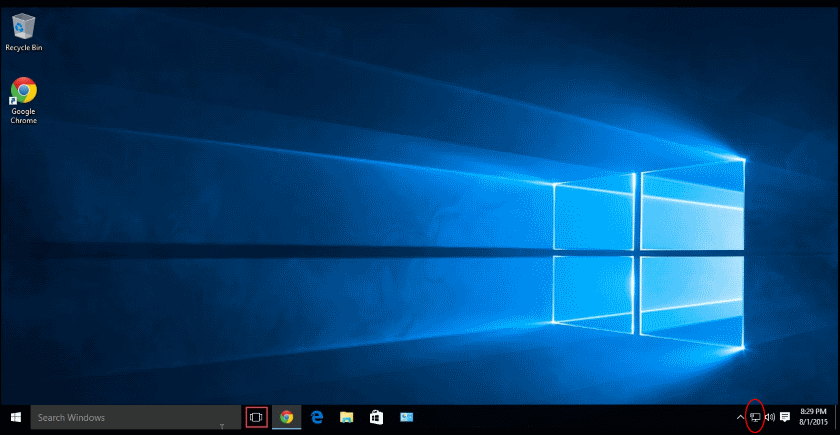
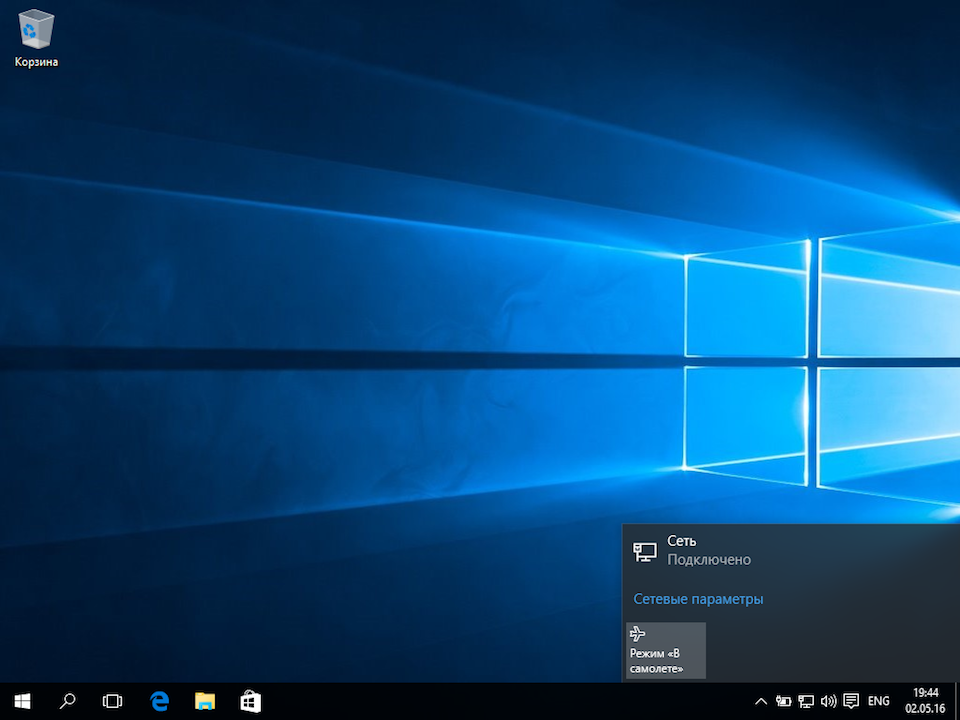
Click on the Network icon on the taskbar and then click on Network settings.
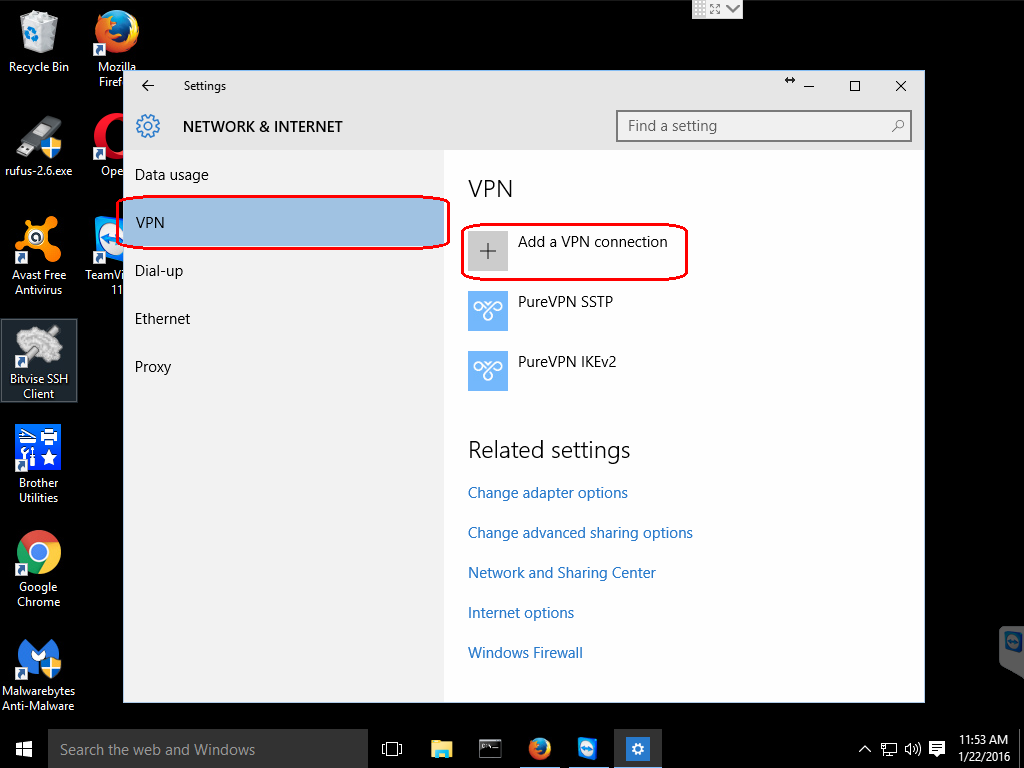
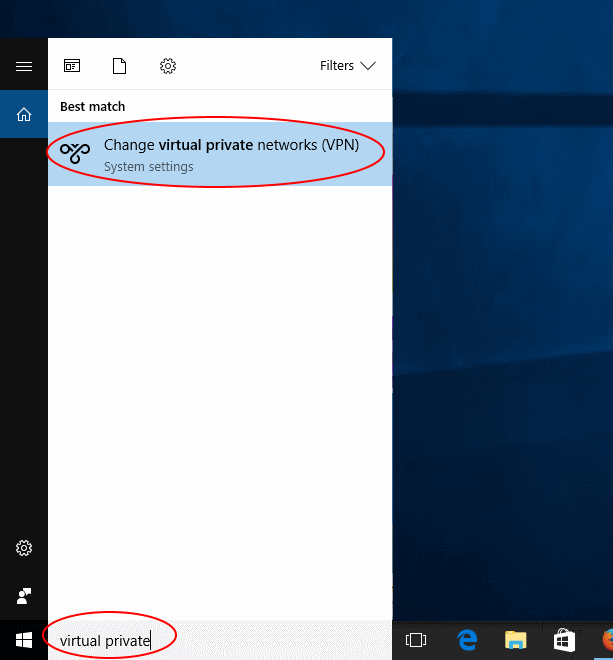
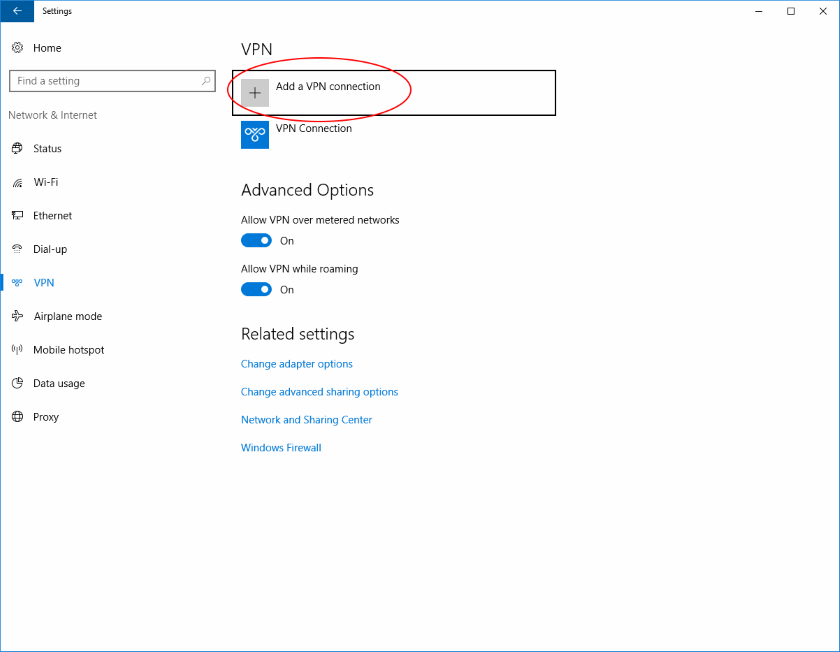
Step 2: Add a VPN connection
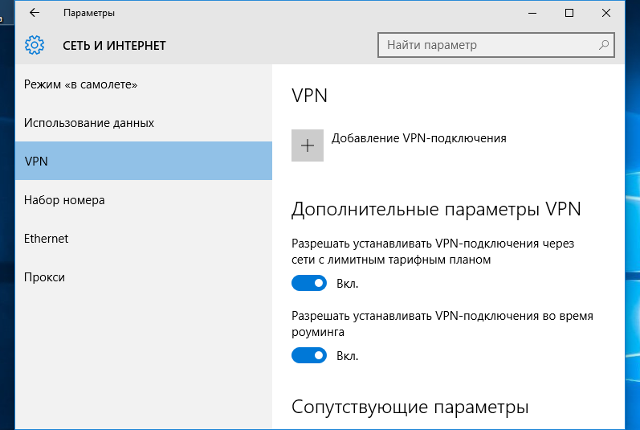
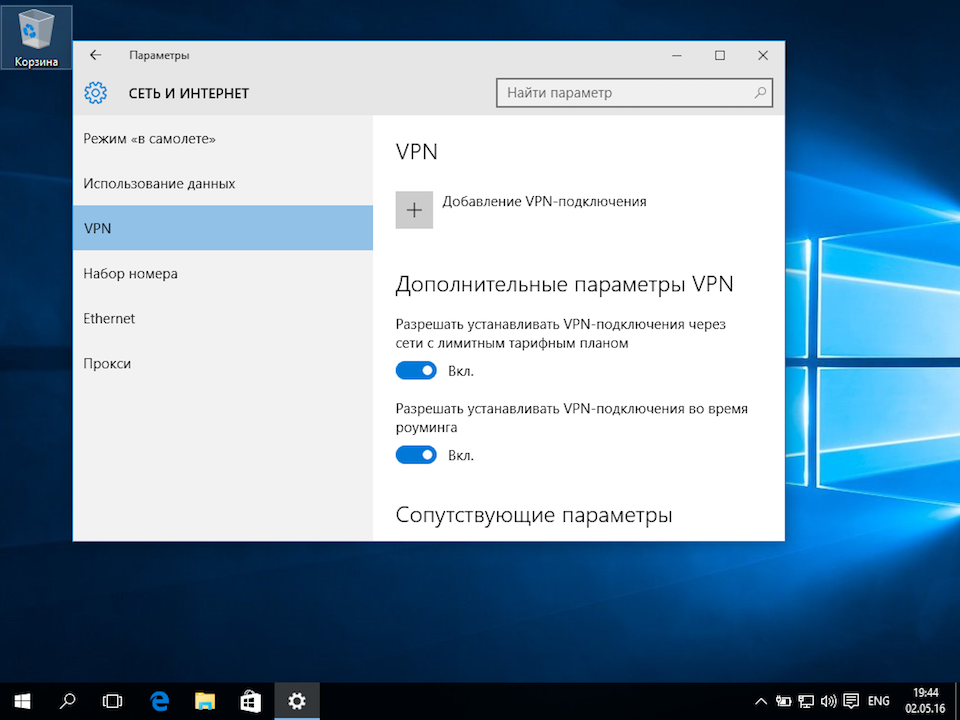
Click on the VPN option and then click on the Add a VPN connection.
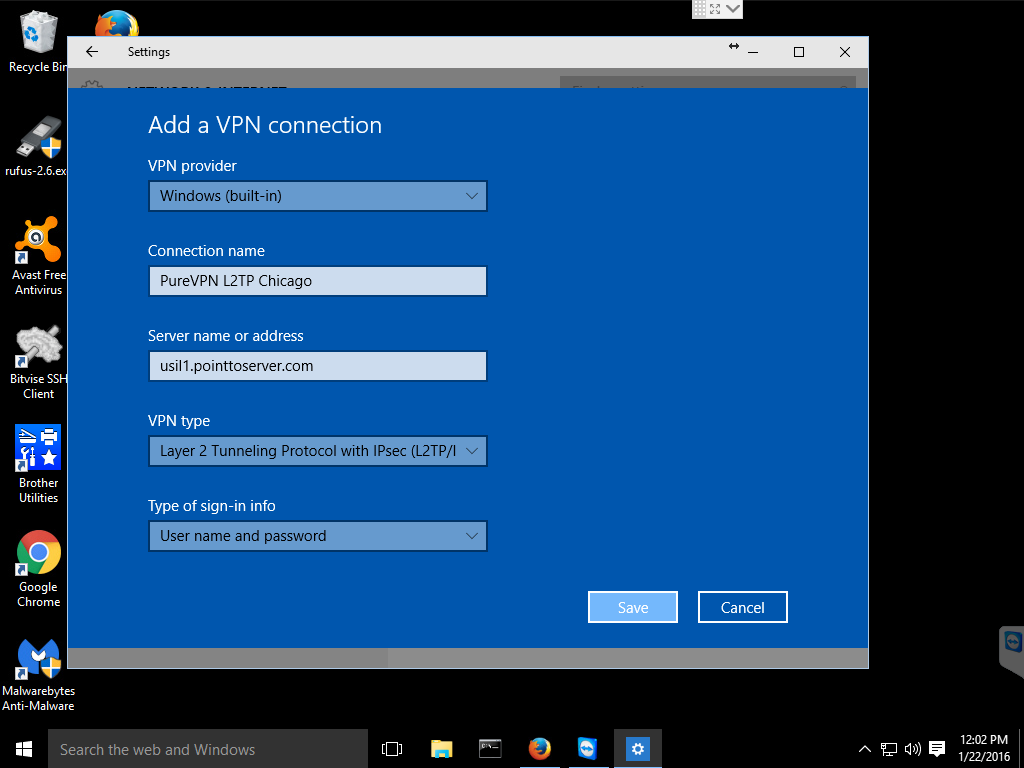
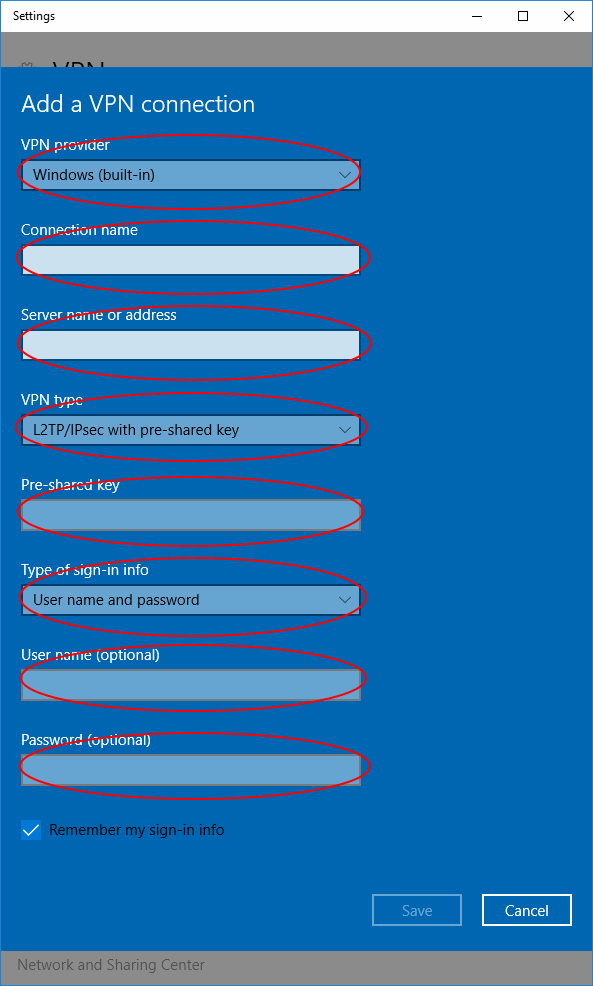
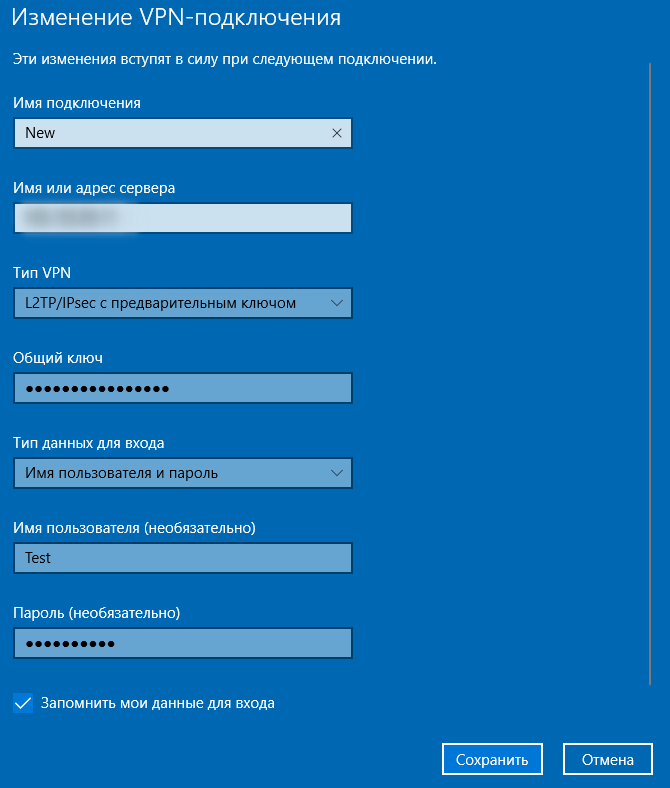
Step 3: Configure VPN connection
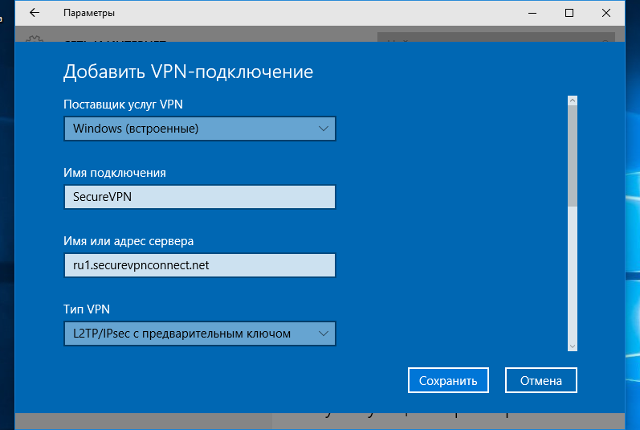
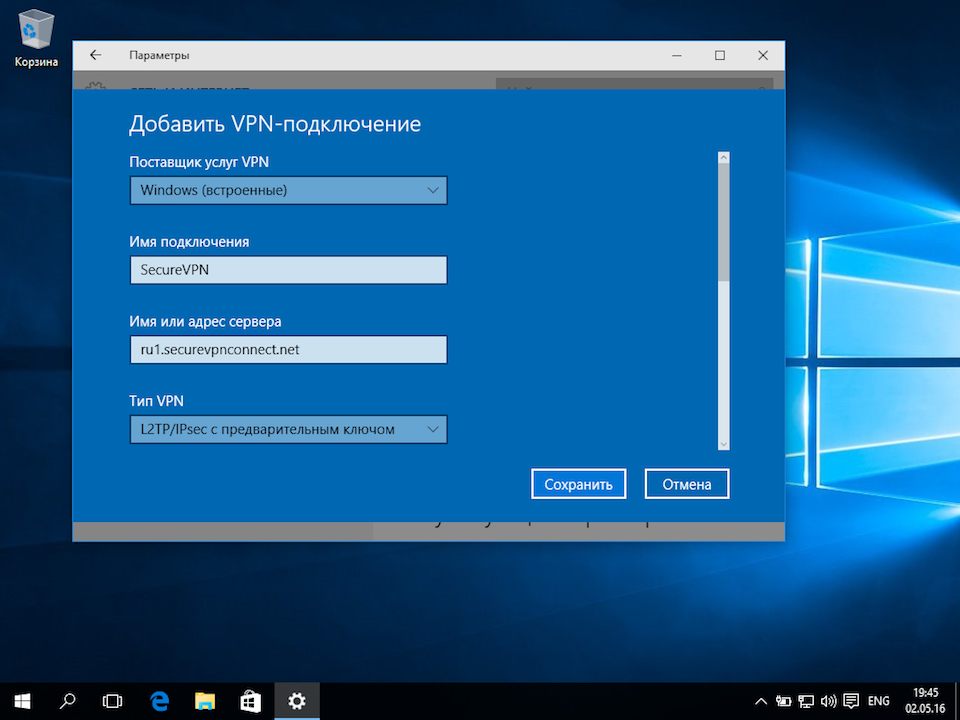
- Left-click the VPN provider drop down menu and select Windows (built-in).
- Click on the Connection name box and enter a name for your connection.
- Click the Server name or address box and enter a FQDN or IP address for your VPN server. Your VPN provider should have a list of their servers available on their website.
- Click the VPN type drop down menu and select Layer 2 Tunneling Protocol with IPsec (L2TP/IPsec).
- Click the Type of sign-in info drop down menu and select User name and password.
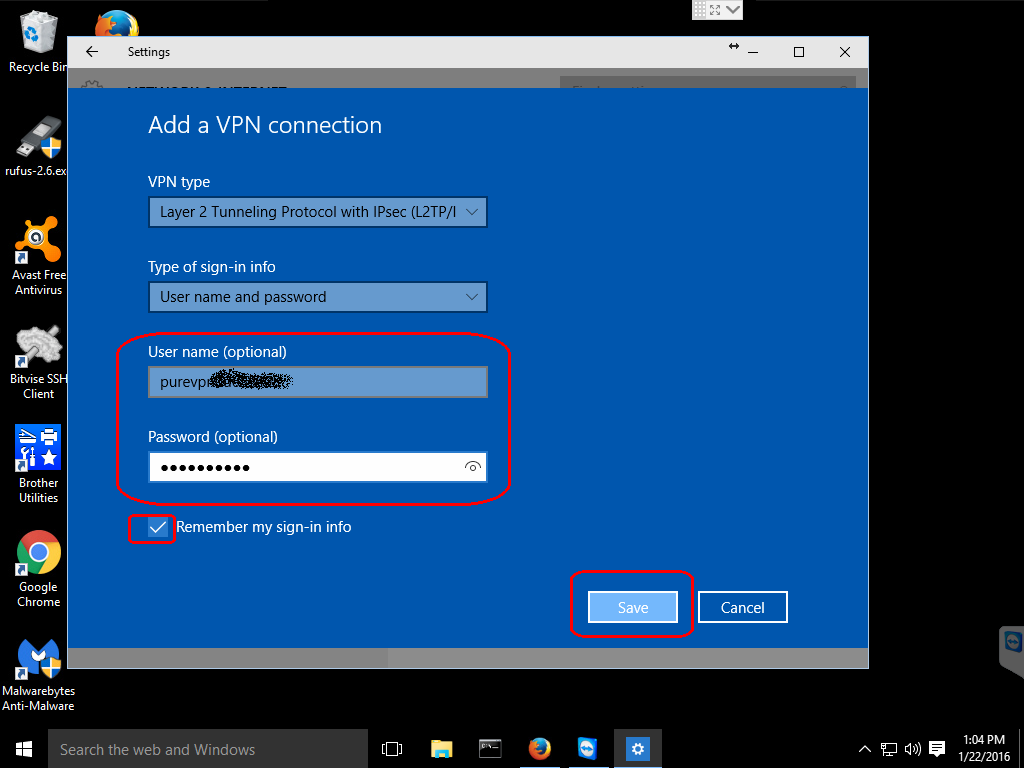
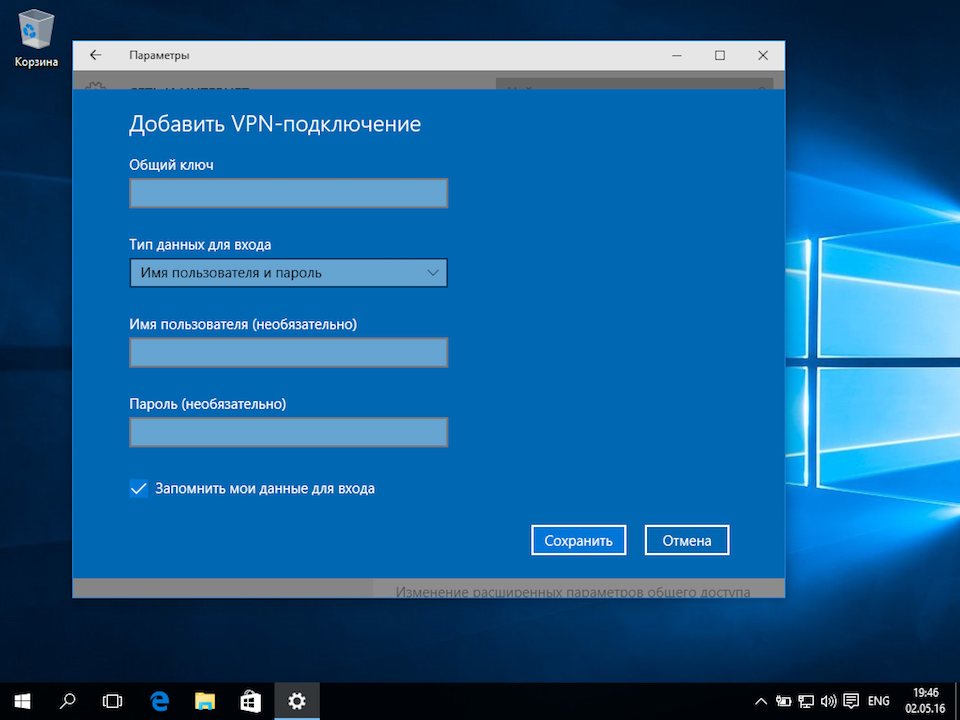
Step 4: Enter username and password (optional)
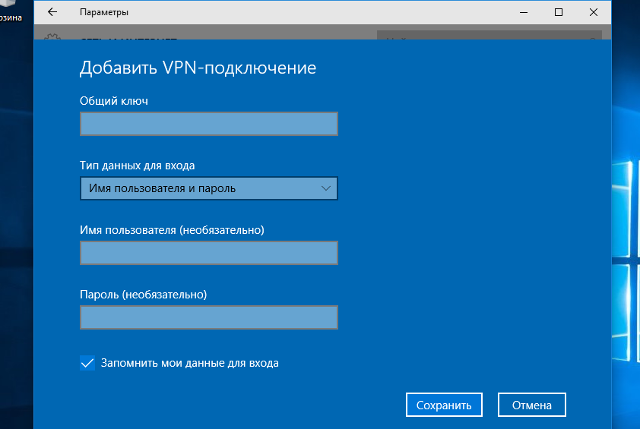
You may need to scroll down in the VPN configuration window to see the rest of the options, depending on the size of your Settings window.
If you desire, you can enter your VPN username and password in the appropriate fields and check the Remember my sign-in info and then you will not be asked for this information every time you activate your VPN connection.
When you are done entering all your information, click on the Save button to save your new VPN connection.
Step 5: Configure advanced settings
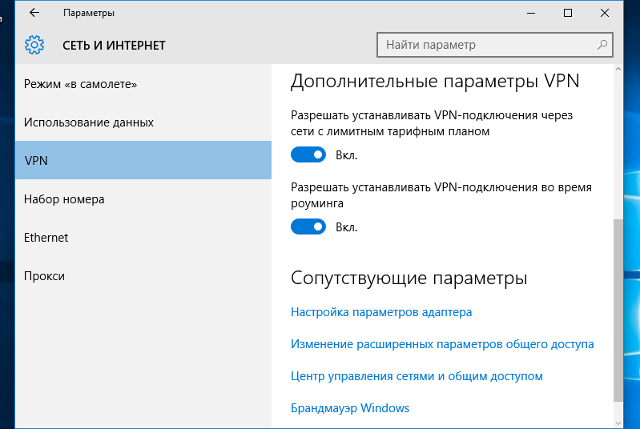
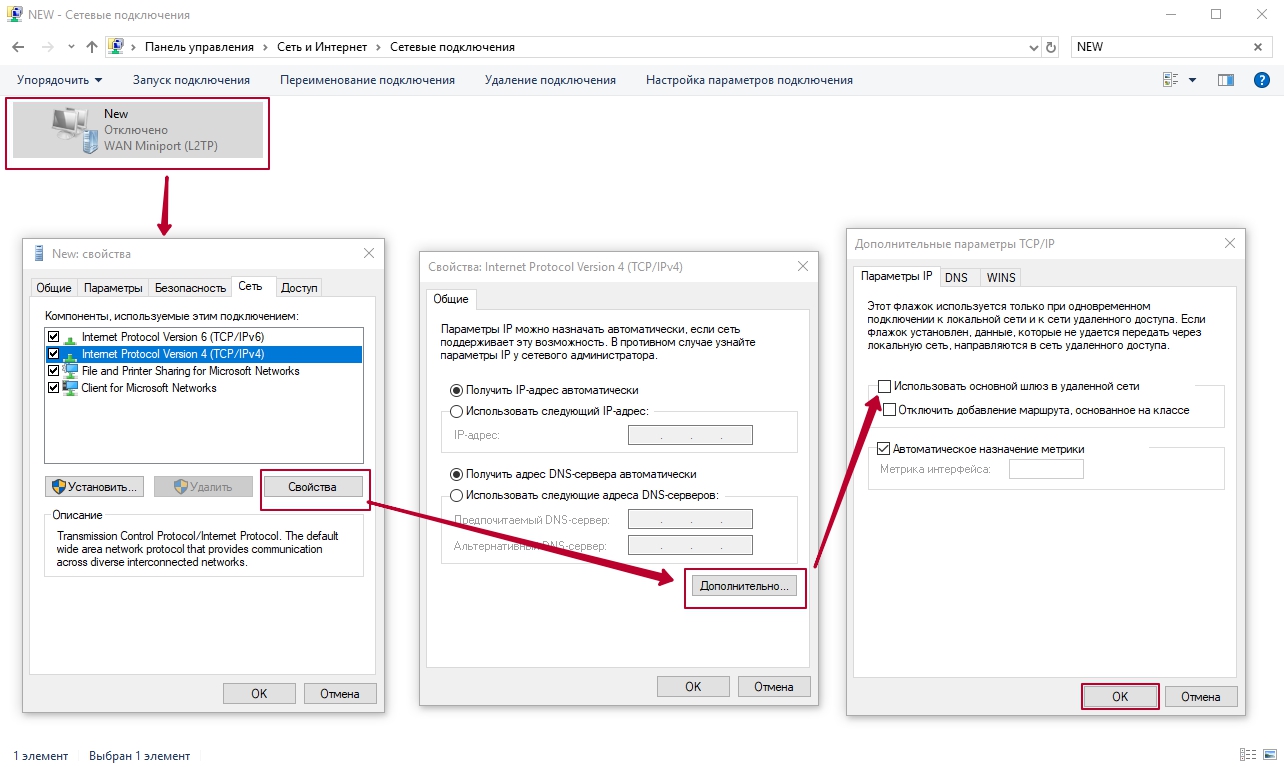
Under Related settings click on the Change adapter options choice.
This will open a new window titled Network Connections. Right-click on your newly created connection and this will bring up another menu. Click on the Properties option in this menu.
This will open a Properties window for the connection. Select the Security tab in this window.
Under the Data encryption: drop-down menu select Require encryption (disconnect if server declines).
Check the Allow these protocols radio button and ensure that only the Microsoft CHAP Version 2 (MS-CHAP v2) is checked.
There might be cases such as geo-unblocking streaming services where you might not want your connection encrypted. But you would probably be better served by using Smart DNS or some other proxy service for this.
MS-CHAP v2 is the only protocol that is still considered secure.
There is still one more setting that you will need to set for most providers. Stay on the Security tab and click the Advanced settings button.
Once you have the advanced settings open, click on the Use preshared key for authentication radio button and enter the key provided by your VPN provider.
Most providers utilize a preshared key for authentication and this should be provided on their website, possibly in the client area or in the tutorials section.
Click the OK button on the Advanced properties. Then click the OK button on the Security tab.
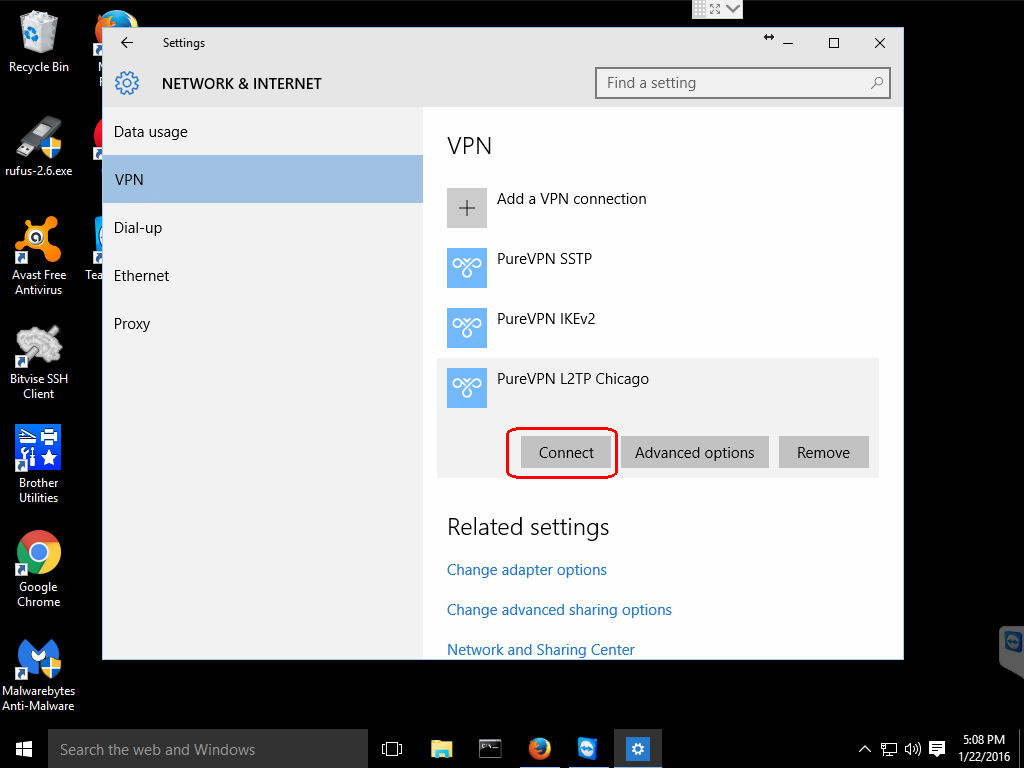
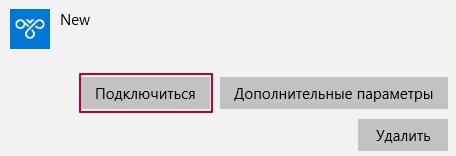
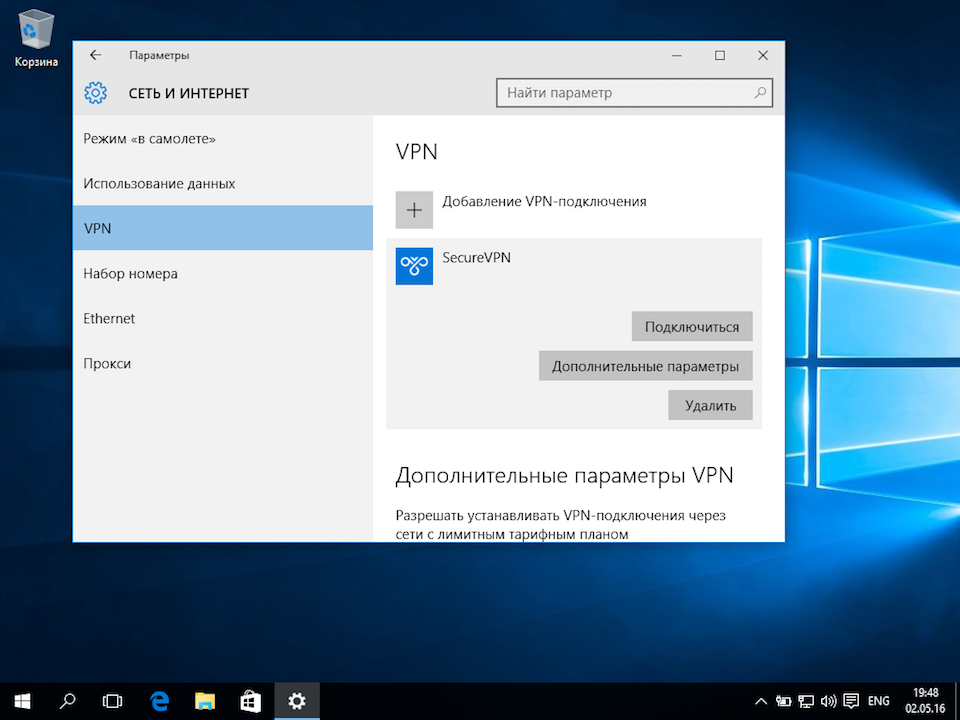
Step 6: Connect to newly configured VPN
If you like, you can close any of the windows that you still have open from configuring your new VPN connection.
Click on the network icon on the taskbar and this will bring up a list of your configured connections.
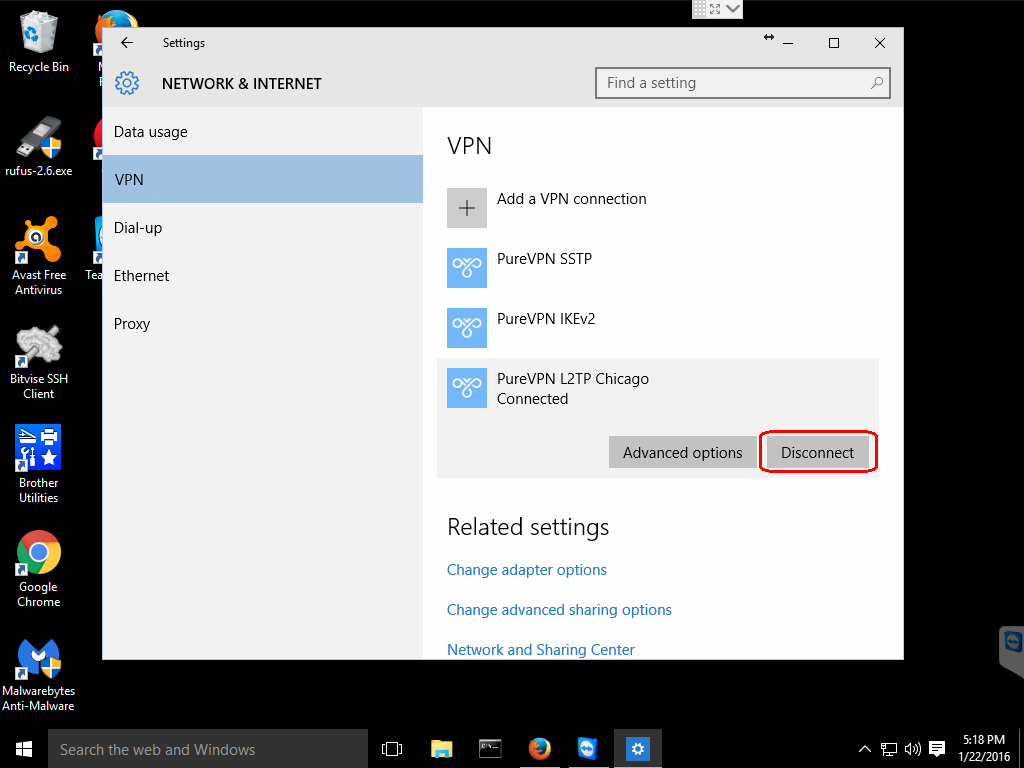
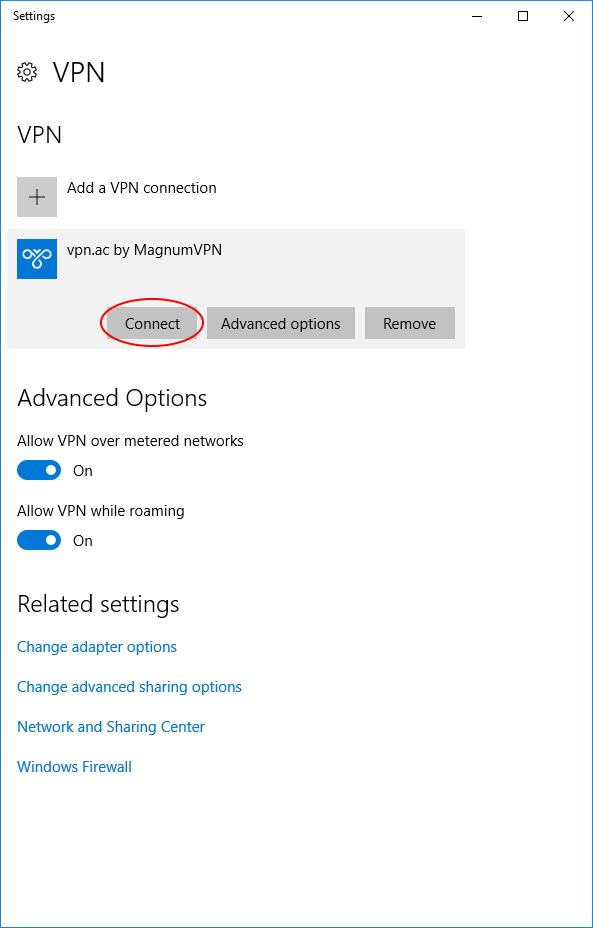
Then, click on the name you gave your new configuration and this will bring up the NETWORK & INTERNET settings screen.
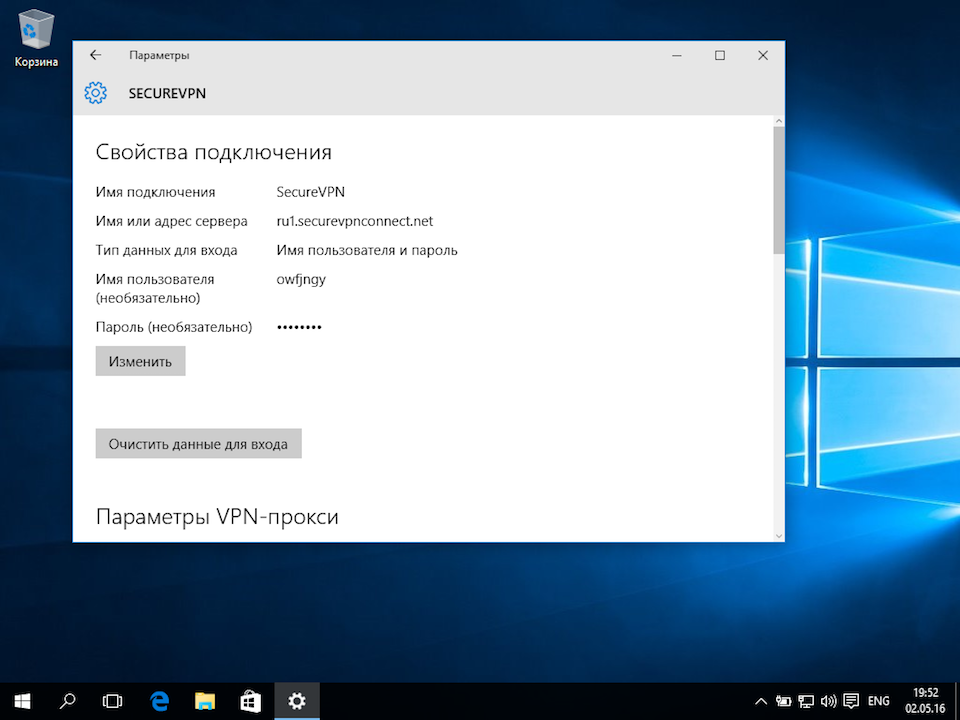
After that, click the name of your new configuration and this will reveal three buttons. Click the Connect button.
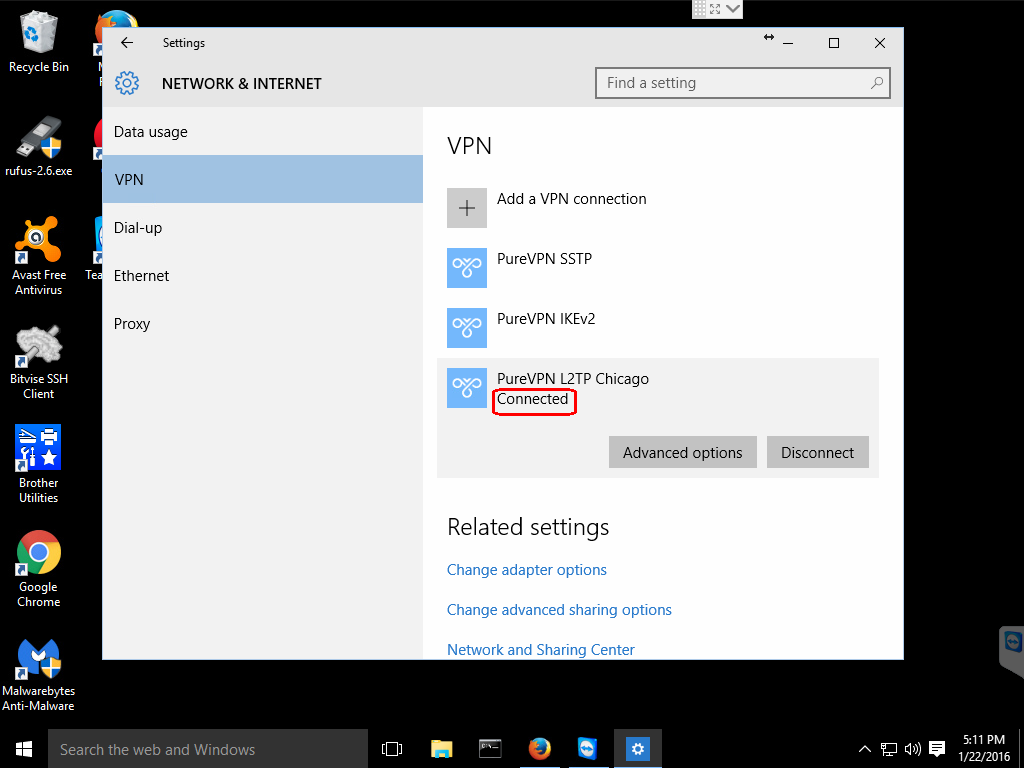
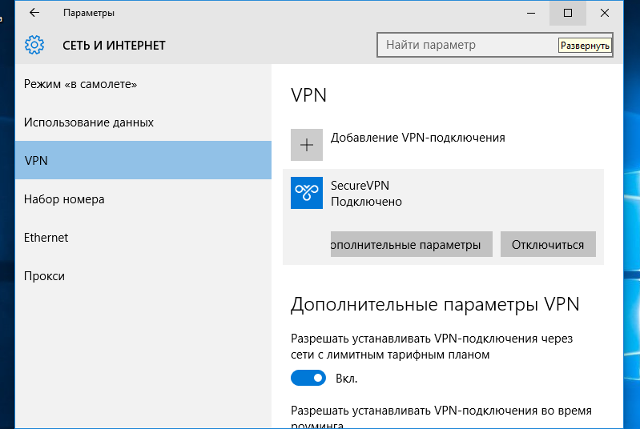
Once you click the Connect button, you will see the Windows 10 spinner and some informative messages and then it should say Connected, if all went well.
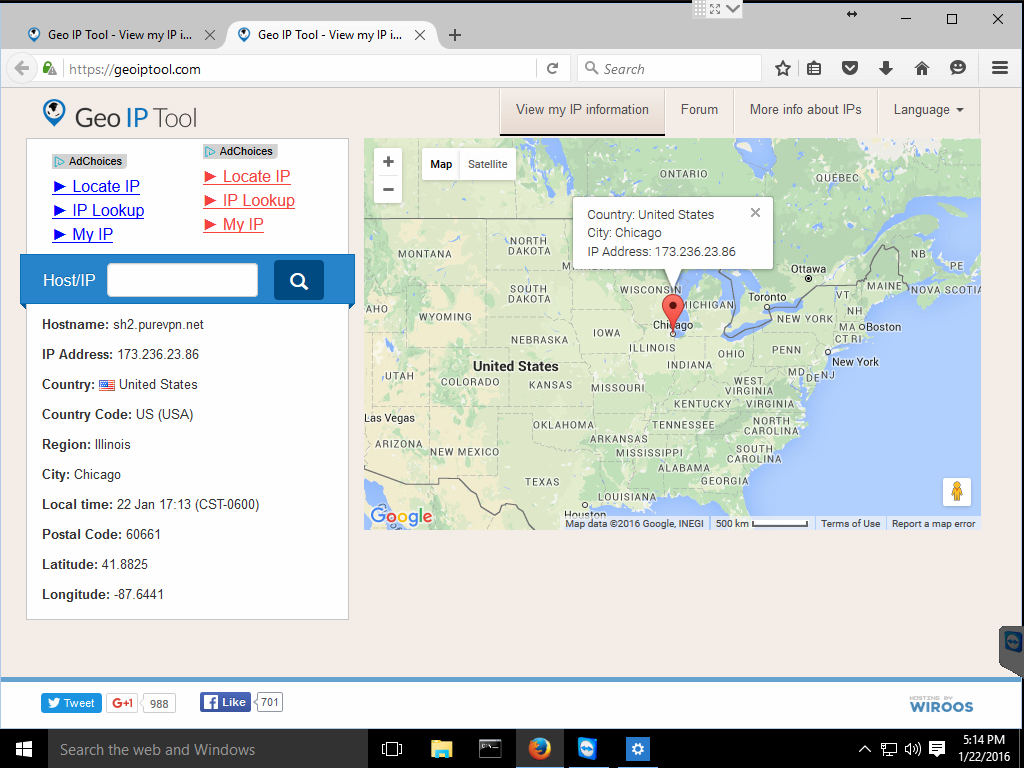
It is a good idea to use a tool to check what your IP is, it should now be reported as your VPN server;
And that is it! I now appear to be coming from the VPN server located in Chicago.
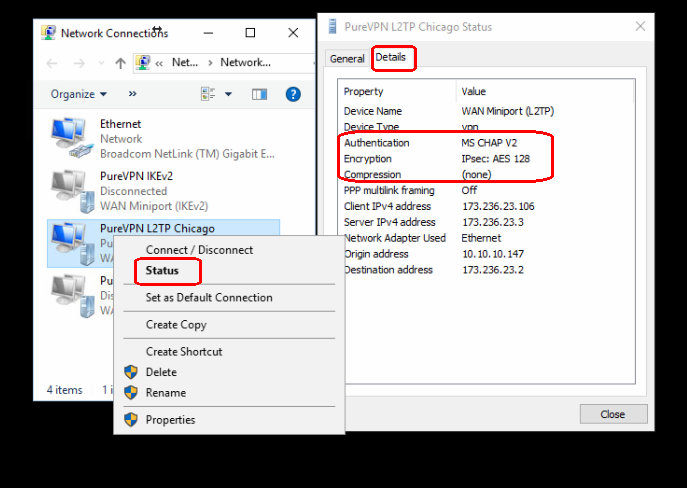
You can also check the network properties to get some information on your connection. Open the NETWORK & INTERNET window again by clicking on the network icon in the taskbar and selecting Network settings.
In the NETWORK & INTERNET window under Related settings select Change adapter options and this will bring up the Network Connections window. Right-click on the icon with the name of your VPN and select Status from that menu.
The General tab has some basic information but if you click on the Details tab you are provided with information about your VPN connection such as the cipher being used.
When you wish to disconnect from the VPN, you can click on the network icon and select your VPN connection profile which will bring up the NETWORK & INTERNET setting window again and click the Disconnect button.
That is all there is to setting up a L2TP/IPsec VPN using the built-in Microsoft Windows 10 functionality. I hope you found this tutorial to be useful and are enjoying your new VPN connection.
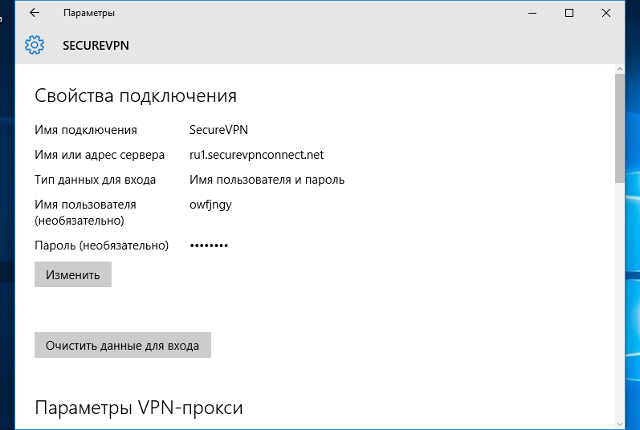
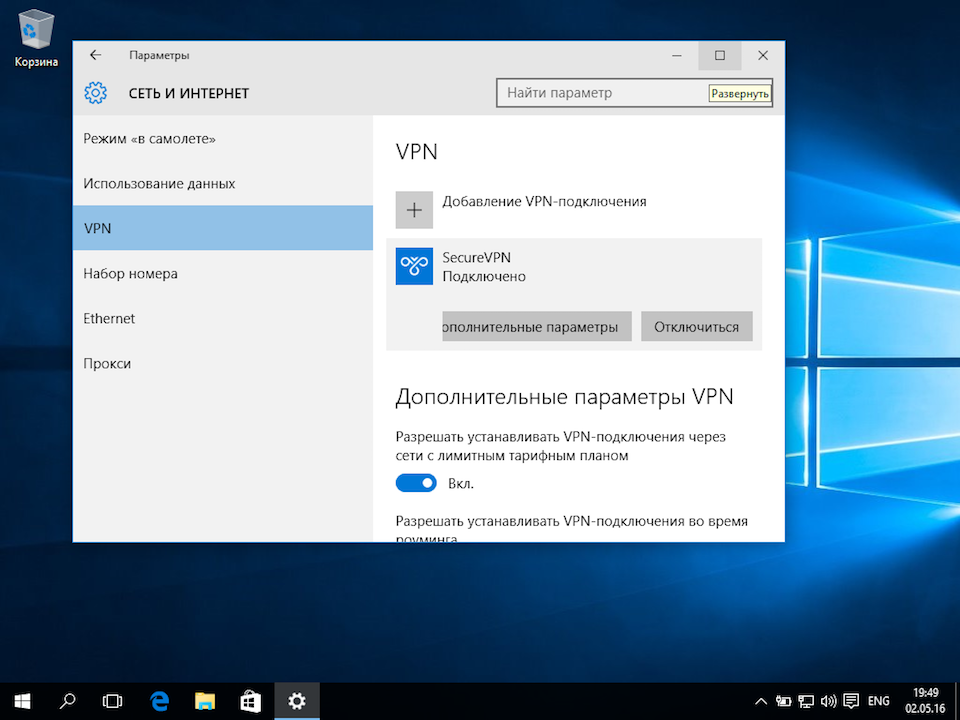
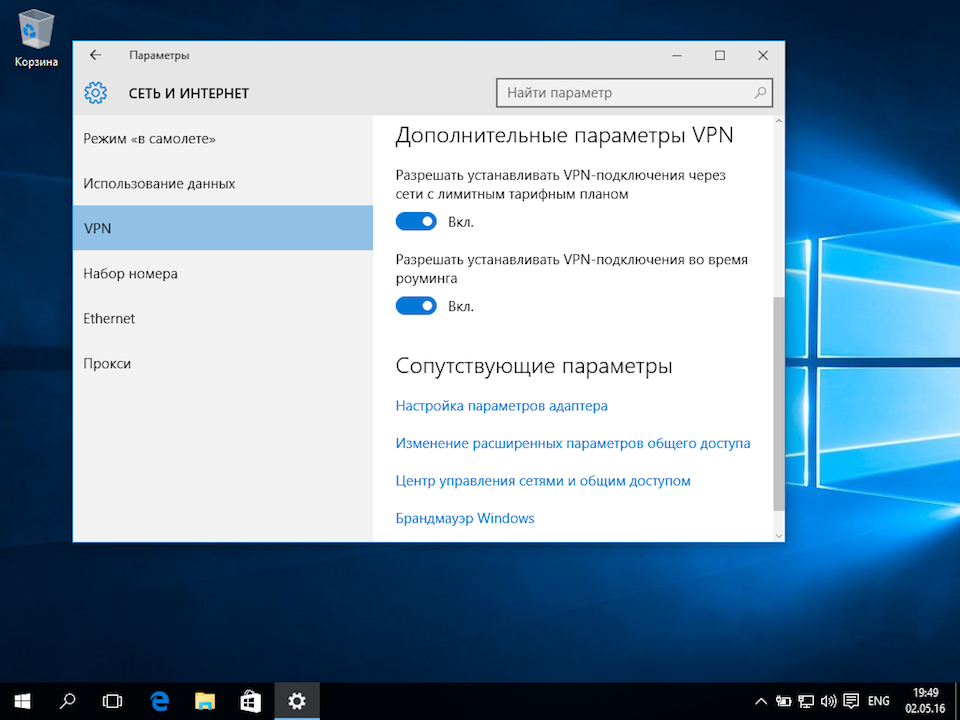
В операционной системе Windows 10 настроить VPN-подключение по протоколу L2TP не составит большого труда — достаточно выполнить все действия, как показано на картинках, и уже через минуту вы сможете анонимно посещать любые сайты, обойти блокировку Вконтакте, безопасно использовать бесплатный Wi-Fi.
1
Кликнуть на иконке сетевого подключения в системном трее, и в появившемся окне выбрать Сетевые параметры.
Далее
4
Указать идентификационные данные:
- Общий ключ — a-secure-psk
- Тип данных для входа — Имя пользователя и пароль
- Имя пользователя — username
- Пароль — password
Для завершения настройки нажать Сохранить.
Важное замечание: имя пользователя и пароль находятся в файле readme.txt, отправленном на Вашу почту после заказа подписки.
Далее
a-secure-psk
username
password
5
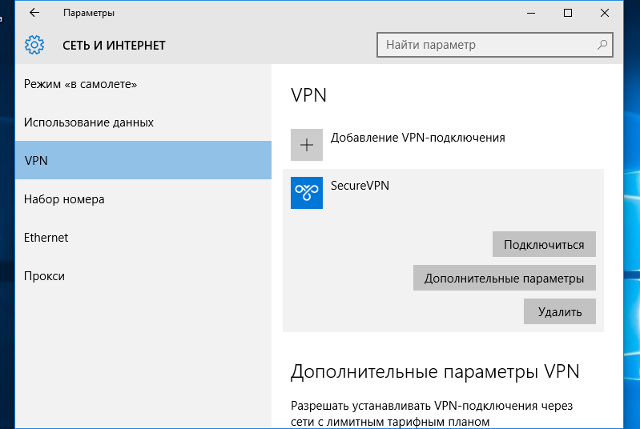
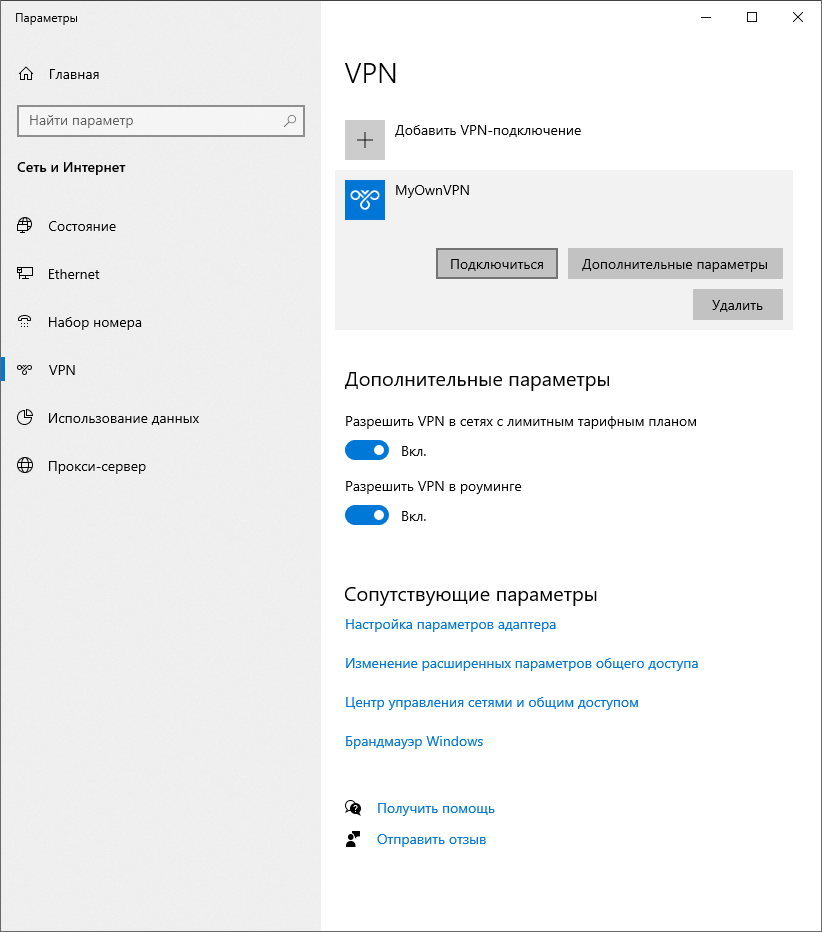
Для подключения выбрать только что созданное соединение, и нажать кнопку Подключиться.
Далее
6
Соединение будет установлено через некоторое время. Для отключения нажать Отключиться.
Далее
8
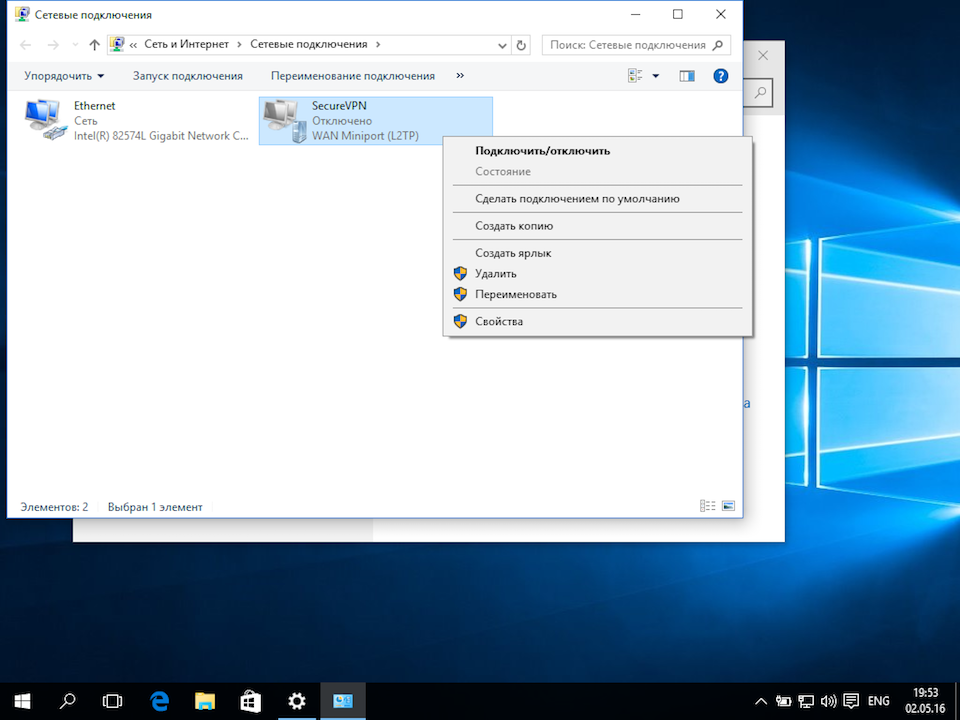
В открывшемся окне Сетевые подключения кликнуть правой кнопкой на созданном подключении, и выбрать Свойства.
Далее
This guide will show you how to get up and running with VPN on Windows 10 using the L2TP/IPSec protocol. For more about the L2TP/IPsec technology you can read this L2TP over IPSec VPNs technet article.
L2TP is a great option for creating a VPN because most operating systems support it automatically, which means you don’t need to install anything. The only downside is that some firewalls and networks might block this protocol. Rest easy, we have a guide to help you configure your windows firewall to allow it.
Steps for Setup VPN on Windows 10 using L2TP/IPSec
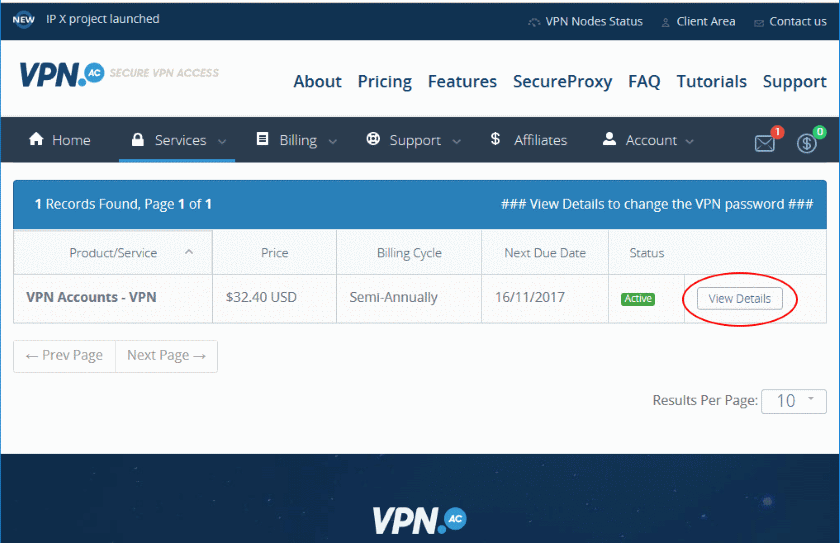
-
Purchase a VPN account
Get an account at the superb VPN provider VPN.ac and start enjoying the peace of mind that your internet privacy is protected. -
Login and navigate to your VPN Service details
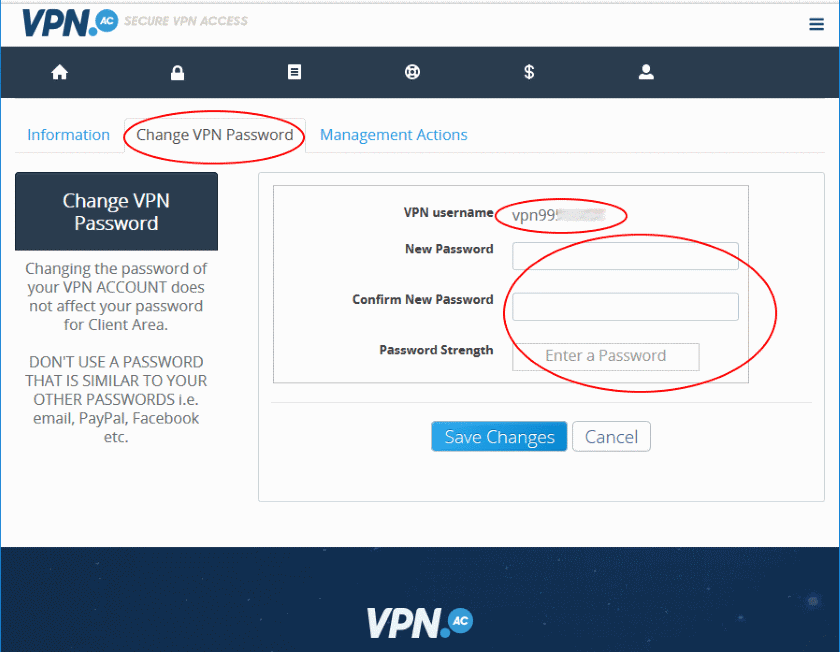
The username and password for your VPN connection are different than your account login. Create these VPN credentials on the VPN username and password management page after you login. You will need to click the ‘View Details’ button to navigate to the password entry screen.
-
Find your VPN username create your VPN password
Your VPN username will automatically be created for you and displayed right above your password entry field. Enter your desired password in both of the password fields and click ‘Save Changes’. Store your username and password in a secure location, we recommend Password Safe, you will need these credentials when you setup your VPN connection.
-
Return to your Windows desktop and locate the Windows taskbar Search Box in the lower left and click in the Search Box.
-
In the Search Box, type ‘Virtual Private’ and click the top result ‘Change Virtual Private Networks (VPN)’.
This will locate and show the VPN settings control panel where you will create a new VPN connection.
-
Click the ‘Add a VPN Connection’ option at the top of the control panel.
-
Enter the VPN Settings using your connection and login information.
‘VPN Provider’ should be set to: ‘Windows (built-in)’
‘Connection name’ can be any name, this will be the name that shows in the list of available VPN connections so make something you will recognize.
‘Server name or address’ should be set to value of the HOSTNAME column from this list of servers, something like us1.vpn.ac, uk1.vpn.ac, etc.; preferably choose the server that is closest to you, although any of these servers will work accordingly.
‘VPN type’ should be set to ‘L2TP/IPSec with pre-shared key’
‘Pre-shared key’ should be set to vpnacshared#
‘Type of sign-in info’ should be set to ‘User name and password’
‘User name (optional)’ should be your VPN username from step 2, something like vpn995XXXXX. THIS IS NOT THE SAME USERNAME as your website login, make sure you followed step 2 and created the separate VPN username and password.
‘Password (optional)’ should be the password you created in step 2.
Click ‘Save’
-
Connect to your new VPN connection.
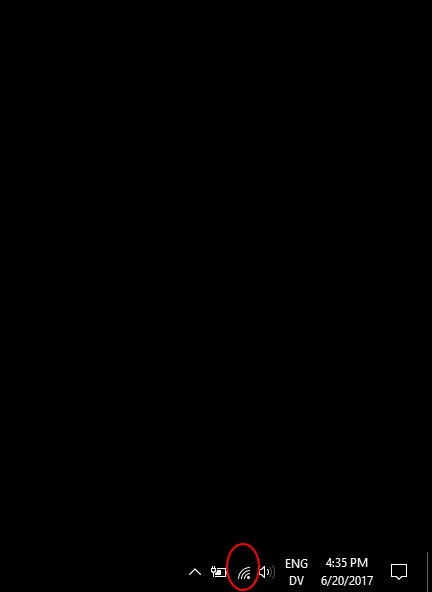
On your windows desktop, click in the right part of the taskbar on the network icon
Or if you are on wifi click the wifi icon
Click ‘Connect’
-
Congratulations! You have now shielded your internet privacy. Anything you connect to on the internet will now be encrypted and routed through this VPN connection. This protects against eavesdroppers and networks monitors from spying on your activity.
-
Troubleshooting. If you get a connection error like the following, you might need to adjust your windows firewall for L2TP. See our Windows 10 firewall for L2TP guide
Author
Neil Proctor
Neil Proctor is a privacy advocate and the co-founder of Prompt Engineering, a start-up engineering consulting firm based in Arizona. Prior to Prompt Engineering, Neil worked for GoDaddy for 13 years, he is a proven leader in nework security and web development. From GoDaddy’s early days to IPO, Neil lead web application development, information security architecture, and was General Manager for the community division and Business Unit Manager for the marketing applications product suite. His passion for product development with emphasis on application and network security has prompted him to apply his talents creating VPN guides for others and publishing them on MagnumVPN.
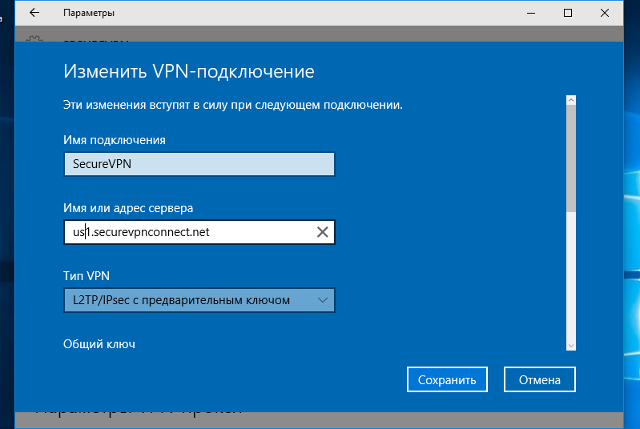
Если вы хотите развернуть собственный VPN сервер прямо из коробки и не мучиться с настройкой, мы создали для вас образ с VPN L2TP ipsec. Заказать такой сервер можно в нашем маркетплейсе.
Итак, вы заказали сервер с L2TP VPN ipsec и хотите подключиться к вашему серверу. Расскажем пошагово, как это сделать
ИНСТРУКЦИЯ ПО ПОДКЛЮЧЕНИЮ К L2TP VPN IPSEC ДЛЯ WINDOWS 10
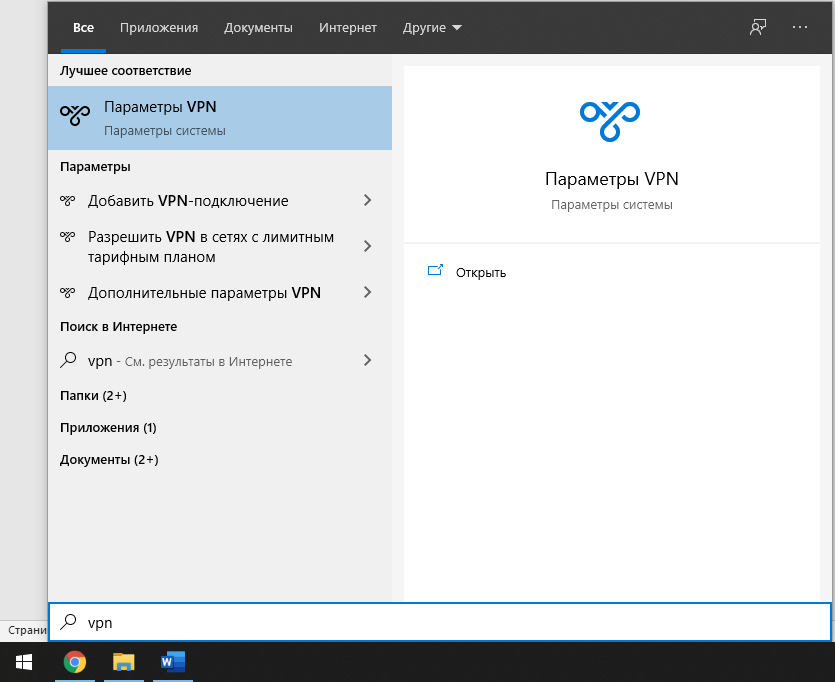
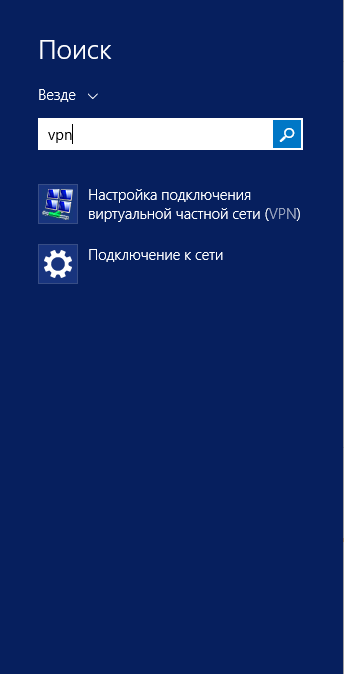
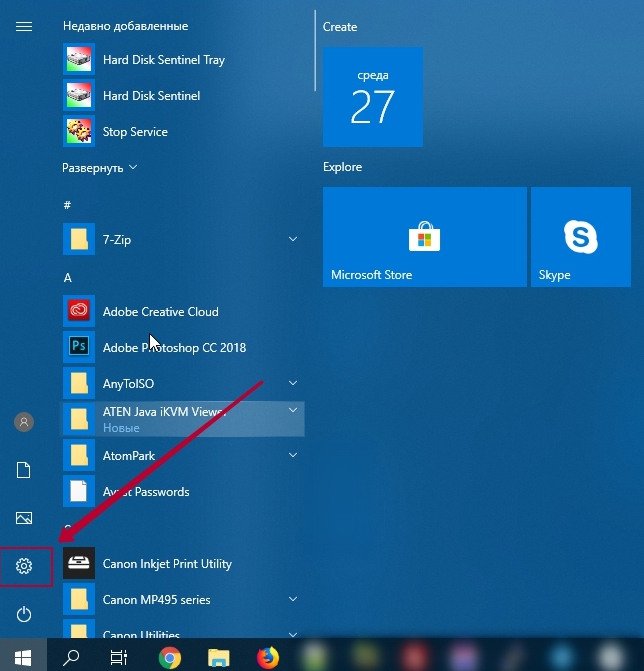
Для демонстрационных целей выберем Windows 10. В меню пуск ищем VPN.
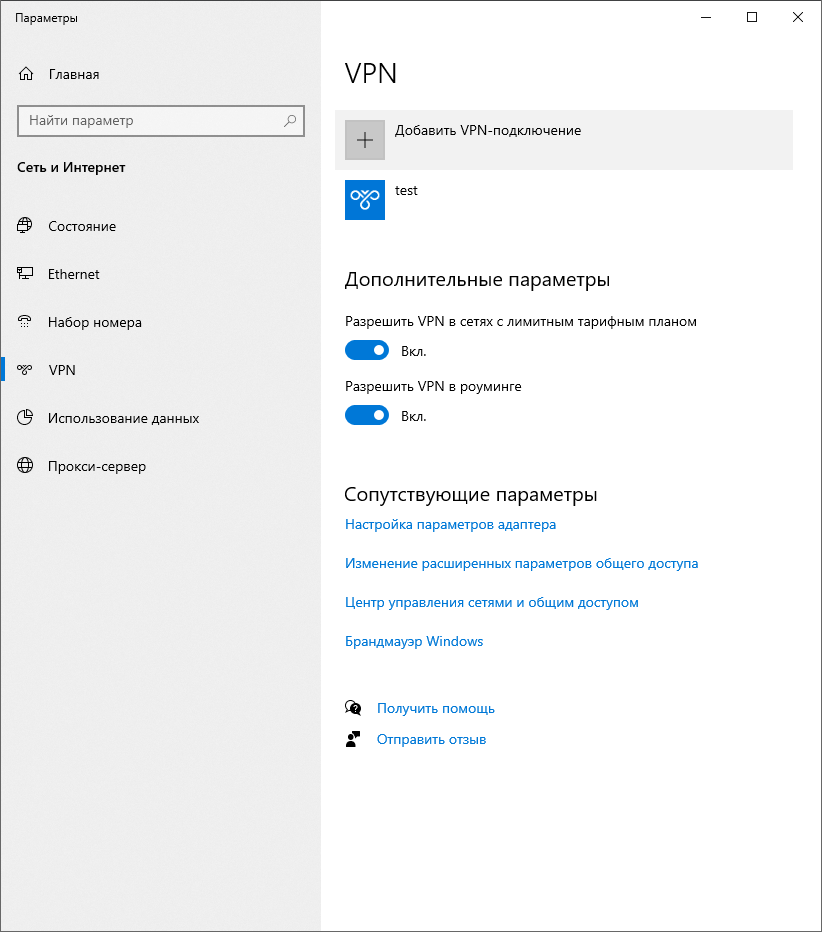
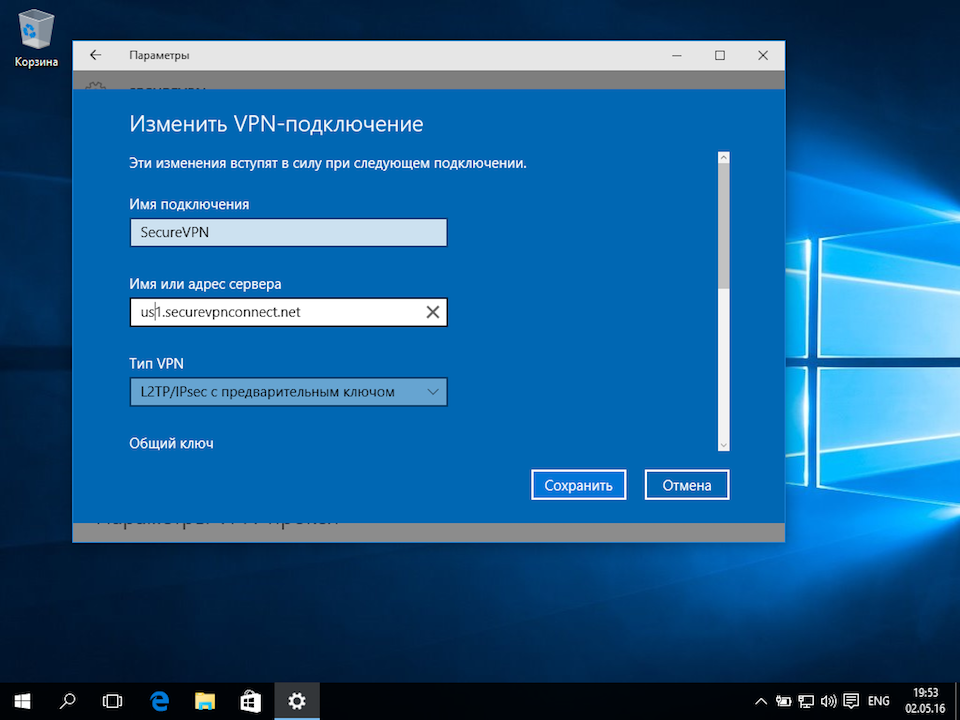
Жмем на кнопку добавления подключения и переходим в настройки.
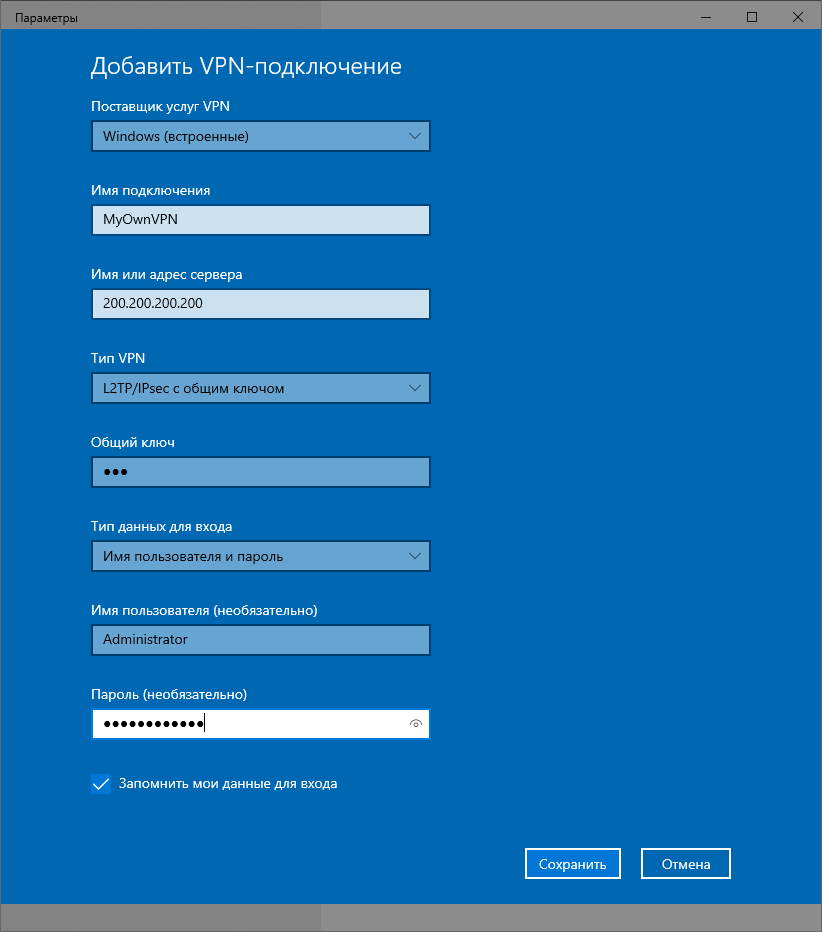
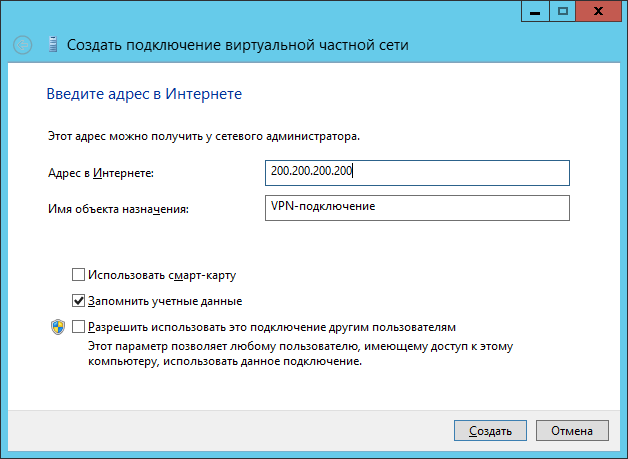
Имя подключения задавайте какое вам хочется. IP адрес – это адрес вашего VPN сервера. Тип VPN – l2TP с предварительным ключом. Общий ключ – vpn (для нашего образа в маркетплейсе.) А логин и пароль – это логин и пароль от локального пользователя, то есть от администратора.
Жмем на подключение и готово. Вот и ваш собственный VPN готов.
ИНСТРУКЦИЯ ПО ПОДКЛЮЧЕНИЮ К L2TP VPN IPSEC ДЛЯ ДЛЯ WINDOWS 8 И НИЖЕ
В Windows 8 и 8,1 ищем в меню пуск VPN би выбираем пункт с настройкой VPN.
В меню адреса вводим ip адрес вашего сервера.
В свойствах подключения нужно выбрать L2Tp IPsec .
В дополнительных параметрах нужно переключиться на первый пункт и ввести ключ. Для нашего образа ключ – vpn.
При подключении к серверу введите логин и пароль.
Вот и все. Приятного использования.
Для того, чтобы подключится к VPN, используя различные операционные системы, необходимо настроить VPN сервер. В данном примере мы рассмотрим подключение к VPN L2TP/IPsec сервера микротик. Однако вы можете использовать PPTP и другие сервера.
Ранее в главе 3 мы рассмотрели, как создать учетную запись для VPN-соединения. Сейчас нам останется разобраться, как настроить VPN сервер и далее по пунктам разберем, как совершить подключение.
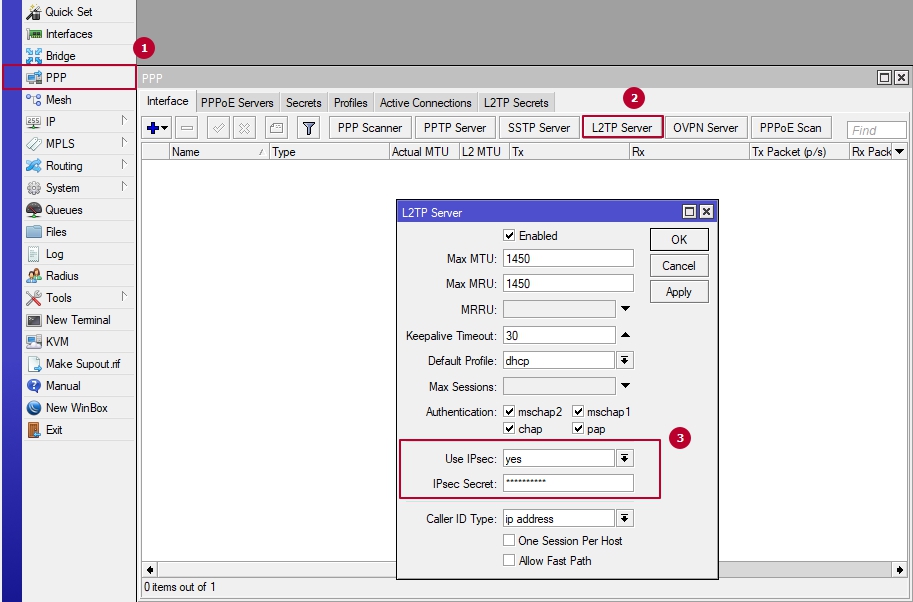
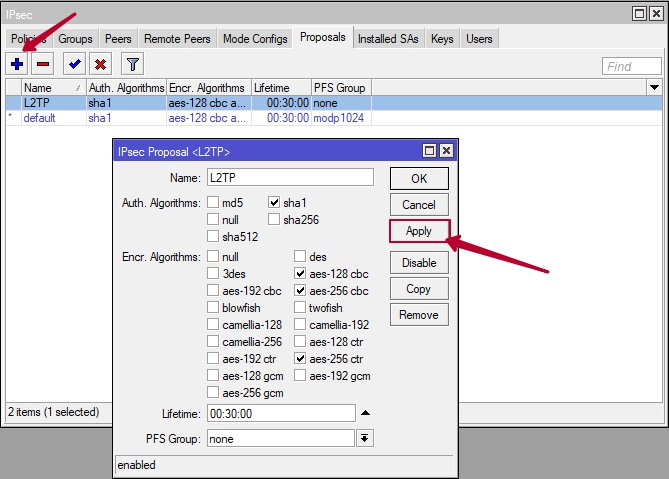
Зайдите по WinBox в ваш маршрутизатор и перейдите в меню PPP -> Вкладка Interface -> L2TP Server. Из скриншота ниже, вы можете наблюдать, что для активации сервера достаточно — Поставить галочку Enable и выбрать Default Profile. Внимание пункт номер 3 (Use IPsec) необязателен! (Скриншот 3). Его необходимо настраивать, в случае использования для соединения с VPN сервером операционной системы iOS (например: iPhone/MacBook).
(Скриншот 3)
Подключение к VPN L2TP с помощью Windows 10
Для этого нужно зайти в меню «Пуск» и выбрать значение «Параметры».
Дальше перейти во вкладку «Сеть и Интернет».
После этого выбираем вкладку «VPN» и жмем «Добавить VPN-подключение».
В окне «Добавить VPN-соединение» вам будет необходимо заполнить поля.
Поставщик услуг VPN (по умолчанию — Windows встроенные).
Имя подключения — любое удобное для вас имя, которое отображаться среди прочих VPN-соединений.
После задаёте IP-адрес сервера, к которому требуется подключиться.( внешний IP роутера)
Тип-VPN — выбираем L2TP/IPsec with certificate.
Тип данных для входа — оставляете «Имя пользователя и пароль»
Имя пользователя — введите требуемое имя пользователя.
Пароль — введите требуемый пароль.
После того, как вы настроили соединение, в списке вы увидите ваше добавленное соединение. Однако перед тем, как подключиться, сначала необходимо внести изменение в параметры маршрутизации.
Внимание!
Если ничего не изменить, то новое соединение VPN система станет использовать в качестве шлюза по умолчанию и все остальные маршруты будут недоступны. В том числе ваше подключение к сети интернет.
Для внесения изменений в настройки нужно во вкладке «Дополнительные параметры TCP/IP» убрать галочку по использованию основного шлюза в удаленной сети.
Для ускорения подключения, требуется изменить Тип VPN и нажать«ОК» в соответствии с этим примером:
После этого можно подключиться через меню сетевых подключений
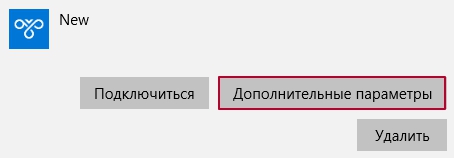
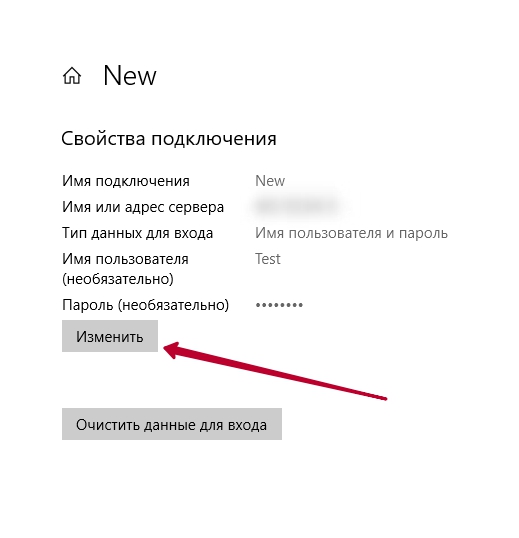
Если вам требуется изменить параметры данного VPN-соединения, нажмите на кнопку «Дополнительные параметры»
Нажмите кнопку «Изменить», измените требуемые настройки и попробуйте подключиться вновь
После этого настройка подключения к VPN закончена.
Подключение к VPN L2TP с помощью Android (на примере телефона Huawei P20 Pro)
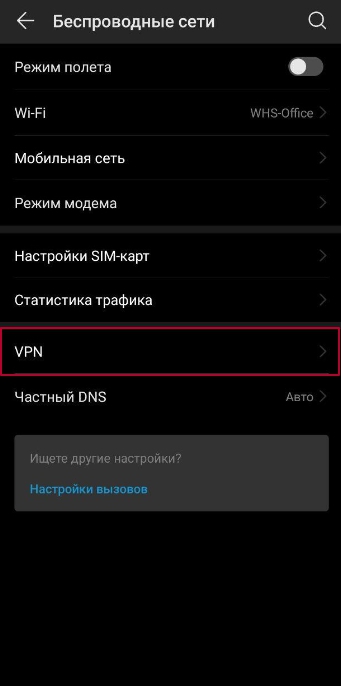
На данном примере мы разберем, как совершить подключение к VPN, пользуйся операционной системой Android. В основном функция VPN находится в меню «Настройки». Вы можете воспользоваться поисковым сервисом GOOGLE и поискать в интернете, где именно для вашего устройства находится функция VPN. В данном примере VPN находится в меню «Настройки»->»Беспроводные сети».
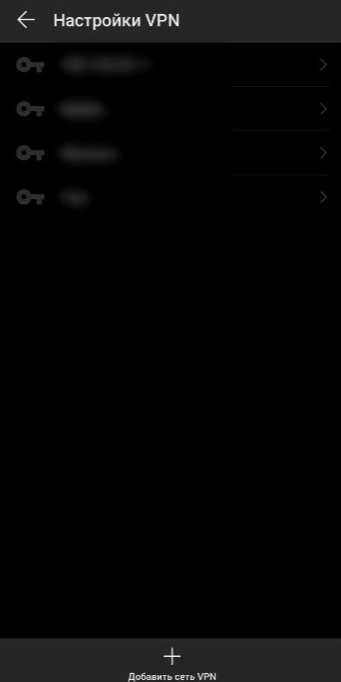
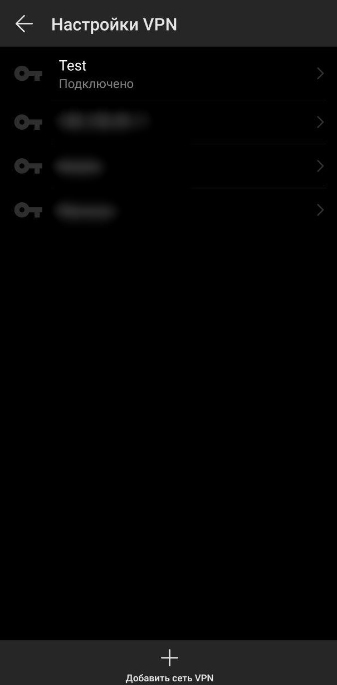
Нажмите на кнопку VPN. После чего у Вас появится пустое окно с возможностью добавления новой сети VPN. Нажмите «Добавить сеть VPN».
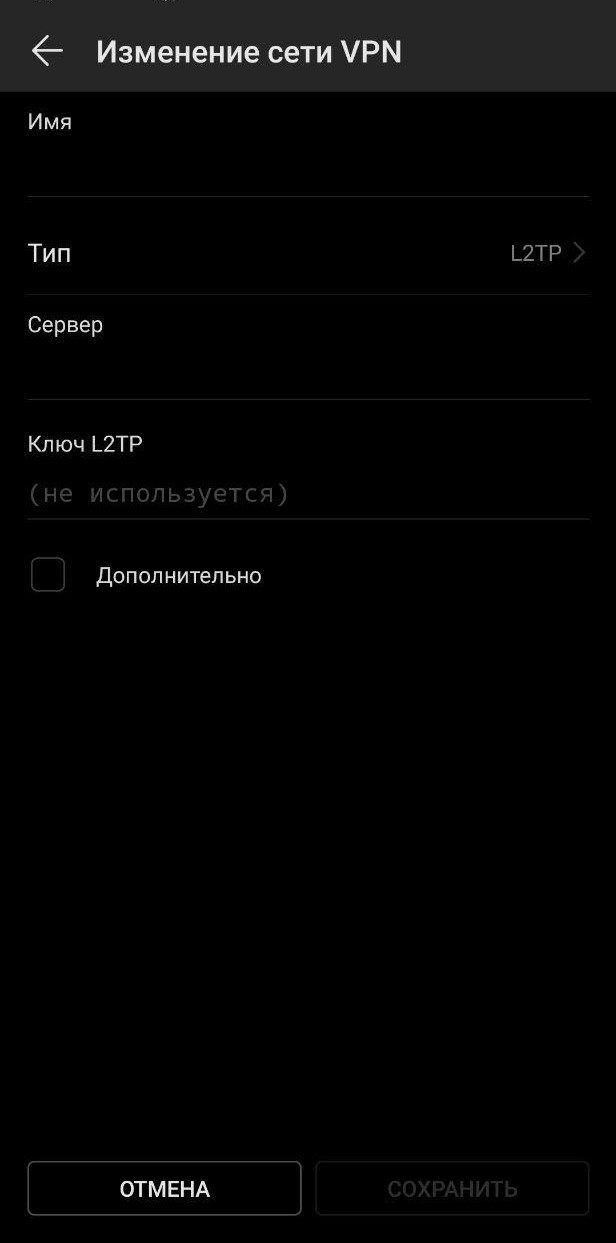
В поле «Изменение сети VPN»
Имя — Название соединение (любое, удобное для Вас)
Тип — L2TP (Если у Вас на роутере включен PPTP, то можете использовать и его)
Сервер — IP адрес роутера
Далее у Вас появится новое соединение, нажмите на него. После Вам останется ввести имя пользователя и пароль. Нажмите кнопку «Подключить».
После этого у Вас должна появится надпись — Подключено. В верхней части экрана появится ключ или слово vpn.
Подключение к VPN L2TP с помощью iPhone
Сразу проясним один момент. Подключение по PPTP протоколу к VPN у смартфонов iPhone невозможно. Компания Apple отключила возможность подключения к PPTP VPN серверам в iOS 10 на iPhone, iPad и iPod Touch.
В данном примере мы используем VPN L2TP/IPsec для подключения. Так как L2TP мы уже настроили, нам необходимо включить IPsec и совершить ряд настроек.
Первым делом перейдите в настройки L2TP сервера и разрешите использование IPsec + введите IPsec Secret (см. Скриншот 3, глава 7). После этого приступаем к настройке непосредственно IPsec.
Внимание! В данном примере мы настроем работу VPN L2TP/IPsec для доступа из вне с любого IP-адреса (0.0.0.0/0). В Вашем случае необходимо будет заменить данные цифры на иные, если вы хотите ограничить доступ.
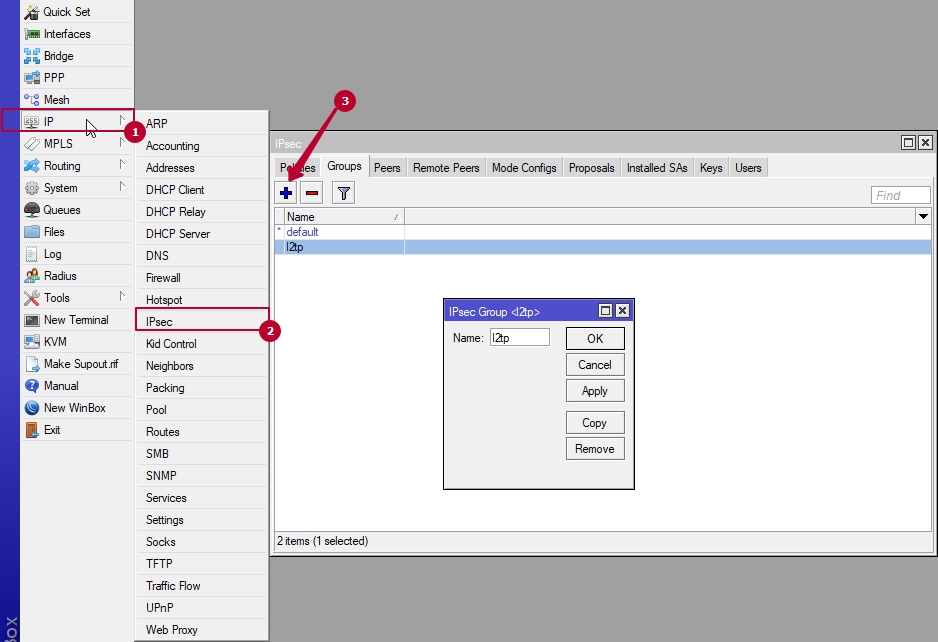
Создадим группу «l2tp».
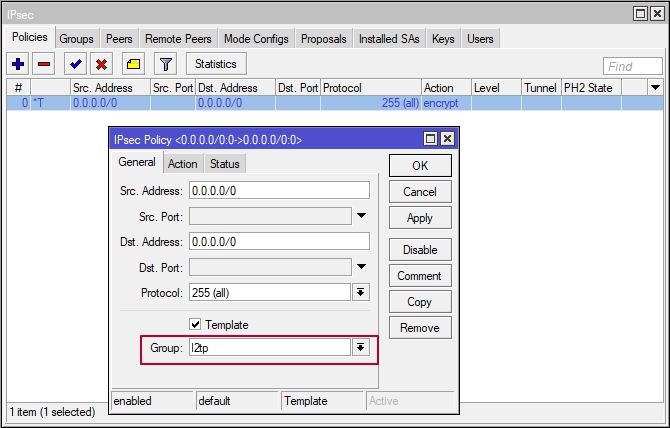
Заходим в меню IP->IPsec и на вкладке Policies нажимаем «+«
Scr. Address — вводим наш внешний IP
Dst. Address — удаленный IP, с которого будет идти подключение
Group — выбираем ранее созданную группу «l2tp»
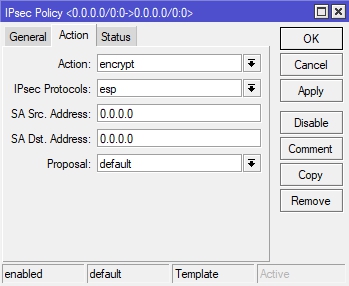
Переходим на вкладку Action
Action — encrypt
IPsec Protocols — esp
SA Scr. Address — вводим наш внешний IP
SA Dst. Address — удаленный ip
Proposal — default
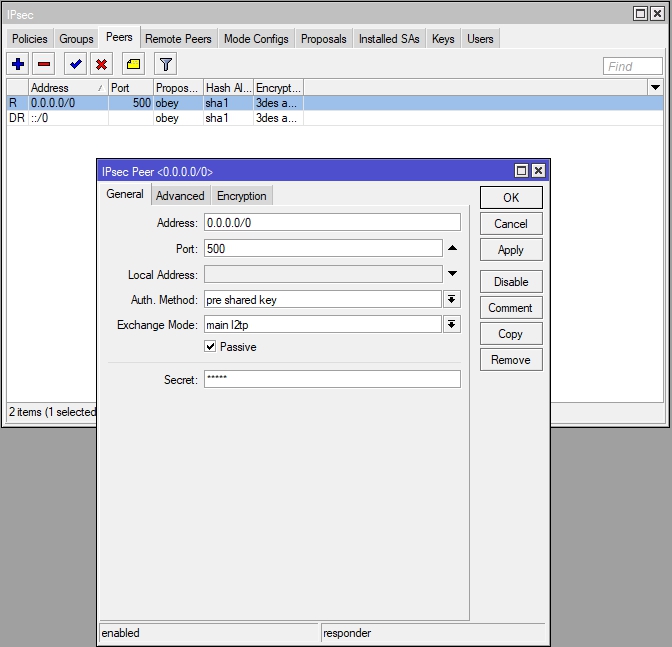
Переходим на вкладку Peers и нажимаем «+»
На вкладке General в поле Address — вбиваем удаленный ip
Port — 500
Auth. Method — pre shared key
Exchange Mode — main l2tp
Passive — ставим галочку
Secret — ключ шифрования
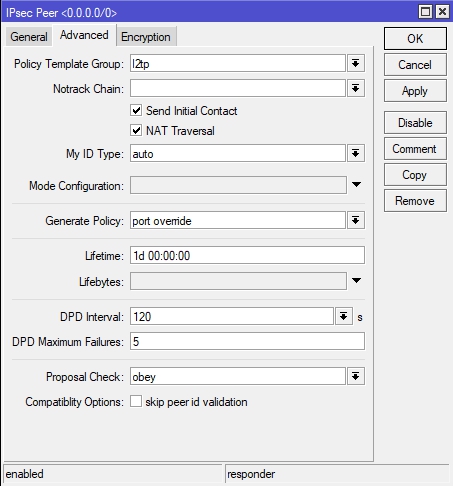
Переходим на вкладку Advanced и настраиваем следующим способом
Последняя настройка — вкладка Proposal (задаём следующие параметры)
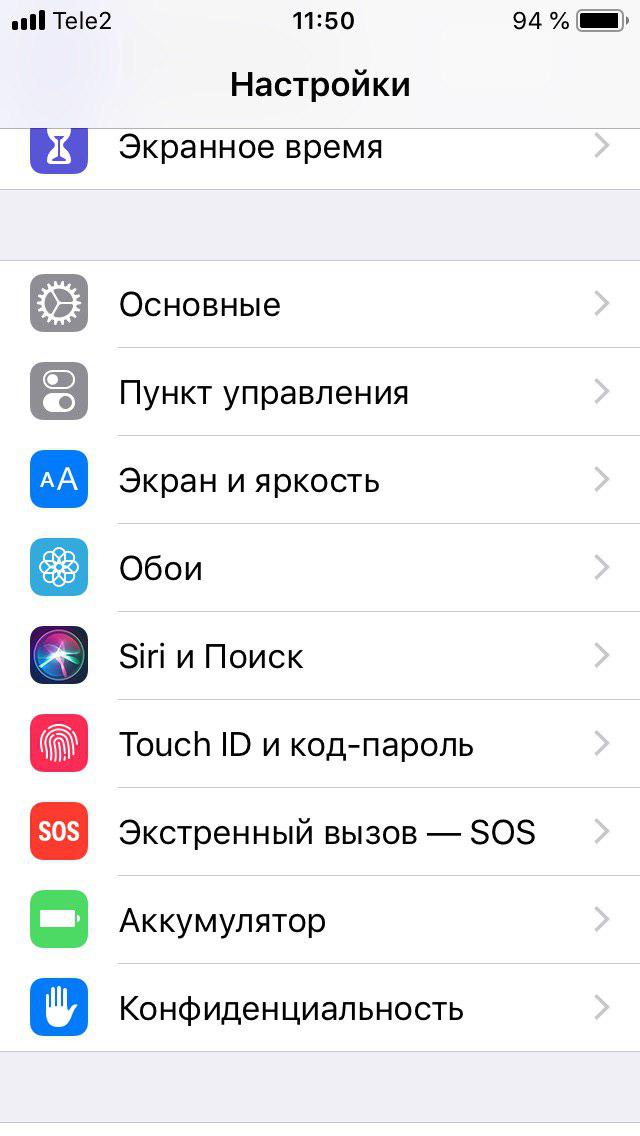
Теперь можем произвести подключение к VPN L2TP серверу с помощью iPhone. Перейдите в меню «Настройки» и выберите пункт «Основные».
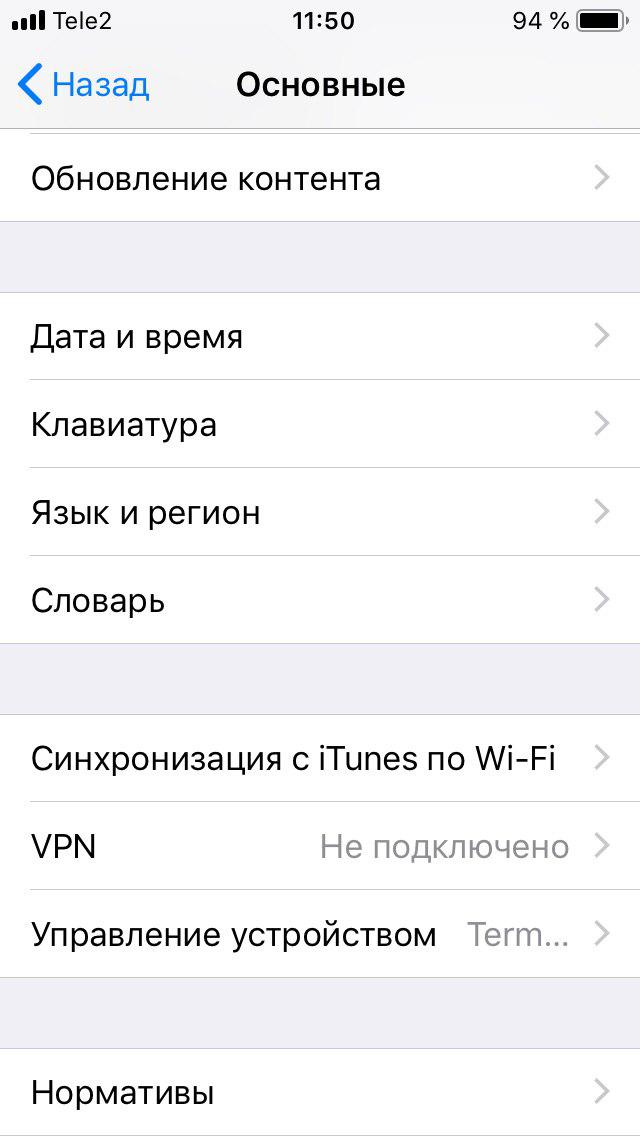
Далее выберите вкладку VPN.
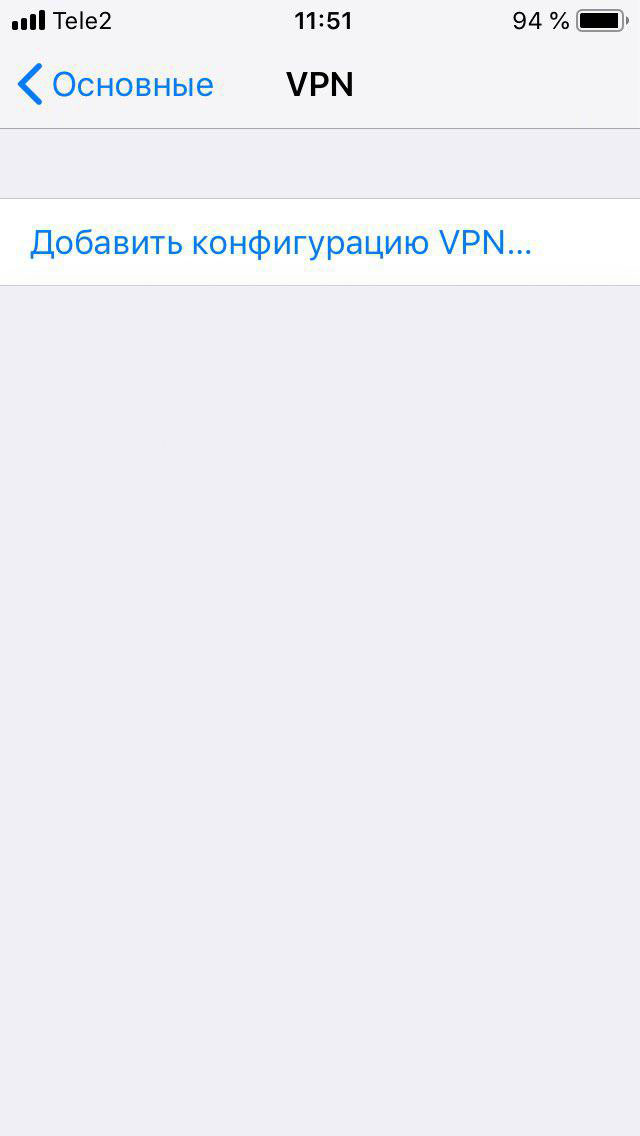
Добавьте новую конфигурацию VPN.
После этого заполните поля:
Тип — L2TP
Описание — Любое удобное для Вас
Сервер — IP-адрес сервера
Учетная запись — созданная учетная запись в PPP->Secrets
Пароль — созданный пароль
Общий ключ — IP->IPsec->Peers->Secret
После того, как запись была добавлена нажмите подключится.
После удачного подключения в верхней части экрана будет виден значок «VPN».
Для L2TP/IPSec с общим ключом
Важно: L2TP IPsec клиенты, находящиеся за одним NAT’ом, могут испытывать проблемы подключения если их более одного. Решить проблему может помочь
инструкция
. Рекомендуем вместо L2TP IPsec использовать IKEv2 IPSec.
Имя подключения — название создаваемого подключения;
-
Имя или адрес сервера — адрес VPN-сервера;
-
Тип VPN — Протокол L2TP/IPSec с общим ключом;
-
Общий ключ — значение строки PSK в разделе Пользователи -> VPN-подключение -> Основное -> Подключение по L2TP/IPSec;
-
Тип данных для входа — Имя пользователя и пароль;
-
Имя пользователя — имя пользователя, которому разрешено подключение по VPN;
-
Пароль — пароль пользователя.
При настройке подключения по VPN из сети Интернет, в свойствах VPN-подключения нужно указать следующие параметры:
-
Перейдите в Настройки параметров адаптера;
-
Нажмите на созданное подключение правой кнопкой мыши и выберите Свойства;
-
Перейдите во вкладку Безопасность и установите:
-
Шифрование данных — обязательное (отключиться, если нет шифрования)
-
Протокол расширенной проверки подлинности (EAP) — Microsoft защищенный пароль (EAP MSCHAPV2)
-
Если вы создаете VPN-подключение к UTM через проброс портов, рекомендуем выполнить следующие действия:
-
1.
Откройте Редактор реестра;
-
2.
Перейдите в
HKEY_LOCAL_MACHINESYSTEMCurrentControlSetServicesPolicyAgentи создайте DWORD-параметр с именем AssumeUDPEncapsulationContextOnSendRule и значением2;
-
1.
Неправильно указан логин или пароль пользователя. Часто при повторном соединении предлагается указать домен. Старайтесь создавать цифро-буквенные пароли, желательно на латинице для ваших учетных записей. Если есть сомнения в этом пункте, то временно установите логин и пароль пользователю «user» и «123456».
-
2.
Для того, чтобы пакеты пошли через VPN-туннель, надо убедиться, что в настройках этого подключения стоит чекбокс Использовать основной шлюз в удалённой сети в разделе Настройка параметров адаптера -> Правой кнопкой мыши по подключению -> Свойства -> Сеть -> Свойства опции «Протокол Интернета версии 4 (TCP/IPv4)» ->Дополнительно. Если же маршрутизировать все пакеты в этот интерфейс не обязательно, то маршрут надо писать вручную.
-
3.
Подключение происходит через DNAT, т.е. внешний интерфейс Ideco UTM не имеет «белого» IP-адреса, а необходимые для работы порты (500 и 4500) «проброшены» на внешний интерфейс устройства, расположенного перед Ideco UTM и имеющего «белый» IP-адрес. В данном случае VPN-подключение либо вообще не будет устанавливаться, либо будут периодические обрывы. Решение — исключить устройство перед Ideco UTM и указать на внешнем интерфейсе Ideco UTM «белый» IP-адрес, к которому в итоге и будут осуществляться L2TP/IPsec-подключения. Либо используйте протокол SSTP, потому что его проще опубликовать с помощью проброса портов.
-
4.
Если в OC Windows 10 повторно подключиться по L2TP, но при этом использовать невалидный ключ PSK (введя его в дополнительных параметрах (скриншот ниже)), подключение все равно будет установлено успешно. Это связано с особенностями работы ОС.
Убедитесь, что локальная сеть (или адрес на сетевой карте) на удалённой машине не пересекается с локальной сетью организации. Если пересекается, то доступа к сети организации не будет (трафик по таблице маршрутизации пойдёт в физический интерфейс, а не в VPN). Адресацию необходимо менять.