How to install VPN on Windows Server 2019 using Routing and Remote Access
-
View Larger Image
In this blog article we are discussing about How to install and configure a VPN on Windows Server 2019 using Routing and Remote Access server role. A VPN is short form of virtual private network, which gives us a privacy, anonymity and security over public internet. A VPN service masks our ISP IP so your online actions are virtually untraceable. A VPN can also be used to connect computers to isolated remote computer networks that is usually inaccessible, by using the Internet or another intermediate network. Another Use of VPN is the client computers can browse websites through VPN server even if they are in the restricted internal network.
Routing and Remote Access Service is a Windows proprietary server role, that supports remote user or site-to-site connectivity by using virtual private network (VPN) or dial-up connections. So using RRAS we can convert a regular Windows Server as VPN server. Microsoft RRAS server and VPN client supports PPTP, L2TP/IPSec, SSTP and IKEv2 based VPN connection.
By default the VPN connections are made using PPTP which is a VPN Point-to-Point Tunnelling Protocol. We can also convert our VPN server to support SSTP. The PPTP protocol connection are established over TCP port 1723. PPTP also uses GRE and it supports encryption keys up to 128-bits. PPTP is a very fast VPN protocol and very easy to setup. Its supported by most operating systems like windows, Mac and Linux PC and android and IOS mobile devices.
System Configuration We Used.
Used Windows server 2019 which is covert as a VPN SSTP server.
Used Windows 10 client PC for connecting to Windows VPN server 2019.
Another thing is we are settings up VPN on windows server 2019 which only have one Network interface and its configured with Static Public IP address not NAT enabled. So this blog article can be implemented on Most of VPS ( Virtual Private Server) provided by Hosting Providers or with the Cloud Windows VMs.
Since its a VPS server, we only have RDP access using the VPS public IP address. So lets get started.
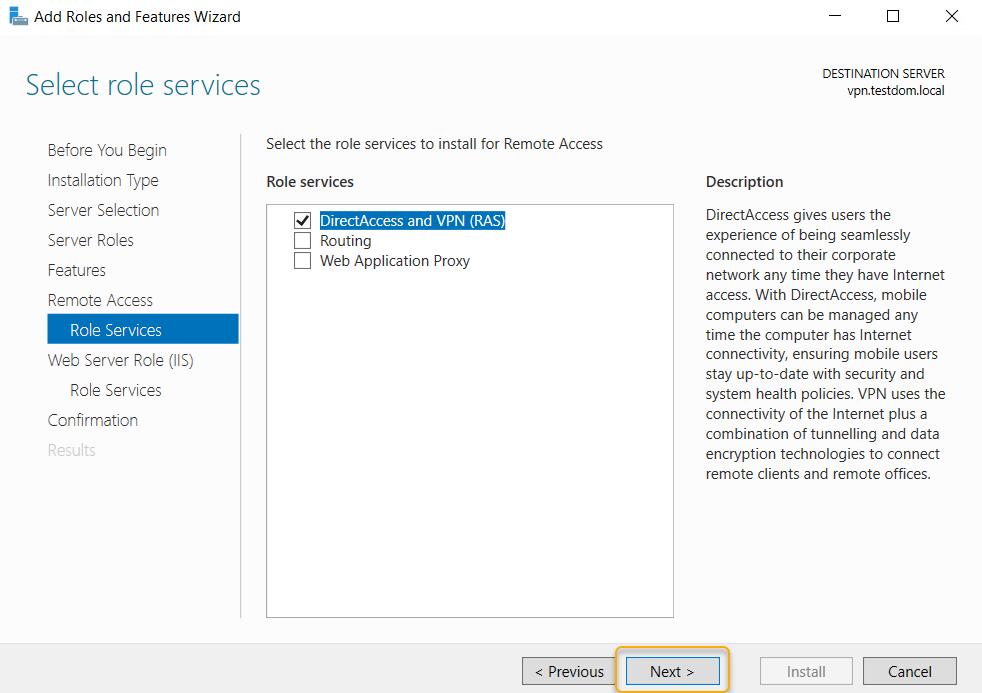
Here I have divided the whole steps in to different parts. Lets get started. Even though we are performing the install on Windows server 2019, you can refer this article for Windows server 2016 and windows server 2012.
Part:1 Install Remote Access Server role on Windows Server 2019
Log into the Windows Server 2019 > Click Windows Start Icon >> Click Server Manager.
Click Add Roles And Features
Click Next
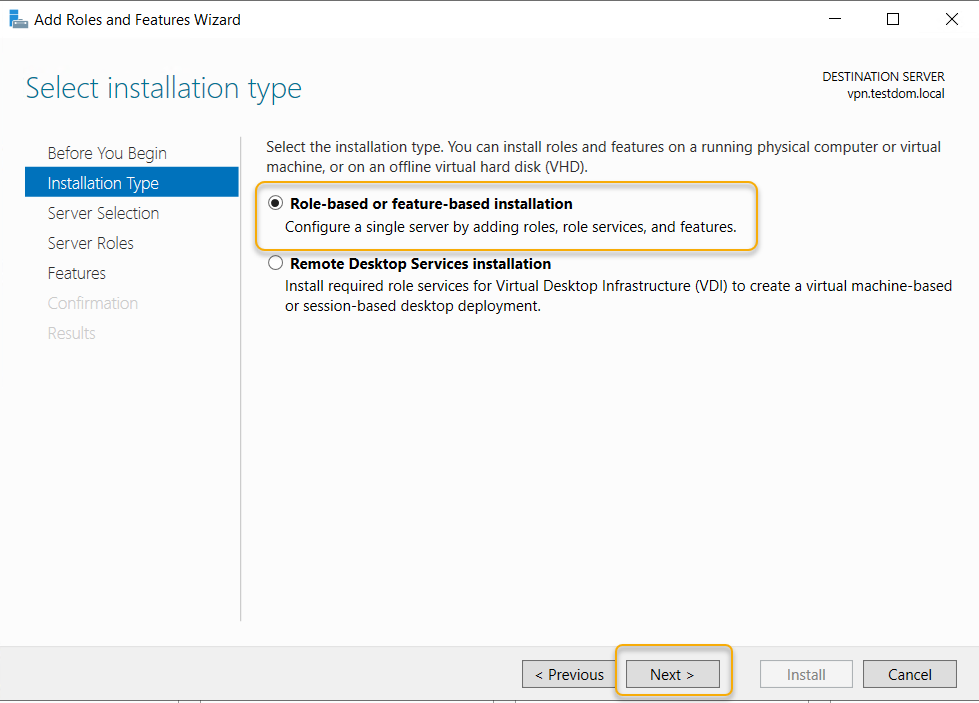
Choose the Installation Type as ” Role based or feature based installation and click Next.
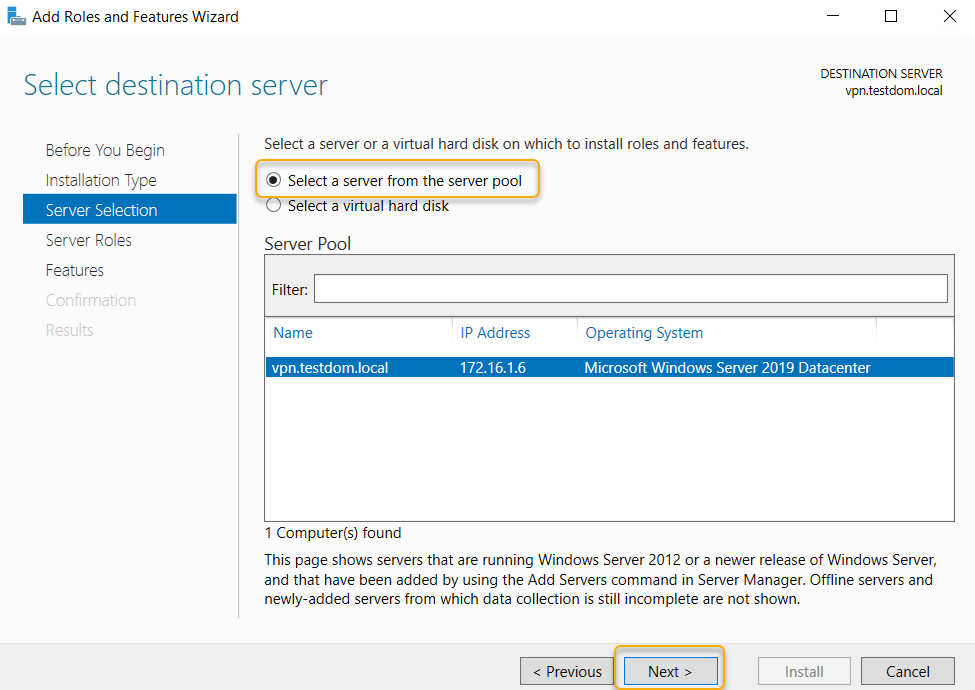
From Server selection, choose “select a server from the server pool” and click Next.
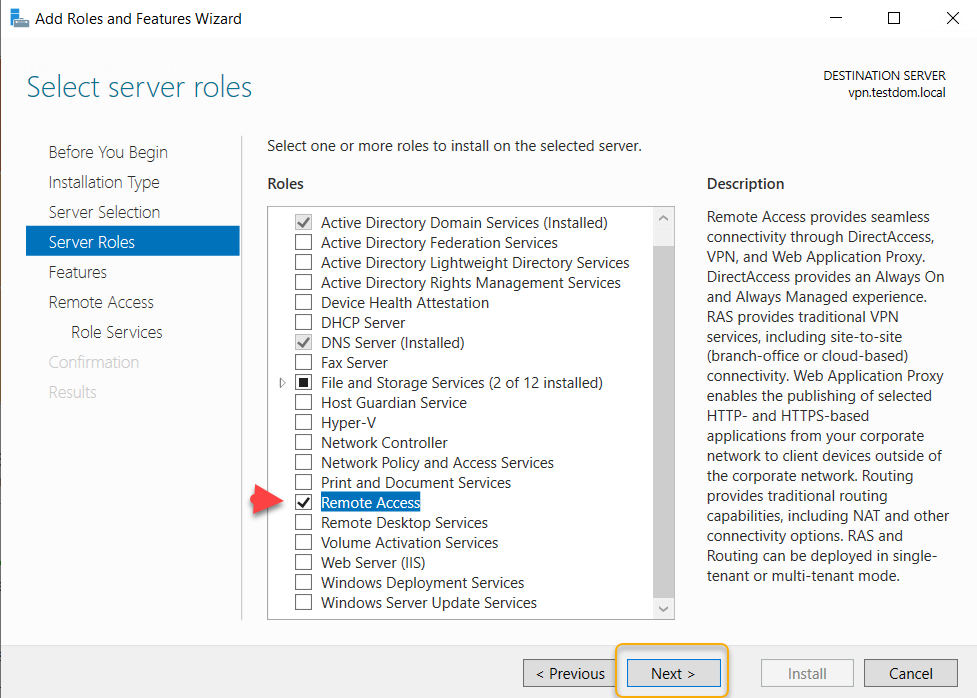
From Server Role choose ” Remote Access” and click Next.
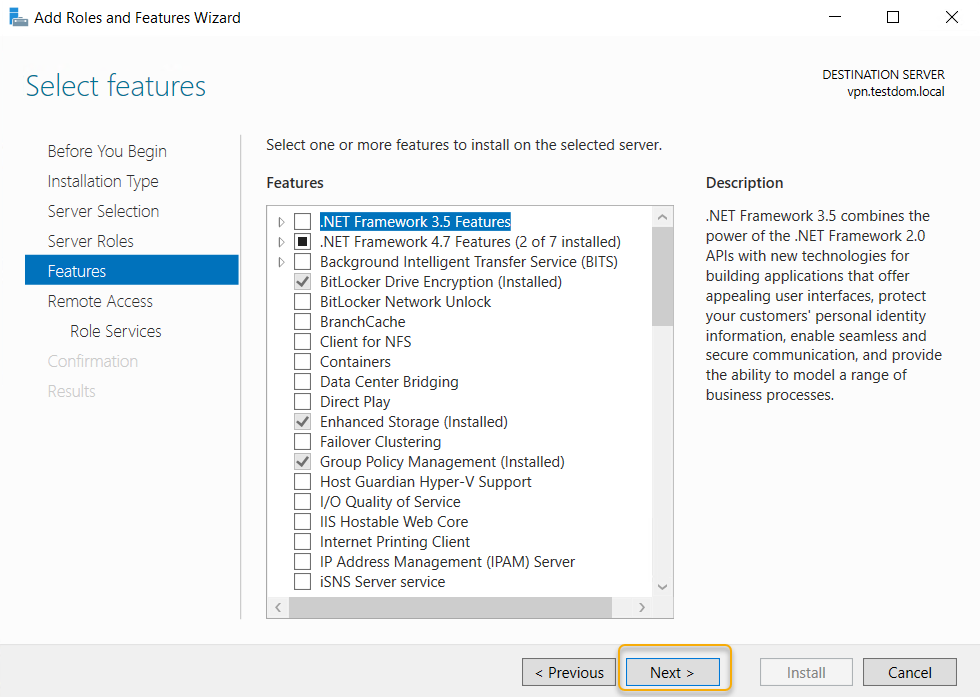
Leave Features section as it is and click Next.
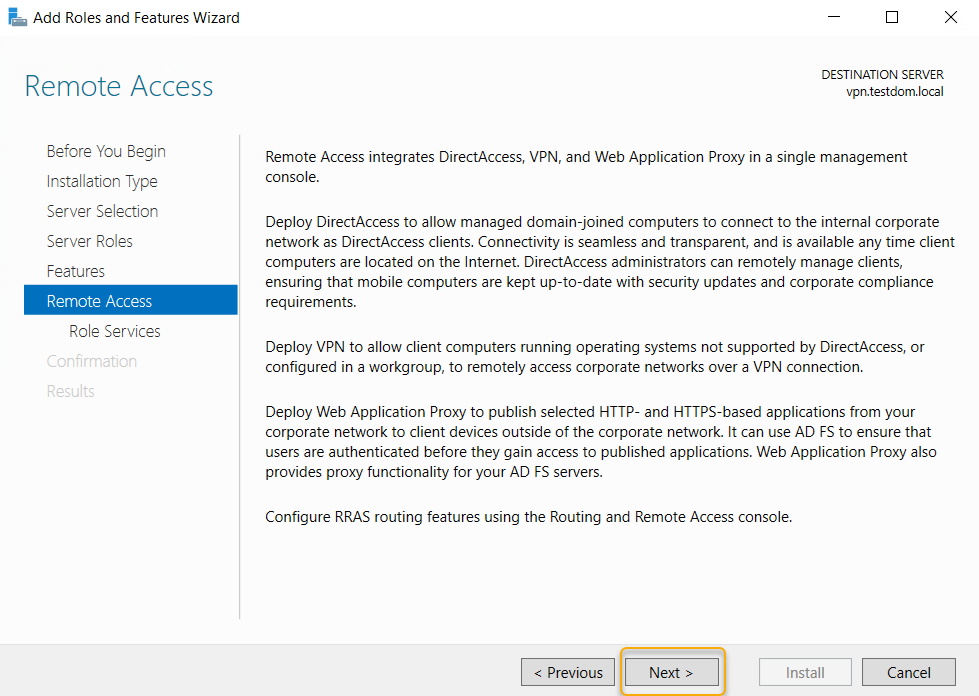
Click Next on Remote Access section.
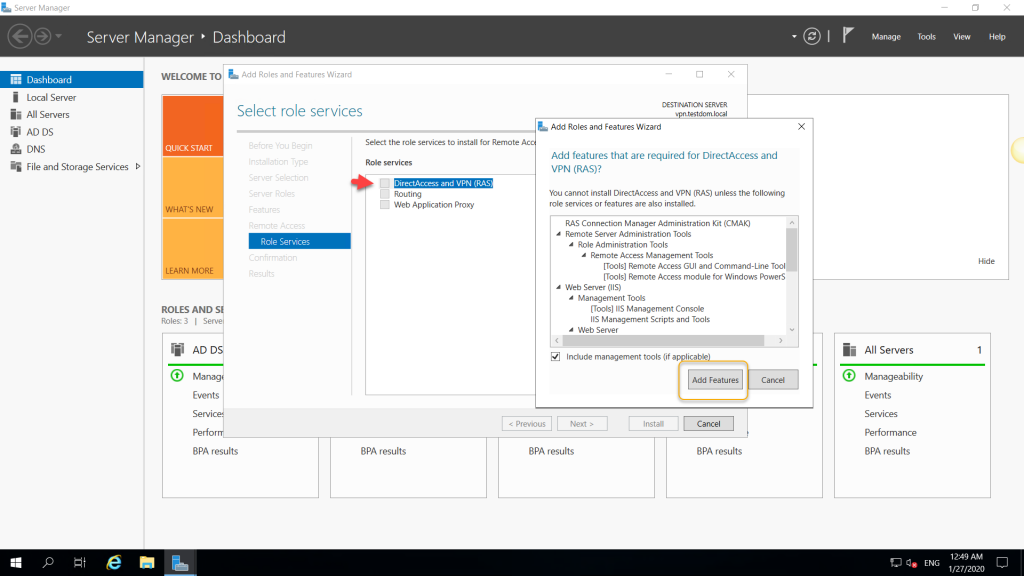
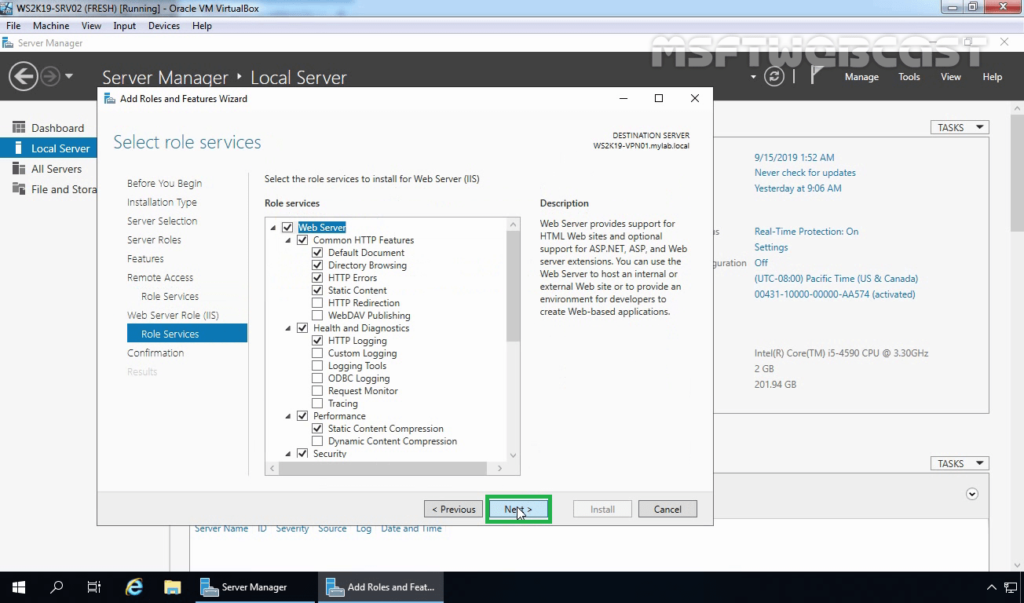
Under Role Services choose “Direct Access and VPN (RAS) and Routing and click Next. A popup window will appear for confirming the features that need to be installed for Direct Access and VPN. Confirm it by clicking “Add Features”.

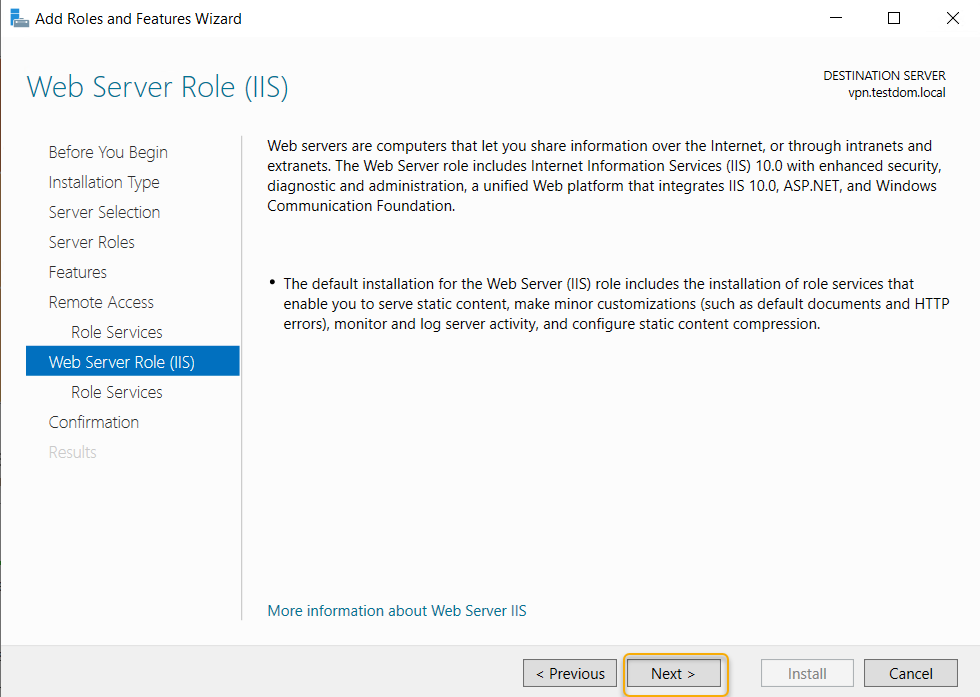
Under Web Server Role (IIS) Section click Next.
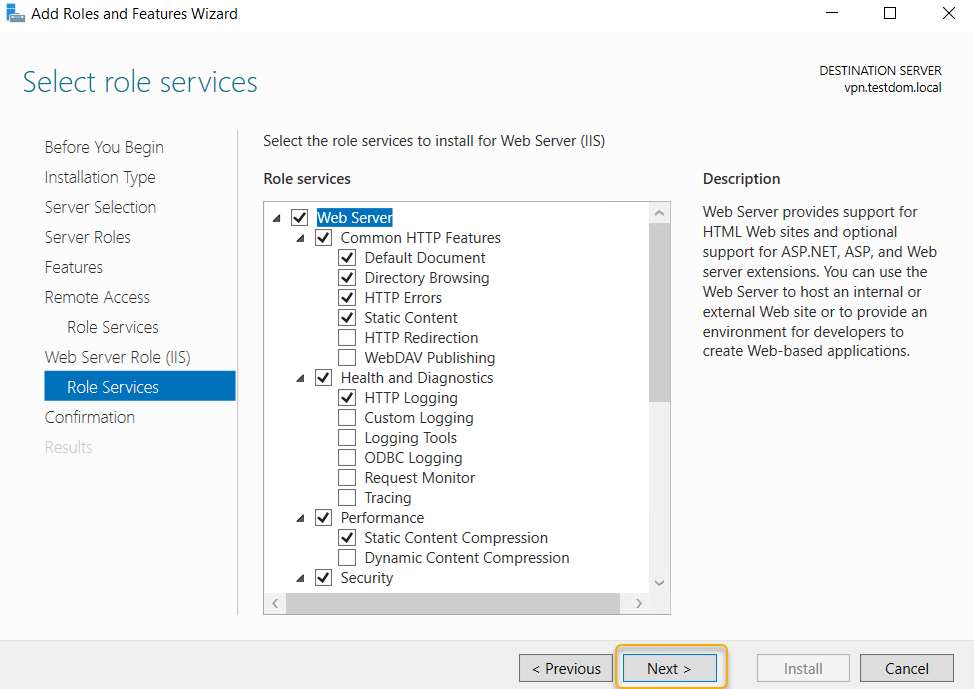
Under IIS Role services section leave the default one and Click Next.
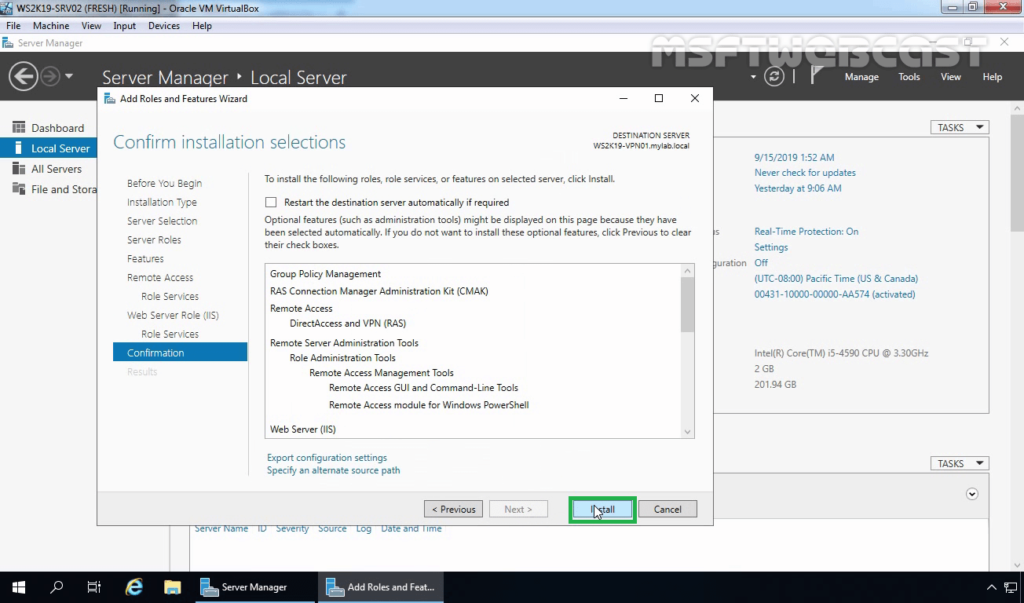
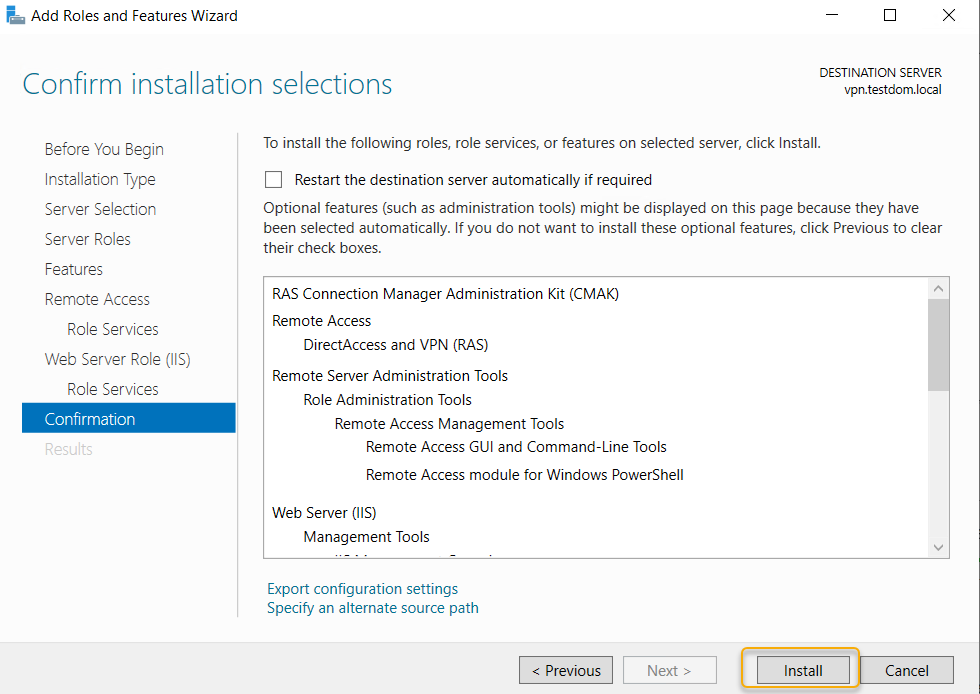
Under Final Confirmation section click Install.
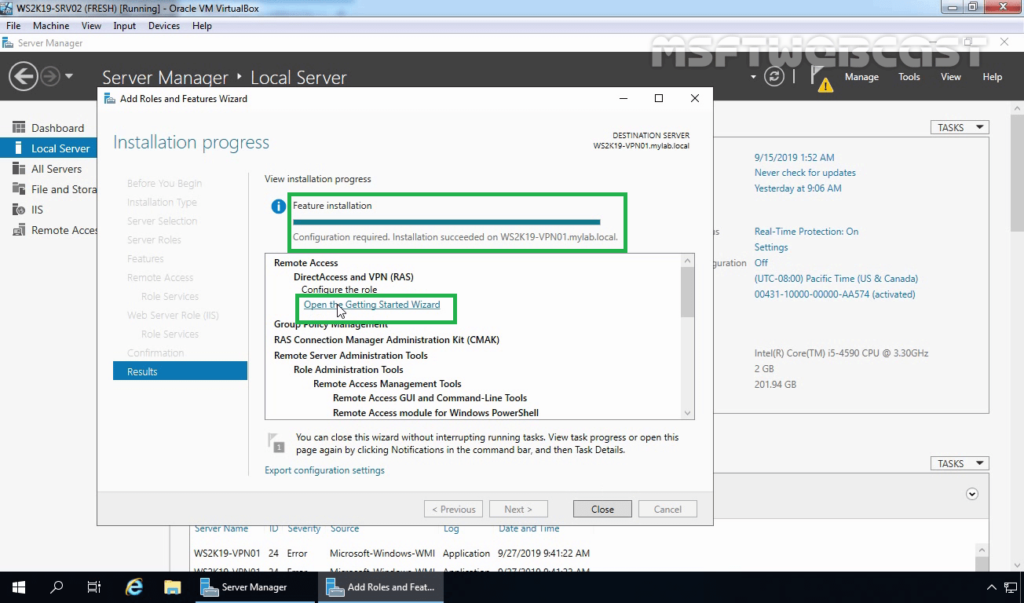
The Remote Access server role install will start automatically and normally it will get completed with in few Minutes. Once the installation succeeded click close.
Part:2 Create Additional Loopback Network Adaptor On Windows Server 2019
Its for skipping the error while running Configuring Remote Access Wizard and the error will be like below.
Less than two network interfaces were detected on this machine. For standard VPN server configuration at least two network interfaces need to be installed. Please use custom configuration path instead.
Under Server Manager click Tools >> Computer Management.
From Computer Management window Click Device Manager >> Click VM name from Right side.
Under Actions tab >> Click “Add legacy Hardware”
A add Hardware wizard will open and click Next.
Choose option ” Install the hardware that I manually select from a list ” and click Next.
Choose “Network Adaptors” and click Next.
Choose “Microsoft” as Manufacturer and ” Microsoft KM-TEST Loopback Adaptor ” as Model. Click Next.
Confirm the Install by clicking Next.
Once the install got completed close the install wizard by clicking Finish.
Now, we can confirm the new network adaptor install from the Computer Management panel itself. For that click Device Manager >> Click VM name >> Expand Network Adaptors, there we can see the newly added LoopBack Network adaptor available.
Part:3 Configuring Remote Access Service on VPN Server.
From Server Manager Choose Remote Access >> Right click the Server name >> Choose Remote Access Management.
Under “Direct Access And VPN” Click “Run the Remote Access Setup Wizard”
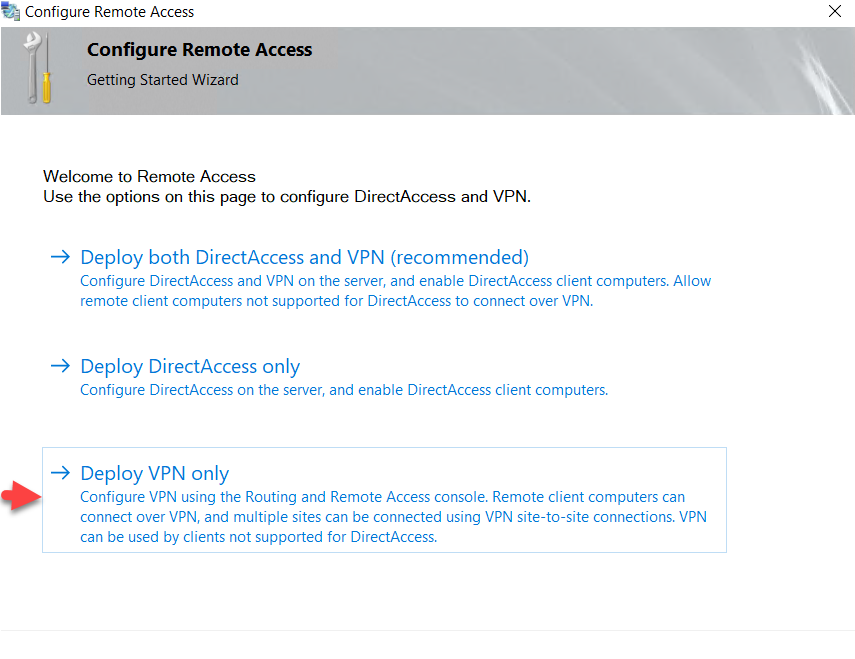
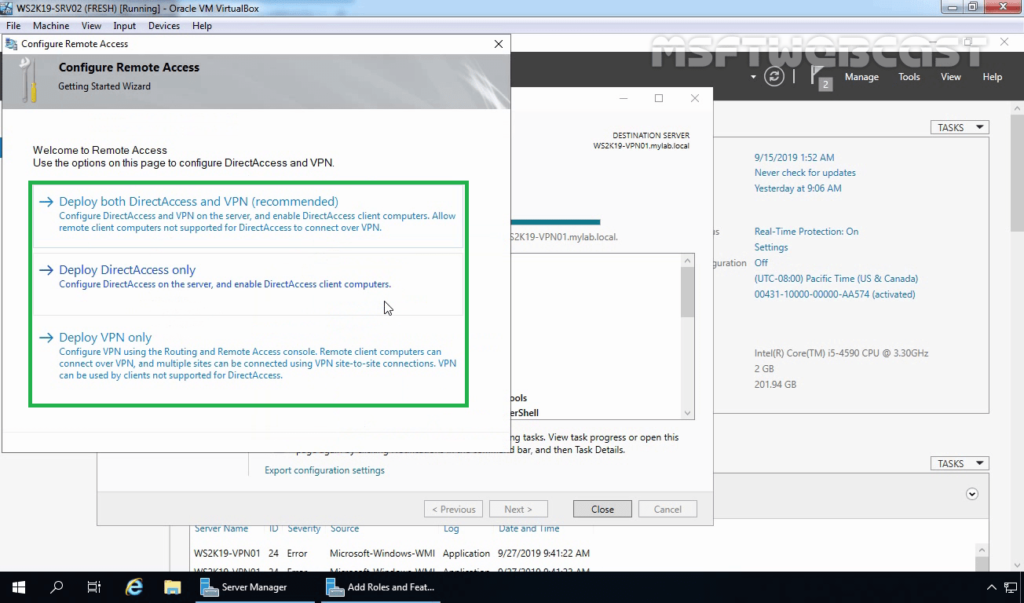
The Configure remote Access wizard will open Click “Deploy VPN only”
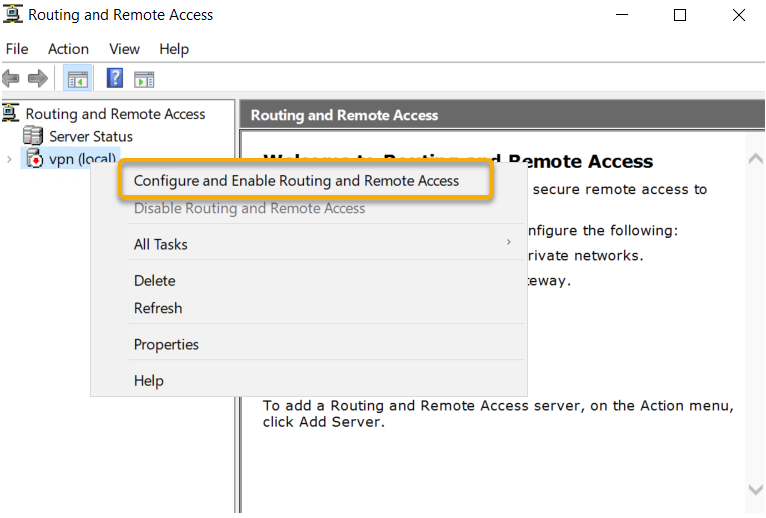
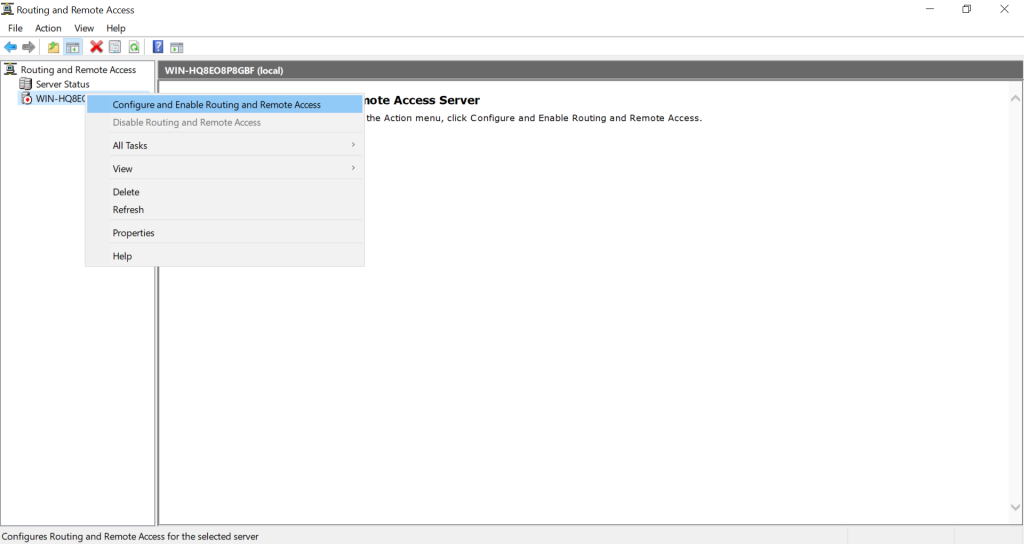
In the Routing and Remote Access Console , right click server name and choose ” configure and Enable routing and remote access ” option.
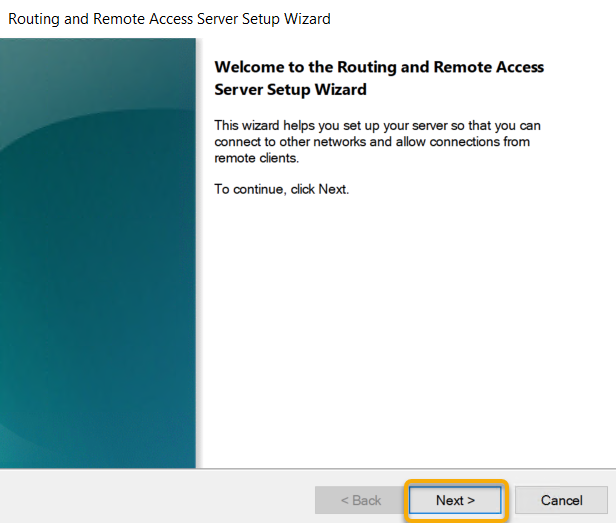
Click Next on Routing and Remote access server setup wizard.
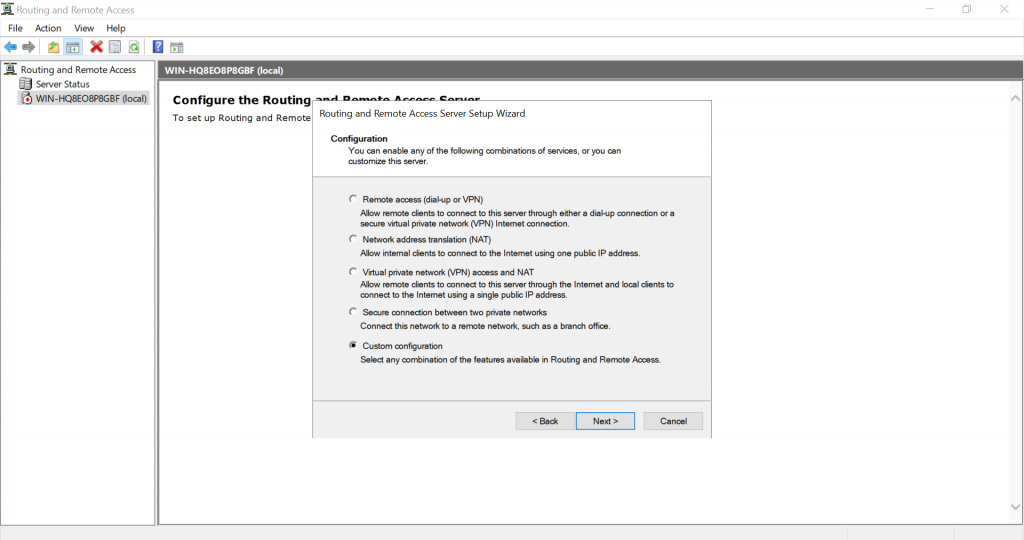
Choose Virtual private network( VPN) access and NAT option. Click Next.
In the select Network Interface section, choose the network adaptor where our public IP configured and click Next.
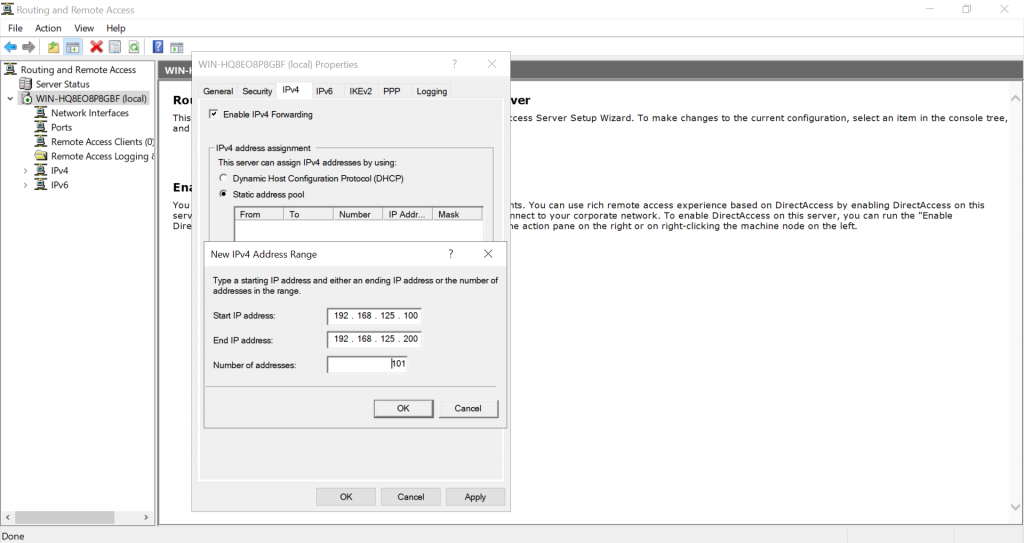
In the IP address Assigned section, choose ” from a specified range of address” and Click Next. Here we are trying to define the private IP address that server give to remote VPN click PC after successful connection.
Click New button.
Give the starting and ending private IP range in the corresponding fields. Click Ok. We are giving IPs starting from 192.168.3.150 to 192.168.3.160.
Now we will see the assigned range and click Next.
In the Do you want to setup this server to work with a radius server question section, select “No, use Routing and Remote Access to authenticate connection requests” and Click next.
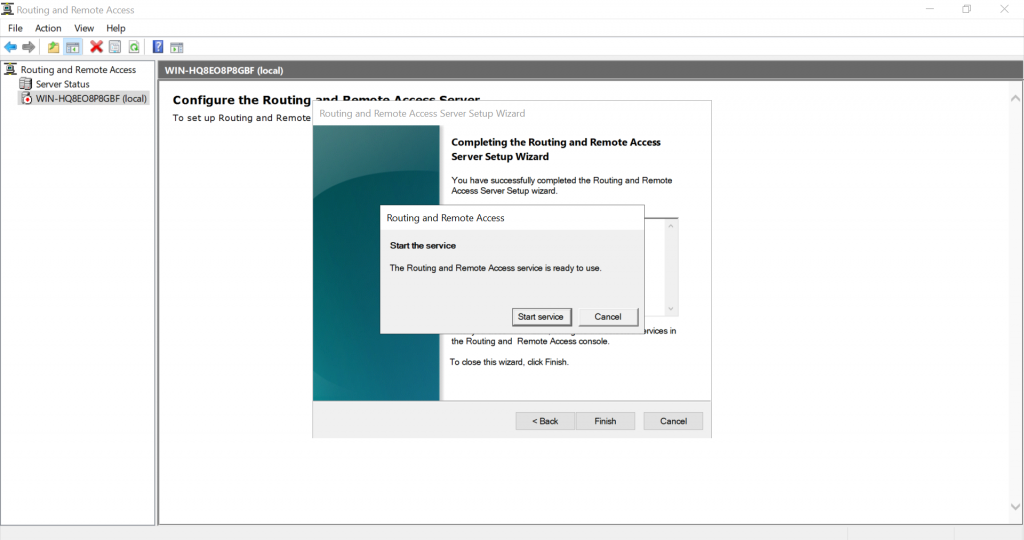
Click Finish on Completing the Routing and Remote Access server setup wizard.
Click Ok.
This completes the configuration of Routing and Remote Access Server. Now we can see a green up arrow next to server hostname and which shows the Routing and Remote access server service started successfully.
Part:4 Allow Remote Access to our VPN server through Public Network Adaptor.
For maintain the access to the VPN server over remote desktop we need to allow the remote access port over our public network adaptor itself through routing and remote access properties section. Otherwise we will loss the access to the server through remote desktop because we only have one Network interface available on server for both VPN traffic and for the remote access.
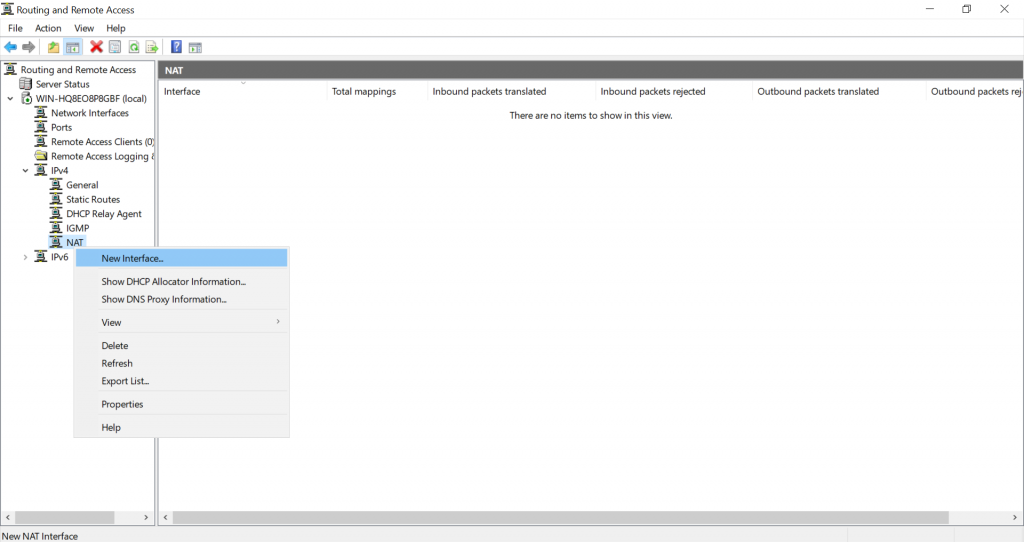
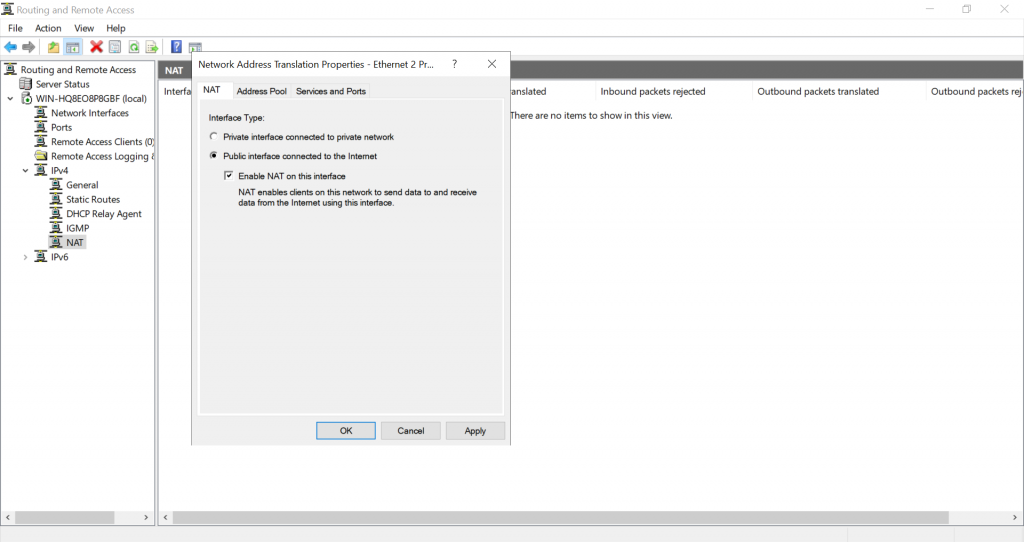
In the Routing and Remote Access Manager , Expand Server name >> Expand IPv4 >> Choose NAT >> Right Click Our Public Network Adaptor and choose Properties.
Select ” Remote Access” , A pop up window will appear, in the Private Address filed give our server public IP address and click OK. After that click Apply and OK.
If you have different RDP port, you need to create a new allow rule by clicking add option.
Part:5 Allow VPN remote access for the Users.
In this part we are giving a existing user on VPN server for remote access. Then only if we give the logins of these server users to remote VPN clients, they can successfully connect to server through VPN.
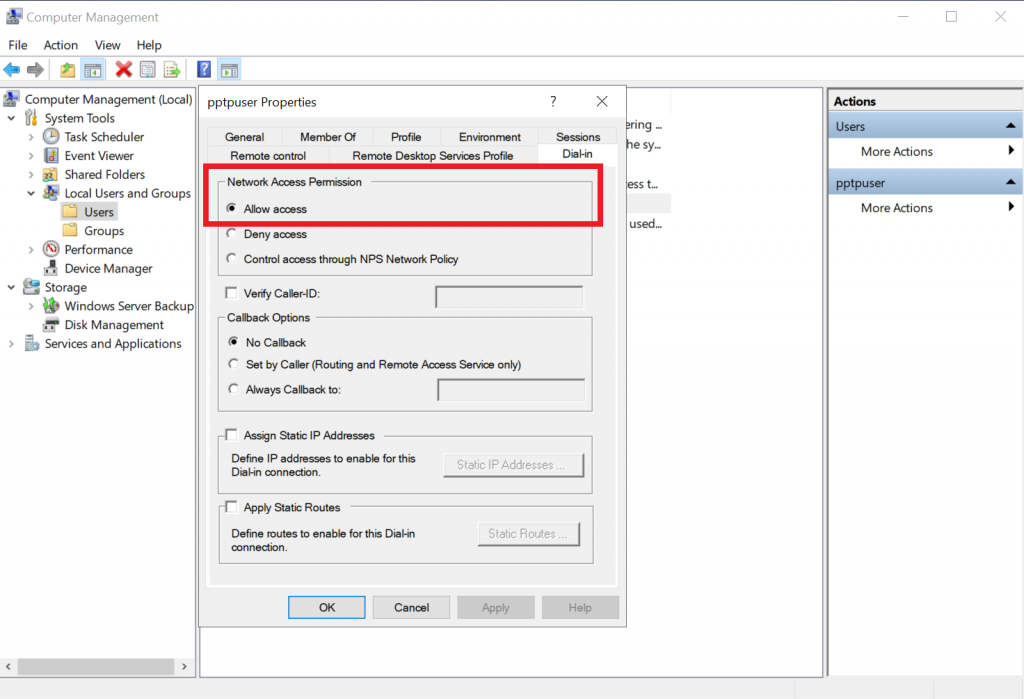
Go to the Computer Management Section >> Expand Local users and Groups >> Choose Users >> Right click a user where we wish to give VPN access and choose properties.
Under “Dial- In” tab >> Choose “Allow Access”. Click Apply and Ok.
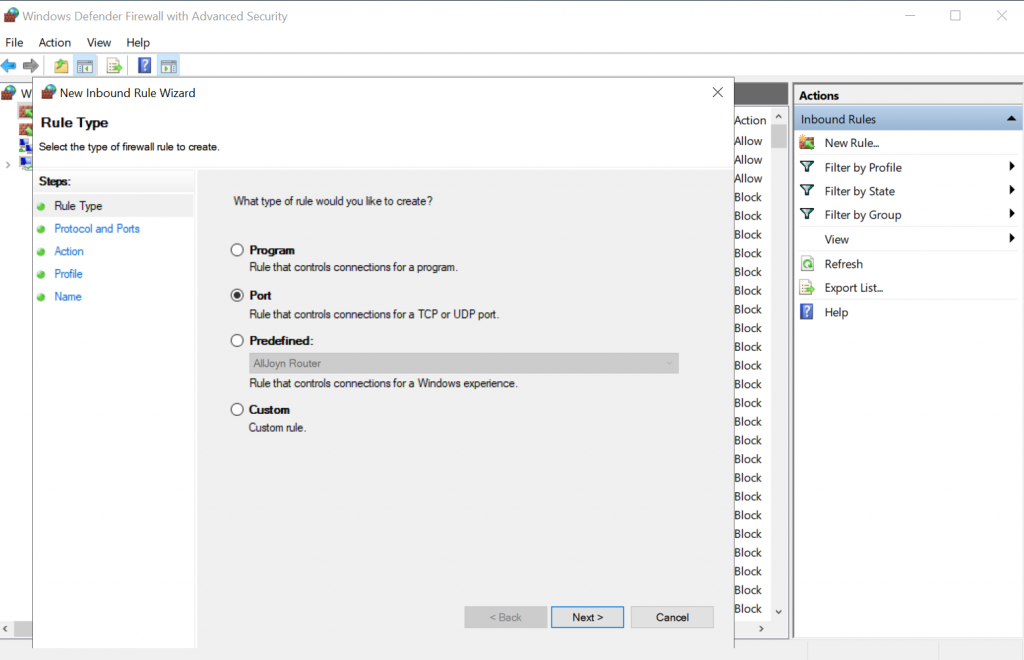
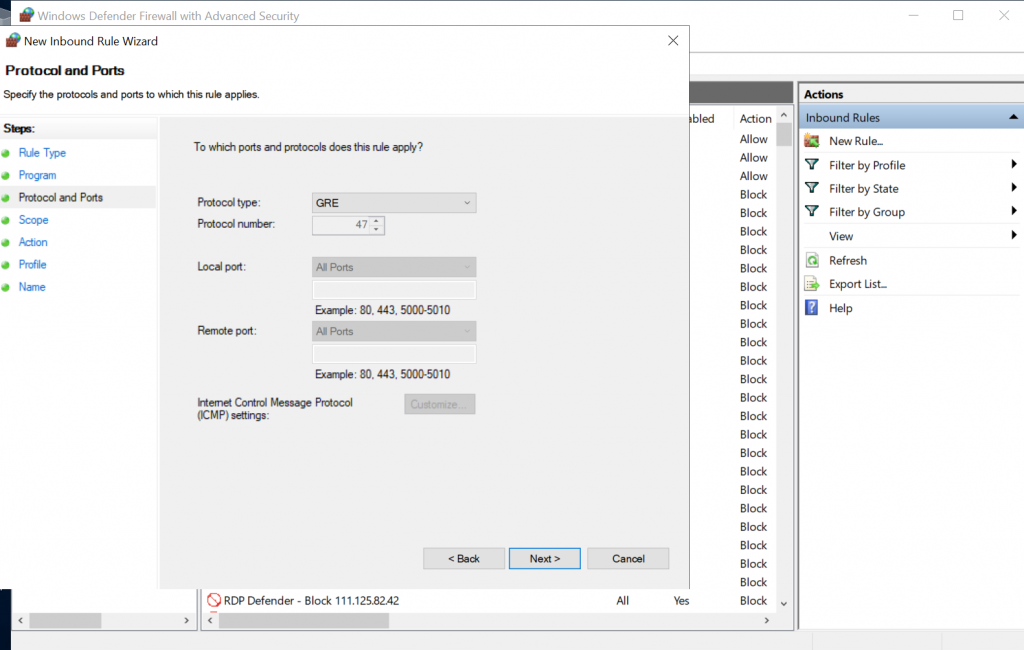
Part:6 Allow VPN ports on Windows Firewall.
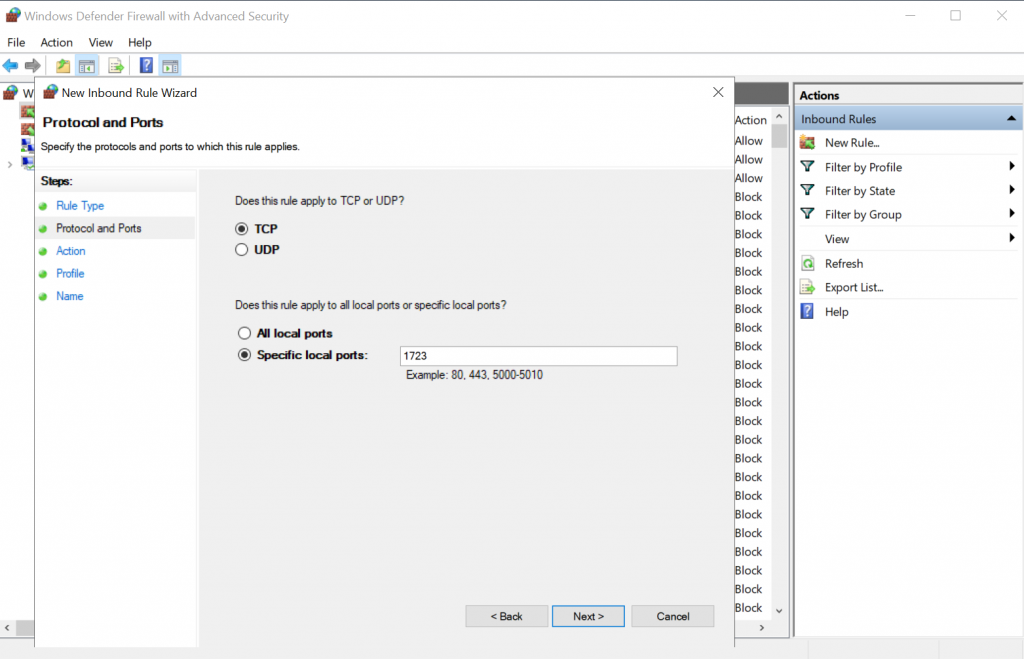
In this part we are allowing the ports used by the VPN server for communication on windows firewall. Otherwise the remote VPN clients won’t be able to communicate with the VPN server. Below are the ports we need to allow in VP server firewall.
- For PPTP: 1723 TCP and Protocol 47 GRE (also known as PPTP Pass-through
- For L2TP over IPSEC: 1701 TCP and 500 UDP
- For SSTP: 443 TCP
Now issue below power shell commands to allow ports in windows firewall.
Now if we look at the windows firewall inbound section , we can see the ports are allowed.
This Completes the PPTP VPN server setup on Windows server 2019. Now Lets Proceed with the Remote VPN Client on Windows 7 PC setup and Try to Establish a VPN server connection.
Step:7 Test VPN Connection.
Open Network and Sharing Center of your local PC/Laptop. Click on ‘Set up a new Connection or Network‘. Please note the screenshots are from a Windows 7 PC.
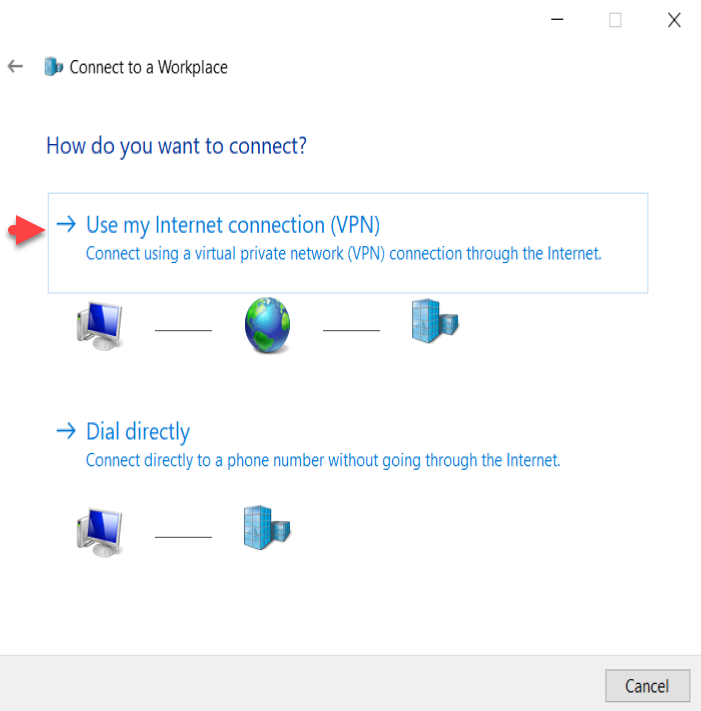
Click on Connect to a workplace.
Click on Use my Internet connection (VPN)
Enter IP address of VPN server (External network’s Primary/static IP which has Internet connection) and click on next.
Enter the user login details of VPN server, the user we created in VPN server or existing one with enabled VPN access and click on Connect.
Now you can see the client machine is trying to connect to the VPN server. Normally the connections are established using PPTP protocol. After successful connection, you can see a new VPN network adapter is created in Client PC Network adapters section.
If you right click on the VPN Network adapter and select “Properties” , you can see many tabs with different settings. Below are the default settings of my Client PC VPN network Adapter.
Refer below screenshots if you have any issues with VPN connection from client side.
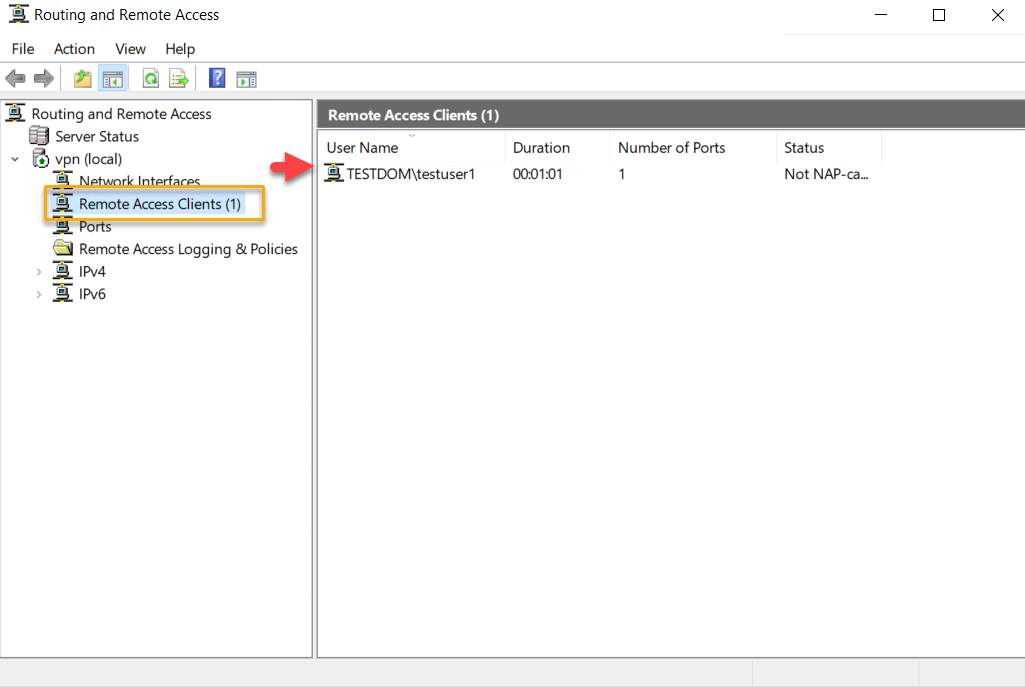
Two other ways to confirm the VPN connection is successful is go back to VPN server 2019 and Open Routing and Remote Access Manager >> From there Expand our server name >> Choose Remote Access client, and in the right side we can see a active connection.
Another option to confirm the successful VPN connection is , open a browser in Windows 7 PC and search the what is my IP and it will show the public ISP IP as VPN server IP. Which means all the internet traffic from client side is routing through our VPN server.
This Concludes the settings up PPTP VPN on Windows server 2019. I hope this blog article is informative. Leave your thoughts in the comment box.
If you are Looking to Convert our PPTP VPN to support SSTP refer our below article.
Share This Story, Choose Your Platform!
Related Posts
9 Comments
-
Maximiliano Ramos
August 27, 2020 at 1:54 am — ReplyHello. I followed this guide to create a VPN network from my clients to our server, but despite all the configurations have been properly completed, the clients are not able to connect nor by SSTP SSL or PPTP. They will not reach out the server public ip address.
Is it possible to get some assistance to get this working?Thanks in advance.
-
admin
August 27, 2020 at 5:17 am — ReplyOkay, we can together find out what causing the issue. Email me the details and error.
-
Mark Fogel
October 13, 2021 at 12:48 pm — ReplyHi thanks for the guide, I have a successful connection to the VPN server however I am unable to connect to anything beyond. Is this a routing issue? Any idea what I should look out for?
Many Thanks,
-
admin
October 13, 2021 at 5:14 pm — ReplyHi Mark, Most probably routing issue. My suggestion is check your local network settings from your PC and make sure there is no Network conflict.
-
-
Tom Phillips
December 3, 2021 at 7:54 pm — ReplyHi,
How do I set this up with machine that is behind our company firewall and is configured with private IP address (access to internet and internal resources). So, basically I can’t configure public IP on this server, we need to use NAT, Firewall public IP -> Windows VPN server private IP. Also, can I use any private IP address for “Address range assignment” or do IPs need to be in the same network as the servers NIC? Thanks, 1st time trying to set this up.-
admin
December 3, 2021 at 8:48 pm — Replyokay, try to choose your private interface which is connected to your Firewall public IP while selecting interface and see if that works.
Also you can use any private IP range in the IP address Assigned section.
-
-
Jason
March 16, 2022 at 11:59 pm — ReplyAwesome guide, the only one I found that works!!
Keep up the good work. -
Aris Repolles
July 29, 2022 at 8:25 am — ReplyHi can you help about VPN connection on the server 2019. i already follow you guide but i enconter an error 807. can you help me?. thank you
-
Aris Repolles
July 29, 2022 at 8:26 am — ReplyHi, can you help with VPN connection on the server 2019? i already follow your guide but i encounter an error 807. can you help me?. thank you
Page load link
Go to Top
This blog post is a step by step guide on how to install Routing and Remote Access Service on Windows Server 2019.
Overview:
The Remote Access server role provides three network access technologies in Windows Server 2019. These technologies are the role services of the Remote Access server role.
- DirectAccess
- Routing and Remote Access
- Web Application Proxy
By using RRAS, you can deploy DirectAccess and VPN connections to provide end-users with remote access to your organization’s network. You can also create a site-to-site VPN connection between two servers at different locations.
- PART-1 How to Install Remote Access Service on Windows Server 2019
- PART-2 How to Install and Configure VPN in Windows Server 2019
- PART-3 Configure Network Policy Server (NPS) for VPN in Windows Server 2019
- PART-4 Configure Port Forwarding and Test VPN Connection on Windows 10
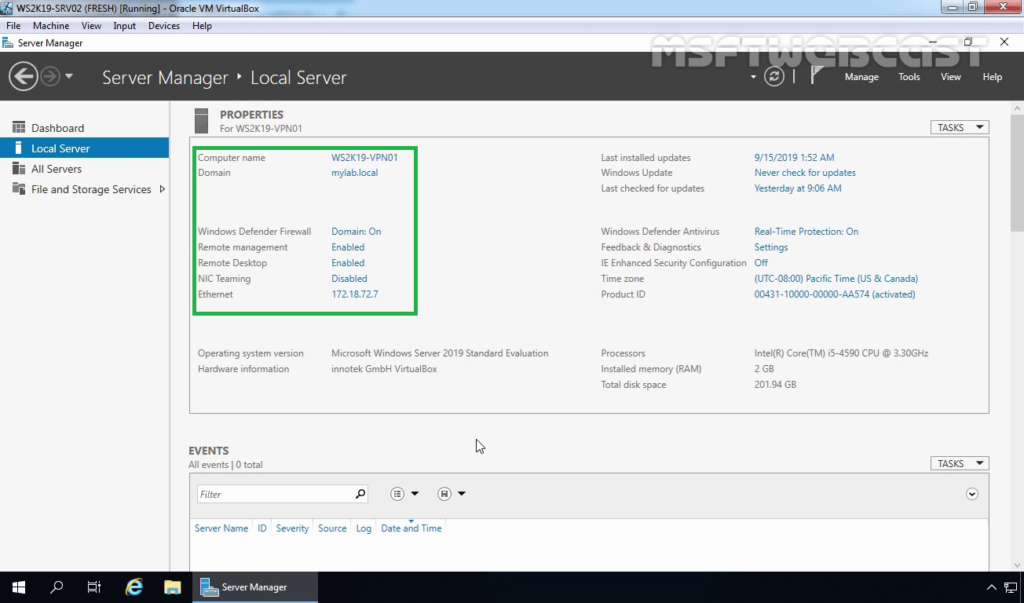
Understanding Test Lab:
- WS2K19-DC01: Domain Controller and DNS server.
- WS2K19-VPN01: Member Server.
- WS10-CLI01: Windows 10 PC.
Install Remote Access service on Windows Server 2019:
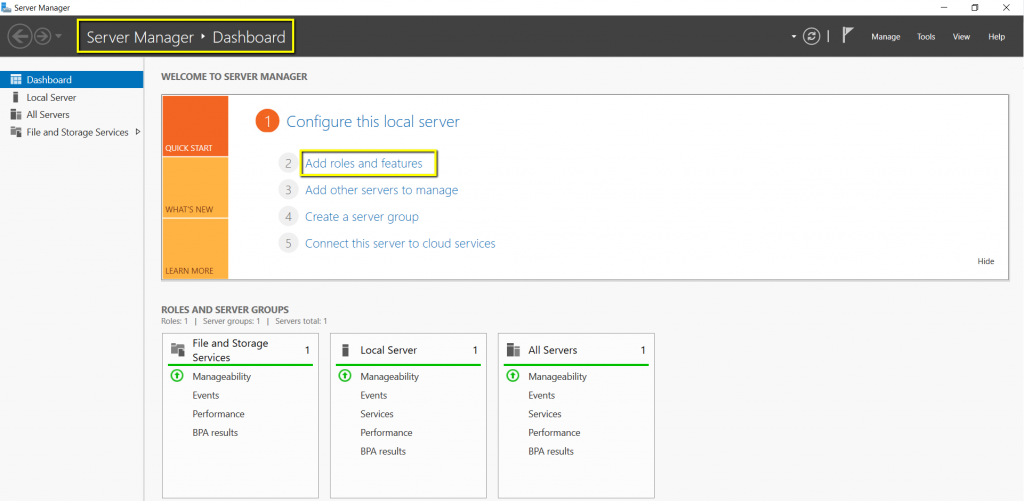
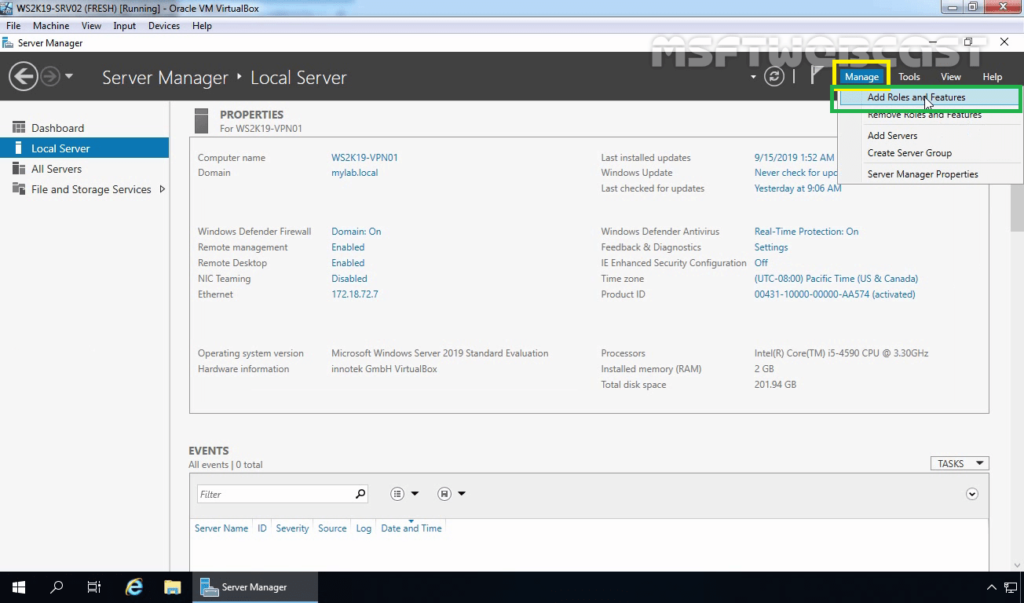
1. Open Server Manager Console.
2. At the top of the Server Manager, click on Manage and select Add Roles and Features.
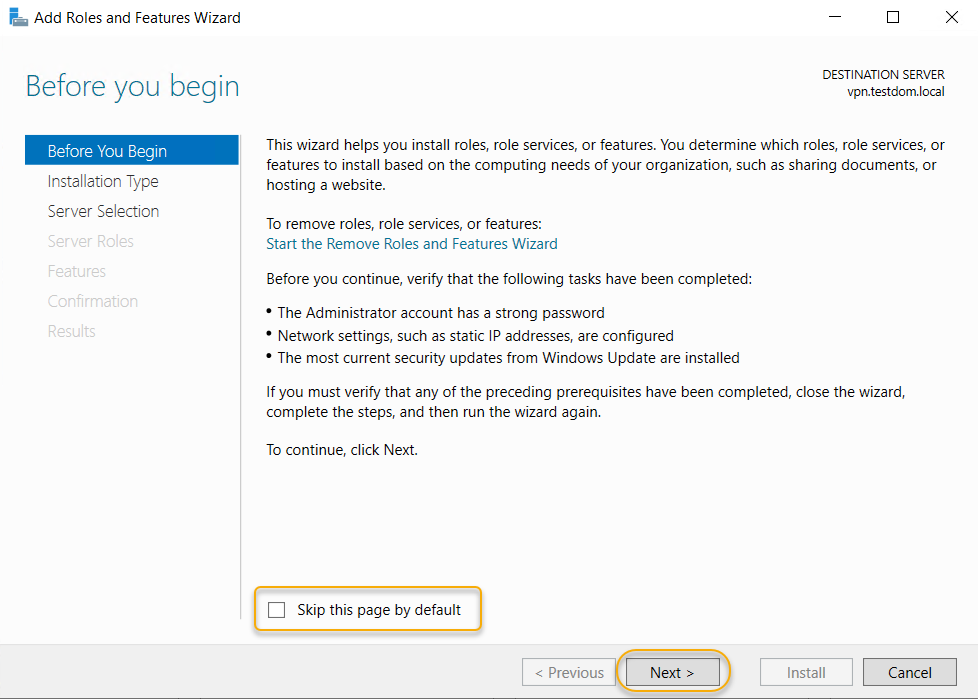
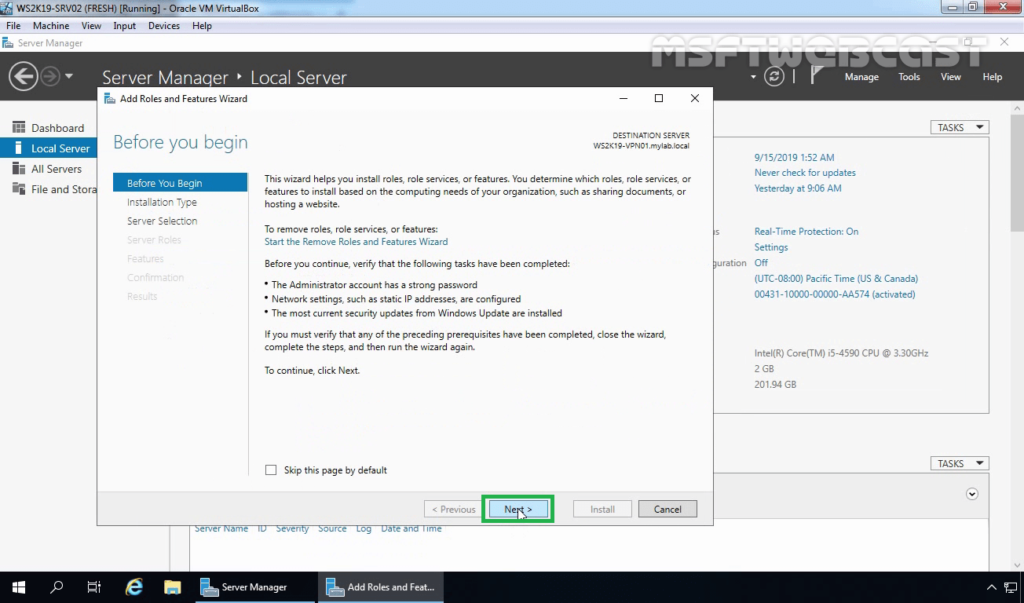
3. On the Before you begin page, click Next.
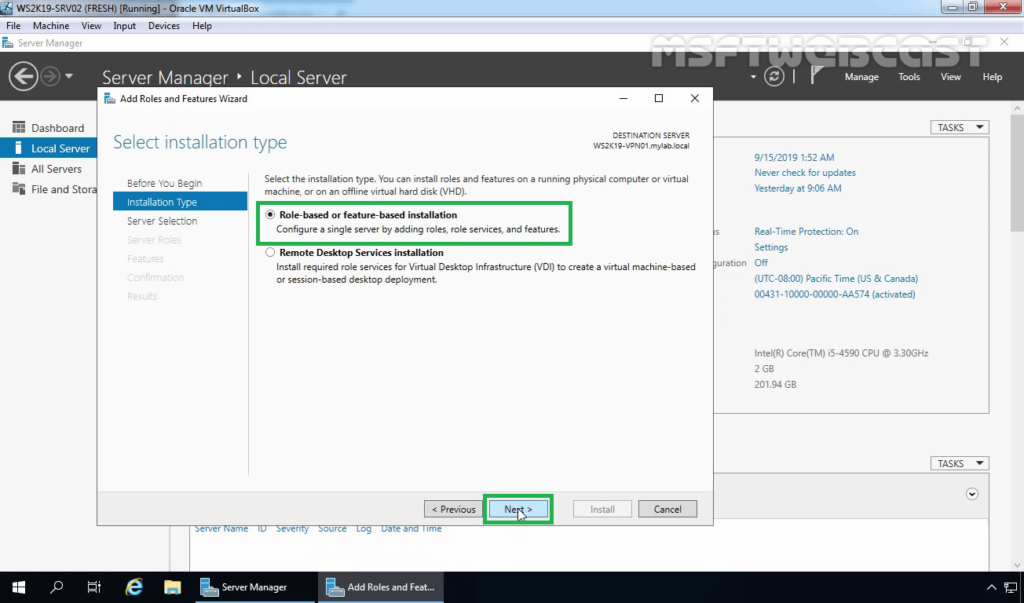
4. Select Role-based or feature-based installation and then click Next.
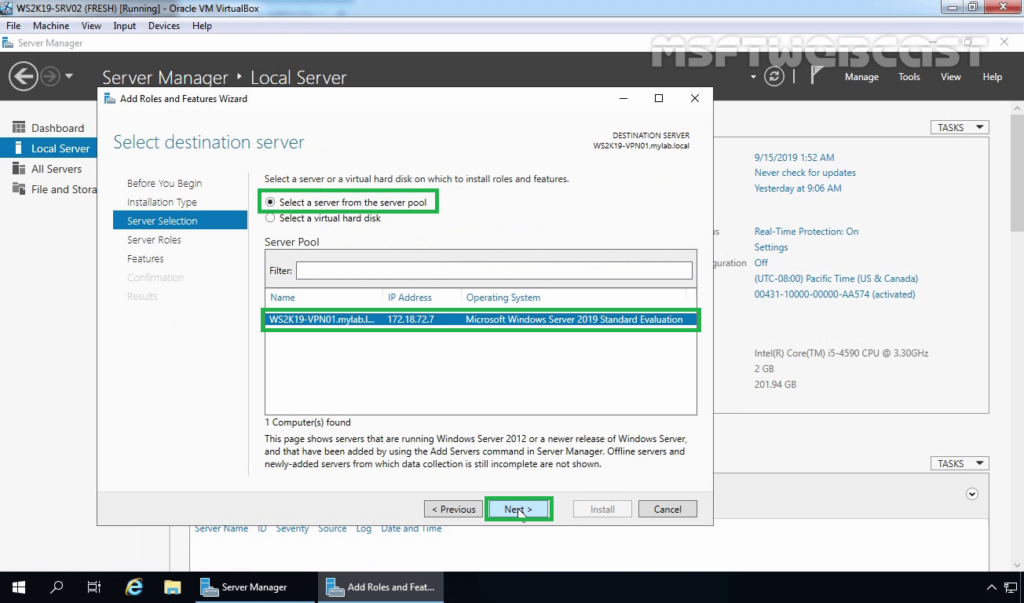
5. Select a server from the server pool on which you want to install the Remote Access Service, click Next.
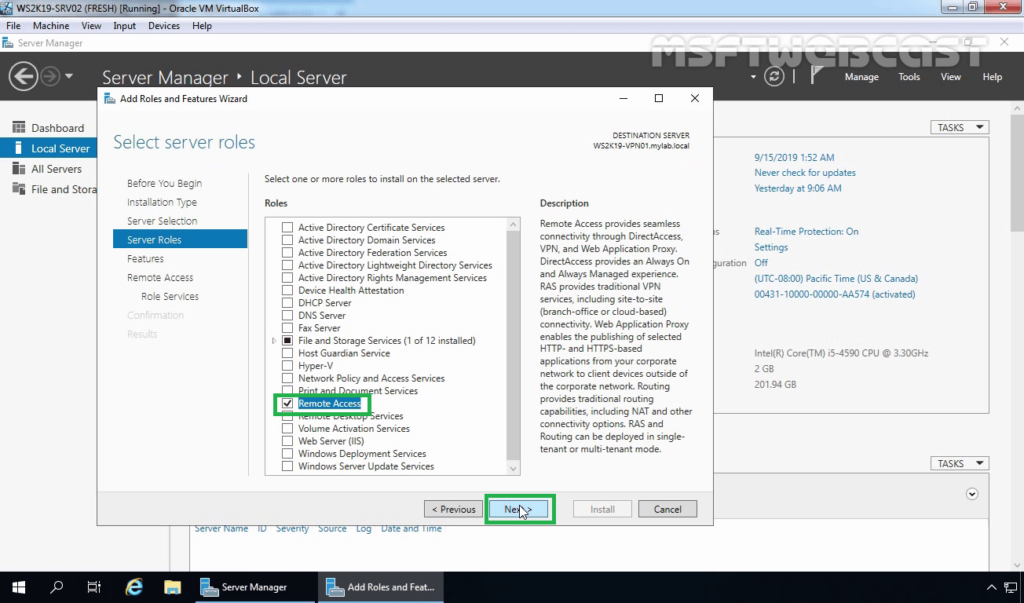
6. On select server roles page, select Remote Access Service. Click Next.
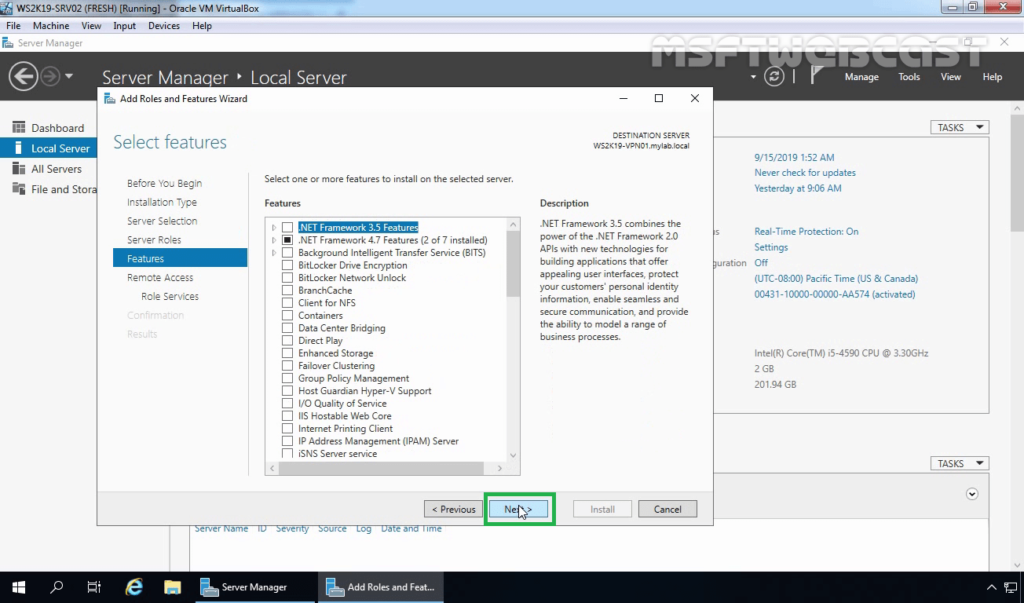
7. On select features page, click Next.
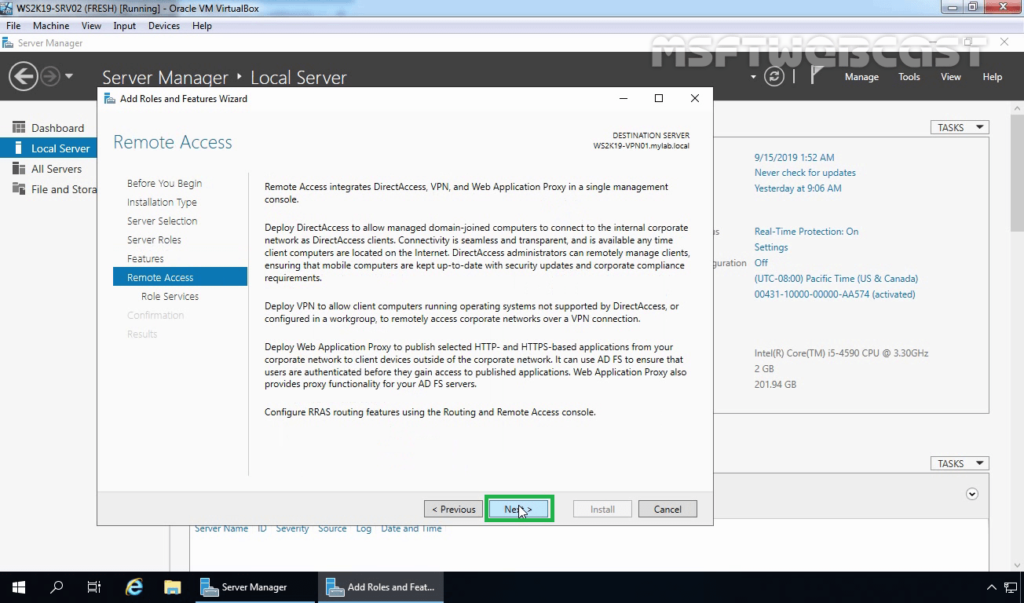
8. On the Remote Access page, read a brief overview of the Routing and Remote Access Service. Click Next.
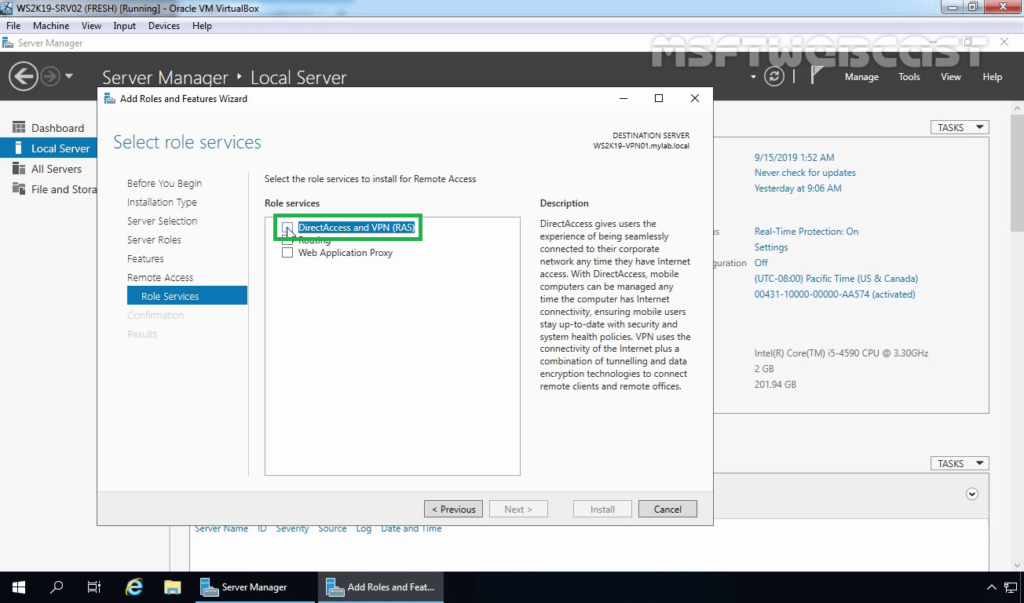
9. On select role services page, select DirectAccess and VPN (RAS) service.
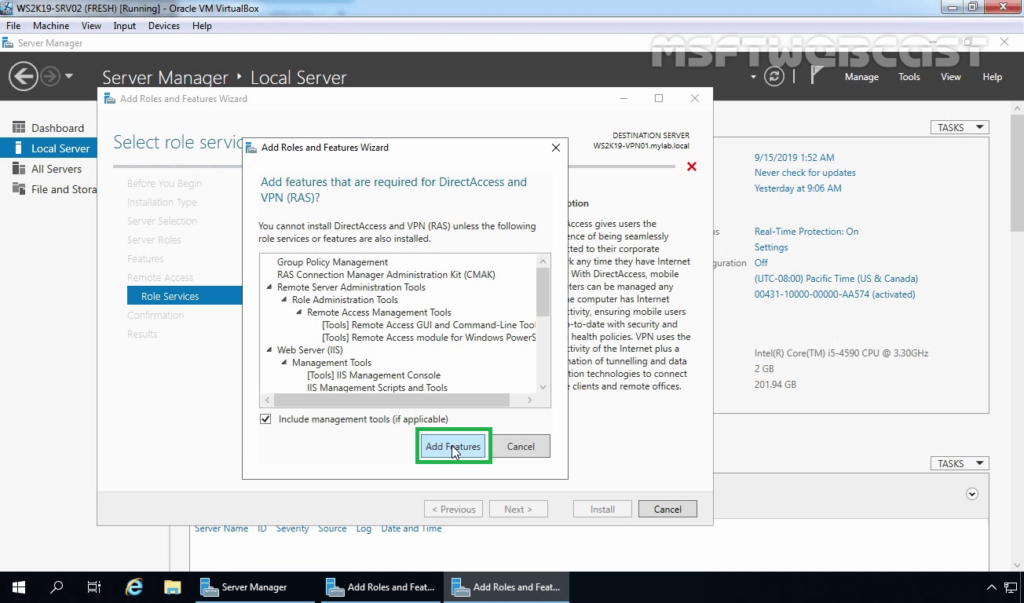
10. A new window will pop up, click on Add Features to include required features and management tools for DirectAccess and VPN.
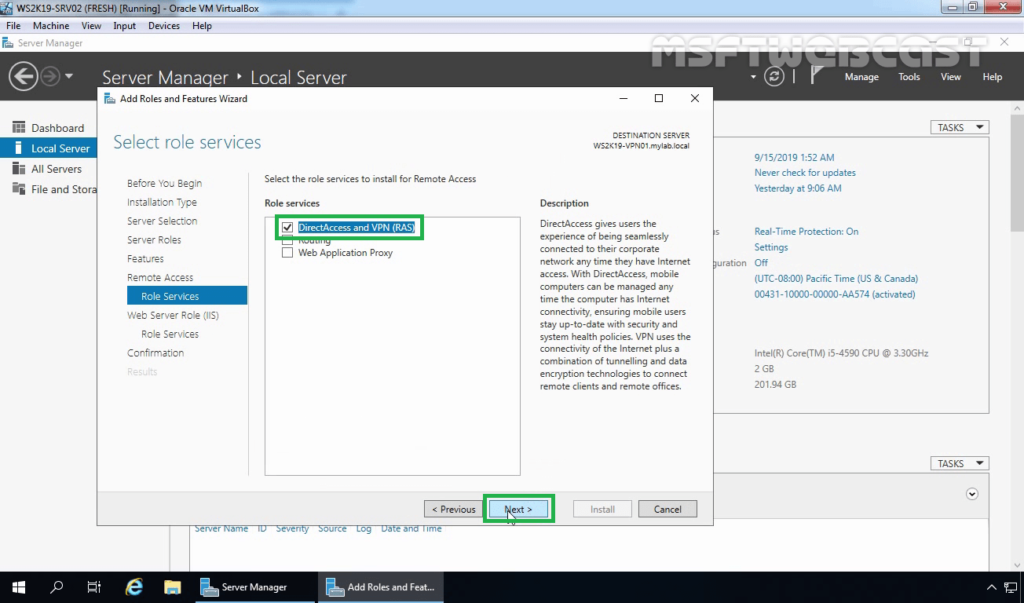
11. Make sure that DirectAccess and VPN role service is selected.
12. On the Web Server Role (IIS) page, read a brief overview of the IIS Service. Click Next.
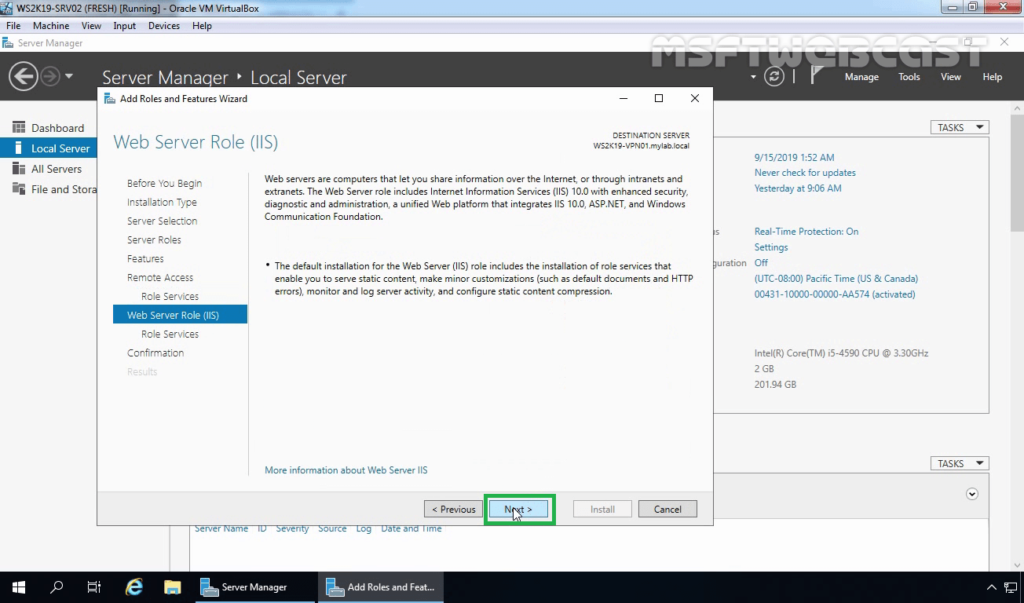
13. All required IIS role services are already selected. Click Next to continue.
14. Click on the Install button to start the installation of Remote Access Service on Windows Server 2019.
15. After installing the Remote Access service on windows server 2019, the next step is to configure the Remote Access server.
16. Click on the Open the Getting Started Wizard link to start the wizard to configure DirectAccess and VPN on Windows Server 2019 Remote Access Server.
17. From this console, we can configure VPN on Windows Server 2019. In the next post on How to Configure VPN using Remote Access Service on Windows Server 2019.
After installing the Remote Access Service, next steps will be configure it.
Thank you for reading.
Post Views: 2,836
A Virtual Private Network (VPN) is used to securely create a tunnel for data between your local computer to a remote server. On Windows Server 2019, you can configure a VPN to provide network access to connected clients and allow connected devices to communicate securely.
This guide explains how to set up a fresh Windows Server 2019 as an L2TP over IPSec, or a PPTP VPN, using the routing and remote access feature. Layer 2 Tunneling Protocol (L2TP) with IPSec offers robust encryption for connections to the server. On the other hand, the Point to Point Tunneling Protocol (PPTP) is simple to deploy but not as secure.
To set up the VPN server, we shall use the built-in Routing and Remote access feature, which offers a graphic interface to configure remote networking features such as Dial-up, LAN routing, NAT, and VPN.
Requirements
-
Deploy a Windows Server 2019 Instance on Vultr
-
Remotely connect to the server and log in as an Administrator
Create a New VPN User
For the VPN service to work well, it must authenticate with a valid user account to the server. So, you need to create a new user on the server.
Click Tools under server manager and select Computer Management from the drop-down list to create a new user.
Once the computer management window pops up, expand Local Users and Groups from the left pane and right-click Users to select New User on the sub-menu.
Under the New User dialog box, enter a username, full name, and password for the VPN user, then click create and close the window.
The new user will now be listed on the list of active server users, right-click on the new user and select properties.
Under the user properties window, navigate to the Dial-in tab and click Allow access under Network Access Permission. Click OK for changes to take effect.
Install the Routing and Remote Access Features
Procedure 1: Through Server Manager
From the Windows start menu, open Server Manager, click Manage, then select Add Roles and Features from the drop-down list.
From the open window, click next and select Role-based or feature based installation, then select your server from the pool. Select Remote Access, Remote Access Administration from the list of server roles.
Next, select DirectAccess and VPN (RAS) and Routing from the features list, then click to Install IIS, which is required for remote access to work well.
Procedure 2: Using Windows PowerShell
You can also install Remote Access from Windows Powershell.
From the Windows start menu, open an Administrative Powershell, then install Remote access by pasting the following code to the console.
Install-WindowsFeature RemoteAccess
Install-WindowsFeature DirectAccess-VPN -IncludeManagementTools
Install-WindowsFeature Routing -IncludeManagementTools
Your output should be similar to:
PS C:UsersAdministrator> Install-WindowsFeature RemoteAccess
>> Install-WindowsFeature DirectAccess-VPN -IncludeManagementTools
>> Install-WindowsFeature Routing -IncludeManagementTools
Success Restart Needed Exit Code Feature Result
------- -------------- --------- --------------
True No Success {Remote Access}
True No Success {RAS Connection Manager Administration Kit...
True No Success {Routing}
Configure Routing and Remote Access
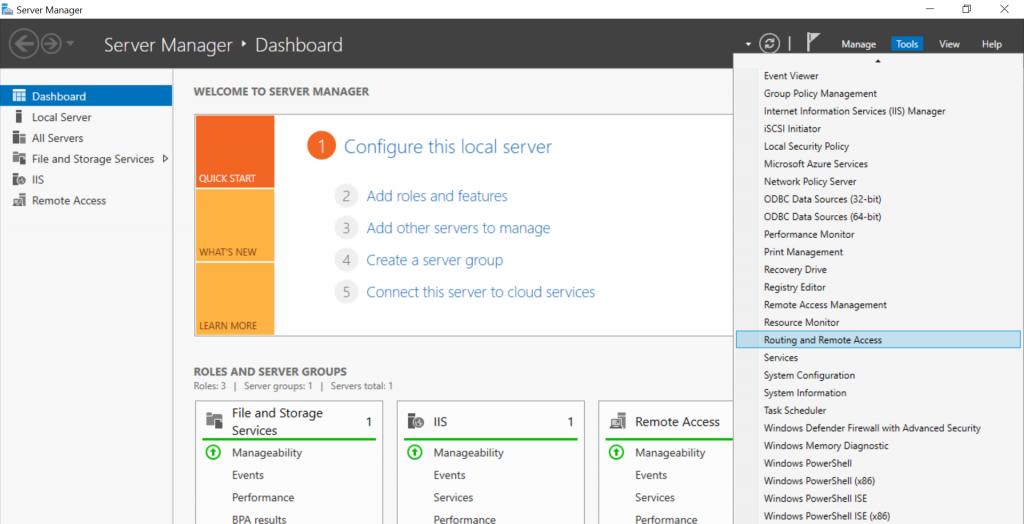
Open Server Manager and click Tools on the top toolbar. From the drop-down list, select Remote Access Management.
In the open Routing and Remote Access window, right click on your server name just below Server status, then select Configure and Enable Routing and Remote Access from the drop-down menu.
Now, select Custom configuration to configure remote access manually.
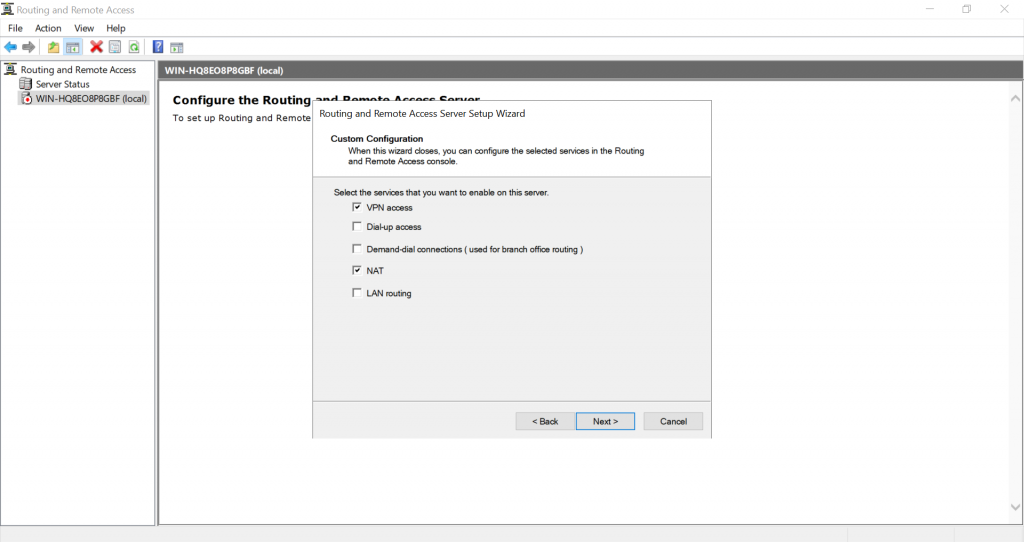
Select VPN Access and NAT as services you want to enable on your server, click next to finish the configuration, and start the service.
Setup a PPTP VPN
Now that Remote Access is running, you can set up your PPTP VPN. To get started, you must assign connected clients** static IP Addresses to avoid possible connection issues. To do this, right-click on your server under the Routing and Remote Access window and select Properties from the drop-down list.
Click IPV4 in the Open Window, then select Static address pool. Now, click Add to craft a new IP Address range from the open pop-up window. In this guide, we use the range 10.0.0.1 to 10.0.0.50, and the server will automatically calculate the number of available addresses.
Click OK to save your static IP Address configuration. You will be prompted to restart Routing and Remote Access for changes to apply; simply click OK.
Configure NAT and enable PPTP
We need to configure Network Address Translation (NAT) for connected clients to use the Internet. On the left pane of the same routing and remote access window, expand the IPv4 options under your server. Right-click on NAT and select New Interface.
Under the open dialog window, select Public interface and enable NAT on the interface.
Next, navigate to Services and Ports and click VPN Gateway (PPTP) from the drop-down list.
Click Edit to set a Private address for the VPN service, change the current address 0.0.0.0 to 127.0.0.1, and click OK to save.
Finally, click OK to save all changes, then right-click on your server from the left pane and click Restart under the All Tasks sub-menu.
This will restart routing and remote access services making your server ready for incoming VPN connections.
Configure Windows Firewall to accept Incoming PPTP VPN Connections
Click Tools from the Windows server manager and select Windows Defender Firewall with Advanced Security from the drop-down list.
Under the open Windows Defender Firewall with Advanced Security window, select Inbound Rules on the left pane, then click New Rule on the right pane.
In the open new Inbound rule wizard, click Predefined and select Routing and Remote Access from the list.
Under predefined rules, choose Routing and Remote Access (PPTP-In), click next to allow the connection, then finish for the new Firewall rule to be applied and test your new PPTP VPN server.
Test your PPTP VPN
Using your personal computer (PC) or Smartphone, go to Networks, Add a new VPN and select PPTP as the VPN type. Then, enter the VPN username and password created earlier to connect.
In this guide, we cover and test the PPTP VPN on a Windows 10 PC. To get started, click the start menu and search for Control Panel, then, click Network and Internet.
Under Network and Internet, open the Network and Sharing Center and click Set up a new connection or network.
Under the open window, select Connect to a workplace and click Use my Internet connection (VPN).
Then, enter your server’s public IP Address (Check your Vultr server dashboard), assign the connection a name, and click create.
Now, on the left pane, click Change adapter settings, then right click your created VPN interface and select Properties.
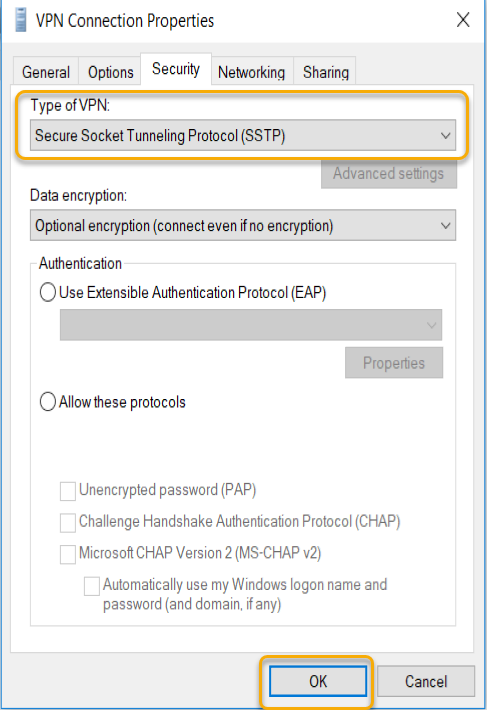
Under the pop-up, click Security, then choose Point to Point Tunneling Protocol (PPTP) under Type of VPN.
Finally, under Allow these protocols, select CHAP and MS-CHAP v2, then click OK to apply changes.
Your new VPN is configured successfully. Click the network connection icon on the taskbar, select your VPN on the list and click Connect to enter the VPN username and password created earlier to establish a connection to your new PPTP VPN server.
Setup L2TP with IPSEC
Open server manager, click Tools, and open Remote Access Management, then right-click your server on the left pane to select Properties from the drop-down list.
Under server properties, navigate to the Security tab, and click Allow custom IPSec policy for L2TP/IKEv2 connection to enter your new pre-shared key.
In this guide, we use 12345678, choose something stronger, then navigate to IPV4 to set a static address pool and click OK to apply changes.
Keep note of the pre-shared key (PSK) since it will be required for every user establishing a connection to the VPN server.
From the left pane, expand the IPV4 sub-menu and right-click on NAT, then select New Interface. If you set PPTP earlier, click NAT and edit the existing interface you already created.
Navigate to the Services and Ports tab and select VPN Gateway [L2TP/IPSec], then click edit to change the private address from 0.0.0.0 to 127.0.0.1. Click OK to save changes and restart remote access from the left pane under All Tasks.
This will restart Routing and Remote Access, then save the applied L2TP configurations.
Allow L2TP Connections through Windows Firewall
Open Windows Defender with Firewall, select inbound rules and add a new rule. Select Predefined and from the list, choose Routing and remote access.
Under Predefined rules, select Routing and Remote Access [L2TP-In] and click next.
Finally, allow the connection and click Finish to apply the new Firewall rule.
Connect and Test Your L2TP VPN server
In this guide, we test the new L2TP with IPSec VPN on a mac. To get started, open System Preferencesand click Network.
Under the Network Preferences window, click the + sign and select VPN under the Interface dialog box. Then, choose L2TP with IPSec as the VPN Type and assign your connection a name.
Click create, then enter your public server IP Address (server address) and username (Account name). Next, click Authentication Settings to enter your account password and Pre-shared key (Shared secret) created earlier.
Next, click Advanced and select Send all Traffic over VPN Connection, then click Apply, and finally click Connect to establish a connection with your new L2TP VPN server.
Conclusion
You have set up a VPN on your Windows server 2019 instance; you can choose to create both PPTP and L2TP VPNs with different users connecting through your server without any limitations.
For every connected device, they will be able to access the Internet through your server and interact with other connected computers.
On Windows Server 2019, a virtual private network (VPN) is a convenient method to allow users to access resources using an encrypted connection from a remote location and through the internet.
Typically, organizations use VPN to extend their private network to allow employees to work from home or another remote location to access files, apps, intranet websites, printers, and other resources through a public network as if they were directly connected into the company’s network.
The way you set up a VPN server hasn’t really changed in many years, which means that the same instructions to configure a virtual private network on Windows Server 2019 applies to older versions, including Windows Server 2016, 2012 R2, and older versions. If you have a Windows 10 device, you can use the “Incoming Connection” feature to set up a VPN server to connect remotely to your home network to access your computer’s files and peripherals, and even other computers in the network.
In this guide, you’ll learn the steps to set up a VPN server on Windows Server 2019.
- How to add VPN role feature on Windows Server
- How to set up VPN server on Windows Server
- How to allow VPN connections through firewall on Windows Server
- How to allow users access through VPN on Windows Server
- How to set up port forwarding on router to enable VPN access
- How to set up a VPN connection on Windows 10
- How to set up a VPN server on Windows 10
How to add VPN role feature on Windows Server
To add the Routing and Remote Access role to set up a VPN server on Windows Server 2019, use these steps:
-
Open Start.
-
Search for Server Manager and click the top result to open the utility.
-
Click the Manage menu button from the top-right corner and select the Add Roles and Features option.
Windows Server add roles option -
Click the Next button.
-
Select the Role-based or feature-based installation option.
Role-based or feature-based installation option -
Click the Next button.
-
Choose the Select a server from the server pool option.
-
Select the server name.
Select destination server option -
Click the Next button.
-
Check the Remote Access option.
Remote access server role option -
Click the Next button.
-
Click the Next button again.
-
Click the Next button one more time.
-
Check the DirectAccess and VPN (RAS) option.
DirectAcess and VPN RAS option -
Click the Add features button.
-
Click the Next button.
-
Click the Next button again.
-
Click the Next button one more time.
-
Click the Install button.
Windows Server 2019 install VPN server option -
Click the Close button.
Once you complete the steps, the VPN server module will install on the device, and you can proceed to configure the remote access feature.
To configure a VPN server on Windows Server 2019, use these steps:
-
Open Start.
-
Search for Server Manager and click the top result to open the utility.
-
Click the Manage menu button from the top-right corner and select the Routing and Remote Access option.
Windows Server 2019 Routing and Remote Access option -
Right-click the server name and select the Configure and Enable Routing and Remote Access option.
Configure and Enable Routing and Remote Access -
Select the Custom configuration option.
Custom configuration option -
Click the Next button.
-
Check the VPN access option.
Windows Server 2019 VPN access option -
Click the Next button.
-
Click the Finish button.
-
Click the Start service button.
-
Right-click the server name and select the Properties option.
Windows Server 2019 VPN properties option -
Click the IPv4 tab.
-
Under the “IPv4 address assignment” section, check the Static address pool option (recommended).
VPN server static address pool option Quick note: If you have DHCP server configured, you can use the Dynamic Host Configuration Protocol (DHCP) option to handle the distribution addresses. However, if you want to control the access to the network, or you don’t have a DHCP server, then the static pool option is your best option. When using this option, make sure to assign an IP range it won’t assign to other devices in the local network.
-
Click the Add button.
-
Specify a start IP address.
-
Specify an end IP address.
VPN address range setup -
Click the OK button.
-
Click the Apply button.
-
Click the OK button.
-
Right-click “Remote Access Logging & Policies” and select the Launch NPS option.
Windows Server 2019 launch NPS -
Select the Network Policies option from the left pane.
Network Policies -
Double-click the Connections to Microsoft Routing and Remote Access server policy.
-
Under the “Access Permission” section, select the Grant access. Grant access if the connection request matches this policy option.
Connection to VPN policy -
Click the Apply button.
-
Click the OK button.
-
Double-click the Connections to other access servers policy.
-
Under the “Access Permission” section, select the Grant access. Grant access if the connection request matches this policy option.
Connection to other server policy -
Click the Apply button.
-
Click the OK button.
-
Close the Network Policy Server console.
After you complete the steps, the VPN server will be created on Windows Server 2019, but you’ll still need to configure the users who are allowed to connect, and you need to configure the firewall to allow connections.
Windows Server 2019, 2016, 2012 R2 and older versions include more options to set up a more secure and advanced VPN server. In this guide, we’re only covering the fast and secure way to get started with the remote access feature.
How to allow VPN connections through firewall on Windows Server
While configuring the Routing and Remote Access feature on Windows Server should automatically open the necessary Windows Firewall ports, you want to make sure the firewall is properly configured.
To allow VPN connections through the firewall on Windows Server 2019, use these steps:
-
Open Start on Windows Server 2019.
-
Search for Allow an app through Windows Firewall, and click the top result to open the experience.
-
Click the Change settings button.
-
Scroll down and make sure Routing and Remote Access is allowed on Private and Public.
-
click the OK button.
After you complete the steps, the Windows Server VPN server should be able to receive connections remotely from other computers.
How to allow users access through VPN on Windows Server
To allow users access through the virtual private network, use these steps:
-
Open Start.
-
Search for Server Manager and click the top result to open the utility.
-
Select the Active Directory Users and Computers option.
Quick note: If you don’t have Active Directory configured on your server, select the Computer Management option, expand the Local Users and Groups branch from the left pane.
-
Click on Users from the left pane.
-
Double-click the user you want allow remote access.
-
Click the Dial-in tab.
-
Under the “Network Access Permission” section, select the Allow access option.
Windows Server 2019 enable user VPN access -
Click the Apply button.
-
Click the OK button.
Once you complete the steps, you may need to repeat the steps to enable other users to access the network using a VPN connection.
These instructions show you the steps to allow remote access on each user individually. If you need to configure access for a lot users, you can also create a group to configure VPN access for users more easily.
How to set up port forwarding on router to enable VPN access
To be able to connect through a public network (such as the internet) to the VPN server, you’ll need to forward port 1723 (Point to Point Tunneling Protocol (PPTP)) to allow VPN connections.
Here are the instructions that will help you set up port forwarding on a router. You can also visit your router’s manufacturer website for more assistance to configure Port Forwarding.
In addition to the forwarding the required port, you’ll also need to know the public IP address assigned to you by your Internet Service Provider (ISP). You will need this information to contact your VPN server remotely.
To find out if your current public IP address, open your web browser, and using any search engine, perform a search for “What’s my IP”, and your information will appear in the first result.
If the network uses a dynamic public IP address, which can change at any time, then you’ll need to configure DDNS (Dynamic Domain Name System) in your router to avoid having to configure the VPN setup every time your public IP address changes.
Here are the instructions that will help you set up DDNS on your router. You can also visit your router’s manufacturer website for additional help to configure DDNS.
How to set up a VPN connection on Windows 10
After setting up the VPN server on Windows Server 2019, you’ll need to configure the devices that will be accessing your local network remotely. You can set up any device, including your desktop, laptop, tablet, and even phone (for example, Android and iPhone). Here are the instructions to set up a VPN connection on Windows 10.
After adding a VPN connection on your computer, you have to adjust the settings with these steps:
-
Open Control Panel.
-
Click on Network & Internet.
-
Click on Network and Sharing Center.
-
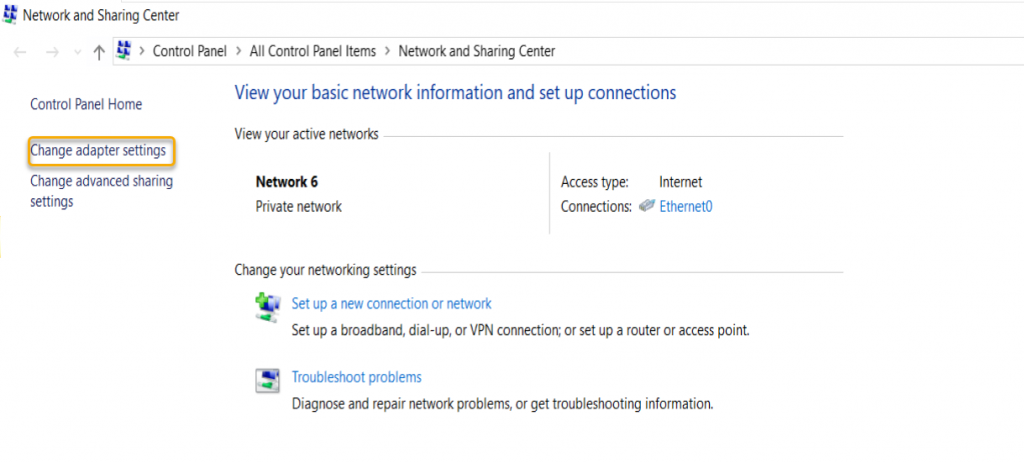
Click the Change adapter settings link from the left pane.
-
Right-click the VPN adapter and select the Properties option.
-
In the General tab, make sure you’re using the correct domain you created while configuring DDNS — or at least you’re using the correct public IP address.
-
Click on the Security tab.
-
Under “Type of VPN,” select the Point to Point Tunneling Protocol (PPTP) option.
-
Under “Data encryption,” select the Maximum strength encryption (disconnect if server declines) option.
-
Click the OK button.
-
Click on the Networking tab.
-
Uncheck the Internet Protocol Version 6 (TCP/IPv6) option.
-
Check the Internet Protocol Version 4 (TCP/IPv4) option.
-
Select the Internet Protocol Version 4 (TCP/IPv4) option.
-
Click the Properties button.
-
Click the Advanced button.
-
Clear the Use default gateway on remote network option.
Important: We’re disabling this option to prevent your web traffic to go through the remote connection, which can slow down your internet connection. However, if you’re looking to access the internet through a VPN connection, then don’t change this last setting.
-
Click the OK button.
-
Click the OK button again.
-
Click the OK button once more.
-
Open Settings.
-
Click on Network & Internet.
-
Click on VPN.
-
Select the VPN connection option and click the Connect button.
Windows 10 remote connection using VPN
Once you complete the steps, the device should be able to connect to VPN server from a remote location.
This step by step tutorial will help you configure a VPN server on Windows server 2019 easily.
First of all, please install the Remote Access Role through Windows PowerShell or Server Manager as highlighted in the screenshot.

Next select DirectAccess and VPN (RAS) in Role services.

For the next steps, use default settings. When the installation completes, a wizard to configure VPN server opens. After that, below window will open. In this, click on Deploy VPN only.

This will open the Routing and Remote Access window.

In the below window, right-click on the server name and then on Configure and Enable Routing and Remote Access.

This will take you to the window as shown below. Click on Next.

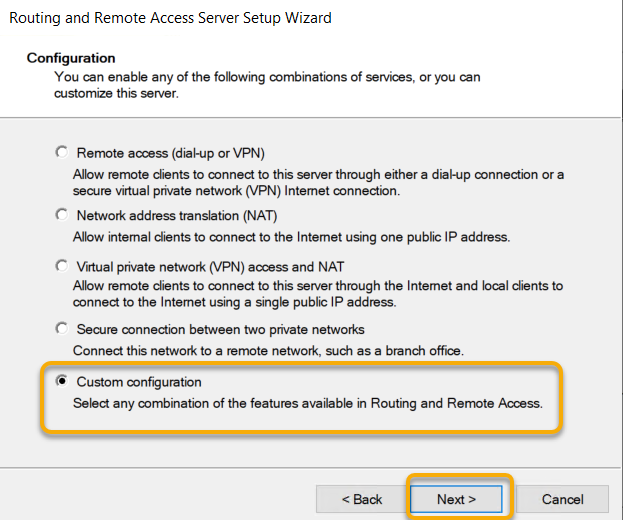
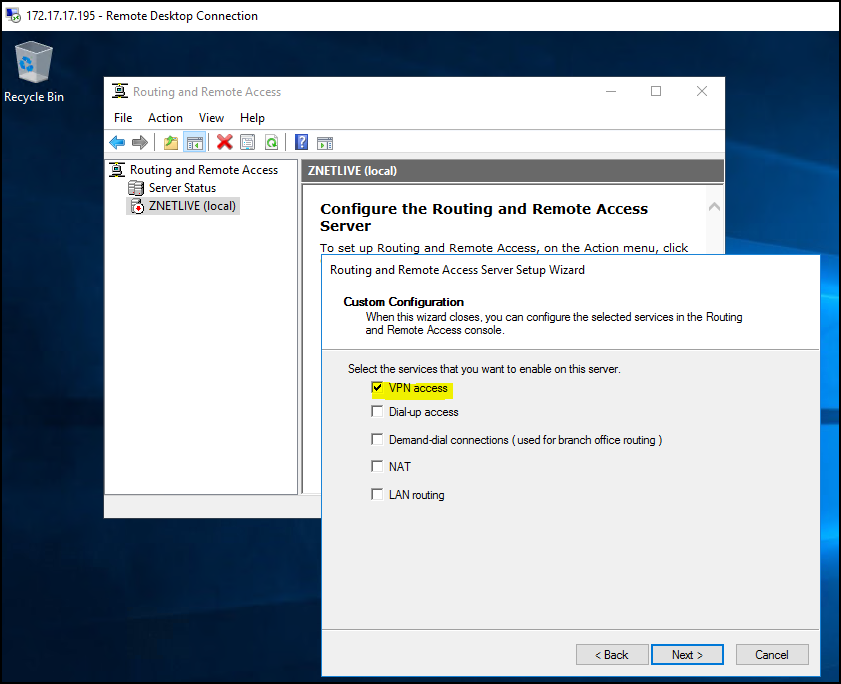
In the Routing and Remote Access Server Setup Wizard window, you need to select Custom Configuration, as highlighted in the screen below.

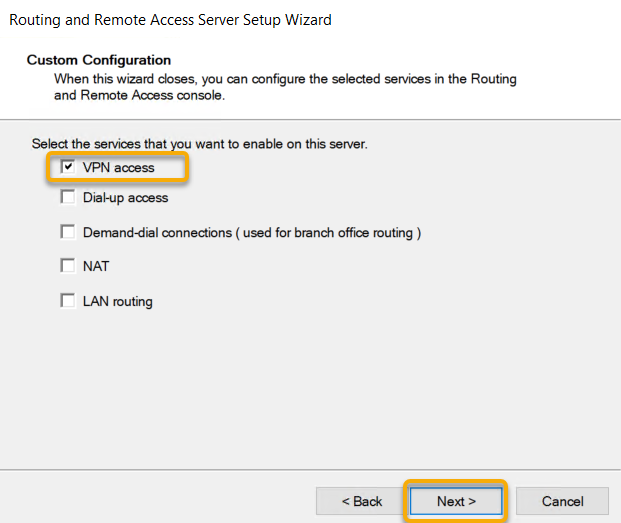
Next, select the VPN access to enable it on the server and click on Next button.

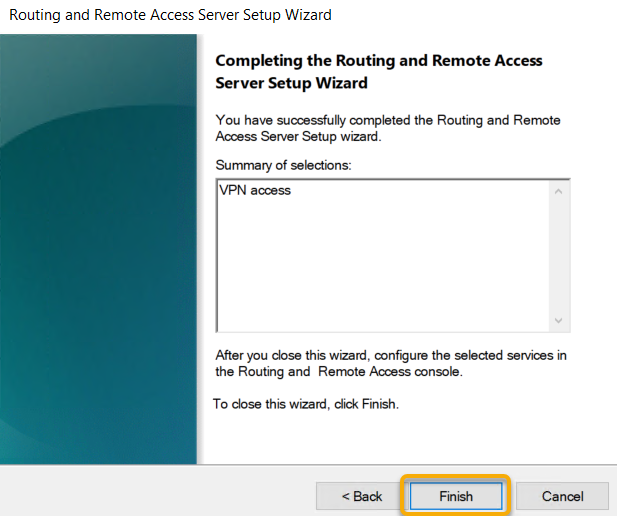
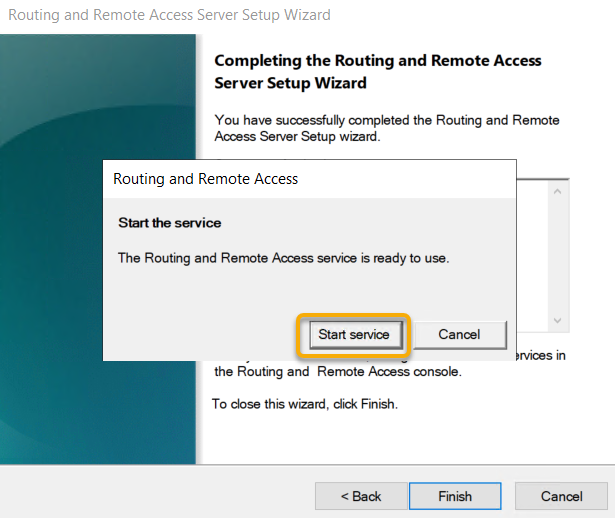
After clicking on the Finish, it will ask you to start the service.
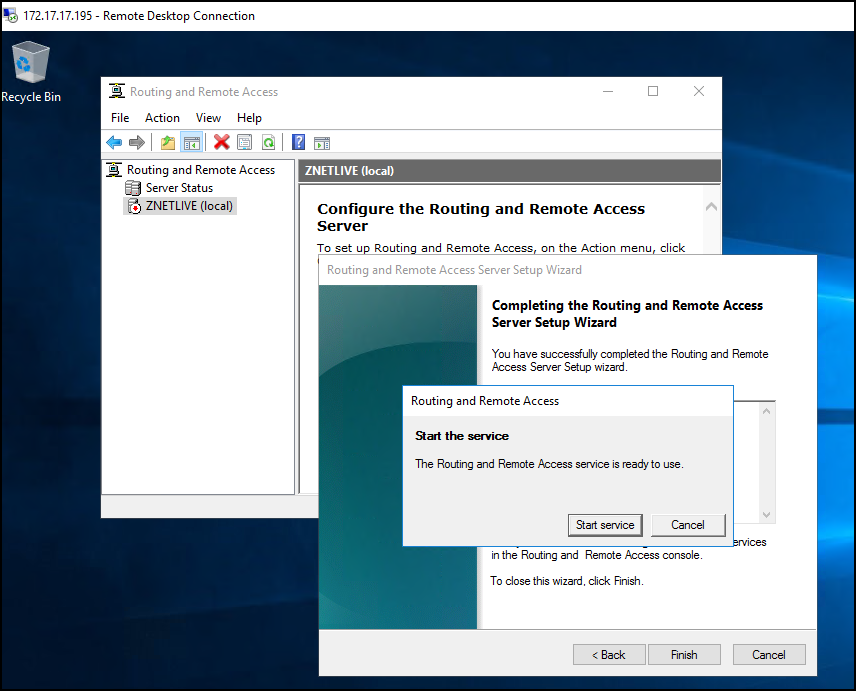
Once the service is started, as shown in the screen below, you will be able to see green colored Hostname in the left pane under Routing and Remote Access.

Now you need to set up the IP address which will be used in the VPN connections. For this, you can choose whatever DHCP and static address you want.
Also Read: What is Digital Information Security in Healthcare Act (DISHA) in India?
Here, we are demonstrating further steps using the static addresses.


Now create a user which will access the VPN service and allow him to have Network Access Permission.

Here Server configuration is completed.
Now go to the Client Machine.
Open Network settings and Click on VPN and Add a VPN connection.


Next, provide relevant details in the fields shown in the screen below.

The VPN connection will now begin to show on the client machine.

When you click on Connect, it will communicate with the VPN server and retrieve VPN access with proper user credentials.
You can also check the Client connection status at Routing and Remote Access Management. Follow the screenshots given below for this.


That’s it! You are done with VPN server setup on the Windows server.
“Acronis is directly responsible for saving our company 1200 hours per year for IT operations staff in backup and recovery workflows.” CIO, high performance IT company.
Read details in a report by Forrester.
[ninja_form id=1]
In case you have any feedback regarding this blog, let me know via the comments section. I’ll be happy to help.
Update: This post has been updated on 29th January 2019.
Services ZNetLive offer:
Domain Name Registration
Best Shared Hosting
WordPress Hosting Plan
VPS Hosting Plans
Buy Dedicated Server
Preface
The Virtual Private Network installation in Windows Server 2019 is like a breeze after the Secure Socket Tunneling Protocol (SSTP) becomes more popular over recent years. The SSTP protocol makes the VPN configuration much easier as the configuration of the firewall needs to open only SSL over Http port 443. The port 443 is used mostly for web servers, and it is common on the networking world organizations to open this port for accessing the https services.
Today I’m going to demonstrate the enablement of this
service by installing and configuring the new and robust server from Microsoft,
which is no other than Windows Server 2019. When we talk about security, we
cannot disregard the concept certificate from certification authority which can
be either an internal CA server or third party one. We need to install a
Certification Authority certificate on the Internet Information Services (IIS),
and the web site installed when we implement Remote Access Services.
There are two parts we need to take into consideration, which setup a Secure VPN (SSTP) on Windows Server 2019 and the VPN client configuration on client operating systems such as Windows 10. On the outset, while we talk about Windows servers and Clients, we can also use this step by step guide to install VPN services on Windows Server 2016 and the Windows 8 and 8.1 client to connect to the Server. There are some minor changes we need to take care of while we do this configuration on earlier operating systems like Windows Server 2016 and Windows 8 and 8.1.
The following steps are involved in Setup a Secure VPN (SSTP) on Windows Server 2019. We see one by one and complete Routing and remote Access implementation for Virtual Private Network Service using Secure Socket Tunneling Protocol (SSTP). We are going to dive deeper into this ‘How to Setup a Secure VPN (SSTP) on Windows Server 2019’, so be with me until we complete the setup.
- Add Remote Access Server Role
- Configure Remote Access with VPN Access
- Limit number of VPN Ports
- Configure Remote Access Settings for VPN
- Configure Dian-in connection on the user object
- Create a VPN network Connection
- Connect to the VPN Server over internet
Add Remote Access Server Role
The first step in Setup a Secure VPN (SSTP) is Adding the Remote Access Server Role on the server. The remote access server role to be installed by going to the Server Manager Dashboard. Once the Server Manager windows would open, click on the Add Roles and Features, and the ‘Add Roles and Features’ wizard would start, and we can go through this wizard to complete the Remote Access role installation.
The wizard will start with instructions on using this tool
to add the roles and features. If you don’t want to see this page, you can
click the checkbox next to ‘Skip this page by default,’ and you won’t be
prompted with this page anymore.
In this wizard, we are going to use the role-based
installation to add this role, so select Role-based or Feature-based
Installation to begin with and click Next to continue.
Make sure the local server in the server pool and select it
and click Next.
In the Select Server Role page, select Remote Access
checkbox, and click Next.
On the next page, leave the Features as it is and click Next.
If you need more details, you may go through the details
about remote access on this page, and once you are ready to move, click Next.
This step is very important, select the Direct Access and
VPN (RAS) alone, and you would be prompted with related features on the pop-up
and click Add Features, which will return to select the role services page.
We have selected the roles services and its feature, and we
are good to move to continue, click Next.
The next page is an information page and it describes that adding
this role service also install the Web Server (IIS) role, Click Next to
continue.
The Web Server(IIS) role will install this role services,
leave the default selection, and click Next.
On the confirmation page, verify that the Roles mentioned above and Role Services are correct and click Install to start the Remote Access role installation. Sit back and relax for a few minutes to get the installation to complete.
You would notice the installation succeeded message and also
there is a link to open the getting started wizard to start the configuration
of the Remote Access Role, click the link.
Configure Remote Access with VPN Access on Setup Secure VPN (SSTP)
Clicking the link will start Configure Remote Access Wizard,
on the wizard click Deploy VPN only tab as in the screen below.
The Routing and Remote Access management console will be
opened and right-click on the server node and click ‘Configure and Enable
Routing and Remote Access.’
The Routing and Remote Access Server Setup Wizard will start
with a Welcome Screen, Click Next to begin the Wizard.
Select the Radio button next to Custom Configuration and
click Next.
On the Custom Configuration page, select the checkbox next
to VPN Access and click Next.
The VPN Access configuration selected on the wizard, and
that is the end of the wizard and click Finish.
As we have configured Routing and Remote Access services
with VPN Access and the wizard will end by prompting to start service.
Once the Routing and Remote Access Service Started, you will
see a green arrow on the server node implying that the service started and running.
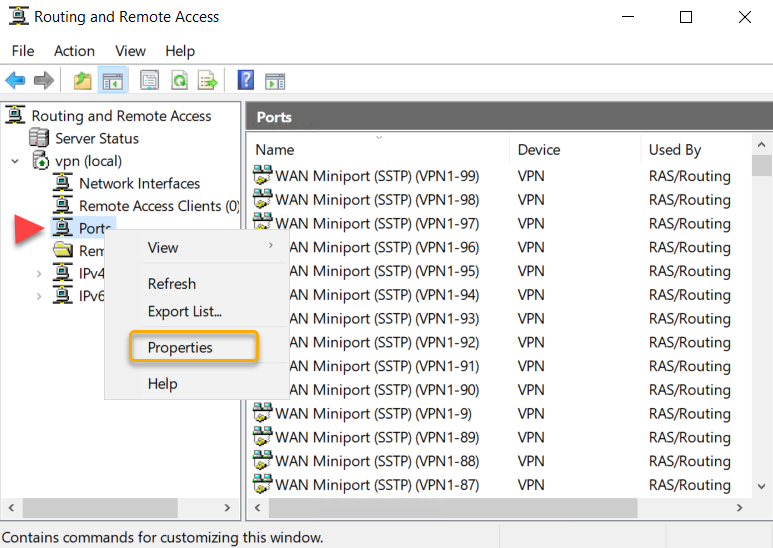
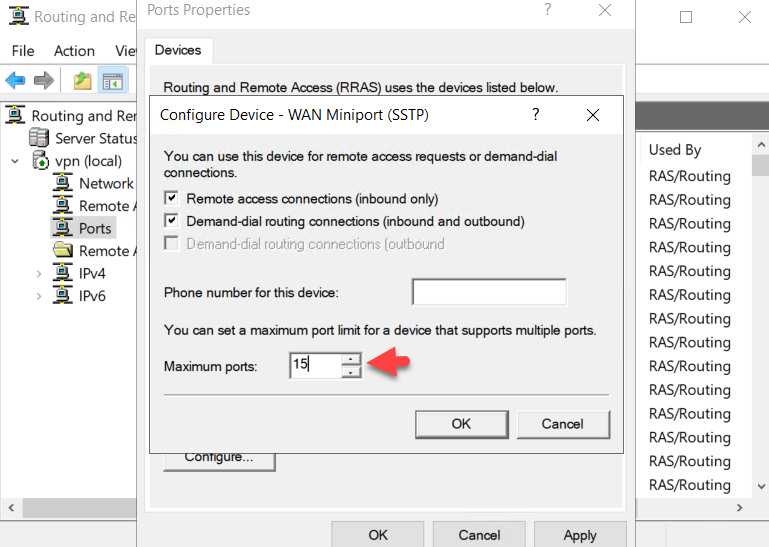
Limit number of VPN Ports
Based on our requirement, we are going to limit the number
of connections on the remote access service. To limit the number of ports, right-click
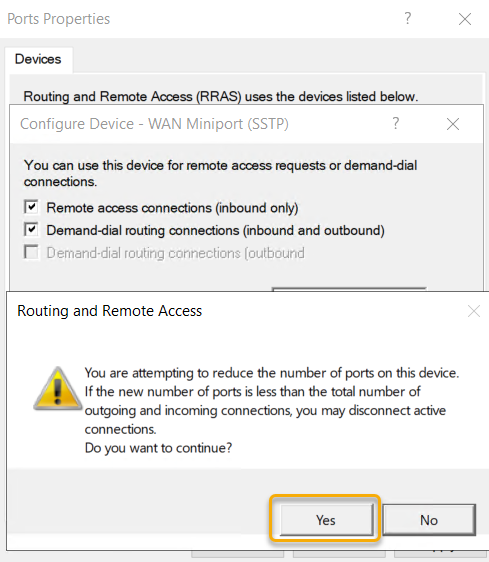
on Ports and select Properties.
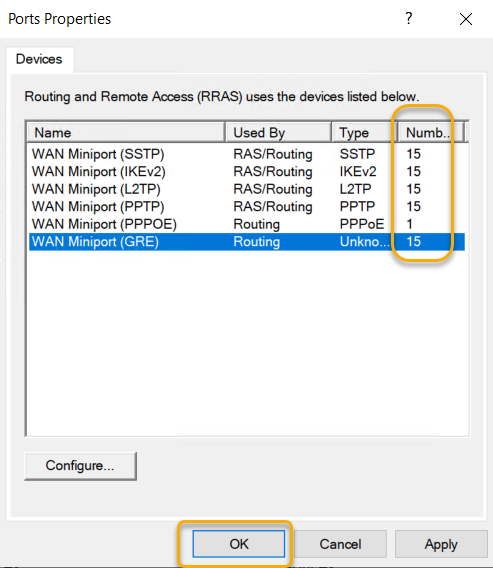
We are going to limit the ports to 15 in this example.
Select Yes to the warning that shows that we are reducing the number of ports.
Once we set all ports to 15 and confirm the numbers and
click OK.
Configure Remote Access Settings for VPN To Secure VPN (SSTP)
There are certain settings we need to update to set the VPN
to function securely and get the IP4 IPs to the client system.
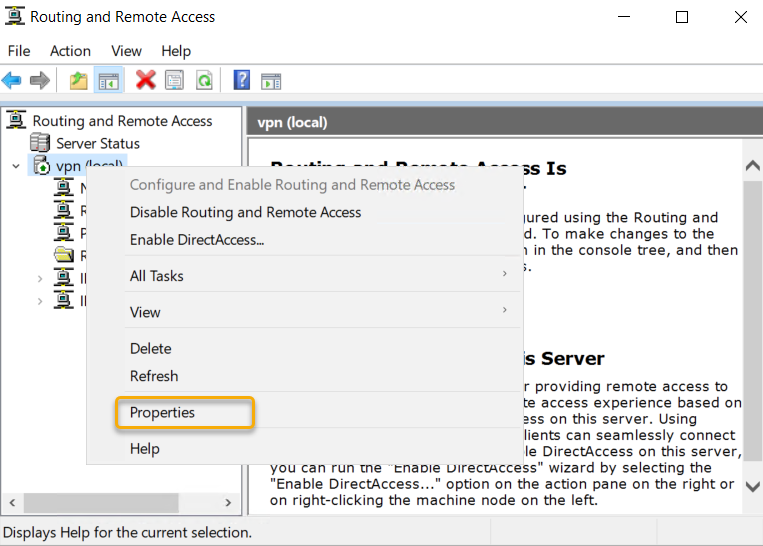
Right-click the server node and click properties as in the
screen below.
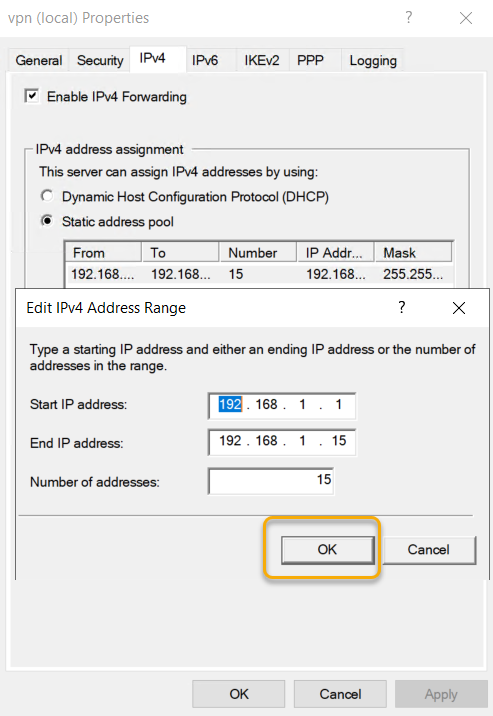
On the Remote Access, Server Properties go to the IPV4 tab
and Select the Static Address pool radio button under IPv4 Assignment and click
add to add IP address pool. Choose an IP address Pool and type start and end IP
address of the pool. The IPV4 address pool is a static one, and if you are
running the DHCP server on the server, you can leave the IP address to assign
from the DHCP server. As we are not running a DHCP service, we are creating a static
address pool in this example.
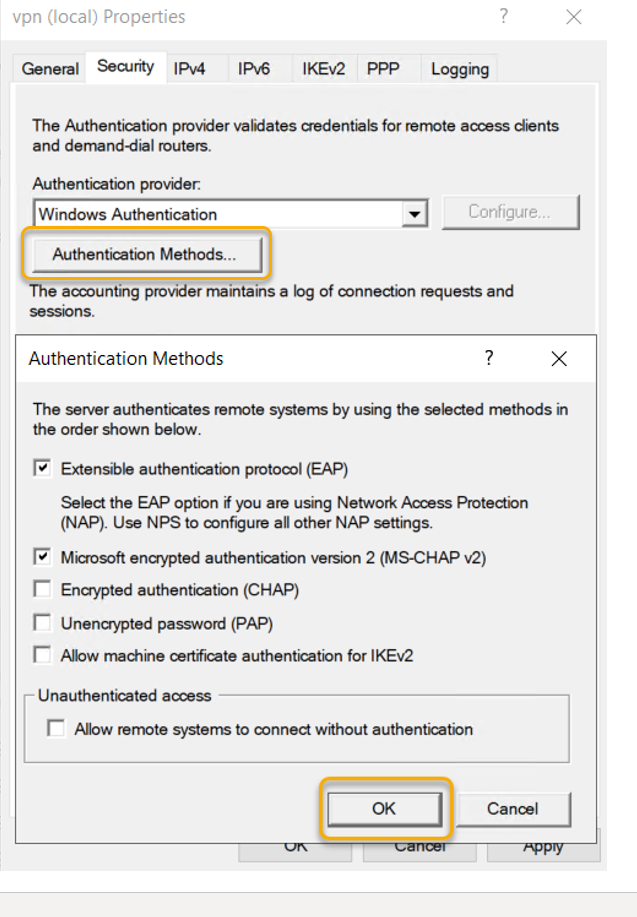
On the Remote Access, Server Properties select
‘Authentication Methods’ check ‘EAP’ and ‘MS-CHAP v2’ selected and click OK.
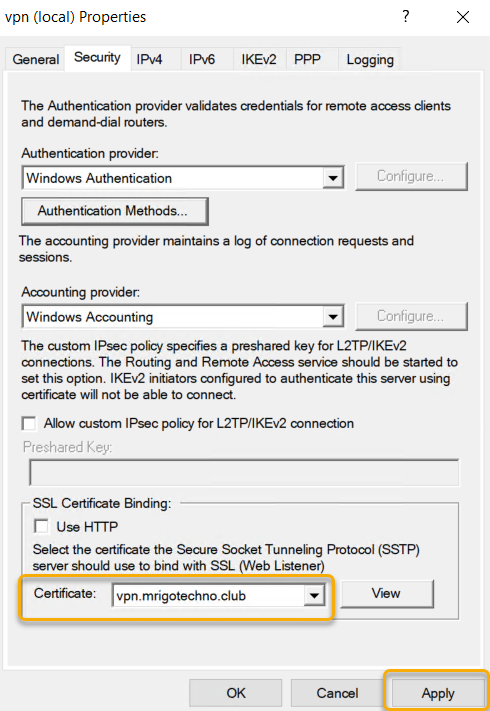
Before starting this installation, I have configured Public
DNS of the domain with a hostname record and assigned the server public IP
address to it. Also, I have generated a certificate from third-party CA. At the
bottom of the page, you can select the certificate that you have installed for
the hostname that you have selected.
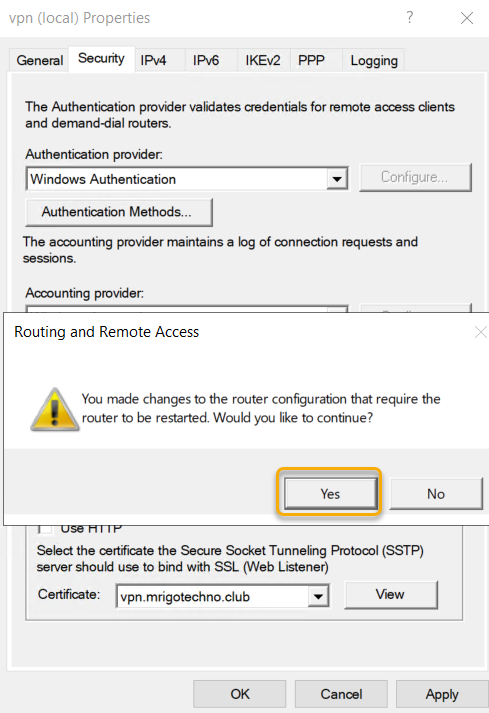
Applying configuration changes will require a restart of the
Remote access service for the configuration to take effect.
We have completed the Routing and Remote Access
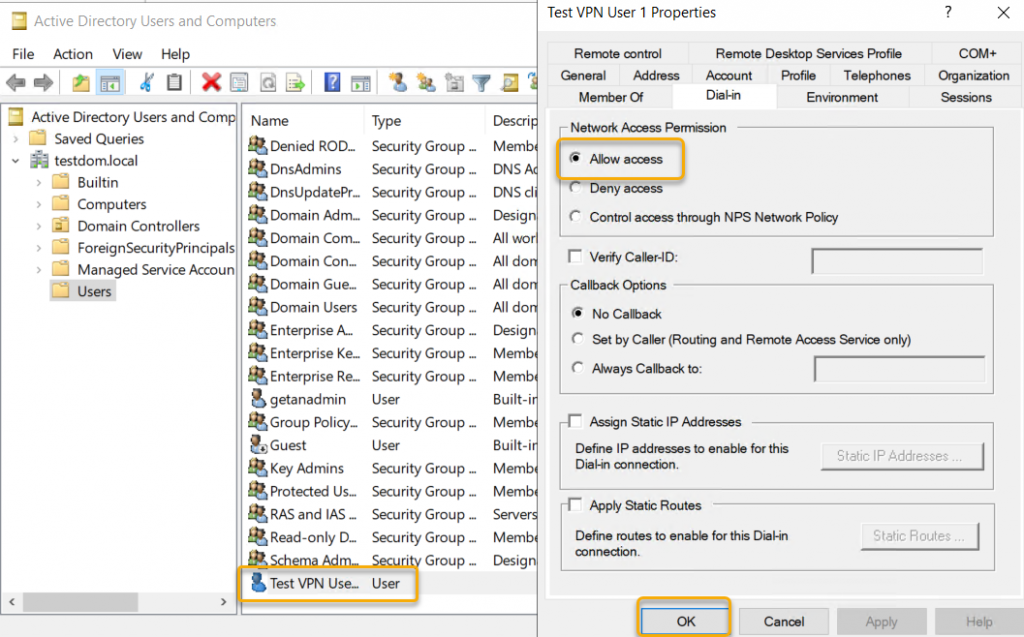
configuration. To connect to the VPN Server from the VPN client, we need to
allow the users who are all needed access. Go to Active Directory Users and
Computers and select the User objects that you want to Allow Dial-in to VPN and
go to Dian-in on the properties of the user object and select the radio button
next to ‘Allow Access.’
Configure Dian-in connection on user object
Create VPN Network Connection to Secure VPN (SSTP)
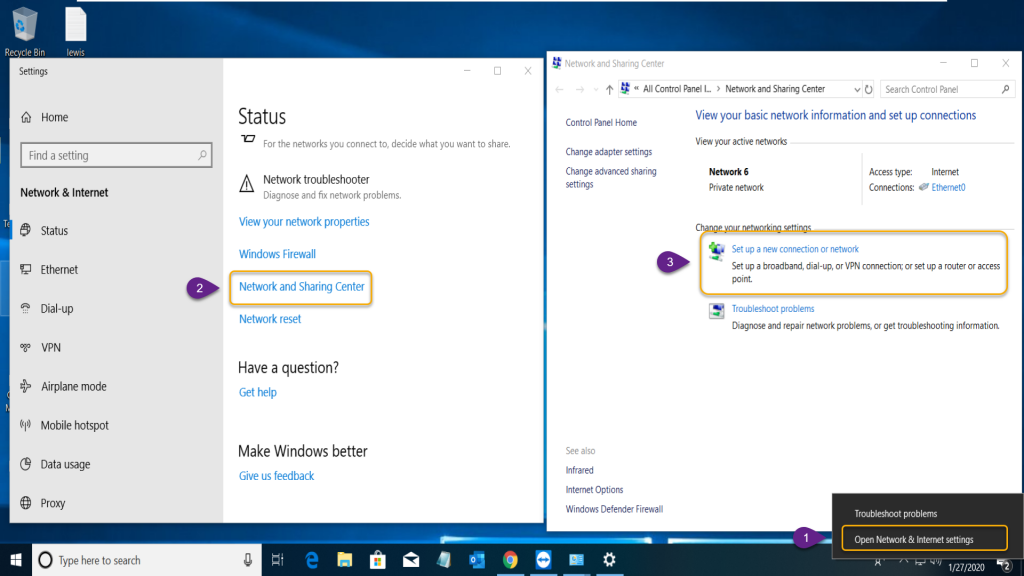
So, we have completed all server configurations, now is the time to create a VPN connection on the Windows 10 client computer on Setup a secure VPN (SSTP).
Right-click network Icon on the taskbar and select ‘Open
Network & Connection Sharing.’ On settings, windows click ‘Network and
Sharing Center’ that will open the ‘Network and Sharing Center’ where we need
to select ‘Set up a New Connection or Network’ as in the steps provided on the
screenshot below.
Select the steps as in the steps below.
- Open Network & Internet Sharing
- Network Sharing Center
- Set up a New Connection or network
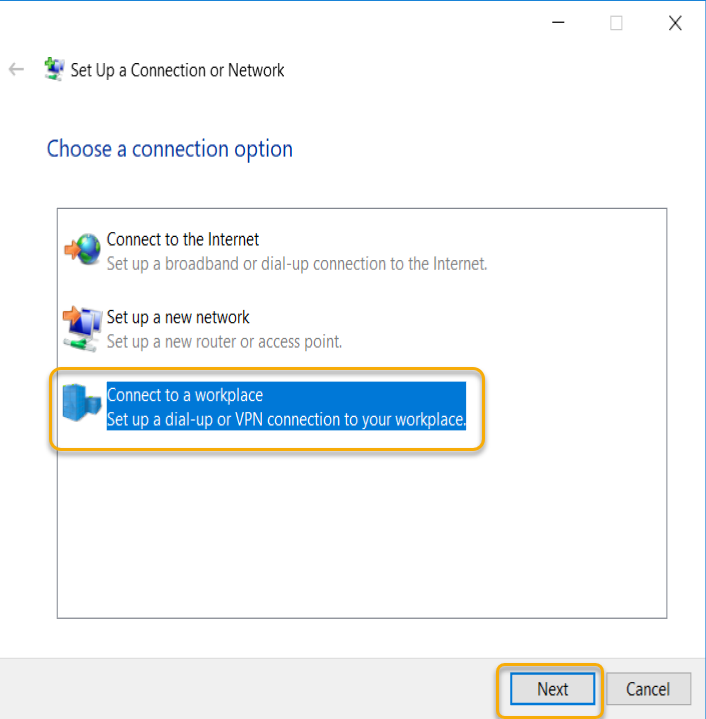
There is a Wizard start, and in the connection options,
select ‘Connect to a workplace’ and click Next.
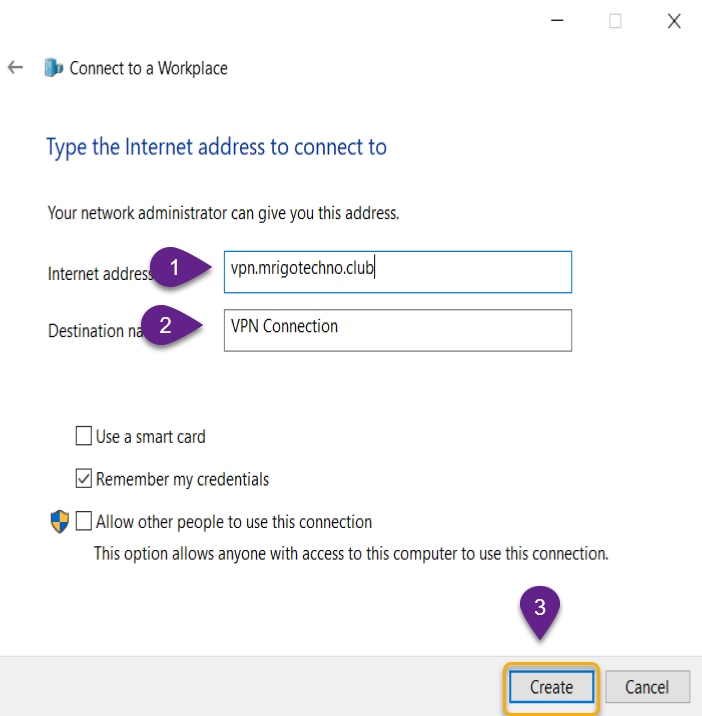
On the How do you want to connect options, select ‘Use my
Internet connection (VPN). Type internet address as I told you earlier I have
created a hostname called ‘vpn.mrigotechno.club’ on my domain for this VPN
configuration.
In the destination name type, a name implies the connection
purpose. I left the default name in this example.
Leave the selection of ‘Remember my credentials’ and click
create.
- Type the VPN server’s internet hostname or IP
address. - Give a name to the VPN Connection.
- Click Create to create a workplace connect.
Connect to the VPN Server over internet
The VPN connection network adapter has been created and now
click change adapter settings to change the VPN network adapter settings to
connect to the VPN server.
Right-click newly created adapter for VPN Connection and
select properties.
On the Security tab, select Secure Socket Tunneling Protocol
(SSTP) and click OK.
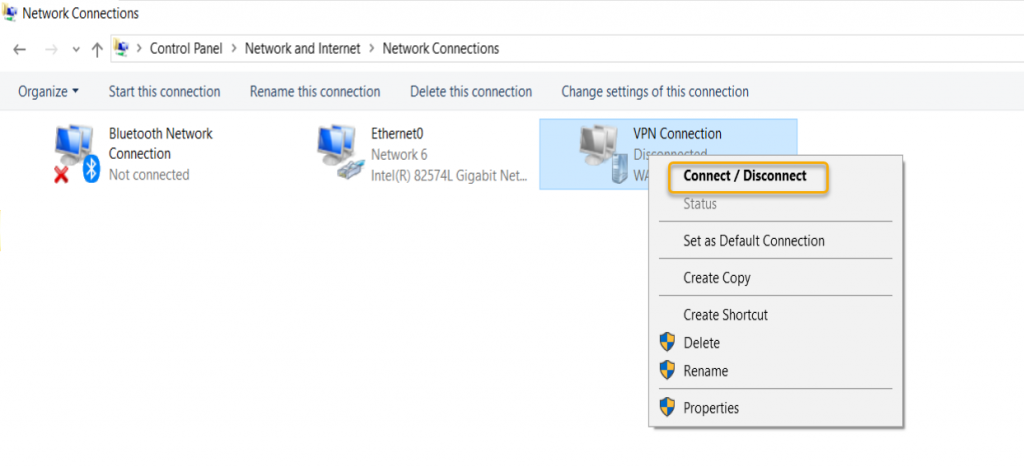
Right-click the adapter one more time and click Connect /
Disconnect
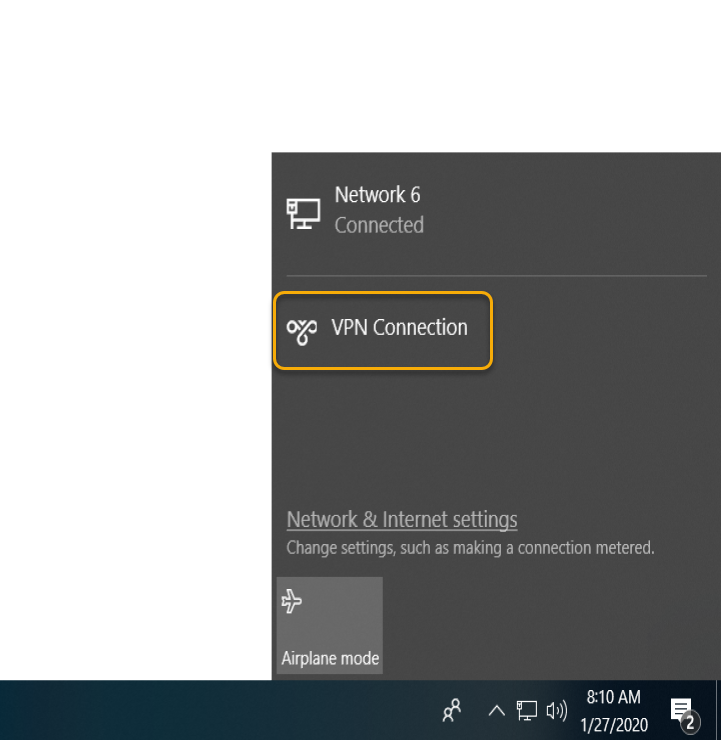
The VPN Connection will popup on the taskbar; now click on
the VPN Connection.
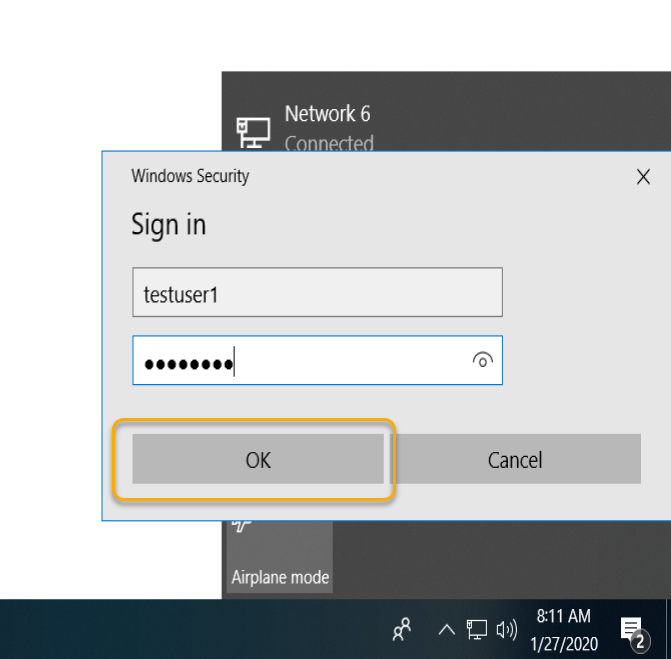
Type the domain credentials and click OK.
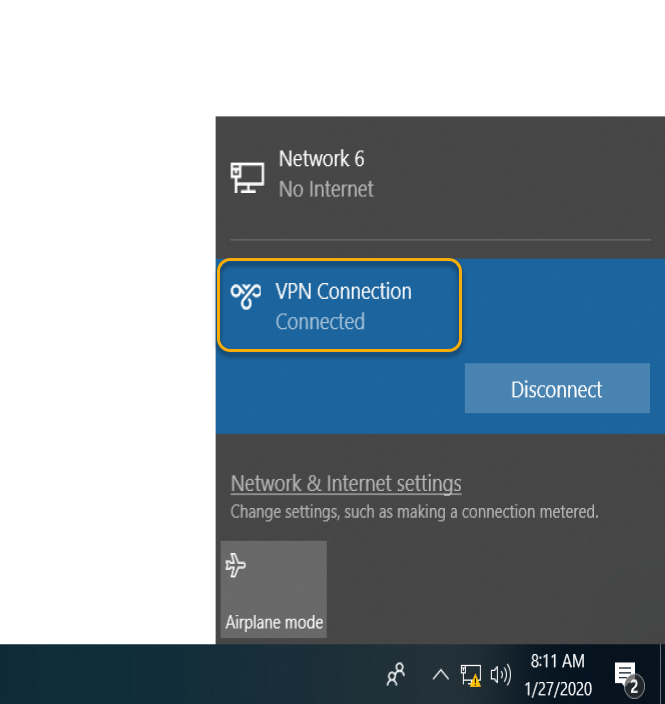
The VPN Connection completed, and you would see the
Connected prompt on the VPN Connection.
The connection made can be verified on the Routing and
Remote Access management console, as in the screen below.
Conclusion
In this article, we have gone through how to set up a secure
VPN (SSTP) on Windows Server 2019. We have covered Installation of Remote
Access Role, after the installation, we have configured Remote Access with VPN
access, and we limit the number of SSTP ports so only maximum allowed
connections possible to connect. We configured Dial-In property of the Active
Directory domain users and we also covered the Windows 10 client computer to
connect the VPN server with the VPN connection adaptor.
I hope this article gives all the details to set up an
environment to implement Virtual Private Network using Secure Socket Tunneling
Protocol (SSTP). You may have some questions or feedback to share with me,
please click the comments below and share your thoughts. I’m so happy to answer
your questions.
If you want to setup VPN on a remote Windows server mainly to change your IP address and security is not the main concern then PPTP VPN is probably the simplest option. In this guide we’ll see how to setup PPTP VPN with NAT on Windows Server 2019 with only a single network interface (as is the case with most VPS deployments).
NAT normally requires two interfaces – one public and one private. Using the method given here you can setup VPN + NAT on a single interface as well. The rest of this tutorial assumes that you are setting this up on a cloud VPS with only 1 NIC.
To setup PPTP VPN go to Server Manager => Add roles and features. In Server Roles tab select “Remote Access” role and click through to the end of the wizard.
After the installation is complete go to Server Manager => Tools and select the Routing and Remote Access role:
Right click on your server and select “Configure and Enable Routing and Remote Access”:
Press Next in the wizard welcome screen. Select Custom configuration option and press Next:
Check “VPN access” and “NAT” options and press Next:
Finish the wizard and start the service:
Right click on your server and select Properties. Go to IPv4 tab and select “Static address pool” option. Add a new IP pool and enter a range of private IPs (we have used 192.168.125.100 – 192.168.125.200):
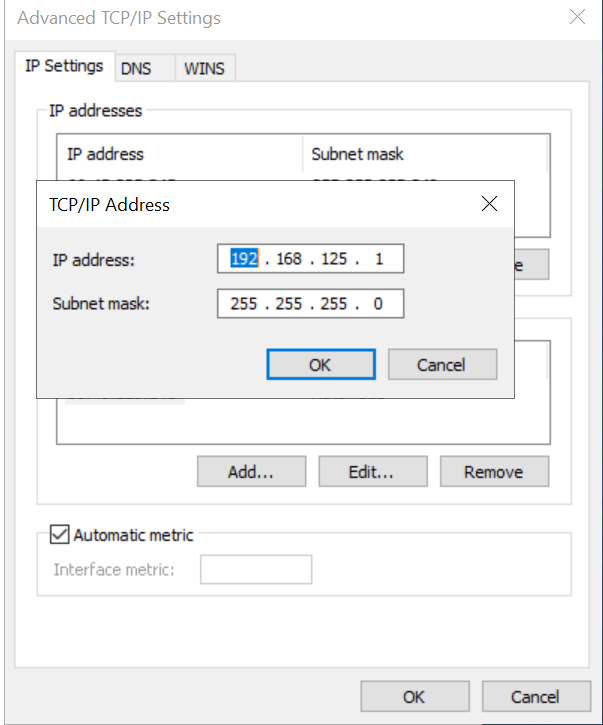
You need to configure an IP of the same range as a secondary IP on your network interface card. Go to Network and Sharing Center and select your network interface. Go to its Properties. Select “Internet Protocol Version 4 (TCP/IPv4)” and go to its properties. In the Advanced portion enter your secondary IP like this (we have used 192.168.125.1):
In Routing and Remote Access expand “IPv4” and right-click on NAT. Select “New Interface…”.
Select the interface with the public IP (and secondary private IP) and configure it as a public interface for NAT:
To create a local user for PPTP go to Computer Management => Local Users and Groups => Users. Right click on Users and add a new user by entering a username and password for it. Next, select that newly created user, right-click and go to Properties. In the Dial-in tab select “Allow access” under Network Access Permission:
Firewall Settings
PPTP VPN uses TCP port 1723 and GRE protocol. They have to be allowed in Firewall Inbound rules for PPTP to work. To manually allow them in the firewall go to Windows Defender Firewall with Advanced Security and select Inbound Rules. Right-click and select “New Rule…”. Create a rule for TCP port 1723:
Click Next through the remaining options and enter a name for this rule at the end. Similarly create a rule to allow GRE traffic. Rule type will be Custom and GRE would be selected in “Procotol and Ports”:
Our PPTP VPN setup is now complete.
References
How to Install VPN on Windows Server 2019