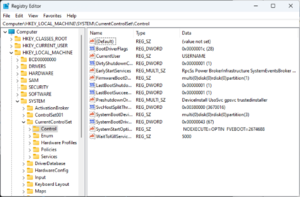
Registry Editor, the user interface for the registry, in Windows 11 |
|
| Developer(s) | Microsoft |
|---|---|
| Initial release | April 6, 1992; 30 years ago with Windows 3.1 |
| Operating system | Microsoft Windows |
| Platform | IA-32, x86-64 and ARM (and historically DEC Alpha, Itanium, MIPS, and PowerPC) |
| Included with | Microsoft Windows |
| Type | Hierarchical database |
| Website | docs.microsoft.com/en-us/windows/desktop/SysInfo/registry |
The Windows Registry is a hierarchical database that stores low-level settings for the Microsoft Windows operating system and for applications that opt to use the registry. The kernel, device drivers, services, Security Accounts Manager, and user interfaces can all use the registry. The registry also allows access to counters for profiling system performance.
In other words, the registry or Windows Registry contains information, settings, options, and other values for programs and hardware installed on all versions of Microsoft Windows operating systems. For example, when a program is installed, a new subkey containing settings such as a program’s location, its version, and how to start the program, are all added to the Windows Registry.
When introduced with Windows 3.1, the Windows Registry primarily stored configuration information for COM-based components. Windows 95 and Windows NT extended its use to rationalize and centralize the information in the profusion of INI files, which held the configurations for individual programs, and were stored at various locations.[1][2] It is not a requirement for Windows applications to use the Windows Registry. For example, .NET Framework applications use XML files for configuration, while portable applications usually keep their configuration files with their executables.
Rationale[edit]
Prior to the Windows Registry, .INI files stored each program’s settings as a text file or binary file, often located in a shared location that did not provide user-specific settings in a multi-user scenario. By contrast, the Windows Registry stores all application settings in one logical repository (but a number of discrete files) and in a standardized form. According to Microsoft, this offers several advantages over .INI files.[2][3] Since file parsing is done much more efficiently with a binary format, it may be read from or written to more quickly than a text INI file. Furthermore, strongly typed data can be stored in the registry, as opposed to the text information stored in .INI files. This is a benefit when editing keys manually using regedit.exe, the built-in Windows Registry Editor. Because user-based registry settings are loaded from a user-specific path rather than from a read-only system location, the registry allows multiple users to share the same machine, and also allows programs to work for less privileged users. Backup and restoration is also simplified as the registry can be accessed over a network connection for remote management/support, including from scripts, using the standard set of APIs, as long as the Remote Registry service is running and firewall rules permit this.
Because the registry is a database, it offers improved system integrity with features such as atomic updates. If two processes attempt to update the same registry value at the same time, one process’s change will precede the other’s and the overall consistency of the data will be maintained. Where changes are made to .INI files, such race conditions can result in inconsistent data that does not match either attempted update. Windows Vista and later operating systems provide transactional updates to the registry by means of the Kernel Transaction Manager, extending the atomicity guarantees across multiple key and/or value changes, with traditional commit–abort semantics. (Note however that NTFS provides such support for the file system as well, so the same guarantees could, in theory, be obtained with traditional configuration files.)
Structure[edit]
Keys and values[edit]
The registry contains two basic elements: keys and values. Registry keys are container objects similar to folders. Registry values are non-container objects similar to files. Keys may contain values and subkeys. Keys are referenced with a syntax similar to Windows’ path names, using backslashes to indicate levels of hierarchy. Keys must have a case insensitive name without backslashes.
The hierarchy of registry keys can only be accessed from a known root key handle (which is anonymous but whose effective value is a constant numeric handle) that is mapped to the content of a registry key preloaded by the kernel from a stored «hive», or to the content of a subkey within another root key, or mapped to a registered service or DLL that provides access to its contained subkeys and values.
E.g. HKEY_LOCAL_MACHINESoftwareMicrosoftWindows refers to the subkey «Windows» of the subkey «Microsoft» of the subkey «Software» of the HKEY_LOCAL_MACHINE root key.
There are seven predefined root keys, traditionally named according to their constant handles defined in the Win32 API, or by synonymous abbreviations (depending on applications):[4]
- HKEY_LOCAL_MACHINE or HKLM
- HKEY_CURRENT_CONFIG or HKCC
- HKEY_CLASSES_ROOT or HKCR
- HKEY_CURRENT_USER or HKCU
- HKEY_USERS or HKU
- HKEY_PERFORMANCE_DATA (only in Windows NT, but invisible in the Windows Registry Editor)[5]
- HKEY_DYN_DATA (only in Windows 9x, and visible in the Windows Registry Editor)
Like other files and services in Windows, all registry keys may be restricted by access control lists (ACLs), depending on user privileges, or on security tokens acquired by applications, or on system security policies enforced by the system (these restrictions may be predefined by the system itself, and configured by local system administrators or by domain administrators). Different users, programs, services or remote systems may only see some parts of the hierarchy or distinct hierarchies from the same root keys.
Registry values are name/data pairs stored within keys. Registry values are referenced separately from registry keys. Each registry value stored in a registry key has a unique name whose letter case is not significant. The Windows API functions that query and manipulate registry values take value names separately from the key path and/or handle that identifies the parent key. Registry values may contain backslashes in their names, but doing so makes them difficult to distinguish from their key paths when using some legacy Windows Registry API functions (whose usage is deprecated in Win32).
The terminology is somewhat misleading, as each registry key is similar to an associative array, where standard terminology would refer to the name part of each registry value as a «key». The terms are a holdout from the 16-bit registry in Windows 3, in which registry keys could not contain arbitrary name/data pairs, but rather contained only one unnamed value (which had to be a string). In this sense, the Windows 3 registry was like a single associative array, in which the keys (in the sense of both ‘registry key’ and ‘associative array key’) formed a hierarchy, and the registry values were all strings. When the 32-bit registry was created, so was the additional capability of creating multiple named values per key, and the meanings of the names were somewhat distorted.[6] For compatibility with the previous behavior, each registry key may have a «default» value, whose name is the empty string.
Each value can store arbitrary data with variable length and encoding, but which is associated with a symbolic type (defined as a numeric constant) defining how to parse this data. The standard types are:[7]
| Type ID | Symbolic type name | Meaning and encoding of the data stored in the registry value |
|---|---|---|
| 0 | REG_NONE | No type (the stored value, if any) |
| 1 | REG_SZ | A string value, normally stored and exposed in UTF-16LE (when using the Unicode version of Win32 API functions), usually terminated by a NUL character |
| 2 | REG_EXPAND_SZ | An «expandable» string value that can contain environment variables, normally stored and exposed in UTF-16LE, usually terminated by a NUL character |
| 3 | REG_BINARY | Binary data (any arbitrary data) |
| 4 | REG_DWORD / REG_DWORD_LITTLE_ENDIAN | A DWORD value, a 32-bit unsigned integer (numbers between 0 and 4,294,967,295 [232 – 1]) (little-endian) |
| 5 | REG_DWORD_BIG_ENDIAN | A DWORD value, a 32-bit unsigned integer (numbers between 0 and 4,294,967,295 [232 – 1]) (big-endian) |
| 6 | REG_LINK | A symbolic link (UNICODE) to another registry key, specifying a root key and the path to the target key |
| 7 | REG_MULTI_SZ | A multi-string value, which is an ordered list of non-empty strings, normally stored and exposed in Unicode, each one terminated by a null character, the list being normally terminated by a second null character.[8] |
| 8 | REG_RESOURCE_LIST | A resource list (used by the Plug-n-Play hardware enumeration and configuration) |
| 9 | REG_FULL_RESOURCE_DESCRIPTOR | A resource descriptor (used by the Plug-n-Play hardware enumeration and configuration) |
| 10 | REG_RESOURCE_REQUIREMENTS_LIST | A resource requirements list (used by the Plug-n-Play hardware enumeration and configuration) |
| 11 | REG_QWORD / REG_QWORD_LITTLE_ENDIAN | A QWORD value, a 64-bit integer (either big- or little-endian, or unspecified) (introduced in Windows 2000)[9] |
Root keys[edit]
The keys at the root level of the hierarchical database are generally named by their Windows API definitions, which all begin «HKEY».[2] They are frequently abbreviated to a three- or four-letter short name starting with «HK» (e.g. HKCU and HKLM). Technically, they are predefined handles (with known constant values) to specific keys that are either maintained in memory, or stored in hive files stored in the local filesystem and loaded by the system kernel at boot time and then shared (with various access rights) between all processes running on the local system, or loaded and mapped in all processes started in a user session when the user logs on the system.
The HKEY_LOCAL_MACHINE (local machine-specific configuration data) and HKEY_CURRENT_USER (user-specific configuration data) nodes have a similar structure to each other; user applications typically look up their settings by first checking for them in «HKEY_CURRENT_USERSoftwareVendor’s nameApplication’s nameVersionSetting name», and if the setting is not found, look instead in the same location under the HKEY_LOCAL_MACHINE key[citation needed]. However, the converse may apply for administrator-enforced policy settings where HKLM may take precedence over HKCU. The Windows Logo Program has specific requirements for where different types of user data may be stored, and that the concept of least privilege be followed so that administrator-level access is not required to use an application.[a][10]
HKEY_LOCAL_MACHINE (HKLM)[edit]
Abbreviated HKLM, HKEY_LOCAL_MACHINE stores settings that are specific to the local computer.[11]
The key located by HKLM is actually not stored on disk, but maintained in memory by the system kernel in order to map all the other subkeys. Applications cannot create any additional subkeys. On Windows NT, this key contains four subkeys, «SAM», «SECURITY», «SYSTEM», and «SOFTWARE», that are loaded at boot time within their respective files located in the %SystemRoot%System32config folder. A fifth subkey, «HARDWARE», is volatile and is created dynamically, and as such is not stored in a file (it exposes a view of all the currently detected Plug-and-Play devices). On Windows Vista and above, a sixth and seventh subkey, «COMPONENTS» and «BCD», are mapped in memory by the kernel on-demand and loaded from %SystemRoot%system32configCOMPONENTS or from boot configuration data, bootBCD on the system partition.
- The «HKLMSAM» key usually appears as empty for most users (unless they are granted access by administrators of the local system or administrators of domains managing the local system). It is used to reference all «Security Accounts Manager» (SAM) databases for all domains into which the local system has been administratively authorized or configured (including the local domain of the running system, whose SAM database is stored in a subkey also named «SAM»: other subkeys will be created as needed, one for each supplementary domain). Each SAM database contains all builtin accounts (mostly group aliases) and configured accounts (users, groups and their aliases, including guest accounts and administrator accounts) created and configured on the respective domain, for each account in that domain, it notably contains the user name which can be used to log on that domain, the internal unique user identifier in the domain, a cryptographic hash of each user’s password for each enabled authentication protocol, the location of storage of their user registry hive, various status flags (for example if the account can be enumerated and be visible in the logon prompt screen), and the list of domains (including the local domain) into which the account was configured.
- The «HKLMSECURITY» key usually appears empty for most users (unless they are granted access by users with administrative privileges) and is linked to the Security database of the domain into which the current user is logged on (if the user is logged on the local system domain, this key will be linked to the registry hive stored by the local machine and managed by local system administrators or by the builtin «System» account and Windows installers). The kernel will access it to read and enforce the security policy applicable to the current user and all applications or operations executed by this user. It also contains a «SAM» subkey which is dynamically linked to the SAM database of the domain onto which the current user is logged on.
- The «HKLMSYSTEM» key is normally only writable by users with administrative privileges on the local system. It contains information about the Windows system setup, data for the secure random number generator (RNG), the list of currently mounted devices containing a filesystem, several numbered «HKLMSYSTEMControl Sets» containing alternative configurations for system hardware drivers and services running on the local system (including the currently used one and a backup), a «HKLMSYSTEMSelect» subkey containing the status of these Control Sets, and a «HKLMSYSTEMCurrentControlSet» which is dynamically linked at boot time to the Control Set which is currently used on the local system. Each configured Control Set contains:
- an «Enum» subkey enumerating all known Plug-and-Play devices and associating them with installed system drivers (and storing the device-specific configurations of these drivers),
- a «Services» subkey listing all installed system drivers (with non device-specific configuration, and the enumeration of devices for which they are instantiated) and all programs running as services (how and when they can be automatically started),
- a «Control» subkey organizing the various hardware drivers and programs running as services and all other system-wide configuration,
- a «Hardware Profiles» subkey enumerating the various profiles that have been tuned (each one with «System» or «Software» settings used to modify the default profile, either in system drivers and services or in the applications) as well as the «Hardware ProfilesCurrent» subkey which is dynamically linked to one of these profiles.
- The «HKLMSOFTWARE» subkey contains software and Windows settings (in the default hardware profile). It is mostly modified by application and system installers. It is organized by software vendor (with a subkey for each), but also contains a «Windows» subkey for some settings of the Windows user interface, a «Classes» subkey containing all registered associations from file extensions, MIME types, Object Classes IDs and interfaces IDs (for OLE, COM/DCOM and ActiveX), to the installed applications or DLLs that may be handling these types on the local machine (however these associations are configurable for each user, see below), and a «Policies» subkey (also organized by vendor) for enforcing general usage policies on applications and system services (including the central certificates store used for authenticating, authorizing or disallowing remote systems or services running outside the local network domain).
- The «HKLMSOFTWAREWow6432Node» key is used by 32-bit applications on a 64-bit Windows OS, and is equivalent to but separate from «HKLMSOFTWARE». The key path is transparently presented to 32-bit applications by WoW64 as HKLMSOFTWARE[12] (in a similar way that 32-bit applications see %SystemRoot%Syswow64 as %SystemRoot%System32)
HKEY_CLASSES_ROOT (HKCR)[edit]
- Abbreviated HKCR, HKEY_CLASSES_ROOT contains information about registered applications, such as file associations and OLE Object Class IDs, tying them to the applications used to handle these items. On Windows 2000 and above, HKCR is a compilation of user-based HKCUSoftwareClasses and machine-based HKLMSoftwareClasses. If a given value exists in both of the subkeys above, the one in HKCUSoftwareClasses takes precedence.[13] The design allows for either machine- or user-specific registration of COM objects.
HKEY_USERS (HKU)[edit]
- Abbreviated HKU, HKEY_USERS contains subkeys corresponding to the HKEY_CURRENT_USER keys for each user profile actively loaded on the machine, though user hives are usually only loaded for currently logged-in users.
HKEY_CURRENT_USER (HKCU)[edit]
- Abbreviated HKCU, HKEY_CURRENT_USER stores settings that are specific to the currently logged-in user.[14] The HKEY_CURRENT_USER key is a link to the subkey of HKEY_USERS that corresponds to the user; the same information is accessible in both locations. The specific subkey referenced is «(HKU)(SID)…» where (SID) corresponds to the Windows SID; if the «(HKCU)» key has the following suffix «(HKCU)SoftwareClasses…» then it corresponds to «(HKU)(SID)_CLASSES…» i.e. the suffix has the string «_CLASSES» is appended to the (SID).
- On Windows NT systems, each user’s settings are stored in their own files called NTUSER.DAT and USRCLASS.DAT inside their own Documents and Settings subfolder (or their own Users sub folder in Windows Vista and above). Settings in this hive follow users with a roaming profile from machine to machine.
HKEY_PERFORMANCE_DATA[edit]
- This key provides runtime information into performance data provided by either the NT kernel itself, or running system drivers, programs and services that provide performance data. This key is not stored in any hive and not displayed in the Registry Editor, but it is visible through the registry functions in the Windows API, or in a simplified view via the Performance tab of the Task Manager (only for a few performance data on the local system) or via more advanced control panels (such as the Performances Monitor or the Performances Analyzer which allows collecting and logging these data, including from remote systems).
HKEY_DYN_DATA[edit]
- This key is used only on Windows 95, Windows 98 and Windows ME.[15] It contains information about hardware devices, including Plug and Play and network performance statistics. The information in this hive is also not stored on the hard drive. The Plug and Play information is gathered and configured at startup and is stored in memory.[16]
Hives[edit]
Even though the registry presents itself as an integrated hierarchical database, branches of the registry are actually stored in a number of disk files called hives.[17] (The word hive constitutes an in-joke.)[18]
Some hives are volatile and are not stored on disk at all. An example of this is the hive of the branch starting at HKLMHARDWARE. This hive records information about system hardware and is created each time the system boots and performs hardware detection.
Individual settings for users on a system are stored in a hive (disk file) per user. During user login, the system loads the user hive under the HKEY_USERS key and sets the HKCU (HKEY_CURRENT_USER) symbolic reference to point to the current user. This allows applications to store/retrieve settings for the current user implicitly under the HKCU key.
Not all hives are loaded at any one time. At boot time, only a minimal set of hives are loaded, and after that, hives are loaded as the operating system initializes and as users log in or whenever a hive is explicitly loaded by an application.
File locations[edit]
The registry is physically stored in several files, which are generally obfuscated from the user-mode APIs used to manipulate the data inside the registry. Depending upon the version of Windows, there will be different files and different locations for these files, but they are all on the local machine. The location for system registry files in Windows NT is %SystemRoot%System32Config; the user-specific HKEY_CURRENT_USER user registry hive is stored in Ntuser.dat inside the user profile. There is one of these per user; if a user has a roaming profile, then this file will be copied to and from a server at logout and login respectively. A second user-specific registry file named UsrClass.dat contains COM registry entries and does not roam by default.
Windows NT[edit]
Windows NT systems store the registry in a binary file format which can be exported, loaded and unloaded by the Registry Editor in these operating systems. The following system registry files are stored in %SystemRoot%System32Config:
Sam– HKEY_LOCAL_MACHINESAMSecurity– HKEY_LOCAL_MACHINESECURITYSoftware– HKEY_LOCAL_MACHINESOFTWARESystem– HKEY_LOCAL_MACHINESYSTEMDefault– HKEY_USERS.DEFAULTUserdiff– Not associated with a hive. Used only when upgrading operating systems.[19]
The following file is stored in each user’s profile folder:
%USERPROFILE%Ntuser.dat– HKEY_USERS<User SID> (linked to by HKEY_CURRENT_USER)
For Windows 2000, Server 2003 and Windows XP, the following additional user-specific file is used for file associations and COM information:
%USERPROFILE%Local SettingsApplication DataMicrosoftWindowsUsrclass.dat(path is localized) – HKEY_USERS<User SID>_Classes (HKEY_CURRENT_USERSoftwareClasses)
For Windows Vista and later, the path was changed to:
%USERPROFILE%AppDataLocalMicrosoftWindowsUsrclass.dat(path is not localized) alias%LocalAppData%MicrosoftWindowsUsrclass.dat– HKEY_USERS<User SID>_Classes (HKEY_CURRENT_USERSoftwareClasses)
Windows 2000 keeps an alternate copy of the registry hives (.ALT) and attempts to switch to it when corruption is detected.[20] Windows XP and Windows Server 2003 do not maintain a System.alt hive because NTLDR on those versions of Windows can process the System.log file to bring up to date a System hive that has become inconsistent during a shutdown or crash. In addition, the %SystemRoot%Repair folder contains a copy of the system’s registry hives that were created after installation and the first successful startup of Windows.
Each registry data file has an associated file with a «.log» extension that acts as a transaction log that is used to ensure that any interrupted updates can be completed upon next startup.[21] Internally, Registry files are split into 4 kB «bins» that contain collections of «cells».[21]
Windows 9x[edit]
The registry files are stored in the %WINDIR% directory under the names USER.DAT and SYSTEM.DAT with the addition of CLASSES.DAT in Windows ME. Also, each user profile (if profiles are enabled) has its own USER.DAT file which is located in the user’s profile directory in %WINDIR%Profiles<Username>.
Windows 3.11[edit]
The only registry file is called REG.DAT and it is stored in the %WINDIR% directory.
Windows 10 Mobile[edit]
Note: To access the registry files, the Phone needs to be set in a special mode using either:
- WpInternals ( Put the mobile device into flash mode. )
- InterOp Tools ( mount the MainOS Partition with MTP. )
If any of above Methods worked — The Device Registry Files can be found in the following location:
{Phone}EFIESPWindowsSystem32config
Note: InterOp Tools also includes a registry editor.
Editing[edit]
Registry editors[edit]
The registry contains important configuration information for the operating system, for installed applications as well as individual settings for each user and application. A careless change to the operating system configuration in the registry could cause irreversible damage, so it is usually only installer programs which perform changes to the registry database during installation/configuration and removal. If a user wants to edit the registry manually, Microsoft recommends that a backup of the registry be performed before the change.[22] When a program is removed from control panel, it may not be completely removed and, in case of errors or glitches caused by references to missing programs, the user might have to manually check inside directories such as program files. After this, the user might need to manually remove any reference to the uninstalled program in the registry. This is usually done by using RegEdit.exe.[23] Editing the registry is sometimes necessary when working around Windows-specific issues e.g. problems when logging onto a domain can be resolved by editing the registry.[24]
Windows Registry can be edited manually using programs such as RegEdit.exe, although these tools do not expose some of the registry’s metadata such as the last modified date.
The registry editor for the 3.1/95 series of operating systems is RegEdit.exe and for Windows NT it is RegEdt32.exe; the functionalities are merged in Windows XP. Optional and/or third-party tools similar to RegEdit.exe are available for many Windows CE versions.
Registry Editor allows users to perform the following functions:
- Creating, manipulating, renaming[25] and deleting registry keys, subkeys, values and value data
- Importing and exporting .
REGfiles, exporting data in the binary hive format - Loading, manipulating and unloading registry hive format files (Windows NT systems only)
- Setting permissions based on ACLs (Windows NT systems only)
- Bookmarking user-selected registry keys as Favorites
- Finding particular strings in key names, value names and value data
- Remotely editing the registry on another networked computer
.REG files[edit]
.REG files (also known as Registration entries) are text-based human-readable files for exporting and importing portions of the registry using an INI-based syntax. On Windows 2000 and later, they contain the string Windows Registry Editor Version 5.00 at the beginning and are Unicode-based. On Windows 9x and NT 4.0 systems, they contain the string REGEDIT4 and are ANSI-based.[26] Windows 9x format .REG files are compatible with Windows 2000 and later. The Registry Editor on Windows on these systems also supports exporting .REG files in Windows 9x/NT format. Data is stored in .REG files using the following syntax:[26]
[<Hive name><Key name><Subkey name>] "Value name"=<Value type>:<Value data>
The Default Value of a key can be edited by using «@» instead of «Value Name»:
[<Hive name><Key name><Subkey name>] @=<Value type>:<Value data>
String values do not require a <Value type> (see example), but backslashes (») need to be written as a double-backslash (‘\’), and quotes (‘»‘) as backslash-quote (‘»‘).
For example, to add the values «Value A», «Value B», «Value C», «Value D», «Value E», «Value F», «Value G», «Value H», «Value I», «Value J», «Value K», «Value L», and «Value M» to the HKLMSOFTWAREFoobar key:
Windows Registry Editor Version 5.00 [HKEY_LOCAL_MACHINESOFTWAREFoobar] "Value A"="<String value data with escape characters>" "Value B"=hex:<Binary data (as comma-delimited list of hexadecimal values)> "Value C"=dword:<DWORD value integer> "Value D"=hex(0):<REG_NONE (as comma-delimited list of hexadecimal values)> "Value E"=hex(1):<REG_SZ (as comma-delimited list of hexadecimal values representing a UTF-16LE NUL-terminated string)> "Value F"=hex(2):<Expandable string value data (as comma-delimited list of hexadecimal values representing a UTF-16LE NUL-terminated string)> "Value G"=hex(3):<Binary data (as comma-delimited list of hexadecimal values)> ; equal to "Value B" "Value H"=hex(4):<DWORD value (as comma-delimited list of 4 hexadecimal values, in little endian byte order)> "Value I"=hex(5):<DWORD value (as comma-delimited list of 4 hexadecimal values, in big endian byte order)> "Value J"=hex(7):<Multi-string value data (as comma-delimited list of hexadecimal values representing UTF-16LE NUL-terminated strings)> "Value K"=hex(8):<REG_RESOURCE_LIST (as comma-delimited list of hexadecimal values)> "Value L"=hex(a):<REG_RESOURCE_REQUIREMENTS_LIST (as comma-delimited list of hexadecimal values)> "Value M"=hex(b):<QWORD value (as comma-delimited list of 8 hexadecimal values, in little endian byte order)>
Data from .REG files can be added/merged with the registry by double-clicking these files or using the /s switch in the command line. REG files can also be used to remove registry data.
To remove a key (and all subkeys, values and data), the key name must be preceded by a minus sign («-«).[26]
For example, to remove the HKLMSOFTWAREFoobar key (and all subkeys, values and data),
[-HKEY_LOCAL_MACHINESOFTWAREFoobar]
To remove a value (and its data), the values to be removed must have a minus sign («-«) after the equal sign («=»).[26]
For example, to remove only the «Value A» and «Value B» values (and their data) from the HKLMSOFTWAREFoobar key:
[HKEY_LOCAL_MACHINESOFTWAREFoobar] "Value A"=- "Value B"=-
To remove only the Default value of the key HKLMSOFTWAREFoobar (and its data):
[HKEY_LOCAL_MACHINESOFTWAREFoobar] @=-
Lines beginning with a semicolon are considered comments:
; This is a comment. This can be placed in any part of a .reg file [HKEY_LOCAL_MACHINESOFTWAREFoobar] "Value"="Example string"
Group policies[edit]
Windows group policies can change registry keys for a number of machines or individual users based on policies. When a policy first takes effect for a machine or for an individual user of a machine, the registry settings specified as part of the policy are applied to the machine or user settings.
Windows will also look for updated policies and apply them periodically, typically every 90 minutes.[27]
Through its scope a policy defines which machines and/or users the policy is to be applied to. Whether a machine or user is within the scope of a policy or not is defined by a set of rules which can filter on the location of the machine or user account in organizational directory, specific users or machine accounts or security groups. More advanced rules can be set up using Windows Management Instrumentation expressions. Such rules can filter on properties such as computer vendor name, CPU architecture, installed software, or networks connected to.
For instance, the administrator can create a policy with one set of registry settings for machines in the accounting department and policy with another (lock-down) set of registry settings for kiosk terminals in the visitors area. When a machine is moved from one scope to another (e.g. changing its name or moving it to another organizational unit), the correct policy is automatically applied. When a policy is changed it is automatically re-applied to all machines currently in its scope.
The policy is edited through a number of administrative templates which provides a user interface for picking and changing settings. The set of administrative templates is extensible and software packages which support such remote administration can register their own templates.
Command line editing[edit]
| Developer(s) | Microsoft |
|---|---|
| Operating system | Microsoft Windows |
| Type | Command |
| License | Proprietary commercial software |
| Website | docs.microsoft.com/en-us/windows-server/administration/windows-commands/reg |
| Developer(s) | Microsoft |
|---|---|
| Operating system | Microsoft Windows |
| Type | Command |
| License | Proprietary commercial software |
| Website | docs.microsoft.com/en-us/windows-server/administration/windows-commands/regini |
The registry can be manipulated in a number of ways from the command line. The Reg.exe and RegIni.exe utility tools are included in Windows XP and later versions of Windows. Alternative locations for legacy versions of Windows include the Resource Kit CDs or the original Installation CD of Windows.
Also, a .REG file can be imported from the command line with the following command:
RegEdit.exe /s file
The /s means the file will be silent merged to the registry. If the /s parameter is omitted the user will be asked to confirm the operation. In Windows 98, Windows 95 and at least some configurations of Windows XP the /s switch also causes RegEdit.exe to ignore the setting in the registry that allows administrators to disable it. When using the /s switch RegEdit.exe does not return an appropriate return code if the operation fails, unlike Reg.exe which does.
RegEdit.exe /e file
exports the whole registry in V5 format to a UNICODE .REG file, while any of
RegEdit.exe /e file HKEY_CLASSES_ROOT[<key>] RegEdit.exe /e file HKEY_CURRENT_CONFIG[<key>] RegEdit.exe /e file HKEY_CURRENT_USER[<key>] RegEdit.exe /e file HKEY_LOCAL_MACHINE[<key>] RegEdit.exe /e file HKEY_USERS[<key>]
export the specified (sub)key (which has to be enclosed in quotes if it contains spaces) only.
RegEdit.exe /a file
exports the whole registry in V4 format to an ANSI .REG file.
RegEdit.exe /a file <key>
exports the specified (sub)key (which has to be enclosed in quotes if it contains spaces) only.
It is also possible to use Reg.exe. Here is a sample to display the value of the registry value Version:
Reg.exe QUERY HKLMSoftwareMicrosoftResKit /v Version
Other command line options include a VBScript or JScript together with CScript, WMI or WMIC.exe and Windows PowerShell.
Registry permissions can be manipulated through the command line using RegIni.exe and the SubInACL.exe tool. For example, the permissions on the HKEY_LOCAL_MACHINESOFTWARE key can be displayed using:
SubInACL.exe /keyreg HKEY_LOCAL_MACHINESOFTWARE /display
PowerShell commands and scripts[edit]
Using PowerShell to navigate the registry
Windows PowerShell comes with a registry provider which presents the registry as a location type similar to the file system. The same commands used to manipulate files and directories in the file system can be used to manipulate keys and values of the registry.[28]
Also like the file system, PowerShell uses the concept of a current location which defines the context on which commands by default operate. The Get-ChildItem (also available through the aliases ls, dir or gci) retrieves the child keys of the current location. By using the Set-Location (or the alias cd) command the user can change the current location to another key of the registry.[28] Commands which rename items, remove items, create new items or set content of items or properties can be used to rename keys, remove keys or entire sub-trees or change values.
Through PowerShell scripts files, an administrator can prepare scripts which, when executed, make changes to the registry. Such scripts can be distributed to administrators who can execute them on individual machines. The PowerShell Registry provider supports transactions, i.e. multiple changes to the registry can be bundled into a single atomic transaction. An atomic transaction ensures that either all of the changes are committed to the database, or if the script fails, none of the changes are committed to the database.[28][29]
Programs or scripts[edit]
The registry can be edited through the APIs of the Advanced Windows 32 Base API Library (advapi32.dll).[30] List of registry API functions:
- RegCloseKey
- RegConnectRegistry
- RegCreateKey
- RegCreateKeyEx
- RegDeleteKey
- RegDeleteValue
- RegEnumKey
- RegEnumKeyEx
- RegEnumValue
- RegFlushKey
- RegGetKeySecurity
- RegLoadKey
- RegNotifyChangeKeyValue
- RegOpenKey
- RegOpenKeyEx
- RegQueryInfoKey
- RegQueryMultipleValues
- RegQueryValue
- RegQueryValueEx
- RegReplaceKey
- RegRestoreKey
- RegSaveKey
- RegSetKeySecurity
- RegSetValue
- RegSetValueEx
- RegUnLoadKey
Many programming languages offer built-in runtime library functions or classes that wrap the underlying Windows APIs and thereby enable programs to store settings in the registry (e.g. Microsoft.Win32.Registry in VB.NET and C#, or TRegistry in Delphi and Free Pascal). COM-enabled applications like Visual Basic 6 can use the WSH WScript.Shell object. Another way is to use the Windows Resource Kit Tool, Reg.exe by executing it from code,[31] although this is considered poor programming practice.
Similarly, scripting languages such as Perl (with Win32::TieRegistry), Python (with winreg), TCL (which comes bundled with the registry package),[32] Windows Powershell and Windows Scripting Host also enable registry editing from scripts.
Offline editing[edit]
The offreg.dll[33] available from the Windows Driver Kit offers a set of APIs for the creation and manipulation of currently not loaded registry hives similar to those provided by advapi32.dll.
It is also possible to edit the registry (hives) of an offline system from Windows PE or Linux (in the latter case using open source tools).
COM self-registration[edit]
Prior to the introduction of registration-free COM, developers were encouraged to add initialization code to in-process and out-of-process binaries to perform the registry configuration required for that object to work. For in-process binaries such as .DLL and .OCX files, the modules typically exported a function called DllInstall()[34] that could be called by installation programs or invoked manually with utilities like Regsvr32.exe;[35] out-of-process binaries typically support the commandline arguments /Regserver and /Unregserver that created or deleted the required registry settings.[36] COM applications that break because of DLL Hell issues can commonly be repaired with RegSvr32.exe or the /RegServer switch without having to re-invoke installation programs.[37]
Advanced functionality[edit]
Windows exposes APIs that allows user-mode applications to register to receive a notification event if a particular registry key is changed.[38] APIs are also available to allow kernel-mode applications to filter and modify registry calls made by other applications.[39]
Windows also supports remote access to the registry of another computer via the RegConnectRegistry function[40] if the Remote Registry service is running, correctly configured and its network traffic is not firewalled.[41]
Security[edit]
Each key in the registry of Windows NT versions can have an associated security descriptor. The security descriptor contains an access control list (ACL) that describes which user groups or individual users are granted or denied access permissions. The set of registry permissions include 10 rights/permissions which can be explicitly allowed or denied to a user or a group of users.
| Permission | Description |
|---|---|
| Query Value | The right to read the registry key value. |
| Set Value | The right to write a new value |
| Create Subkey | The right to create subkeys. |
| Enumerate Subkeys | Allow the enumeration of subkeys. |
| Notify | The right to request change notifications for registry keys or subkeys. |
| Create Link | Reserved by the operating system. |
| Delete | The right to delete a key. |
| Write DACL | The right to modify permissions of the container’s DACL. |
| Write Owner | The right to modify the container’s owner. |
| Read Control | The right to read the DACL. |
As with other securable objects in the operating system, individual access control entries (ACE) on the security descriptor can be explicit or inherited from a parent object.[42]
Windows Resource Protection is a feature of Windows Vista and later versions of Windows that uses security to deny Administrators and the system WRITE access to some sensitive keys to protect the integrity of the system from malware and accidental modification.[43]
Special ACEs on the security descriptor can also implement mandatory integrity control for the registry key and subkeys. A process running at a lower integrity level cannot write, change or delete a registry key/value, even if the account of the process has otherwise been granted access through the ACL. For instance, Internet Explorer running in Protected Mode can read medium and low integrity registry keys/values of the currently logged on user, but it can only modify low integrity keys.[44]
Outside security, registry keys cannot be deleted or edited due to other causes. Registry keys containing NUL characters cannot be deleted with standard registry editors and require a special utility for deletion, such as RegDelNull.[45][46]
Backups and recovery[edit]
Different editions of Windows have supported a number of different methods to back up and restore the registry over the years, some of which are now deprecated:
- System Restore can back up the registry and restore it as long as Windows is bootable, or from the Windows Recovery Environment (starting with Windows Vista).
- NTBackup can back up the registry as part of the System State and restore it. Automated System Recovery in Windows XP can also restore the registry.
- On Windows NT, the Last Known Good Configuration option in startup menu relinks the
HKLMSYSTEMCurrentControlSetkey, which stores hardware and device driver information. - Windows 98 and Windows ME include command line (Scanreg.exe) and GUI (Scanregw.exe) registry checker tools to check and fix the integrity of the registry, create up to five automatic regular backups by default and restore them manually or whenever corruption is detected.[47] The registry checker tool backs up the registry, by default, to
%Windir%SysbckupScanreg.exe can also run from MS-DOS.[48] - The Windows 95 CD-ROM included an Emergency Recovery Utility (ERU.exe) and a Configuration Backup Tool (Cfgback.exe) to back up and restore the registry. Additionally Windows 95 backs up the registry to the files system.da0 and user.da0 on every successful boot.
- Windows NT 4.0 included
RDISK.EXE, a utility to back up and restore the entire registry.[49] - Windows 2000 Resource Kit contained an unsupported pair of utilities called Regback.exe and RegRest.exe for backup and recovery of the registry.[50]
- Periodic automatic backups of the registry are now disabled by default on Windows 10 May 2019 Update (version 1903). Microsoft recommends System Restore be used instead.[51]
Policy[edit]
Group policy[edit]
Windows 2000 and later versions of Windows use Group Policy to enforce registry settings through a registry-specific client extension in the Group Policy processing engine.[52] Policy may be applied locally to a single computer using gpedit.msc, or to multiple users and/or computers in a domain using gpmc.msc.
Legacy systems[edit]
With Windows 95, Windows 98, Windows ME and Windows NT 4.0, administrators can use a special file to be merged into the registry, called a policy file (POLICY.POL). The policy file allows administrators to prevent non-administrator users from changing registry settings like, for instance, the security level of Internet Explorer and the desktop background wallpaper. The policy file is primarily used in a business with a large number of computers where the business needs to be protected from rogue or careless users.
The default extension for the policy file is .POL.
The policy file filters the settings it enforces by user and by group (a «group» is a defined set of users). To do that the policy file merges into the registry, preventing users from circumventing it by simply changing back the settings.
The policy file is usually distributed through a LAN, but can be placed on the local computer.
The policy file is created by a free tool by Microsoft that goes by the filename poledit.exe for Windows 95/Windows 98 and with a computer management module for Windows NT. The editor requires administrative permissions to be run on systems that uses permissions.
The editor can also directly change the current registry settings of the local computer and if the remote registry service is installed and started on another computer it can also change the registry on that computer.
The policy editor loads the settings it can change from .ADM files, of which one is included, that contains the settings the Windows shell provides. The .ADM file is plain text and supports easy localisation by allowing all the strings to be stored in one place.
Virtualization[edit]
INI file virtualization[edit]
Windows NT kernels support redirection of INI file-related APIs into a virtual file in a registry location such as HKEY_CURRENT_USER using a feature called «InifileMapping».[53] This functionality was introduced to allow legacy applications written for 16-bit versions of Windows to be able to run under Windows NT platforms on which the System folder is no longer considered an appropriate location for user-specific data or configuration. Non-compliant 32-bit applications can also be redirected in this manner, even though the feature was originally intended for 16-bit applications.
Registry virtualization[edit]
Windows Vista introduced limited registry virtualization, whereby poorly written applications that do not respect the principle of least privilege and instead try to write user data to a read-only system location (such as the HKEY_LOCAL_MACHINE hive), are silently redirected to a more appropriate location, without changing the application itself.
Similarly, application virtualization redirects all of an application’s invalid registry operations to a location such as a file. Used together with file virtualization, this allows applications to run on a machine without being installed on it.
Low integrity processes may also use registry virtualization. For example, Internet Explorer 7 or 8 running in «Protected Mode» on Windows Vista and above will automatically redirect registry writes by ActiveX controls to a sandboxed location in order to frustrate some classes of security exploits.
The Application Compatibility Toolkit[54] provides shims that can transparently redirect HKEY_LOCAL_MACHINE or HKEY_CLASSES_ROOT Registry operations to HKEY_CURRENT_USER to address «LUA» bugs that cause applications not to work for users with insufficient rights.
Disadvantages[edit]
Critics labeled the registry in Windows 95 a single point of failure, because re-installation of the operating system was required if the registry became corrupt.[citation needed] However, Windows NT uses transaction logs to protect against corruption during updates. Current versions of Windows use two levels of log files to ensure integrity even in the case of power failure or similar catastrophic events during database updates.[55] Even in the case of a non-recoverable error, Windows can repair or re-initialize damaged registry entries during system boot.[55]
Equivalents and alternatives[edit]
In Windows, use of the registry for storing program data is a matter of developer’s discretion. Microsoft provides programming interfaces for storing data in XML files (via MSXML) or database files (via SQL Server Compact) which developers can use instead. Developers are also free to use non-Microsoft alternatives or develop their own proprietary data stores.
In contrast to Windows Registry’s binary-based database model, some other operating systems use separate plain-text files for daemon and application configuration, but group these configurations together for ease of management.
- In Unix-like operating systems (including Linux) that follow the Filesystem Hierarchy Standard, system-wide configuration files (information similar to what would appear in HKEY_LOCAL_MACHINE on Windows) are traditionally stored in files in
/etc/and its subdirectories, or sometimes in/usr/local/etc. Per-user information (information that would be roughly equivalent to that in HKEY_CURRENT_USER) is stored in hidden directories and files (that start with a period/full stop) within the user’s home directory. However XDG-compliant applications should refer to the environment variables defined in the Base Directory specification.[56] - In macOS, system-wide configuration files are typically stored in the
/Library/folder, whereas per-user configuration files are stored in the corresponding~/Library/folder in the user’s home directory, and configuration files set by the system are in/System/Library/. Within these respective directories, an application typically stores a property list file in thePreferences/sub-directory. - RISC OS (not to be confused with MIPS RISC/os) uses directories for configuration data, which allows applications to be copied into application directories, as opposed to the separate installation process that typifies Windows applications; this approach is also used on the ROX Desktop for Linux.[57] This directory-based configuration also makes it possible to use different versions of the same application, since the configuration is done «on the fly».[58] If one wishes to remove the application, it is possible to simply delete the folder belonging to the application.[59][60] This will often not remove configuration settings which are stored independently from the application, usually within the computer’s !Boot structure, in !Boot.Choices or potentially anywhere on a network fileserver. It is possible to copy installed programs between computers running RISC OS by copying the application directories belonging to the programs, however some programs may require re-installing, e.g. when shared files are placed outside an application directory.[58]
- IBM AIX (a Unix variant) uses a registry component called Object Data Manager (ODM). The ODM is used to store information about system and device configuration. An extensive set of tools and utilities provides users with means of extending, checking, correcting the ODM database. The ODM stores its information in several files, default location is
/etc/objrepos. - The GNOME desktop environment uses a registry-like interface called dconf for storing configuration settings for the desktop and applications.
- The Elektra Initiative provides alternative back-ends for various different text configuration files.
- While not an operating system, the Wine compatibility layer, which allows Windows software to run on a Unix-like system, also employs a Windows-like registry as text files in the WINEPREFIX folder: system.reg (HKEY_LOCAL_MACHINE), user.reg (HKEY_CURRENT_USER) and userdef.reg.[61]
See also[edit]
- Registry cleaner
- Application virtualization
- LogParser – SQL-like querying of various types of log files
- List of Shell Icon Overlay Identifiers
- Ransomware attack that uses Registry
Notes[edit]
- ^ When applications fail to execute because they request more privileges than they require (and are denied those privileges), this is known as a limited user application (LUA) bug.
Footnotes[edit]
- ^ Esposito, Dino (November 2000). «Windows 2000 Registry: Latest Features and APIs Provide the Power to Customize and Extend Your Apps». MSDN Magazine. Microsoft. Archived from the original on April 15, 2003. Retrieved July 19, 2007.
- ^ a b c «The System Registry».
- ^ «Windows 95 Architecture Components». www.microsoft.com. Archived from the original on February 7, 2008. Retrieved April 29, 2008.
The following table shows other difficulties or limitations caused by using .INI files that are overcome by using the Registry.
- ^ Hipson 2002, p. 5, 41–43.
- ^ Richter, Jeffrey; Nasarre, Christophe (2008). Windows Via C/C++ (Fifth ed.). Microsoft Press. ISBN 9780735642461. Retrieved August 28, 2021.
- ^ Raymond Chen, «Why do registry keys have a default value?»
- ^ Hipson 2002, pp. 207, 513–514.
- ^ Hipson 2002, pp. 520–521.
- ^ Hipson 2002, p. 7.
- ^ «Designed for Windows XP Application Specification». Microsoft. August 20, 2002. Retrieved April 8, 2009.
- ^ «HKEY_LOCAL_MACHINE». Gautam. 2009. Retrieved April 8, 2009.
- ^ «Registry Keys Affected by WOW64 (Windows)». Msdn.microsoft.com. Retrieved April 10, 2014.
- ^ «Description of the Microsoft Windows registry». Retrieved September 25, 2008.
- ^ «HKEY_CURRENT_USER». Microsoft. 2009. Retrieved April 8, 2009.
- ^ «Description of the HKEY_DYN_DATA Registry Key in Windows 95, Windows 98, and Windows 98 SE». support.microsoft.com.
- ^ «A Closer Look at HKEY_DYN_DATA». rinet.ru. Archived from the original on May 9, 2008.
- ^ «Registry hives». Retrieved July 19, 2007.
- ^ Chen, Raymond (August 8, 2011). «Why is a registry file called a «hive»?». The Old New Thing. Retrieved July 29, 2011.
- ^ «Overview of the Windows NT Registry». Retrieved December 2, 2011.
- ^ «Inside the Registry». Retrieved December 28, 2007.
- ^ a b Norris, Peter (February 2009). «The Internal Structure of the Windows Registry» (PDF). Cranfield University. Archived from the original (PDF) on May 29, 2009.
- ^ «Incorrect Icons Displayed for .ico Files». November 15, 2009. Retrieved March 31, 2012.
- ^ «How to Completely Uninstall / Remove a Software Program in Windows without using 3rd Party Software? — AskVG». www.askvg.com. August 26, 2011.
- ^ «You may receive a «STOP 0x00000035 NO_MORE_IRP_STACK_LOCATIONS» error message when you try to log on to a domain». October 9, 2011. Retrieved March 31, 2012. This page tells the user to edit the registry when resolving the issue.
- ^ key renaming is implemented as removal and add while retaining subkeys/values, as the underlying APIs do not support the rename function directly
- ^ a b c d «How to add, modify, or delete registry subkeys and values by using a .reg file». support.microsoft.com.
- ^ «Applying Group Policy». Microsoft.
- ^ a b c Payette, Bruce; Siddaway, Richard (2018). Windows PowerShell in Action (Third ed.). Manning Publications. pp. 7–8, 24, 608, 708–710. ISBN 9781633430297. Retrieved August 28, 2021.
- ^ Warner, Timothy L. (May 2015). Windows PowerShell in 24 Hours, Sams Teach Yourself. Sams Publishing. p. 19, 211. ISBN 9780134049359. Retrieved August 28, 2021.
- ^ «Reading and Writing Registry Values with Visual Basic». Retrieved July 19, 2007.
- ^ «REG command in Windows XP». Retrieved July 19, 2007.
- ^ «registry manual page – Tcl Bundled Packages». www.tcl.tk. Retrieved December 14, 2017.
- ^ «Offline Registry Library». Retrieved June 4, 2014.
- ^ «DllInstall Function». Microsoft. March 7, 2012. Retrieved March 22, 2012.
- ^ «Regsvr32». Microsoft. Retrieved March 22, 2012.
- ^ «How to: Register Automation Servers». Microsoft. Retrieved March 22, 2012.
- ^ «How to re-register PowerPoint 2000, PowerPoint 2003, PowerPoint 2007 and PowerPoint 2010». Microsoft. January 2012. Retrieved March 22, 2012.
- ^ «RegNotifyChangeKeyValue function». Microsoft.
- ^ «Registering for Notifications». Microsoft.
- ^ «RegConnectRegistry function». Microsoft.
- ^ «How to Manage Remote Access to the Registry». Microsoft.
- ^ Gibson, Darril (June 28, 2011). «Chapter 4: Securing Access with Permissions». Microsoft Windows security : essentials. Indianapolis, Ind.: Wiley. ISBN 978-1-118-01684-8.
- ^ «Application Compatibility: Windows Resource Protection (WRP)». Microsoft. Retrieved August 8, 2012.
- ^ Marc Silbey, Peter Brundrett. «Understanding and Working in Protected Mode Internet Explorer». Retrieved August 8, 2012.
- ^ «RegDelNull v1.1». November 1, 2006. Retrieved August 8, 2012.
- ^ «Unable to delete certain registry keys – Error while deleting key». March 23, 2010. Retrieved August 8, 2012. Microsoft Support page.
- ^ «Description of the Windows Registry Checker Tool (Scanreg.exe)».
- ^ «Command-Line Switches for the Registry Checker Tool».
- ^ «How To Backup, Edit, and Restore the Registry in Windows NT 4.0». support.microsoft.com.
- ^ «Technical Reference to the Registry: Related Resources». Microsoft. Retrieved September 9, 2011.
- ^ «Microsoft Kills Automatic Registry Backups in Windows 10». ExtremeTech. Retrieved July 1, 2019.
- ^ «How Core Group Policy Works». Microsoft. September 2, 2009. Retrieved August 13, 2012.
- ^ «Chapter 26 – Initialization Files and the Registry». Microsoft. Retrieved March 3, 2008.
- ^ «Microsoft Application Compatibility Toolkit 5.0». Microsoft. Retrieved July 26, 2008.
- ^ a b Ionescu, Mark Russinovich, David A. Solomon, Alex (2012). «Registry Internals». Windows internals (6th ed.). Redmond, Wash.: Microsoft Press. ISBN 978-0-7356-4873-9.
- ^ «XDG Base Directory Specification». standards.freedesktop.org.
- ^ «Application directories». Archived from the original on May 27, 2012. Retrieved May 17, 2012.
- ^ a b «Case Studies Of The Top 132 Annoyances With Operating Systems Other Than RISC OS». Retrieved April 3, 2012. Page from the riscos.com website. Mentioned in points 82 and 104.
- ^ «RISC OS tour». Retrieved July 19, 2007.
- ^ «The RISC OS Products Directory». November 2, 2006. Archived from the original on February 19, 2007. Retrieved April 1, 2012.
- ^ 3.2. Using the Registry and Regedit (Wine User Guide)
References[edit]
- Hipson, Peter (2002). Mastering Windows XP Registry. Wiley. ISBN 0-7821-2987-0. Retrieved August 28, 2021.
- Russinovich, Mark E.; Solomon, David A. (2005). Microsoft Windows Internals (Fourth ed.). Microsoft Press. pp. 183–236. ISBN 978-0-7356-1917-3.
External links[edit]
- Windows Registry info & reference in the MSDN Library
Registry Editor, the user interface for the registry, in Windows 11 |
|
| Developer(s) | Microsoft |
|---|---|
| Initial release | April 6, 1992; 30 years ago with Windows 3.1 |
| Operating system | Microsoft Windows |
| Platform | IA-32, x86-64 and ARM (and historically DEC Alpha, Itanium, MIPS, and PowerPC) |
| Included with | Microsoft Windows |
| Type | Hierarchical database |
| Website | docs.microsoft.com/en-us/windows/desktop/SysInfo/registry |
The Windows Registry is a hierarchical database that stores low-level settings for the Microsoft Windows operating system and for applications that opt to use the registry. The kernel, device drivers, services, Security Accounts Manager, and user interfaces can all use the registry. The registry also allows access to counters for profiling system performance.
In other words, the registry or Windows Registry contains information, settings, options, and other values for programs and hardware installed on all versions of Microsoft Windows operating systems. For example, when a program is installed, a new subkey containing settings such as a program’s location, its version, and how to start the program, are all added to the Windows Registry.
When introduced with Windows 3.1, the Windows Registry primarily stored configuration information for COM-based components. Windows 95 and Windows NT extended its use to rationalize and centralize the information in the profusion of INI files, which held the configurations for individual programs, and were stored at various locations.[1][2] It is not a requirement for Windows applications to use the Windows Registry. For example, .NET Framework applications use XML files for configuration, while portable applications usually keep their configuration files with their executables.
Rationale[edit]
Prior to the Windows Registry, .INI files stored each program’s settings as a text file or binary file, often located in a shared location that did not provide user-specific settings in a multi-user scenario. By contrast, the Windows Registry stores all application settings in one logical repository (but a number of discrete files) and in a standardized form. According to Microsoft, this offers several advantages over .INI files.[2][3] Since file parsing is done much more efficiently with a binary format, it may be read from or written to more quickly than a text INI file. Furthermore, strongly typed data can be stored in the registry, as opposed to the text information stored in .INI files. This is a benefit when editing keys manually using regedit.exe, the built-in Windows Registry Editor. Because user-based registry settings are loaded from a user-specific path rather than from a read-only system location, the registry allows multiple users to share the same machine, and also allows programs to work for less privileged users. Backup and restoration is also simplified as the registry can be accessed over a network connection for remote management/support, including from scripts, using the standard set of APIs, as long as the Remote Registry service is running and firewall rules permit this.
Because the registry is a database, it offers improved system integrity with features such as atomic updates. If two processes attempt to update the same registry value at the same time, one process’s change will precede the other’s and the overall consistency of the data will be maintained. Where changes are made to .INI files, such race conditions can result in inconsistent data that does not match either attempted update. Windows Vista and later operating systems provide transactional updates to the registry by means of the Kernel Transaction Manager, extending the atomicity guarantees across multiple key and/or value changes, with traditional commit–abort semantics. (Note however that NTFS provides such support for the file system as well, so the same guarantees could, in theory, be obtained with traditional configuration files.)
Structure[edit]
Keys and values[edit]
The registry contains two basic elements: keys and values. Registry keys are container objects similar to folders. Registry values are non-container objects similar to files. Keys may contain values and subkeys. Keys are referenced with a syntax similar to Windows’ path names, using backslashes to indicate levels of hierarchy. Keys must have a case insensitive name without backslashes.
The hierarchy of registry keys can only be accessed from a known root key handle (which is anonymous but whose effective value is a constant numeric handle) that is mapped to the content of a registry key preloaded by the kernel from a stored «hive», or to the content of a subkey within another root key, or mapped to a registered service or DLL that provides access to its contained subkeys and values.
E.g. HKEY_LOCAL_MACHINESoftwareMicrosoftWindows refers to the subkey «Windows» of the subkey «Microsoft» of the subkey «Software» of the HKEY_LOCAL_MACHINE root key.
There are seven predefined root keys, traditionally named according to their constant handles defined in the Win32 API, or by synonymous abbreviations (depending on applications):[4]
- HKEY_LOCAL_MACHINE or HKLM
- HKEY_CURRENT_CONFIG or HKCC
- HKEY_CLASSES_ROOT or HKCR
- HKEY_CURRENT_USER or HKCU
- HKEY_USERS or HKU
- HKEY_PERFORMANCE_DATA (only in Windows NT, but invisible in the Windows Registry Editor)[5]
- HKEY_DYN_DATA (only in Windows 9x, and visible in the Windows Registry Editor)
Like other files and services in Windows, all registry keys may be restricted by access control lists (ACLs), depending on user privileges, or on security tokens acquired by applications, or on system security policies enforced by the system (these restrictions may be predefined by the system itself, and configured by local system administrators or by domain administrators). Different users, programs, services or remote systems may only see some parts of the hierarchy or distinct hierarchies from the same root keys.
Registry values are name/data pairs stored within keys. Registry values are referenced separately from registry keys. Each registry value stored in a registry key has a unique name whose letter case is not significant. The Windows API functions that query and manipulate registry values take value names separately from the key path and/or handle that identifies the parent key. Registry values may contain backslashes in their names, but doing so makes them difficult to distinguish from their key paths when using some legacy Windows Registry API functions (whose usage is deprecated in Win32).
The terminology is somewhat misleading, as each registry key is similar to an associative array, where standard terminology would refer to the name part of each registry value as a «key». The terms are a holdout from the 16-bit registry in Windows 3, in which registry keys could not contain arbitrary name/data pairs, but rather contained only one unnamed value (which had to be a string). In this sense, the Windows 3 registry was like a single associative array, in which the keys (in the sense of both ‘registry key’ and ‘associative array key’) formed a hierarchy, and the registry values were all strings. When the 32-bit registry was created, so was the additional capability of creating multiple named values per key, and the meanings of the names were somewhat distorted.[6] For compatibility with the previous behavior, each registry key may have a «default» value, whose name is the empty string.
Each value can store arbitrary data with variable length and encoding, but which is associated with a symbolic type (defined as a numeric constant) defining how to parse this data. The standard types are:[7]
| Type ID | Symbolic type name | Meaning and encoding of the data stored in the registry value |
|---|---|---|
| 0 | REG_NONE | No type (the stored value, if any) |
| 1 | REG_SZ | A string value, normally stored and exposed in UTF-16LE (when using the Unicode version of Win32 API functions), usually terminated by a NUL character |
| 2 | REG_EXPAND_SZ | An «expandable» string value that can contain environment variables, normally stored and exposed in UTF-16LE, usually terminated by a NUL character |
| 3 | REG_BINARY | Binary data (any arbitrary data) |
| 4 | REG_DWORD / REG_DWORD_LITTLE_ENDIAN | A DWORD value, a 32-bit unsigned integer (numbers between 0 and 4,294,967,295 [232 – 1]) (little-endian) |
| 5 | REG_DWORD_BIG_ENDIAN | A DWORD value, a 32-bit unsigned integer (numbers between 0 and 4,294,967,295 [232 – 1]) (big-endian) |
| 6 | REG_LINK | A symbolic link (UNICODE) to another registry key, specifying a root key and the path to the target key |
| 7 | REG_MULTI_SZ | A multi-string value, which is an ordered list of non-empty strings, normally stored and exposed in Unicode, each one terminated by a null character, the list being normally terminated by a second null character.[8] |
| 8 | REG_RESOURCE_LIST | A resource list (used by the Plug-n-Play hardware enumeration and configuration) |
| 9 | REG_FULL_RESOURCE_DESCRIPTOR | A resource descriptor (used by the Plug-n-Play hardware enumeration and configuration) |
| 10 | REG_RESOURCE_REQUIREMENTS_LIST | A resource requirements list (used by the Plug-n-Play hardware enumeration and configuration) |
| 11 | REG_QWORD / REG_QWORD_LITTLE_ENDIAN | A QWORD value, a 64-bit integer (either big- or little-endian, or unspecified) (introduced in Windows 2000)[9] |
Root keys[edit]
The keys at the root level of the hierarchical database are generally named by their Windows API definitions, which all begin «HKEY».[2] They are frequently abbreviated to a three- or four-letter short name starting with «HK» (e.g. HKCU and HKLM). Technically, they are predefined handles (with known constant values) to specific keys that are either maintained in memory, or stored in hive files stored in the local filesystem and loaded by the system kernel at boot time and then shared (with various access rights) between all processes running on the local system, or loaded and mapped in all processes started in a user session when the user logs on the system.
The HKEY_LOCAL_MACHINE (local machine-specific configuration data) and HKEY_CURRENT_USER (user-specific configuration data) nodes have a similar structure to each other; user applications typically look up their settings by first checking for them in «HKEY_CURRENT_USERSoftwareVendor’s nameApplication’s nameVersionSetting name», and if the setting is not found, look instead in the same location under the HKEY_LOCAL_MACHINE key[citation needed]. However, the converse may apply for administrator-enforced policy settings where HKLM may take precedence over HKCU. The Windows Logo Program has specific requirements for where different types of user data may be stored, and that the concept of least privilege be followed so that administrator-level access is not required to use an application.[a][10]
HKEY_LOCAL_MACHINE (HKLM)[edit]
Abbreviated HKLM, HKEY_LOCAL_MACHINE stores settings that are specific to the local computer.[11]
The key located by HKLM is actually not stored on disk, but maintained in memory by the system kernel in order to map all the other subkeys. Applications cannot create any additional subkeys. On Windows NT, this key contains four subkeys, «SAM», «SECURITY», «SYSTEM», and «SOFTWARE», that are loaded at boot time within their respective files located in the %SystemRoot%System32config folder. A fifth subkey, «HARDWARE», is volatile and is created dynamically, and as such is not stored in a file (it exposes a view of all the currently detected Plug-and-Play devices). On Windows Vista and above, a sixth and seventh subkey, «COMPONENTS» and «BCD», are mapped in memory by the kernel on-demand and loaded from %SystemRoot%system32configCOMPONENTS or from boot configuration data, bootBCD on the system partition.
- The «HKLMSAM» key usually appears as empty for most users (unless they are granted access by administrators of the local system or administrators of domains managing the local system). It is used to reference all «Security Accounts Manager» (SAM) databases for all domains into which the local system has been administratively authorized or configured (including the local domain of the running system, whose SAM database is stored in a subkey also named «SAM»: other subkeys will be created as needed, one for each supplementary domain). Each SAM database contains all builtin accounts (mostly group aliases) and configured accounts (users, groups and their aliases, including guest accounts and administrator accounts) created and configured on the respective domain, for each account in that domain, it notably contains the user name which can be used to log on that domain, the internal unique user identifier in the domain, a cryptographic hash of each user’s password for each enabled authentication protocol, the location of storage of their user registry hive, various status flags (for example if the account can be enumerated and be visible in the logon prompt screen), and the list of domains (including the local domain) into which the account was configured.
- The «HKLMSECURITY» key usually appears empty for most users (unless they are granted access by users with administrative privileges) and is linked to the Security database of the domain into which the current user is logged on (if the user is logged on the local system domain, this key will be linked to the registry hive stored by the local machine and managed by local system administrators or by the builtin «System» account and Windows installers). The kernel will access it to read and enforce the security policy applicable to the current user and all applications or operations executed by this user. It also contains a «SAM» subkey which is dynamically linked to the SAM database of the domain onto which the current user is logged on.
- The «HKLMSYSTEM» key is normally only writable by users with administrative privileges on the local system. It contains information about the Windows system setup, data for the secure random number generator (RNG), the list of currently mounted devices containing a filesystem, several numbered «HKLMSYSTEMControl Sets» containing alternative configurations for system hardware drivers and services running on the local system (including the currently used one and a backup), a «HKLMSYSTEMSelect» subkey containing the status of these Control Sets, and a «HKLMSYSTEMCurrentControlSet» which is dynamically linked at boot time to the Control Set which is currently used on the local system. Each configured Control Set contains:
- an «Enum» subkey enumerating all known Plug-and-Play devices and associating them with installed system drivers (and storing the device-specific configurations of these drivers),
- a «Services» subkey listing all installed system drivers (with non device-specific configuration, and the enumeration of devices for which they are instantiated) and all programs running as services (how and when they can be automatically started),
- a «Control» subkey organizing the various hardware drivers and programs running as services and all other system-wide configuration,
- a «Hardware Profiles» subkey enumerating the various profiles that have been tuned (each one with «System» or «Software» settings used to modify the default profile, either in system drivers and services or in the applications) as well as the «Hardware ProfilesCurrent» subkey which is dynamically linked to one of these profiles.
- The «HKLMSOFTWARE» subkey contains software and Windows settings (in the default hardware profile). It is mostly modified by application and system installers. It is organized by software vendor (with a subkey for each), but also contains a «Windows» subkey for some settings of the Windows user interface, a «Classes» subkey containing all registered associations from file extensions, MIME types, Object Classes IDs and interfaces IDs (for OLE, COM/DCOM and ActiveX), to the installed applications or DLLs that may be handling these types on the local machine (however these associations are configurable for each user, see below), and a «Policies» subkey (also organized by vendor) for enforcing general usage policies on applications and system services (including the central certificates store used for authenticating, authorizing or disallowing remote systems or services running outside the local network domain).
- The «HKLMSOFTWAREWow6432Node» key is used by 32-bit applications on a 64-bit Windows OS, and is equivalent to but separate from «HKLMSOFTWARE». The key path is transparently presented to 32-bit applications by WoW64 as HKLMSOFTWARE[12] (in a similar way that 32-bit applications see %SystemRoot%Syswow64 as %SystemRoot%System32)
HKEY_CLASSES_ROOT (HKCR)[edit]
- Abbreviated HKCR, HKEY_CLASSES_ROOT contains information about registered applications, such as file associations and OLE Object Class IDs, tying them to the applications used to handle these items. On Windows 2000 and above, HKCR is a compilation of user-based HKCUSoftwareClasses and machine-based HKLMSoftwareClasses. If a given value exists in both of the subkeys above, the one in HKCUSoftwareClasses takes precedence.[13] The design allows for either machine- or user-specific registration of COM objects.
HKEY_USERS (HKU)[edit]
- Abbreviated HKU, HKEY_USERS contains subkeys corresponding to the HKEY_CURRENT_USER keys for each user profile actively loaded on the machine, though user hives are usually only loaded for currently logged-in users.
HKEY_CURRENT_USER (HKCU)[edit]
- Abbreviated HKCU, HKEY_CURRENT_USER stores settings that are specific to the currently logged-in user.[14] The HKEY_CURRENT_USER key is a link to the subkey of HKEY_USERS that corresponds to the user; the same information is accessible in both locations. The specific subkey referenced is «(HKU)(SID)…» where (SID) corresponds to the Windows SID; if the «(HKCU)» key has the following suffix «(HKCU)SoftwareClasses…» then it corresponds to «(HKU)(SID)_CLASSES…» i.e. the suffix has the string «_CLASSES» is appended to the (SID).
- On Windows NT systems, each user’s settings are stored in their own files called NTUSER.DAT and USRCLASS.DAT inside their own Documents and Settings subfolder (or their own Users sub folder in Windows Vista and above). Settings in this hive follow users with a roaming profile from machine to machine.
HKEY_PERFORMANCE_DATA[edit]
- This key provides runtime information into performance data provided by either the NT kernel itself, or running system drivers, programs and services that provide performance data. This key is not stored in any hive and not displayed in the Registry Editor, but it is visible through the registry functions in the Windows API, or in a simplified view via the Performance tab of the Task Manager (only for a few performance data on the local system) or via more advanced control panels (such as the Performances Monitor or the Performances Analyzer which allows collecting and logging these data, including from remote systems).
HKEY_DYN_DATA[edit]
- This key is used only on Windows 95, Windows 98 and Windows ME.[15] It contains information about hardware devices, including Plug and Play and network performance statistics. The information in this hive is also not stored on the hard drive. The Plug and Play information is gathered and configured at startup and is stored in memory.[16]
Hives[edit]
Even though the registry presents itself as an integrated hierarchical database, branches of the registry are actually stored in a number of disk files called hives.[17] (The word hive constitutes an in-joke.)[18]
Some hives are volatile and are not stored on disk at all. An example of this is the hive of the branch starting at HKLMHARDWARE. This hive records information about system hardware and is created each time the system boots and performs hardware detection.
Individual settings for users on a system are stored in a hive (disk file) per user. During user login, the system loads the user hive under the HKEY_USERS key and sets the HKCU (HKEY_CURRENT_USER) symbolic reference to point to the current user. This allows applications to store/retrieve settings for the current user implicitly under the HKCU key.
Not all hives are loaded at any one time. At boot time, only a minimal set of hives are loaded, and after that, hives are loaded as the operating system initializes and as users log in or whenever a hive is explicitly loaded by an application.
File locations[edit]
The registry is physically stored in several files, which are generally obfuscated from the user-mode APIs used to manipulate the data inside the registry. Depending upon the version of Windows, there will be different files and different locations for these files, but they are all on the local machine. The location for system registry files in Windows NT is %SystemRoot%System32Config; the user-specific HKEY_CURRENT_USER user registry hive is stored in Ntuser.dat inside the user profile. There is one of these per user; if a user has a roaming profile, then this file will be copied to and from a server at logout and login respectively. A second user-specific registry file named UsrClass.dat contains COM registry entries and does not roam by default.
Windows NT[edit]
Windows NT systems store the registry in a binary file format which can be exported, loaded and unloaded by the Registry Editor in these operating systems. The following system registry files are stored in %SystemRoot%System32Config:
Sam– HKEY_LOCAL_MACHINESAMSecurity– HKEY_LOCAL_MACHINESECURITYSoftware– HKEY_LOCAL_MACHINESOFTWARESystem– HKEY_LOCAL_MACHINESYSTEMDefault– HKEY_USERS.DEFAULTUserdiff– Not associated with a hive. Used only when upgrading operating systems.[19]
The following file is stored in each user’s profile folder:
%USERPROFILE%Ntuser.dat– HKEY_USERS<User SID> (linked to by HKEY_CURRENT_USER)
For Windows 2000, Server 2003 and Windows XP, the following additional user-specific file is used for file associations and COM information:
%USERPROFILE%Local SettingsApplication DataMicrosoftWindowsUsrclass.dat(path is localized) – HKEY_USERS<User SID>_Classes (HKEY_CURRENT_USERSoftwareClasses)
For Windows Vista and later, the path was changed to:
%USERPROFILE%AppDataLocalMicrosoftWindowsUsrclass.dat(path is not localized) alias%LocalAppData%MicrosoftWindowsUsrclass.dat– HKEY_USERS<User SID>_Classes (HKEY_CURRENT_USERSoftwareClasses)
Windows 2000 keeps an alternate copy of the registry hives (.ALT) and attempts to switch to it when corruption is detected.[20] Windows XP and Windows Server 2003 do not maintain a System.alt hive because NTLDR on those versions of Windows can process the System.log file to bring up to date a System hive that has become inconsistent during a shutdown or crash. In addition, the %SystemRoot%Repair folder contains a copy of the system’s registry hives that were created after installation and the first successful startup of Windows.
Each registry data file has an associated file with a «.log» extension that acts as a transaction log that is used to ensure that any interrupted updates can be completed upon next startup.[21] Internally, Registry files are split into 4 kB «bins» that contain collections of «cells».[21]
Windows 9x[edit]
The registry files are stored in the %WINDIR% directory under the names USER.DAT and SYSTEM.DAT with the addition of CLASSES.DAT in Windows ME. Also, each user profile (if profiles are enabled) has its own USER.DAT file which is located in the user’s profile directory in %WINDIR%Profiles<Username>.
Windows 3.11[edit]
The only registry file is called REG.DAT and it is stored in the %WINDIR% directory.
Windows 10 Mobile[edit]
Note: To access the registry files, the Phone needs to be set in a special mode using either:
- WpInternals ( Put the mobile device into flash mode. )
- InterOp Tools ( mount the MainOS Partition with MTP. )
If any of above Methods worked — The Device Registry Files can be found in the following location:
{Phone}EFIESPWindowsSystem32config
Note: InterOp Tools also includes a registry editor.
Editing[edit]
Registry editors[edit]
The registry contains important configuration information for the operating system, for installed applications as well as individual settings for each user and application. A careless change to the operating system configuration in the registry could cause irreversible damage, so it is usually only installer programs which perform changes to the registry database during installation/configuration and removal. If a user wants to edit the registry manually, Microsoft recommends that a backup of the registry be performed before the change.[22] When a program is removed from control panel, it may not be completely removed and, in case of errors or glitches caused by references to missing programs, the user might have to manually check inside directories such as program files. After this, the user might need to manually remove any reference to the uninstalled program in the registry. This is usually done by using RegEdit.exe.[23] Editing the registry is sometimes necessary when working around Windows-specific issues e.g. problems when logging onto a domain can be resolved by editing the registry.[24]
Windows Registry can be edited manually using programs such as RegEdit.exe, although these tools do not expose some of the registry’s metadata such as the last modified date.
The registry editor for the 3.1/95 series of operating systems is RegEdit.exe and for Windows NT it is RegEdt32.exe; the functionalities are merged in Windows XP. Optional and/or third-party tools similar to RegEdit.exe are available for many Windows CE versions.
Registry Editor allows users to perform the following functions:
- Creating, manipulating, renaming[25] and deleting registry keys, subkeys, values and value data
- Importing and exporting .
REGfiles, exporting data in the binary hive format - Loading, manipulating and unloading registry hive format files (Windows NT systems only)
- Setting permissions based on ACLs (Windows NT systems only)
- Bookmarking user-selected registry keys as Favorites
- Finding particular strings in key names, value names and value data
- Remotely editing the registry on another networked computer
.REG files[edit]
.REG files (also known as Registration entries) are text-based human-readable files for exporting and importing portions of the registry using an INI-based syntax. On Windows 2000 and later, they contain the string Windows Registry Editor Version 5.00 at the beginning and are Unicode-based. On Windows 9x and NT 4.0 systems, they contain the string REGEDIT4 and are ANSI-based.[26] Windows 9x format .REG files are compatible with Windows 2000 and later. The Registry Editor on Windows on these systems also supports exporting .REG files in Windows 9x/NT format. Data is stored in .REG files using the following syntax:[26]
[<Hive name><Key name><Subkey name>] "Value name"=<Value type>:<Value data>
The Default Value of a key can be edited by using «@» instead of «Value Name»:
[<Hive name><Key name><Subkey name>] @=<Value type>:<Value data>
String values do not require a <Value type> (see example), but backslashes (») need to be written as a double-backslash (‘\’), and quotes (‘»‘) as backslash-quote (‘»‘).
For example, to add the values «Value A», «Value B», «Value C», «Value D», «Value E», «Value F», «Value G», «Value H», «Value I», «Value J», «Value K», «Value L», and «Value M» to the HKLMSOFTWAREFoobar key:
Windows Registry Editor Version 5.00 [HKEY_LOCAL_MACHINESOFTWAREFoobar] "Value A"="<String value data with escape characters>" "Value B"=hex:<Binary data (as comma-delimited list of hexadecimal values)> "Value C"=dword:<DWORD value integer> "Value D"=hex(0):<REG_NONE (as comma-delimited list of hexadecimal values)> "Value E"=hex(1):<REG_SZ (as comma-delimited list of hexadecimal values representing a UTF-16LE NUL-terminated string)> "Value F"=hex(2):<Expandable string value data (as comma-delimited list of hexadecimal values representing a UTF-16LE NUL-terminated string)> "Value G"=hex(3):<Binary data (as comma-delimited list of hexadecimal values)> ; equal to "Value B" "Value H"=hex(4):<DWORD value (as comma-delimited list of 4 hexadecimal values, in little endian byte order)> "Value I"=hex(5):<DWORD value (as comma-delimited list of 4 hexadecimal values, in big endian byte order)> "Value J"=hex(7):<Multi-string value data (as comma-delimited list of hexadecimal values representing UTF-16LE NUL-terminated strings)> "Value K"=hex(8):<REG_RESOURCE_LIST (as comma-delimited list of hexadecimal values)> "Value L"=hex(a):<REG_RESOURCE_REQUIREMENTS_LIST (as comma-delimited list of hexadecimal values)> "Value M"=hex(b):<QWORD value (as comma-delimited list of 8 hexadecimal values, in little endian byte order)>
Data from .REG files can be added/merged with the registry by double-clicking these files or using the /s switch in the command line. REG files can also be used to remove registry data.
To remove a key (and all subkeys, values and data), the key name must be preceded by a minus sign («-«).[26]
For example, to remove the HKLMSOFTWAREFoobar key (and all subkeys, values and data),
[-HKEY_LOCAL_MACHINESOFTWAREFoobar]
To remove a value (and its data), the values to be removed must have a minus sign («-«) after the equal sign («=»).[26]
For example, to remove only the «Value A» and «Value B» values (and their data) from the HKLMSOFTWAREFoobar key:
[HKEY_LOCAL_MACHINESOFTWAREFoobar] "Value A"=- "Value B"=-
To remove only the Default value of the key HKLMSOFTWAREFoobar (and its data):
[HKEY_LOCAL_MACHINESOFTWAREFoobar] @=-
Lines beginning with a semicolon are considered comments:
; This is a comment. This can be placed in any part of a .reg file [HKEY_LOCAL_MACHINESOFTWAREFoobar] "Value"="Example string"
Group policies[edit]
Windows group policies can change registry keys for a number of machines or individual users based on policies. When a policy first takes effect for a machine or for an individual user of a machine, the registry settings specified as part of the policy are applied to the machine or user settings.
Windows will also look for updated policies and apply them periodically, typically every 90 minutes.[27]
Through its scope a policy defines which machines and/or users the policy is to be applied to. Whether a machine or user is within the scope of a policy or not is defined by a set of rules which can filter on the location of the machine or user account in organizational directory, specific users or machine accounts or security groups. More advanced rules can be set up using Windows Management Instrumentation expressions. Such rules can filter on properties such as computer vendor name, CPU architecture, installed software, or networks connected to.
For instance, the administrator can create a policy with one set of registry settings for machines in the accounting department and policy with another (lock-down) set of registry settings for kiosk terminals in the visitors area. When a machine is moved from one scope to another (e.g. changing its name or moving it to another organizational unit), the correct policy is automatically applied. When a policy is changed it is automatically re-applied to all machines currently in its scope.
The policy is edited through a number of administrative templates which provides a user interface for picking and changing settings. The set of administrative templates is extensible and software packages which support such remote administration can register their own templates.
Command line editing[edit]
| Developer(s) | Microsoft |
|---|---|
| Operating system | Microsoft Windows |
| Type | Command |
| License | Proprietary commercial software |
| Website | docs.microsoft.com/en-us/windows-server/administration/windows-commands/reg |
| Developer(s) | Microsoft |
|---|---|
| Operating system | Microsoft Windows |
| Type | Command |
| License | Proprietary commercial software |
| Website | docs.microsoft.com/en-us/windows-server/administration/windows-commands/regini |
The registry can be manipulated in a number of ways from the command line. The Reg.exe and RegIni.exe utility tools are included in Windows XP and later versions of Windows. Alternative locations for legacy versions of Windows include the Resource Kit CDs or the original Installation CD of Windows.
Also, a .REG file can be imported from the command line with the following command:
RegEdit.exe /s file
The /s means the file will be silent merged to the registry. If the /s parameter is omitted the user will be asked to confirm the operation. In Windows 98, Windows 95 and at least some configurations of Windows XP the /s switch also causes RegEdit.exe to ignore the setting in the registry that allows administrators to disable it. When using the /s switch RegEdit.exe does not return an appropriate return code if the operation fails, unlike Reg.exe which does.
RegEdit.exe /e file
exports the whole registry in V5 format to a UNICODE .REG file, while any of
RegEdit.exe /e file HKEY_CLASSES_ROOT[<key>] RegEdit.exe /e file HKEY_CURRENT_CONFIG[<key>] RegEdit.exe /e file HKEY_CURRENT_USER[<key>] RegEdit.exe /e file HKEY_LOCAL_MACHINE[<key>] RegEdit.exe /e file HKEY_USERS[<key>]
export the specified (sub)key (which has to be enclosed in quotes if it contains spaces) only.
RegEdit.exe /a file
exports the whole registry in V4 format to an ANSI .REG file.
RegEdit.exe /a file <key>
exports the specified (sub)key (which has to be enclosed in quotes if it contains spaces) only.
It is also possible to use Reg.exe. Here is a sample to display the value of the registry value Version:
Reg.exe QUERY HKLMSoftwareMicrosoftResKit /v Version
Other command line options include a VBScript or JScript together with CScript, WMI or WMIC.exe and Windows PowerShell.
Registry permissions can be manipulated through the command line using RegIni.exe and the SubInACL.exe tool. For example, the permissions on the HKEY_LOCAL_MACHINESOFTWARE key can be displayed using:
SubInACL.exe /keyreg HKEY_LOCAL_MACHINESOFTWARE /display
PowerShell commands and scripts[edit]
Using PowerShell to navigate the registry
Windows PowerShell comes with a registry provider which presents the registry as a location type similar to the file system. The same commands used to manipulate files and directories in the file system can be used to manipulate keys and values of the registry.[28]
Also like the file system, PowerShell uses the concept of a current location which defines the context on which commands by default operate. The Get-ChildItem (also available through the aliases ls, dir or gci) retrieves the child keys of the current location. By using the Set-Location (or the alias cd) command the user can change the current location to another key of the registry.[28] Commands which rename items, remove items, create new items or set content of items or properties can be used to rename keys, remove keys or entire sub-trees or change values.
Through PowerShell scripts files, an administrator can prepare scripts which, when executed, make changes to the registry. Such scripts can be distributed to administrators who can execute them on individual machines. The PowerShell Registry provider supports transactions, i.e. multiple changes to the registry can be bundled into a single atomic transaction. An atomic transaction ensures that either all of the changes are committed to the database, or if the script fails, none of the changes are committed to the database.[28][29]
Programs or scripts[edit]
The registry can be edited through the APIs of the Advanced Windows 32 Base API Library (advapi32.dll).[30] List of registry API functions:
- RegCloseKey
- RegConnectRegistry
- RegCreateKey
- RegCreateKeyEx
- RegDeleteKey
- RegDeleteValue
- RegEnumKey
- RegEnumKeyEx
- RegEnumValue
- RegFlushKey
- RegGetKeySecurity
- RegLoadKey
- RegNotifyChangeKeyValue
- RegOpenKey
- RegOpenKeyEx
- RegQueryInfoKey
- RegQueryMultipleValues
- RegQueryValue
- RegQueryValueEx
- RegReplaceKey
- RegRestoreKey
- RegSaveKey
- RegSetKeySecurity
- RegSetValue
- RegSetValueEx
- RegUnLoadKey
Many programming languages offer built-in runtime library functions or classes that wrap the underlying Windows APIs and thereby enable programs to store settings in the registry (e.g. Microsoft.Win32.Registry in VB.NET and C#, or TRegistry in Delphi and Free Pascal). COM-enabled applications like Visual Basic 6 can use the WSH WScript.Shell object. Another way is to use the Windows Resource Kit Tool, Reg.exe by executing it from code,[31] although this is considered poor programming practice.
Similarly, scripting languages such as Perl (with Win32::TieRegistry), Python (with winreg), TCL (which comes bundled with the registry package),[32] Windows Powershell and Windows Scripting Host also enable registry editing from scripts.
Offline editing[edit]
The offreg.dll[33] available from the Windows Driver Kit offers a set of APIs for the creation and manipulation of currently not loaded registry hives similar to those provided by advapi32.dll.
It is also possible to edit the registry (hives) of an offline system from Windows PE or Linux (in the latter case using open source tools).
COM self-registration[edit]
Prior to the introduction of registration-free COM, developers were encouraged to add initialization code to in-process and out-of-process binaries to perform the registry configuration required for that object to work. For in-process binaries such as .DLL and .OCX files, the modules typically exported a function called DllInstall()[34] that could be called by installation programs or invoked manually with utilities like Regsvr32.exe;[35] out-of-process binaries typically support the commandline arguments /Regserver and /Unregserver that created or deleted the required registry settings.[36] COM applications that break because of DLL Hell issues can commonly be repaired with RegSvr32.exe or the /RegServer switch without having to re-invoke installation programs.[37]
Advanced functionality[edit]
Windows exposes APIs that allows user-mode applications to register to receive a notification event if a particular registry key is changed.[38] APIs are also available to allow kernel-mode applications to filter and modify registry calls made by other applications.[39]
Windows also supports remote access to the registry of another computer via the RegConnectRegistry function[40] if the Remote Registry service is running, correctly configured and its network traffic is not firewalled.[41]
Security[edit]
Each key in the registry of Windows NT versions can have an associated security descriptor. The security descriptor contains an access control list (ACL) that describes which user groups or individual users are granted or denied access permissions. The set of registry permissions include 10 rights/permissions which can be explicitly allowed or denied to a user or a group of users.
| Permission | Description |
|---|---|
| Query Value | The right to read the registry key value. |
| Set Value | The right to write a new value |
| Create Subkey | The right to create subkeys. |
| Enumerate Subkeys | Allow the enumeration of subkeys. |
| Notify | The right to request change notifications for registry keys or subkeys. |
| Create Link | Reserved by the operating system. |
| Delete | The right to delete a key. |
| Write DACL | The right to modify permissions of the container’s DACL. |
| Write Owner | The right to modify the container’s owner. |
| Read Control | The right to read the DACL. |
As with other securable objects in the operating system, individual access control entries (ACE) on the security descriptor can be explicit or inherited from a parent object.[42]
Windows Resource Protection is a feature of Windows Vista and later versions of Windows that uses security to deny Administrators and the system WRITE access to some sensitive keys to protect the integrity of the system from malware and accidental modification.[43]
Special ACEs on the security descriptor can also implement mandatory integrity control for the registry key and subkeys. A process running at a lower integrity level cannot write, change or delete a registry key/value, even if the account of the process has otherwise been granted access through the ACL. For instance, Internet Explorer running in Protected Mode can read medium and low integrity registry keys/values of the currently logged on user, but it can only modify low integrity keys.[44]
Outside security, registry keys cannot be deleted or edited due to other causes. Registry keys containing NUL characters cannot be deleted with standard registry editors and require a special utility for deletion, such as RegDelNull.[45][46]
Backups and recovery[edit]
Different editions of Windows have supported a number of different methods to back up and restore the registry over the years, some of which are now deprecated:
- System Restore can back up the registry and restore it as long as Windows is bootable, or from the Windows Recovery Environment (starting with Windows Vista).
- NTBackup can back up the registry as part of the System State and restore it. Automated System Recovery in Windows XP can also restore the registry.
- On Windows NT, the Last Known Good Configuration option in startup menu relinks the
HKLMSYSTEMCurrentControlSetkey, which stores hardware and device driver information. - Windows 98 and Windows ME include command line (Scanreg.exe) and GUI (Scanregw.exe) registry checker tools to check and fix the integrity of the registry, create up to five automatic regular backups by default and restore them manually or whenever corruption is detected.[47] The registry checker tool backs up the registry, by default, to
%Windir%SysbckupScanreg.exe can also run from MS-DOS.[48] - The Windows 95 CD-ROM included an Emergency Recovery Utility (ERU.exe) and a Configuration Backup Tool (Cfgback.exe) to back up and restore the registry. Additionally Windows 95 backs up the registry to the files system.da0 and user.da0 on every successful boot.
- Windows NT 4.0 included
RDISK.EXE, a utility to back up and restore the entire registry.[49] - Windows 2000 Resource Kit contained an unsupported pair of utilities called Regback.exe and RegRest.exe for backup and recovery of the registry.[50]
- Periodic automatic backups of the registry are now disabled by default on Windows 10 May 2019 Update (version 1903). Microsoft recommends System Restore be used instead.[51]
Policy[edit]
Group policy[edit]
Windows 2000 and later versions of Windows use Group Policy to enforce registry settings through a registry-specific client extension in the Group Policy processing engine.[52] Policy may be applied locally to a single computer using gpedit.msc, or to multiple users and/or computers in a domain using gpmc.msc.
Legacy systems[edit]
With Windows 95, Windows 98, Windows ME and Windows NT 4.0, administrators can use a special file to be merged into the registry, called a policy file (POLICY.POL). The policy file allows administrators to prevent non-administrator users from changing registry settings like, for instance, the security level of Internet Explorer and the desktop background wallpaper. The policy file is primarily used in a business with a large number of computers where the business needs to be protected from rogue or careless users.
The default extension for the policy file is .POL.
The policy file filters the settings it enforces by user and by group (a «group» is a defined set of users). To do that the policy file merges into the registry, preventing users from circumventing it by simply changing back the settings.
The policy file is usually distributed through a LAN, but can be placed on the local computer.
The policy file is created by a free tool by Microsoft that goes by the filename poledit.exe for Windows 95/Windows 98 and with a computer management module for Windows NT. The editor requires administrative permissions to be run on systems that uses permissions.
The editor can also directly change the current registry settings of the local computer and if the remote registry service is installed and started on another computer it can also change the registry on that computer.
The policy editor loads the settings it can change from .ADM files, of which one is included, that contains the settings the Windows shell provides. The .ADM file is plain text and supports easy localisation by allowing all the strings to be stored in one place.
Virtualization[edit]
INI file virtualization[edit]
Windows NT kernels support redirection of INI file-related APIs into a virtual file in a registry location such as HKEY_CURRENT_USER using a feature called «InifileMapping».[53] This functionality was introduced to allow legacy applications written for 16-bit versions of Windows to be able to run under Windows NT platforms on which the System folder is no longer considered an appropriate location for user-specific data or configuration. Non-compliant 32-bit applications can also be redirected in this manner, even though the feature was originally intended for 16-bit applications.
Registry virtualization[edit]
Windows Vista introduced limited registry virtualization, whereby poorly written applications that do not respect the principle of least privilege and instead try to write user data to a read-only system location (such as the HKEY_LOCAL_MACHINE hive), are silently redirected to a more appropriate location, without changing the application itself.
Similarly, application virtualization redirects all of an application’s invalid registry operations to a location such as a file. Used together with file virtualization, this allows applications to run on a machine without being installed on it.
Low integrity processes may also use registry virtualization. For example, Internet Explorer 7 or 8 running in «Protected Mode» on Windows Vista and above will automatically redirect registry writes by ActiveX controls to a sandboxed location in order to frustrate some classes of security exploits.
The Application Compatibility Toolkit[54] provides shims that can transparently redirect HKEY_LOCAL_MACHINE or HKEY_CLASSES_ROOT Registry operations to HKEY_CURRENT_USER to address «LUA» bugs that cause applications not to work for users with insufficient rights.
Disadvantages[edit]
Critics labeled the registry in Windows 95 a single point of failure, because re-installation of the operating system was required if the registry became corrupt.[citation needed] However, Windows NT uses transaction logs to protect against corruption during updates. Current versions of Windows use two levels of log files to ensure integrity even in the case of power failure or similar catastrophic events during database updates.[55] Even in the case of a non-recoverable error, Windows can repair or re-initialize damaged registry entries during system boot.[55]
Equivalents and alternatives[edit]
In Windows, use of the registry for storing program data is a matter of developer’s discretion. Microsoft provides programming interfaces for storing data in XML files (via MSXML) or database files (via SQL Server Compact) which developers can use instead. Developers are also free to use non-Microsoft alternatives or develop their own proprietary data stores.
In contrast to Windows Registry’s binary-based database model, some other operating systems use separate plain-text files for daemon and application configuration, but group these configurations together for ease of management.
- In Unix-like operating systems (including Linux) that follow the Filesystem Hierarchy Standard, system-wide configuration files (information similar to what would appear in HKEY_LOCAL_MACHINE on Windows) are traditionally stored in files in
/etc/and its subdirectories, or sometimes in/usr/local/etc. Per-user information (information that would be roughly equivalent to that in HKEY_CURRENT_USER) is stored in hidden directories and files (that start with a period/full stop) within the user’s home directory. However XDG-compliant applications should refer to the environment variables defined in the Base Directory specification.[56] - In macOS, system-wide configuration files are typically stored in the
/Library/folder, whereas per-user configuration files are stored in the corresponding~/Library/folder in the user’s home directory, and configuration files set by the system are in/System/Library/. Within these respective directories, an application typically stores a property list file in thePreferences/sub-directory. - RISC OS (not to be confused with MIPS RISC/os) uses directories for configuration data, which allows applications to be copied into application directories, as opposed to the separate installation process that typifies Windows applications; this approach is also used on the ROX Desktop for Linux.[57] This directory-based configuration also makes it possible to use different versions of the same application, since the configuration is done «on the fly».[58] If one wishes to remove the application, it is possible to simply delete the folder belonging to the application.[59][60] This will often not remove configuration settings which are stored independently from the application, usually within the computer’s !Boot structure, in !Boot.Choices or potentially anywhere on a network fileserver. It is possible to copy installed programs between computers running RISC OS by copying the application directories belonging to the programs, however some programs may require re-installing, e.g. when shared files are placed outside an application directory.[58]
- IBM AIX (a Unix variant) uses a registry component called Object Data Manager (ODM). The ODM is used to store information about system and device configuration. An extensive set of tools and utilities provides users with means of extending, checking, correcting the ODM database. The ODM stores its information in several files, default location is
/etc/objrepos. - The GNOME desktop environment uses a registry-like interface called dconf for storing configuration settings for the desktop and applications.
- The Elektra Initiative provides alternative back-ends for various different text configuration files.
- While not an operating system, the Wine compatibility layer, which allows Windows software to run on a Unix-like system, also employs a Windows-like registry as text files in the WINEPREFIX folder: system.reg (HKEY_LOCAL_MACHINE), user.reg (HKEY_CURRENT_USER) and userdef.reg.[61]
See also[edit]
- Registry cleaner
- Application virtualization
- LogParser – SQL-like querying of various types of log files
- List of Shell Icon Overlay Identifiers
- Ransomware attack that uses Registry
Notes[edit]
- ^ When applications fail to execute because they request more privileges than they require (and are denied those privileges), this is known as a limited user application (LUA) bug.
Footnotes[edit]
- ^ Esposito, Dino (November 2000). «Windows 2000 Registry: Latest Features and APIs Provide the Power to Customize and Extend Your Apps». MSDN Magazine. Microsoft. Archived from the original on April 15, 2003. Retrieved July 19, 2007.
- ^ a b c «The System Registry».
- ^ «Windows 95 Architecture Components». www.microsoft.com. Archived from the original on February 7, 2008. Retrieved April 29, 2008.
The following table shows other difficulties or limitations caused by using .INI files that are overcome by using the Registry.
- ^ Hipson 2002, p. 5, 41–43.
- ^ Richter, Jeffrey; Nasarre, Christophe (2008). Windows Via C/C++ (Fifth ed.). Microsoft Press. ISBN 9780735642461. Retrieved August 28, 2021.
- ^ Raymond Chen, «Why do registry keys have a default value?»
- ^ Hipson 2002, pp. 207, 513–514.
- ^ Hipson 2002, pp. 520–521.
- ^ Hipson 2002, p. 7.
- ^ «Designed for Windows XP Application Specification». Microsoft. August 20, 2002. Retrieved April 8, 2009.
- ^ «HKEY_LOCAL_MACHINE». Gautam. 2009. Retrieved April 8, 2009.
- ^ «Registry Keys Affected by WOW64 (Windows)». Msdn.microsoft.com. Retrieved April 10, 2014.
- ^ «Description of the Microsoft Windows registry». Retrieved September 25, 2008.
- ^ «HKEY_CURRENT_USER». Microsoft. 2009. Retrieved April 8, 2009.
- ^ «Description of the HKEY_DYN_DATA Registry Key in Windows 95, Windows 98, and Windows 98 SE». support.microsoft.com.
- ^ «A Closer Look at HKEY_DYN_DATA». rinet.ru. Archived from the original on May 9, 2008.
- ^ «Registry hives». Retrieved July 19, 2007.
- ^ Chen, Raymond (August 8, 2011). «Why is a registry file called a «hive»?». The Old New Thing. Retrieved July 29, 2011.
- ^ «Overview of the Windows NT Registry». Retrieved December 2, 2011.
- ^ «Inside the Registry». Retrieved December 28, 2007.
- ^ a b Norris, Peter (February 2009). «The Internal Structure of the Windows Registry» (PDF). Cranfield University. Archived from the original (PDF) on May 29, 2009.
- ^ «Incorrect Icons Displayed for .ico Files». November 15, 2009. Retrieved March 31, 2012.
- ^ «How to Completely Uninstall / Remove a Software Program in Windows without using 3rd Party Software? — AskVG». www.askvg.com. August 26, 2011.
- ^ «You may receive a «STOP 0x00000035 NO_MORE_IRP_STACK_LOCATIONS» error message when you try to log on to a domain». October 9, 2011. Retrieved March 31, 2012. This page tells the user to edit the registry when resolving the issue.
- ^ key renaming is implemented as removal and add while retaining subkeys/values, as the underlying APIs do not support the rename function directly
- ^ a b c d «How to add, modify, or delete registry subkeys and values by using a .reg file». support.microsoft.com.
- ^ «Applying Group Policy». Microsoft.
- ^ a b c Payette, Bruce; Siddaway, Richard (2018). Windows PowerShell in Action (Third ed.). Manning Publications. pp. 7–8, 24, 608, 708–710. ISBN 9781633430297. Retrieved August 28, 2021.
- ^ Warner, Timothy L. (May 2015). Windows PowerShell in 24 Hours, Sams Teach Yourself. Sams Publishing. p. 19, 211. ISBN 9780134049359. Retrieved August 28, 2021.
- ^ «Reading and Writing Registry Values with Visual Basic». Retrieved July 19, 2007.
- ^ «REG command in Windows XP». Retrieved July 19, 2007.
- ^ «registry manual page – Tcl Bundled Packages». www.tcl.tk. Retrieved December 14, 2017.
- ^ «Offline Registry Library». Retrieved June 4, 2014.
- ^ «DllInstall Function». Microsoft. March 7, 2012. Retrieved March 22, 2012.
- ^ «Regsvr32». Microsoft. Retrieved March 22, 2012.
- ^ «How to: Register Automation Servers». Microsoft. Retrieved March 22, 2012.
- ^ «How to re-register PowerPoint 2000, PowerPoint 2003, PowerPoint 2007 and PowerPoint 2010». Microsoft. January 2012. Retrieved March 22, 2012.
- ^ «RegNotifyChangeKeyValue function». Microsoft.
- ^ «Registering for Notifications». Microsoft.
- ^ «RegConnectRegistry function». Microsoft.
- ^ «How to Manage Remote Access to the Registry». Microsoft.
- ^ Gibson, Darril (June 28, 2011). «Chapter 4: Securing Access with Permissions». Microsoft Windows security : essentials. Indianapolis, Ind.: Wiley. ISBN 978-1-118-01684-8.
- ^ «Application Compatibility: Windows Resource Protection (WRP)». Microsoft. Retrieved August 8, 2012.
- ^ Marc Silbey, Peter Brundrett. «Understanding and Working in Protected Mode Internet Explorer». Retrieved August 8, 2012.
- ^ «RegDelNull v1.1». November 1, 2006. Retrieved August 8, 2012.
- ^ «Unable to delete certain registry keys – Error while deleting key». March 23, 2010. Retrieved August 8, 2012. Microsoft Support page.
- ^ «Description of the Windows Registry Checker Tool (Scanreg.exe)».
- ^ «Command-Line Switches for the Registry Checker Tool».
- ^ «How To Backup, Edit, and Restore the Registry in Windows NT 4.0». support.microsoft.com.
- ^ «Technical Reference to the Registry: Related Resources». Microsoft. Retrieved September 9, 2011.
- ^ «Microsoft Kills Automatic Registry Backups in Windows 10». ExtremeTech. Retrieved July 1, 2019.
- ^ «How Core Group Policy Works». Microsoft. September 2, 2009. Retrieved August 13, 2012.
- ^ «Chapter 26 – Initialization Files and the Registry». Microsoft. Retrieved March 3, 2008.
- ^ «Microsoft Application Compatibility Toolkit 5.0». Microsoft. Retrieved July 26, 2008.
- ^ a b Ionescu, Mark Russinovich, David A. Solomon, Alex (2012). «Registry Internals». Windows internals (6th ed.). Redmond, Wash.: Microsoft Press. ISBN 978-0-7356-4873-9.
- ^ «XDG Base Directory Specification». standards.freedesktop.org.
- ^ «Application directories». Archived from the original on May 27, 2012. Retrieved May 17, 2012.
- ^ a b «Case Studies Of The Top 132 Annoyances With Operating Systems Other Than RISC OS». Retrieved April 3, 2012. Page from the riscos.com website. Mentioned in points 82 and 104.
- ^ «RISC OS tour». Retrieved July 19, 2007.
- ^ «The RISC OS Products Directory». November 2, 2006. Archived from the original on February 19, 2007. Retrieved April 1, 2012.
- ^ 3.2. Using the Registry and Regedit (Wine User Guide)
References[edit]
- Hipson, Peter (2002). Mastering Windows XP Registry. Wiley. ISBN 0-7821-2987-0. Retrieved August 28, 2021.
- Russinovich, Mark E.; Solomon, David A. (2005). Microsoft Windows Internals (Fourth ed.). Microsoft Press. pp. 183–236. ISBN 978-0-7356-1917-3.
External links[edit]
- Windows Registry info & reference in the MSDN Library
В данной статье рассмотрены общие сведения о реестре операционной системы Windows.
Реестр Windows (Windows Registry, системный реестр) — это иерархическая (древовидная) база данных, содержащая записи, определяющие параметры и настройки операционных систем Microsoft Windows.
Реестр в том виде, как он выглядит при просмотре редактором реестра, формируется из данных, источниками которых являются файлы реестра и информация об оборудовании, собираемая в процессе загрузки. В описании файлов реестра на английском языке используется термин Hive. В документации от Microsoft этот термин переводится как Куст.
Содержание
- Основные файлы, отвечающие за формирование реестра
- Структура реестра
- Основные типы данных, применяемые в реестре
- Взаимодействие реестра с операционной системой
Основные файлы, отвечающие за формирование реестра
Файлы реестра создаются в процессе установки операционной системы и хранятся в папке:
%SystemRoot%\system32\config (обычно C:\windows\system32\config).
Для операционных систем Windows это файлы с именами:
- system
- software
- sam
- security
- default
- components
- bcd-template
В операционных системах Windows Vista, Windows 7, Windows8, Windows 8.1, Windows 10, файлы реестра располагаются в каталоге \Windows\system32\config и имеют такие же имена, однако в этих операционных системах добавился новый раздел реестра для хранения данных конфигурации загрузки (Boot Configuration Data) с именем BCD00000000.
Файл с данными этого раздела имеет имя bcd и находится в скрытой папке Boot активного раздела (раздела, с которого выполняется загрузка системы).
Обычно, при стандартной установке Windows, создается активный раздел небольшого размера (от 100 до 500 мегабайт в зависимости от операционной системы), который скрыт от пользователя и содержит только служебные данные для загрузки системы – загрузочные записи, менеджер загрузки bootmgr, хранилище конфигурации загрузки BCD, файлы локализации и программы тестирования памяти
Расположение куста bcd зависит от того, как сконфигурирован загрузчик системы при ее установке, и может находиться на том же разделе, где и каталог Windows.
Место расположения файлов реестра в любой версии Windows можно просмотреть с помощью редактора реестра, в разделе:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\hivelist
В этом разделе хранится информация о всех кустах, включая пользовательские профили, со ссылками на их расположение в файловой системе Windows.
Структура реестра
Реестр Windows имеет древовидную структуру и состоит из 5 основных разделов реестра:
HKEY_LOCAL_MACHINE (HKLM) — самый большой раздел реестра. В нем сосредоточены все основные настройки операционной системы, а также аппаратного и программного обеспечения компьютера. Информация, содержащаяся в этом разделе, применяется ко всем пользователям, регистрирующимся в системе.
HKEY_ CLASSES_ ROOT (HKCR) — содержит ассоциации между приложениями и типами файлов (по расширениям файлов). Кроме того, в этом разделе находится информация о зарегистрированных типах файлов и объектах COM и ActiveX. Кроме HKEY_ CLASSES_ ROOT эти сведения хранятся также в разделах HKEY_LOCAL_MACHINE и HKEY_CURRENT_USER.
Раздел HKEY_LOCAL_MACHINE\Software\Classes содержит параметры по умолчанию, которые относятся ко всем пользователям локального компьютера. Параметры, содержащиеся в разделе HKEY_CURRENT_USER\Software\Classes, переопределяют принятые по умолчанию и относятся только к текущему пользователю. Раздел HKEY_CLASSES_ROOT включает в себя данные из обоих источников.
HKEY_USERS (HKU) — содержит настройки среды для каждого из загруженных пользовательских профилей, а также для профиля по умолчанию. В HKEY_USERS находится вложенный раздел \Default, а также другие подразделы, определяемые идентификатором безопасности (Security ID, SID) каждого пользователя.
HKEY_CURRENT USER (HKCU) — cодержит настройки среды для пользователя, на данный момент зарегистрировавшегося в системе (переменные окружения, настройки рабочего стола, параметры сети, приложений и подключенных устройств).
Этот раздел дублирует информацию в HKEY_USERS\user SID, где user SID — идентификатор безопасности пользователя, зарегистрировавшегося в системе на текущий момент (узнать SID текущего пользователя можно, набрав в командной строке whoami /user).
HKEY_CURRENT_ CONFIG (HKCC) — cодержит настройки для текущего аппаратного профиля. Текущий аппаратный профиль включает в себя наборы изменений, внесенных в стандартную конфигурацию устройств, заданную в подразделах Software и System корневого раздела HKEY LOCAL_MACHINE.
В HKEY_CURRENT_CONFIG отражаются только изменения. Кроме того, информация этого раздела находится в HKEY_LOCAL_MACHINE\System\CurrentControlSet\HardwareProfiles\Current.
Данные в реестре хранятся в виде параметров, расположенных в ключах реестра. Каждый параметр характеризуется именем, типом данных и значением.
Основные типы данных, применяемые в реестре
REG_DWORD — 32-х разрядное число. Этот тип данных используют многие параметры драйверов устройств и сервисов. Редакторы реестра могут отображать эти данные в двоичном, шестнадцатеричном и десятичном формате.
REG_SZ — Текстовая строка в формате, удобном для восприятия человеком. Значениям, представляющим собой описания компонентов, обычно присваивается именно этот тип данных.
REG_EXPAND_SZ — Расширяемая строка данных. Эта строка представляет собой текст, содержащий переменную, которая может быть заменена при вызове со стороны приложения, например, используется для записи переменных окружения.
REG_MULTI_SZ — Многострочное поле. Значения, которые фактически представляют собой списки текстовых строк в формате, удобном для восприятия человеком, обычно имеют этот тип данных. Строки разделены символом NULL.
REG_BINARY — Двоичные данные. Большинство аппаратных компонентов используют информацию, которая хранится в виде двоичных данных. Редакторы реестра отображают эту информацию в шестнадцатеричном формате.
REG_RESOURCE_LIST — Список аппаратных ресурсов. Применяется только в ветви HKEY_LOCAL_MACHINE\HARDWARE.
Также иногда можно встретить такие типы данных реестра:
- REG_RESOURCE_ REQUIREMENTS_LIST — Список необходимых аппаратных ресурсов. Применяется только в ветви HKEY_LOCAL_MACHINE\HARDWARE.
- REG_FULL_RESOURCE_ DESCRIPTOR — Дескриптор (описатель) аппаратного ресурса. Применяется только в ветви HKEY_LOCAL_MACHINE\HARDWARE.
- REG_LINK — Символическая ссылка Unicode. Этот тип данных интересен тем, что позволяет одному элементу реестра ссылаться на другой ключ или параметр.
- REG_QWORD — 64-х разрядное число.
- REG_DWORD_ LITTLE_ENDIAN — 32-разрядное число в формате «остроконечников» (little-endian), эквивалент REG_DWORD.
- REG_DWORD_BIG_ ENDIAN — 32-разрядное число в формате «тупоконечников» (big-endian).
- REG_QWORD_LITTLE_ ENDIAN — 64-разрядное число в формате «остроконечников». Эквивалент REG_QWORD.
- REG_NONE — Параметр не имеет определенного типа данных.
Взаимодействие реестра с операционной системой
При запуске компьютера распознаватель аппаратных средств (hardware recognizer) помещает в реестр список обнаруженных им устройств. Обычно распознавание аппаратных средств осуществляется программой Ntdetect.com и ядром операционной системы Ntoskrnl.exe.
При старте системы ядро системы извлекает из реестра сведения о загружаемых драйверах устройств и порядке их загрузки. Кроме того, программа Ntoskrnl.exe передает в реестр информацию о себе (напр. номер версии).
В процессе загрузки системы драйверы устройств обмениваются с реестром параметрами загрузки и конфигурационными данными. Драйвер устройства сообщает об используемых им системных ресурсах, включая аппаратные прерывания (IRQ) и каналы доступа к памяти (DMA), чтобы система могла включить эти данные в реестр.
Кстати, реестр позволяет создавать несколько аппаратных профилей. Аппаратный профиль (hardware profile) представляет собой набор инструкций, с помощью которого можно указать операционной системе, драйверы каких устройств должны загружаться при запуске компьютера. По умолчанию системой создается стандартный аппаратный профиль, который содержит информацию обо всех аппаратных средствах, обнаруженных на компьютере.
При входе пользователя в систему загружаются пользовательские профили (user profiles). Вся информация, относящаяся к конкретному имени пользователя и связанными с ним правами хранится в реестре. Пользовательский профиль определяет индивидуальные параметры настройки системы (разрешение дисплея, параметры сетевых соединений, подключенные устройства и многое другое). Информация о пользовательских профилях также хранится в реестре.
При установке приложений. Каждый раз при запуске программы установки происходит добавление в реестр новых конфигурационных данных. Начиная свою работу, все программы установки должны считывать информацию из реестра, чтобы определить, присутствуют ли в системе необходимые им компоненты. Кроме того, системный реестр позволяет приложениям совместно использовать конфигурационную информацию, что предоставляет им больше возможностей для взаимодействия. Приложение должно активно и правильно использовать реестр, а также иметь возможность корректного удаления, не затрагивая при этом компонентов, которые могут использоваться другими программами (библиотеки, программные модули и т. п.). Эта информация тоже хранится в реестре.
При администрировании системы. Когда пользователь вносит изменения в конфигурацию системы с помощью средств администрирования системы (например при помощиПанели управления или оснастки MMC), все изменения сразу отражаются в системном реестре. По сути средства администрирования представляют собой наиболее удобные и безопасные средства модификации реестра. Кстати, к средствам администрирования можно отнести и редактор реестра (regedit.exe), ведь все изменения в систему можно вносить непосредственно правкой реестра.
В процессе загрузки и функционирования операционной системы выполняется постоянное обращение к данным реестра, как для чтения, так и для записи. Файлы реестра постоянно изменяются, поскольку не только система, но и отдельные приложения могут использовать реестр для хранения собственных данных, параметров и настроек. Другими словами, обращение к реестру — это одна из наиболее распространенных операций. Даже если пользователь не работает за компьютером, обращения к реестру все равно выполняются системными службами, драйверами и приложениями.
Нарушение целостности файлов реестра (нарушение структуры данных) или неверное значение отдельных критических параметров может привести к краху системы . Поэтому, прежде чем экспериментировать с реестром, позаботьтесь о возможности его сохранения и восстановления.
Реестр системы Windows
•Реестр операционной системы Windows представляет собой централизованную базу данных параметров настройки системы и работающих в ней приложений.
•Аналогичен разнообразным INI-файлам, а также файлам Autoexec.bat и Config.sys, которые использовались ранее.
•Реестр содержит информацию обо всех аппаратных средствах, программном обеспечении, операционной системе и сетевых параметрах компьютера
2
Программные компоненты системы, работающие с реестром
•Программы установки. Каждый раз при запуске программы установки или других установочных программ (для аппаратных и программных средств) в реестр добавляются новые конфигурационные данные. Начиная свою работу, все грамотно разработанные программы установки считывают информацию реестра, чтобы определить, присутствуют ли в системе компоненты, обязательные для успешного завершения установки. Централизованный реестр позволяет приложениям совместно использовать конфигурационную информацию и предоставляет им больше возможностей взаимодействия между собой.
•Распознаватель. Каждый раз при запуске компьютера под управлением Windows распознаватель аппаратных средств (Hardware Recognizer) помещает в реестр список обнаруженных им устройств.
•Ядро Windows. При старте системы ядро Windows извлекает из реестра сведения о загружаемых драйверах устройств и порядке их загрузки. Кроме того, программа Ntoskrnl.ехе передает в реестр информацию о себе (примером такой информации может служить, например, номер3версии).
Программные компоненты системы, работающие с реестром (продолжение)
•Драйверы устройств. Драйверы устройств
обмениваются с реестром параметрами загрузки и
конфигурационными данными.
•Административные средства Windows.
Административные средства Windows, в том числе
утилиты панели управления и оснастки, собранные в
группу Администрирование, представляют собой наиболее удобные и безопасные средства
модификации реестра. Редакторы реестра также
полезны для его просмотра и, время от времени, для внесения изменений в конфигурацию системы.
•Пользовательские профили. Windows обеспечивает возможность создания множества пользовательских
профилей. Вся информация, относящаяся к конкретному пользовательскому имени и
ассоциированным с ним правам, хранится в реестре (файл ntuser.dat в профиле каждого пользователя).
•Аппаратные профили. Реестр позволяет хранить множественные аппаратные конфигурации.
Аппаратный профиль представляет 4собой набор
инструкций, с помощью которого можно указать ОС,

Структура реестра
Реестр
Раздел (ветвь)
Параметр
5
Структура реестра
Корневые разделы:
•HKEY_CLASSES_ROOT
•HKEY_CURRENT_USER
•HKEY_LOCAL_MACHINE
•HKEY_USERS
•HKEY_CURRENT_ CONFIG
6
Корневые разделы

HKEY_CLASSES_ Содержит ассоциации между приложениями и ROOT типами файлов (по расширениям имени файла).
Кроме того, этот раздел содержит информацию OLE (Оbject Linking and Embedding), ассоциированную с объектами СОМ, а также данные по ассоциациям файлов и классов Параметры этого раздела совпадают с параметрами, расположенными в разделе НКЕУ_LOCAL_MACHINESoftwareClasses.
|
HKEY_CURRENT |
Содержит конфигурационные данные для текущего |
||||
|
_CONFIG |
аппаратного профиля. Кроме того, параметры этого |
||||
|
раздела |
появляются |
также |
в |
разделе |
|
|
HKEY_LOCAL_MACHINESystemCurrentControlS |
|||||
|
et HardwareProfilesCurrent |
7

Корневые разделы
реестр
HKEY_LOCAL_ Содержит глобальную информацию о компьютерной MACHINE системе, включая такие данные об аппаратных средствах и операционной системе, как: тип шины, системная память, драйверы устройств и управляющие данные, используемые при запуске
системы.
|
HKEY_USERS |
Содержит |
все |
активно |
загруженные |
|
пользовательские |
профили, |
включая |
||
|
НКЕY_CURRENT_USER, а также профиль по |
||||
|
умолчанию. Раздел HKEY_USERS содержит |
||||
|
вложенный раздел Default, |
||||
|
HKEY_CURREN |
Содержит профиль пользователя, на данный момент |
|||
|
T_ USER |
зарегистрировавшегося в системе. |
8

Структура параметра реестра
|
RegistrySizeLimit REG_DWORD |
0x8000000 |
9
Хранение данных реестра (понятие куста)
Куст представляет собой дискретную совокупность разделов, вложенных разделов и параметров, берущую начало в вершине иерархии реестра.
•Отличие кустов от других групп разделов состоит в том, что они являются постоянными компонентами реестра.
•Кусты не создаются динамически при загрузке операционной системы и не удаляются при ее остановке.
10
Соседние файлы в папке Операционные системы_1
- #
- #
- #
- #
- #
- #
Для работы операционной системы Windows должны использоваться различные сведения. Реестр представляет собой специальную базу данных. В нем имеется информация, касающаяся оборудования, программного обеспечения, а также многое другое. В процессе функционирования системы происходит постоянное обращение к этой информации. Она может изменяться или дополняться, в зависимости от конкретных действий. Подобные мероприятия происходят в автоматическом порядке и пользователю нет необходимости беспокоиться об их выполнении.
ВАЖНО: если Вы решили работать с реестром Windows, то предварительно создайте его копию. Неосторожные действия легко могут стать причиной серьёзных системных сбоев. В результате придется восстанавливать ОС или даже осуществить её переустановку.
Реестр в операционных системах


Чтобы продемонстрировать важность реестра, требуется сказать о простой статистике. В ходе запуска ОС сюда осуществляется около тысячи обращений, а в течение одного дня количество может достигнуть 10.000 и даже более. Достаточно запустить какую-либо программу, задать настройки или выполнить иные действия, чтобы информация в реестре была отредактирована.
Где хранится реестр?
Довольно часто можно услышать вопрос о расположении файлов. Реестр Windows располагается по директории CWindowsSystem32config. Здесь в качестве диска указан С, но для Вашего устройства ситуация может быть иной. Все зависит от того, куда именно установлена система.
Если рассматривать наиболее популярную ОС Windows 7, то файлы реестра здесь располагаются в специальных местах. Подобный момент требует к себе отдельного внимания:
- «HKEY_LOCAL_MACHINEHARDWARE». Указанная ветка будет создаваться на основании того, какое именно подключено периферийное оборудование. Процесс является динамическим.
- «HKEY_LOCAL_MACHINEBCD00000000» использует для своего создания специальный файл «%SystemRoot%BootBCD».
- «HKEY_LOCAL_MACHINESYSTEM». Чтобы сформировать указанную ветку, применяется документ «%SystemRoot%System32config SYSTEM».
- «HKEY_LOCAL_MACHINESOFTWARE». Создание происходит на основании документа «%SystemRoot%System32configSOFTWARE».
- «HKEY_LOCAL_MACHINESECURITY». В ветке происходит хранение параметров безопасности устройства и она создается из документа «%SystemRoot%System32configSECURITY».
- «HKEY_LOCAL_MACHINESAM». Для создания применяется информация из документа, находящегося по адресу «%SystemRoot%System32configSAM».
- «HKEY_USERSDEFAULT». Формирование ветки реестра производится за счет документа «%SystemRoot%System32configDEFAULT».
- Ветки реестра «HKEY_USERSS-1-5-18», «HKEY_USERSS-1-5-19» и «HKEY_USERSS-1-5-20». Для их создания используется документ NTUSER.DAT, который лежит в различных директориях. Это «%SystemRoot%System32configsystemprofile», «%SystemRoot%System32configsystemprofile» и «%SystemRoot%ServiceProfilesNetworkService».
- «HKEY_USERS<SID_юзера>». С целью формирование происходит применение документа «%USERPROFILE%NTUSER.DAT».
- «HKEY_USERS<SID_юзера>_Classes». В указанном случае, формирование производится в ходе использования документа «%USERPROFILE%AppDataLocalMicrosoftWindowsUsrClass.dat».
Реестр имеет отдельные файлы, которые заслуживают к себе внимания – это резервные копии. Они необходимы в случае восстановления системы. Данные документы находятся по директории «%SystemRoot%System32configRegBack». Если рассматривать ситуацию по умолчанию, то копия будет создавать один раз в 10 дней. Можно выполнить настройку подобного процесса – периодичности и времени запуска. Пользовательская часть реестра находится в документе %userprofile%ntuser.dat.
Когда речь заходит о реестре ОС 32х и 64х разрядного типа, тут предусматриваются определенные особенности. В первом случае все папки являются единичными. Для 64х разрядов предусматривается разделение на 32х и, непосредственно, 64х разрядные разделы.
Как открыть реестр?
Для получения доступа можно использовать несколько способов и необходимо рассмотреть среди них наиболее популярные.
Через утилиту «Выполнить»
Подобный вариант можно назвать наиболее привлекательным, поскольку он сочетает в себе простоту и удобство. Требуется действовать в соответствии с рекомендациями:
- Зажимаем сочетание клавиш Win+R или запускаем утилиту «Выполнить» другим способом.
- Производим ввод regedit и нажимаем подтверждение. Крайне важно, чтобы подобное действие проводилось от имени администратора.
Посредством поиска через меню «Пуск»
Тут могут быть определенные отличия при работе с различными ОС. Например, для Windows 8 отсутствует классическое меню «Пуск». В любом случае, необходимо получить доступ к строке поиска. В неё требуется ввести regedit и запустить выданную программу.
Посредством проводника Windows
Поставлена задача найти конкретный файл в системой папке CWindows (ранее уже говорилось о возможности использования другой буквы диска, в зависимости от места установки ОС). Нас интересует regedit. Его нужно найти в общем перечне и запустить.
Структура реестра
Реестр Windows включает в себя 5 ветвей. Каждая из них предусматривает хранение сведений конкретного типа. Данные разделы не разрешается изменять. Они не могут быть перенесены, переименованы или удалены. Требуется описать каждую из ветвей и указать их особенности:
- HKEY_CLASSES_ROOT (HKCR). Здесь хранятся данные о многочисленных расширениях, что позволяет системе работать с файлами различного типа. Если каких-либо сведений нет, всегда можно внести дополнительные изменения для расширения возможностей.
- HKEY_CURRENT_USER (HKCU). В указанной ветке находятся сведения об учетной записи. Сюда можно отнести различные настройки и элементы персонализации.
- HKEY_LOCAL_MACHINE (HKLM). Здесь располагается все данные о подсоединённых устройствах и драйверах. Что особенно важно, тут находятся сведения, касающиеся загрузки ОС.
- HKEY_USERS (HKU). Здесь представлены данные о полном списке пользователей для конкретного устройства.
- HKEY_CURRENT_CONFIG (HKCC). Представлены сведения об оборудовании, которое применяет устройство в ходе запуска ОС. Как показывает практика, тут находится мало информации и почти вся она является копией из иных разделов.
В процессе работы с реестром Windows, интерес представляют HKEY_CURRENT_USER и HKEY_LOCAL_MACHINE. Здесь находится большинство настроек, которые возникает необходимость изменять.
Необходимо уделить внимание такой составляющей, как параметры. Они позволяют вносить изменения в различные аспекты работы системы. Существует несколько типов параметров:
- Двоичный. Получил наибольшее распространение и используется во всех разделах. При выдаче в редакторе реестра предусматривается применение 16х формата.
- Dword. Используется значение с длиной 4 байта. Необходим для осуществления хранения параметров драйверов и различных программ.
- Расширяемая строка данных. Основное отличие от строкового параметра заключается в отсутствии четкого фиксирования длины.
- Многострочный. Используется более чем одна строка. Довольно часто применяется при необходимости хранения табличных данных.
- Строковый. Строка текста, которая обладает фиксированной длиной.
- Qword. Сведения указываются в виде 64х разрядного целого.
- Ссылка. Используется символическая ссылка в формате Юникод.
Резервная копия всего реестра или отдельного раздела
Ранее уже говорилось об опасностях работы с реестром. Всегда имеется вероятность причинить вред системе и нужно заранее позаботиться о создании копии. Следует войти в редактор реестра Windows, где открыть раздел «Файл». В появившемся списке происходит выбор пункта «Экспорт». Теперь можно осуществить создание копии всего реестра или конкретного подраздела. Для удобства, процесс демонстрируется на скриншоте ниже.
С целью повышения надежности допускается сохранить копию не только на жёстком диске устройства, но внешнем носителе.
Восстановление реестра
Так, самое худшее случилось и в системе произошел сбой. Что необходимо сделать в такой ситуации? Стоит рассмотреть три способа восстановления, каждый из которых обладает своими особенностями. В любой ситуации требуется предварительно завершить работу всех программ и приложений. Не станет лишним отключение антивирусных средств.
Восстановление из файла
Переходим к документу, который ранее был сохранен. Там должна находиться копия всего реестра Windows. Требуется осуществить двойной клик, после чего подтвердить полученное сообщение. Оно представлено на скриншоте далее.
Определенное время потребуется для восстановления, а сам процесс будет завершен после перезагрузки устройства.
Слияние
Нужно открыть папку с копией и нажать на ней правой кнопкой мыши. Произойдет выдача меню, в котором требуется указать «Слияние». Для Вашего удобства, это действие представлено на скриншоте.
Как и в предыдущем случае, восстановление завершится после перезагрузки.
Импорт
Необходимо открыть реестр Windows. Как это сделать уже рассматривалось ранее и было представлено несколько подходов. В самом редакторе нас интересует меню «Файл». Там следует выбрать «Импорт». Будет предложено указать путь до сохраненной копии.
Отдельно требуется вынести вариант, который предусматривает восстановление всей системы. Это предусматривает использование встроенных средств. Важно самостоятельно делать бэкап или не отключать резервное копирование.
Восстановление с использованием live CD
В некоторых ситуациях загрузка операционной системы не будет представляться возможной. Это наиболее сложный вариант и для решения такой проблемы рекомендуется использовать специальный способ. Он заключается в осуществлении загрузки через live CD. Когда это выполнено, необходимо проследовать дальше – посетить корень диска, где установлена Windows. Предусматривается следующая инструкция:
- Создаем на диске с системой временную папку. Ей требуется дать название tmp. Именно здесь будут располагаться дефектные файлы реестра.
- Теперь осуществляем вход в папку C:WINDOWSsystem32config
- Все файлы, найденные здесь, должны быть перенесены в созданную ранее временную папку C:tmp
- Идем в папку восстановления, которая располагается в директории C:System Volume Information. В ней должно располагаться некоторое количество папок следующего типа — _restore{длинный символьный код с дефисами}. Проверяем дату создания подобных папок и находим в списке самую позднюю.
- Внутри будут находиться папки с названиями RP1, RP2 и так далее. Нас опять интересует самая последняя. Важно ознакомиться с датой и уточнить, работали ли ОС в указанное время стабильно. Если нет, выбираем последнее работоспособное сохранение.
- Переходим в папку Snapshot. Именно здесь располагаются резервные копии файлов реестра.
- Требуется использовать _REGISTRY_USER_DEFAULT, _REGISTRY_MACHINE_SECURITY, _REGISTRY_MACHINE_SOFTWARE, _REGISTRY_MACHINE_SYSTEM и _REGISTRY_MACHINE_SAM
- Указанные в прошлом пункте файлы копируются и ими производится замена аналогичных файлов реестра в директории C:WINDOWSsystem32config. Требуется выполнить смену названия на DEFAULT, SECURITY, SOFTWARE, SYSTEM и SAM
- Для того, чтобы изменения вступили в силу, необходимо перезагрузиться.
Чистка реестра
Нередко можно столкнуться с запросом о том, как очистить реестр на Windows (Виндовс). Здесь можно использовать специализированное ПО или ручной метод. В первом случае, можно порекомендовать достаточно большое количество приложений. К наиболее популярным следует отнести Reg Organizer, CCleaner и Windows Cleaner. Данные программы отлично себя зарекомендовали – их возможности по оптимизации работы системы находятся на весьма высоком уровне.
Ручная чистка реестра Windows больше подходит для опытных пользователей, которые знают, что делают. Предварительно рекомендуется выполнить копирование файлов, чтобы провести восстановление в случае неудачи.
Непосредственно процесс очистки требует удалить любые сведения об уже удаленной программе. Подобные данные содержатся в «HKEY_CURRENT_USER» и именно туда лежит наш путь. В подразделе Software требуется найти необходимую папку. Ниже на скриншоте показан пример для программы Скайп.
Создание и удаление разделов и параметров через файл с расширением reg
Все reg файлы обладают строго установленным синтаксисом, который должен в обязательном порядке соблюдаться. Это является особенностью документов подобного типа. REG файлы допускается применять в качестве средства для создания или удаления подразделов, а также параметров.
Создание подразделов или изменение параметров
- Осуществляем доступ к редактору реестра
- Выбирается тот подраздел, изменения для которого должны быть проведены
- Происходит нажатие на вкладку «Файл», где надо нажать «Экспорт»
- В поле «Имя файла» прописывается название документа для сохранения REG-файла с изначальными элементами реестра и нажимается кнопку «Сохранить»
Удаление разделов реестра или параметров
Для выполнения поставленной задачи требуется поместить дефис перед путем реестра. Следует рассмотреть это на простом примере. Имеем:
HKEY_LOCAL_MACHINESoftware
Из него необходимо выполнить удаление раздела Program. Это будет выглядеть следующим образом:
[-HKEY_LOCAL_MACHINESoftwareProgram]
Удаление значения имеет схожий способ. В данном случае, дефис должен располагаться непосредственно перед знаком равенства. Расширим прошлый пример – теперь нужно удалить параметр ProgramValue. Это выполняется следующим образом:
[HKEY_LOCAL_MACHINESoftwareProgram]
» ProgramValue»=-
Вносить изменения можно через обычную программу-блокнот. Не забывайте предварительно делать копии.
Что хранится в реестре
В системном реестре хранятся все данные, которые необходимы для правильной работы ОС: информация обо всех подключенных к вашему компьютеру устройствах и встроенных компонентах системного блока – все они обращаются к реестру. Так, видеоадаптер при запуске системы отправляет запрос, касающийся разрешения и качества цветопередачи выводимого на экран изображения (соответствующие настройки драйвер видеоадаптера вносит в реестр при установке);
В MS-DOS – прародительнице современных ОС семейства Windows – реестра не было. Важнейшие настройки хранились в двух текстовых файлах — config.sys и autoexec.bat. Каждый из них содержал по 10–20 строк текстовой информации
Windows 3.0 хранила все настройки в текстовом файле win.ini. Записей в нем было гораздо больше, чем в файлах настройки MSDOS, — свыше 1000
Реестр впервые появился в выпущенной в 1993 году Windows NT. И если в этой ОС и появившейся немногим позже Windows 95 он включал в себя приблизительно 10 000 записей, то в Windows XP и Vista их количество увеличилось в десять раз
■
настройки операционной системы – значения любого параметра Windows XP или Windows Vista. К примеру, Windows заносит в реестр сведения об ассоциациях типов файлов с приложениями, в которых они обрабатываются: так, после двойного щелчка по названию MP3-файла автоматически запускается «Проигрыватель Windows Media»;
■
параметры оформления – начиная с ширины панели задач и внешнего вида значка Мой компьютер и заканчивая названиями пунктов контекстного меню;
■
для ПО реестр служит своего рода записной книжкой, позволяющей, например, программе для «прожига» дисков Nero 9 «не забывать» об установленной скорости записи, а приложению
Word «запоминать» документы, с которыми пользователь работал в последнее время, и отображать их в виде наглядного списка.
«Общаясь» с реестром, пользователь должен быть чрезвычайно осторожен, а все его действия – обдуманны, так как изменение некоторых параметров реестра может привести к нарушению работы Windows или даже к ее выходу из строя.
Принцип работы реестра
Как уже говорилось выше, каждая программа, установленная в операционной системе Windows, неразрывно связана с реестром. Мы расскажем на наглядном примере, как строится процесс обмена данными между приложениями и реестром на примере «Проигрывателя Windows Media».
Пользователь помещает компакт-диск в привод ПК, чтобы сохранить записанные на нем музыкальные композиции в формате MP3 на жестком диске. «Проигрыватель» обращается к реестру и узнает, в какую папку следует помещать конвертированные файлы.Если бы не было реестра, пользователю пришлось бы каждый раз самостоятельно задавать этот путь
Для настройки звучания пользователь устанавливает параметры качества звука в соответствующем окне программы. Чтобы эти настройки сохранились при закрытии приложения, «Проигрыватель Windows Media» сразу же заносит их в реестр
Зачем нужен реестр
Впервые реестр появился в ОС Windows NT. Ее предшественницы – MS-DOS и Windows 1.0–3.11 хранили все настройки в текстовых файлах config.sys и autoexec.bat. Манипулирование сложносочиненными командами с множеством ключей, используемыми в этих файлах, считалось высшим пилотажем и зачастую было не «по зубам» неопытному пользователю. Кроме того, каждая программа имела свой собственный конфигурационный файл, что добавляло еще больше трудностей при настройке системы. Реестр, как централизованное хранилище всех настроек ОС, аппаратных компонентов и установленных приложений, был призван устранить этот хаос и успешно справляется с этой задачей по сей день. Он используется в последней версии ОС Windows – Vista, а затем «переедет» и в Windows 7.
Во времена Windows 95 реестр состоял всего лишь из нескольких тысяч записей, сейчас же – в Windows XP и Vista — он содержит до 150 000 записей. Файлы, составляющие реестр, занимают на жестком диске около 80 Мб.
Где хранится реестр
Реестр состоит из семи различных файлов. Шесть из них находятся в папке Windowssystem32config
Файл, хранящий личные настройки пользователя, «скрыт» в папке соответствующей учетной записи, например, в C:Documents and Settingsmakarova
Поскольку файлов в реестре несколько, его нельзя открыть, например, в текстовом редакторе и внести какие-либо коррективы. Для работы с ним требуется специальная программа – редактор реестра, который является встроенным компонентом операционной системы Windows и вызывается путем ввода команды Regedit.
А Самый большой раздел реестра – в нем содержится информация о типах файлов и файловых ассоциациях. Здесь хранится основная часть всех программных настроек – к примеру, функций управления ОС, настройки принтера и параметры сети.
Б Данный раздел содержит настройки учетной записи вошедшего в систему пользователя. Наиболее интересным является подраздел Software, который включает в себя настройки всех установленных в системе приложений.
В Раздел содержит абсолютно одинаковые для всех пользователей системы параметры аппаратной конфигурации компьютера.
Г
Здесь хранятся настройки (профили) всех пользователей компьютера. Если в систему вошел другой пользователь, соответствующие подразделы автоматически перемещаются в раздел «Б».
Д
Данный раздел содержит сведения о настройках всех встроенных компонентов компьютера и подключенных к нему устройств. Информация о них заимствуется из раздела «В».
Какова структура реестра
Реестр имеет иерархическую структуру, он напоминает файловую систему жесткого диска – с его каталогами, подкаталогами и файлами. Однако называются элементы реестра по-другому: верхний уровень иерархии составляют разделы (или ключи от англ. key), каждый из которых может содержать вложенные подразделы, а также параметры. Именно в параметрах хранится основное содержимое реестра, разделы служат лишь для группировки схожих по назначению параметров.
Параметры реестра соответствуют определенному типу, который определяет область их возможных значений, способ хранения и обработки (всего предусмотрено 7 типов). К основным типам параметров относятся числовые и текстовые.
■
Текстовые параметры представляют собой текстовые строки фиксированной длины. Самыми распространенными являются строковый параметр REG_SZ и многострочный параметр REG_MULTI_SZ. С помощью текстовых параметров можно, к примеру, задать стартовую страницу веб-браузера.
Изменять записи реестра или добавлять новые могут не только программы, но и сами пользователи. Загляните в реестр и попробуйте применить следующий прием, который влияет на скорость завершения работы Windows XP и Vista. По умолчанию всем программам на завершение работы отводится 20 с, но многим приложениям требуется гораздо меньше времени. Дайте Windows команду закрывать программы по прошествии 4 с, чтобы ускорить выключение ПК.
Мы в данном примере шаг за шагом поясним, как выполнить необходимые изменения. В точности соблюдайте все указания, так как малейшая ошибка может вывести из строя как саму операционную систему, так и установленные в ней приложения.
1 Удерживая клавишу Win, нажмите R. В появившемся окне введите команду «Regedit» и нажмите на кнопку OK. В Vista вам потребуется дополнительно щелкнуть по кнопке «Продолжить».
2 В открывшемся окне раскройте раздел «HKEY_LOCAL_MACHINE», а затем – подразделы «SYSTEM» и «CurrentControlSet».
3 Щелкните по подразделу «Control» — справа появятся все параметры этого подраздела. Выполните двойной щелчок по параметру «WaitToKillServiceTimeout»
4 Если в открывшемся окне уже указано значение «4000», то в этом случае совет будет для вас закончен. В противном случае введите значение «4000», щелкните по кнопке OK и по X. Выполните перезагрузку Windows — теперь система будет быстрее завершать свою работу.
■
Числовые параметры содержат значение какой-либо функции Windows. Считывая это значение, ОС получает данные о том, как должна вести себя эта функция. Пример числового типа – тип REG_DWORD. Так, параметр REG_DWORD устанавливает, каким образом будет поддерживаться актуальное состояние системы. По умолчанию установлено значение 3, которое определяет, что Windows будет автоматически загружать из Интернета и устанавливать важные обновления. Если изменить значение параметра на 2, то Windows будет только извещать о наличии новых компонентов обновления, а их закачку и установку придется выполнять вручную.
При работе ОС параметры реестра постоянно меняются: добавляются новые разделы или параметры, удаляются либо модифицируются старые. Множество изменений вносится в реестр при установке нового ПО или устройства – иногда несколько сотен записей за один раз.
Так как вызов многих скрытых функций недоступен из Панели управления, «продвинутые» пользователи используют редактор реестра для настройки Windows «под себя». Однако менять параметры следует, тщательно изучив руководство, так как один неверный шаг может привести к нежелательным для операционной системы последствиям.
Чтобы снизить риск ввода ошибочных значений, рекомендуем пользоваться специальными программами-оптимизаторами. Они избавят вас от необходимости вручную вносить изменения в реестр – несколькими щелчками мышью вы сможете легко изменить все скрытые настройки.
Как Windows Vista защищает реестр
Вредоносные программы, проникнув на ПК, первым делом стремятся захватить управление реестром. В Windows XP никаких препятствий для этого не существует: если на компьютере не установлено антивирусное ПО, способное задержать вредителя, он сможет свободно считывать или удалять данные из реестра.
В Windows Vista, благодаря наличию системы управления учетными записями, это будет сделать не так-то легко: в отличие от Windows ХР здесь программы работают с ограниченными правами доступа к реестру. Только в том случае, если пользователь щелкнет по кнопке «Продолжить», программе будет дозволено обратиться к реестру.
Запустите редактор реестра, как это описано во врезке выше. Откройте меню «Файл» и выберите пункт «Экспорт…». Укажите, в каком месте будет сохранена резервная копия, и укажите «Имя файла». Нажмите на кнопку «Сохранить». Готово! Резервная копия реестра сохранена!
Примечание. Аналогичным образом можно делать резервные копии отдельных разделов реестра. Выберите нужный раздел, например
В окне убедитесь, что активирован параметр
Введите имя файла и нажмите на кнопку «Сохранить». Для восстановления реестра (или его раздела) выполните операцию экспорта из резервного файла, воспользовавшись в меню «Файл» командой «Импорт…».
Почему Windows со временем начинает работать медленнее
Чем дольше вы используете операционную систему, тем медленнее она работает и загружается. Почему это происходит? Одна из причин – интенсивная работа с приложениями: установка новых программ, опробование демоверсий, деинсталляция ненужного «софта». При удалении программы в реестре, как правило, остаются ее «следы», особенно если деинсталлятор приложения написан разработчиком с ошибками. Уже после нескольких месяцев работы реестр оказывается безнадежно захламлен этими «мертвыми» записями – в результате системе требуется больше времени на его загрузку.
Помогут в данной ситуации утилиты для очистки системы – они работают, в том числе, и с реестром Windows, отыскивая в нем ошибочные записи и удаляя их. Надежно функционируют программы CCleaner, TuneUp Utilities 2009 и Glary Registry Repair – это подтверждено результатами тестов, проведенных в разное время специалистами Computer Bild.





















