Reaver

- Размер: 917 Кб
- Версия: 1.4
- ОС:
UNIX - Ссылки:
скачать
Reaver предназначен для надёжной и практичной атаки на WPS (Wifi Protected Setup) и подборки пина WPS методом перебора. Конечной целью является получение пароля от WPA/WPA2.
В среднем, Reaver раскрывает пароль к WPA/WPA2 целевой точки доступа за 4-10 часов.
08:58 / 5 Октября, 2018

Размер: 917 Кб
Версия: 1.4
ОС: Windows
UNIX
Ссылки:
скачать
Reaver предназначен для надёжной и практичной атаки на WPS (Wifi Protected Setup) и подборки пина WPS методом перебора. Конечной целью является получение пароля от WPA/WPA2.
В среднем, Reaver раскрывает пароль к WPA/WPA2 целевой точки доступа за 4-10 часов.

Overview
Reaver implements a brute force attack against Wifi Protected Setup (WPS) registrar PINs in order to recover WPA/WPA2 passphrases, as described in Brute forcing Wi-Fi Protected Setup When poor design meets poor implementation. by Stefan Viehböck.
Reaver has been designed to be a robust and practical attack against Wi-Fi Protected Setup (WPS) registrar PINs in order to recover WPA/WPA2 passphrases and has been tested against a wide variety of access points and WPS implementations.
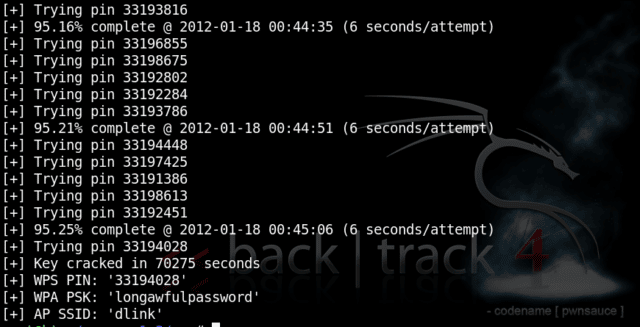
Depending on the target’s Access Point (AP), to recover the plain text WPA/WPA2 passphrase the average amount of time for the transitional online brute force method is between 4-10 hours. In practice, it will generally take half this time to guess the correct WPS pin and recover the passphrase.
When using the offline attack, if the AP is vulnerable, it may take only a matter of seconds to minutes.
The first version of reaver-wps (reaver 1.0) was created by Craig Heffner in 2011.
reaver-wps-fork-t6x version 1.6.x is a community forked version which includes various bug fixes, new features and additional attack method (such as the offline Pixie Dust attack).
- The original Reaver (version 1.0 to 1.4) can be found in google code archives.
- The discontinued reaver-wps-fork-t6x community edition, reaver version 1.5.3, which includes the Pixie Dust attack, is now the old-master branch from this repository.
- The latest revison of reaver-wps-fork-t6x community edition is the master branch from this repository.
Reaver versioning was updated to 1.6.x in order to identify the new cycle.
All stable relases since the first beta version of reaver 1.6 can be downloaded from our Releases page. - More information about the Pixie Dust attack (including which APs are vulnerable) can be found in pixiewps repository,
pixie dust thread (in Kali forum) & Dominique Bongard’s full disclosure
Requirements
Build-time dependencies
- libpcap-dev
- build-essential
Runtime-time dependencies
- pixiewps (optional, required for pixiedust attack)
- aircrack-ng (optional, though recommended)
Example
sudo apt -y install build-essential libpcap-dev aircrack-ng pixiewps
The example uses Kali Linux as the Operating System (OS) as pixiewps is included.
You must already have Wiire’s Pixiewps installed to perform a pixie dust attack, latest version can be found in its official github repository.
Setup
Download
git clone https://github.com/t6x/reaver-wps-fork-t6x
or
wget https://github.com/t6x/reaver-wps-fork-t6x/archive/master.zip && unzip master.zip
Locate the shell
cd reaver-wps-fork-t6x*
cd src
Compile
./configure
make
Install
sudo make install
Reaver Usage
Copyright (c) 2011, Tactical Network Solutions, Craig Heffner <cheffner@tacnetsol.com>
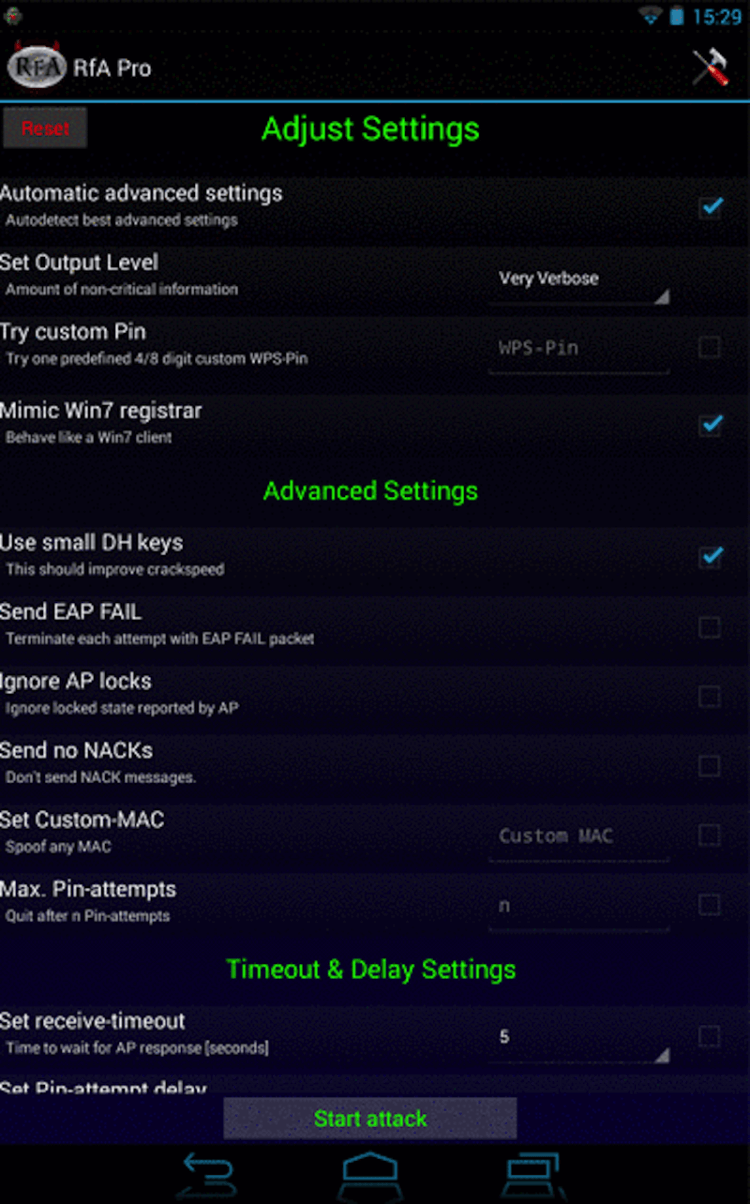
Required Arguments:
-i, --interface=<wlan> Name of the monitor-mode interface to use
-b, --bssid=<mac> BSSID of the target AP
Optional Arguments:
-m, --mac=<mac> MAC of the host system
-e, --essid=<ssid> ESSID of the target AP
-c, --channel=<channel> Set the 802.11 channel for the interface (implies -f)
-s, --session=<file> Restore a previous session file
-C, --exec=<command> Execute the supplied command upon successful pin recovery
-f, --fixed Disable channel hopping
-5, --5ghz Use 5GHz 802.11 channels
-v, --verbose Display non-critical warnings (-vv or -vvv for more)
-q, --quiet Only display critical messages
-h, --help Show help
Advanced Options:
-p, --pin=<wps pin> Use the specified pin (may be arbitrary string or 4/8 digit WPS pin)
-d, --delay=<seconds> Set the delay between pin attempts [1]
-l, --lock-delay=<seconds> Set the time to wait if the AP locks WPS pin attempts [60]
-g, --max-attempts=<num> Quit after num pin attempts
-x, --fail-wait=<seconds> Set the time to sleep after 10 unexpected failures [0]
-r, --recurring-delay=<x:y> Sleep for y seconds every x pin attempts
-t, --timeout=<seconds> Set the receive timeout period [10]
-T, --m57-timeout=<seconds> Set the M5/M7 timeout period [0.40]
-A, --no-associate Do not associate with the AP (association must be done by another application)
-N, --no-nacks Do not send NACK messages when out of order packets are received
-S, --dh-small Use small DH keys to improve crack speed
-L, --ignore-locks Ignore locked state reported by the target AP
-E, --eap-terminate Terminate each WPS session with an EAP FAIL packet
-J, --timeout-is-nack Treat timeout as NACK (DIR-300/320)
-F, --ignore-fcs Ignore frame checksum errors
-w, --win7 Mimic a Windows 7 registrar [False]
-K, --pixie-dust Run pixiedust attack
-Z Run pixiedust attack
Example:
reaver -i wlan0mon -b 00:90:4C:C1:AC:21 -vv
Options description and examples of use can be found in the Readme from Craig Heffner. Here comes a description of the new options introduced since then:
-K or -Z // —pixie-dust
The -K and -Z option perform the offline attack, Pixie Dust (pixiewps), by automatically passing the PKE, PKR, E-Hash1, E-Hash2, E-Nonce and Authkey variables. pixiewps will then try to attack Ralink, Broadcom and Realtek detected chipset.
Special note: If you are attacking a Realtek AP, do NOT use small DH Keys (-S) option.
User will have to execute reaver with the cracked PIN (option -p) to get the WPA pass-phrase.
This is a temporary solution and an option to do a full attack will be implemented soon
-p with arbitrary string // —pin=
See our wiki: Introducing a new way to crack WPS: Option p with an Arbitrary String
Wash Usage
Copyright (c) 2011, Tactical Network Solutions, Craig Heffner
Required Arguments:
-i, --interface=<iface> Interface to capture packets on
-f, --file [FILE1 FILE2 FILE3 ...] Read packets from capture files
Optional Arguments:
-c, --channel=<num> Channel to listen on [auto]
-n, --probes=<num> Maximum number of probes to send to each AP in scan mode [15]
-F, --ignore-fcs Ignore frame checksum errors
-2, --2ghz Use 2.4GHz 802.11 channels
-5, --5ghz Use 5GHz 802.11 channels
-s, --scan Use scan mode
-u, --survey Use survey mode [default]
-a, --all Show all APs, even those without WPS
-j, --json print extended WPS info as json
-p, --progress Show percentage of crack progress
-h, --help Show help
Example:
wash -i wlan0mon
A detailed description of the options with concrete syntax examples can be found in Craig Heffner’s wash readme.
About the new options and features:
-a // —all
The option -a of Wash will list all access points, including those without WPS enabled.
-j // —json
The extended WPS information (serial, model…) from the AP probe answer will be printed in the terminal (in json format)
«Vendor» column
Wash now displays the manufacturer of the wifi chipset from the Acces Points in order to know if they are vulnerable to pixie dust attack.
Stdout can be piped
Notice that wash output can be piped into other commands. For more information see the wiki article Everything about the new options from wash
Acknowledgements
Contribution
Creator of reaver-wps-fork-t6x «community edition»:
t6x
Main developer since version 1.6b:
rofl0r
Modifications made by:
t6_x, DataHead, Soxrok2212, Wiire, AAnarchYY, kib0rg, KokoSoft, rofl0r, horrorho, binarymaster, Ǹotaz
Some ideas made by:
nuroo, kcdtv
Bug fixes made by:
alxchk, USUARIONUEVO, ldm314, vk496, falsovsky, rofl0r, xhebox
Special Thanks
Soxrok2212for all work done to help in the development of toolsWiirefor developing PixiewpsCraig Heffnerfor creating Reaver and for the creation of default pin generators (D-Link, Belkin) — http://www.devttys0.com/Dominique Bongardfor discovering the Pixie Dust attack.
Reaver — это инструмент разработанный для надежного и практического взлома WPS Pin WiFi сетей с помощью Wi-Fi Protected Setup (WPS) регистраторов с помощью восстановления WPA/WPA2 паролей.
Он был протестирован на широком спектре точек доступа с WPS.
Реализация происходит с помощью брутфорса, как описано здесь[документ PDF.] Reaver-WPS-fork-t6x version 1.6 b – это раздвоенная версия сообщества, которая включает в себя различные исправления ошибок и дополнительный метод атаки (автономная атака Pixie Dust).
В зависимости от точки доступа (AP), чтобы восстановить простую текстовую парольную фразу WPA/WPA2, среднее время для проведения метода Brute Force составляет между 4-10 часами. На практике, как правило, потребуется половина этого времени, чтобы угадать правильный pin-код WPS и восстановить парольную фразу. При использовании автономной атаки, если точка доступа уязвима взлом может занять от нескольких секунд до нескольких минут.
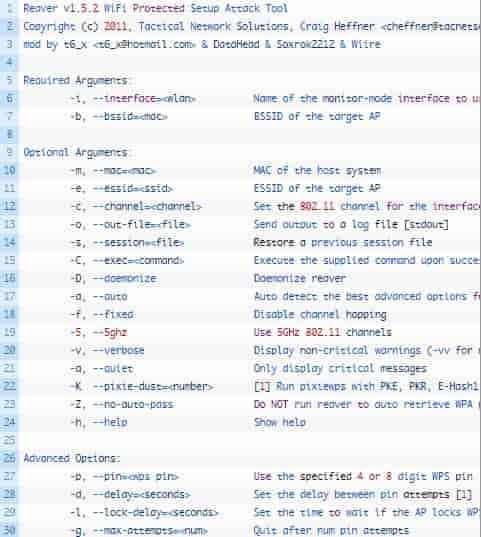
Reaver v1.5.2 WiFi Protected Setup Attack Tool
Copyright (c) 2011, Tactical Network Solutions, Craig Heffner <cheffner@tacnetsol.com>
mod by t6_x <t6_x@hotmail.com> & DataHead & Soxrok2212 & Wiire
Required Arguments:
-i, --interface=<wlan> Name of the monitor-mode interface to use
-b, --bssid=<mac> BSSID of the target AP
Optional Arguments:
-m, --mac=<mac> MAC of the host system
-e, --essid=<ssid> ESSID of the target AP
-c, --channel=<channel> Set the 802.11 channel for the interface (implies -f)
-o, --out-file=<file> Send output to a log file [stdout]
-s, --session=<file> Restore a previous session file
-C, --exec=<command> Execute the supplied command upon successful pin recovery
-D, --daemonize Daemonize reaver
-a, --auto Auto detect the best advanced options for the target AP
-f, --fixed Disable channel hopping
-5, --5ghz Use 5GHz 802.11 channels
-v, --verbose Display non-critical warnings (-vv for more)
-q, --quiet Only display critical messages
-K --pixie-dust=<number> [1] Run pixiewps with PKE, PKR, E-Hash1, E-Hash2, E-Nonce and Authkey (Ralink, Broadcom, Realtek)
-Z, --no-auto-pass Do NOT run reaver to auto retrieve WPA password if pixiewps attack is successful
-h, --help Show help
Advanced Options:
-p, --pin=<wps pin> Use the specified 4 or 8 digit WPS pin
-d, --delay=<seconds> Set the delay between pin attempts [1]
-l, --lock-delay=<seconds> Set the time to wait if the AP locks WPS pin attempts [60]
-g, --max-attempts=<num> Quit after num pin attempts
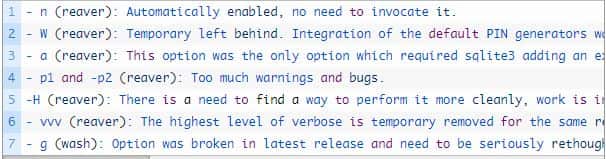
Устаревшие и временно приостановленные методы
- n (reaver): Automatically enabled, no need to invocate it. - W (reaver): Temporary left behind. Integration of the default PIN generators was unstable, leading to many warnings at compilation time. It was also an issue to use a PIN attempt (risk of AP rating limit) in order to get a BSSID and an ESSID. For the moment PIN generation has to be done externally using the scripts provided in "doc". - a (reaver): This option was the only option which required sqlite3 adding an extra dependency. It was only designed for automation scripts and this task (execute the last reaver command again) can be easily done internally by the script that calls reaver - p1 and -p2 (reaver): Too much warnings and bugs. -H (reaver): There is a need to find a way to perform it more cleanly, work is in progress. - vvv (reaver): The highest level of verbose is temporary removed for the same reason. - g (wash): Option was broken in latest release and need to be seriously rethought.
Эта вилка поддерживает атаку Pixie Dust, которая будет работать против современных маршрутизаторов, вы можете найти список маршрутизаторов и для каких типов атак они уязвимы здесь.
Скачать Reaver.
Reaver is considered the world’s most significant application that is used to connect the community of wireless connections and to help people crack WPS pins. Reaver Download is used to connect two or more networks efficiently. With such a device in hand, you can examine the performance of your device quickly. Reaver Pro can work on the following:
- Mac
- Windows
- Android
With the help of its colourful signals, you can take a look at the signals anytime you want. With the help of this tool, you can discover study alerts of networks. If by chance you see purple colour being displayed by Reaver, then it indicates that the signals are weak. If you see green signals, then it means that the signals are active. It has a dominant adopter browser that will log in with 10.9.8.1 signals.
SEE ALSO: 10 Best WiFi Hacking Tools for Kali Linux (Download).
Contents
- 1 What is Reaver?
- 2 Reaver Features
- 3 How to use Reaver and Hack WiFi WPS Pin
- 4 Reaver Alternatives
- 5 How to Install Reaver
- 6 Download Reaver – Free WiFi WPS Pin Hacking Tool
What is Reaver?
The Reaver is used to percentage WPA keys with the users. This shall help the user to reveal wireless APA or routers very quickly. It is used to handle networks at domestic and agency PC. The Reaver application is the only Wi-Fi tracking and hacking software that is used to hack the signal community and then display you the working password to access the unfastened internet
Today the users and customers of Reaver are growing daily due to the excellent performance. Once you have downloaded the Reaver app, then you do not require any high priced network tracking software. It has a friendly user interface that shows you the active signals community. You can join the robust alerts quickly.
SEE ALSO: How to Hack WiFi Passwords with PMKID Vulnerability.
Reaver Features
- The software comes with a natural understanding
- Everyone possessing a computer is allowed
- It has the experience to access the Wi-Fi networks
- This application can retrieve Wi-Fi networks and the usage of WPS (Wi-Fi protected Setup)
- The best thing about reaver latest version is that it works with the working device and browser of your choice and desire
- It uses the colour technique of shade coding to show the weakness and electricity of the goal community
- The colour inexperienced is saved for insecurity and crimson for weakness
- It can crack WEP, WPA, or the modern WPS styles of safety quickly
- The software app is used to ensure the security of your community
- It can detect rapidly and show if the target network can be attacked for eavesdropping
- The Reaver is such a reliable network that even governments, military and intelligence organizations use it all around the world to ensure the safety of their system
- The set of rules that are used inside the software application are prodigious
- the software application is used to crack most of the encrypted packets
- It can be used with almost every running system and browser or even the tabs and telephones
- It can update itself regularly to compromise the essential adjustments. This makes it even more steady and fast.
SEE ALSO: How to Find Saved WiFi Passwords in Windows.
How to use Reaver and Hack WiFi WPS Pin
The reaver pro is a practical and robust tool that has been designed to hack WPS pin in Wi-Fi networks by using WPS (Wi-Fi Protected Setup) register PINs to recover the WPA or WPA2 passphrases. The software application has been tested against a vast variety of WPS and access point implementations.
The original reaver pro is an online brute force attack. It is a rever-wps-fork-t6x version that is a community forked version that has included many bug fixes and additional attack methods (the offline pixie dust attack).
It depends on the targets AP that is the access point to recover plain text WPA or WPA2 passphrase. The average amount of time is 4 to 10 hours for the transitional online brute force method. Practically it takes half of the mentioned time to guess the right WPS pin and recover the passphrase. When you are using the offline attack, and the access point is vulnerable, then it may take only seconds to minutes.
The pixie dust attack is supported by this that shall work against the modern routers. You can also find the types of attacks and list of routers they are vulnerable to over the internet.
SEE ALSO: Shark for Root APK – Android WiFi Hacking App.
Reaver Alternatives
- How to Hack WPA3 WiFi Passwords
- Wireshark
- Top 7 Best Ways to Secure your Wireless Access Points
How to Install Reaver
Many people today would love to have the ability to crack any community surrounding them. Have you tried doing something like this? If yes then you have labored some open-source gear to try this. It is indeed an excellent time to start exploring the river pro software application if you are tired with typing so many complicated Linux instructions and also by following a dense manner. Download it now to fulfill your Wi-Fi cracking desires. This shall, however, provide you with a feeling of control and strength.
SEE ALSO: How to Secure your WiFi Router and Increase Wireless Security.
Today we shared Reaver Free Download application that can be used to connect the community of wireless connection. We have discussed the various features it comes with for you to understand. Reaver WiFi hack is also available for Android.
Reaver Download – WPS Hacking Tool
Views: 250,764
Reaver download below, this tool has been designed to be a robust and practical tool to hack WPS Pin WiFi Networks using WiFi Protected Setup (WPS) registrar PINs in order to recover WPA/WPA2 passphrases.
It has been tested against a wide variety of access points and WPS implementations.
The original Reaver implements an online brute force attack against, as described in here [PDF]. reaver-wps-fork-t6x version 1.6b is a community forked version, which has included various bug fixes and additional attack method (the offline Pixie Dust attack).
How to use Reaver
Depending on the target’s Access Point (AP), to recover the plain text WPA/WPA2 passphrase the average amount of time for the transitional online brute force method is between 4-10 hours. In practice, it will generally take half this time to guess the correct WPS pin and recover the passphrase. When using the offline attack, if the AP is vulnerable, it may take only a matter of seconds to minutes.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 |
Reaver v1.5.2 WiFi Protected Setup Attack Tool Copyright (c) 2011, Tactical Network Solutions, Craig Heffner <cheffner@tacnetsol.com> mod by t6_x <t6_x@hotmail.com> & DataHead & Soxrok2212 & Wiire Required Arguments: —i, —interface=<wlan> Name of the monitor—mode interface to use —b, —bssid=<mac> BSSID of the target AP Optional Arguments: —m, —mac=<mac> MAC of the host system —e, —essid=<ssid> ESSID of the target AP —c, —channel=<channel> Set the 802.11 channel for the interface (implies —f) —o, —out—file=<file> Send output to a log file [stdout] —s, —session=<file> Restore a previous session file —C, —exec=<command> Execute the supplied command upon successful pin recovery —D, —daemonize Daemonize reaver —a, —auto Auto detect the best advanced options for the target AP —f, —fixed Disable channel hopping —5, —5ghz Use 5GHz 802.11 channels —v, —verbose Display non—critical warnings (-vv for more) —q, —quiet Only display critical messages —K —pixie—dust=<number> [1] Run pixiewps with PKE, PKR, E—Hash1, E—Hash2, E—Nonce and Authkey (Ralink, Broadcom, Realtek) —Z, —no—auto—pass Do NOT run reaver to auto retrieve WPA password if pixiewps attack is successful —h, —help Show help Advanced Options: —p, —pin=<wps pin> Use the specified 4 or 8 digit WPS pin —d, —delay=<seconds> Set the delay between pin attempts [1] —l, —lock—delay=<seconds> Set the time to wait if the AP locks WPS pin attempts [60] —g, —max—attempts=<num> Quit after num pin attempts |
Deprecated and temporary left behind options
|
— n (reaver): Automatically enabled, no need to invocate it. — W (reaver): Temporary left behind. Integration of the default PIN generators was unstable, leading to many warnings at compilation time. It was also an issue to use a PIN attempt (risk of AP rating limit) in order to get a BSSID and an ESSID. For the moment PIN generation has to be done externally using the scripts provided in «doc». — a (reaver): This option was the only option which required sqlite3 adding an extra dependency. It was only designed for automation scripts and this task (execute the last reaver command again) can be easily done internally by the script that calls reaver — p1 and —p2 (reaver): Too much warnings and bugs. —H (reaver): There is a need to find a way to perform it more cleanly, work is in progress. — vvv (reaver): The highest level of verbose is temporary removed for the same reason. — g (wash): Option was broken in latest release and need to be seriously rethought. |
This fork supports the Pixie Dust attack which will work against modern routers, you can find a list of routers and which types of attack they are vulnerable to here.
There are other tools which rely on Reaver for WiFi hacking such as:
– wifite – Mass Wifi WEP / WPA Key Cracking Tool
– Fern Wifi Cracker – Wireless Security Auditing Tool
And don’t forget to check out:
– Hijacker – Reaver For Android Wifi Hacker App
You can find the Reaver download here:
reaver-1.6.1.tar.xz
Or read more here.
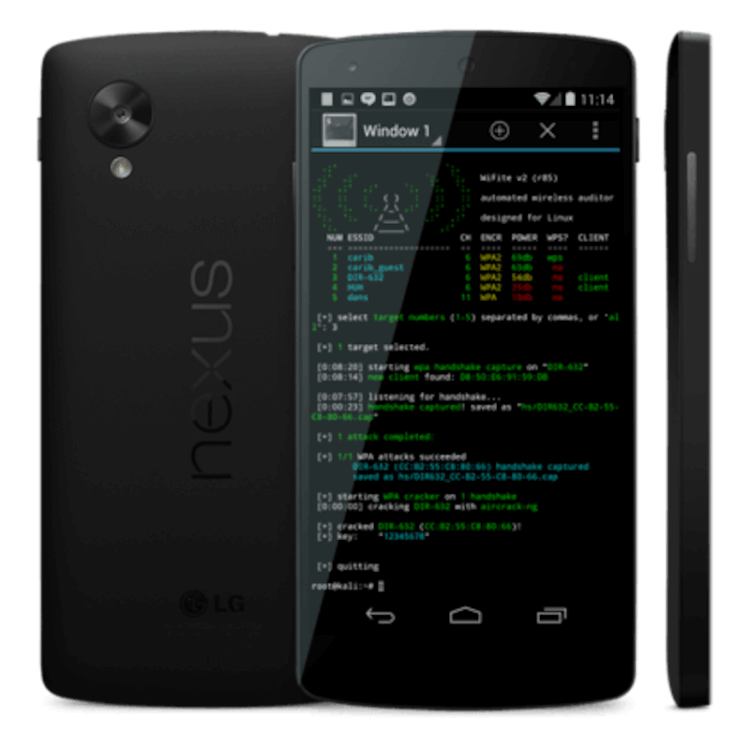
В одном из наших предыдущих материалов мы уже рассказывали вам о лучших хакерских приложениях. Чтобы не пропускать такие материалы — подпишитесь на наш канал в Телеграм, если эта тема вам интересна. Сегодня же мы хотели бы продолжить разговор, посвятив его доступу к Wi-Fi сетям. Но сразу оговоримся. Мы никого не призываем вламываться в личное пространство других людей. Вся информация предоставлена для того, чтобы вы знали больше о безопасности и не дали себя подловить. В крайнем случае, ее можно использовать для доступа к своей сети, если вы вдруг забыли от нее пароль.
Android-смартфон способен на многое. В том числе и на то, чтобы взломать беспроводную сеть
Содержание
- 1 Kali Linux Nethunter — Почувствуйте себя хакером
- 2 aircrack-ng — Взломщик для профессионалов
- 3 Shark For Root — Поиск уязвимостей в беспроводных сетях
- 4 Zanti — Контроль доступа и не только
- 5 Reaver — Как узнать пароль от сети Wi-Fi
- 6 WPA WPS Tester — Не только взлом, но и защита
Kali Linux Nethunter — Почувствуйте себя хакером
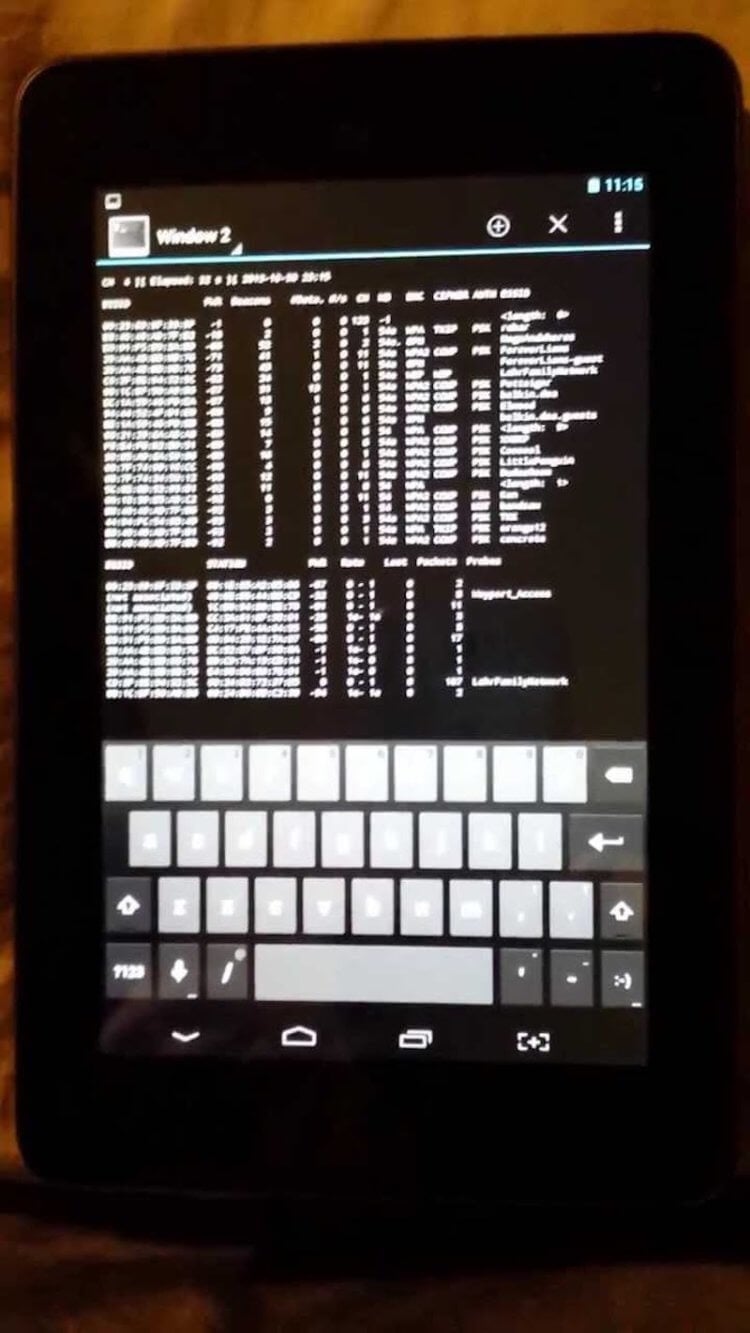
Kali Linux Nethunter является первой в своем роде платформой для работы с Wi-Fi под Android с открытым исходным кодом. Используя это приложение, интерфейс которого, к сожалению, сложно назвать простым и понятным, можно получить полный доступ к беспроводным сетям и даже узнать некоторую информацию об устройствах, которые подключены к Wi-Fi.
Скачать: Kali Linux Nethunter
aircrack-ng — Взломщик для профессионалов
Популярный инструмент для работы с сетями aircrack-ng является одним из тех, элементы которого очень часто заимствовали другие разработчики подобного софта. При этом основное предназначение программы — совсем не взлом, а защита беспроводных каналов связи. Но без специальных знаний за программу лучше не браться. Она разработана явно не для новичков. Работа aircrack-ng нацелена на поиск уязвимостей и «слабых мест» в беспроводных сетях, что позволит вам улучшить безопасность и предотвратить хакерские атаки в дальнейшем.
Скачать: aircrack-ng
Shark For Root — Поиск уязвимостей в беспроводных сетях
Shark For Root — это Android-версия популярного пакета Wireshark с открытым исходным кодом, который обычно используется для анализа сетевого трафика и разработки протоколов безопасности. Обратите внимание, что вам понадобится Wireshark на вашем настольном компьютере, чтобы начать работу, так как приложение на смартфоне работает в паре со «старшим братом», дополняя его функциональность.
Скачать: Shark For Root
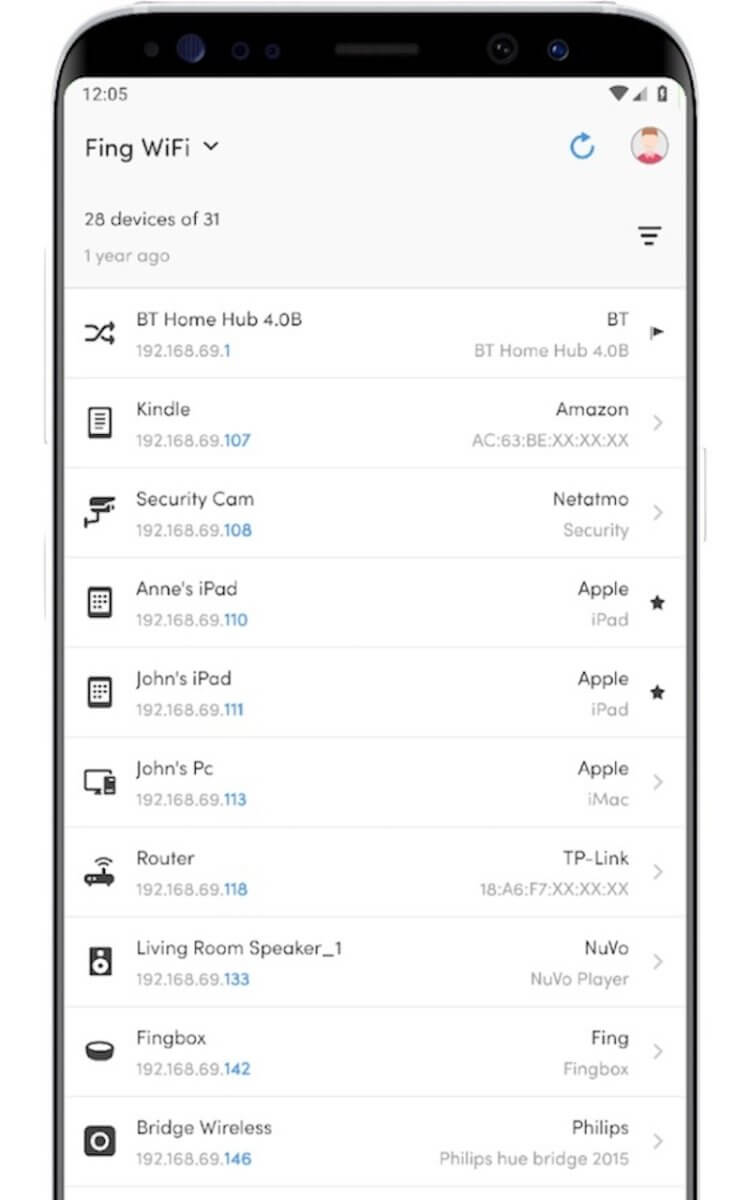
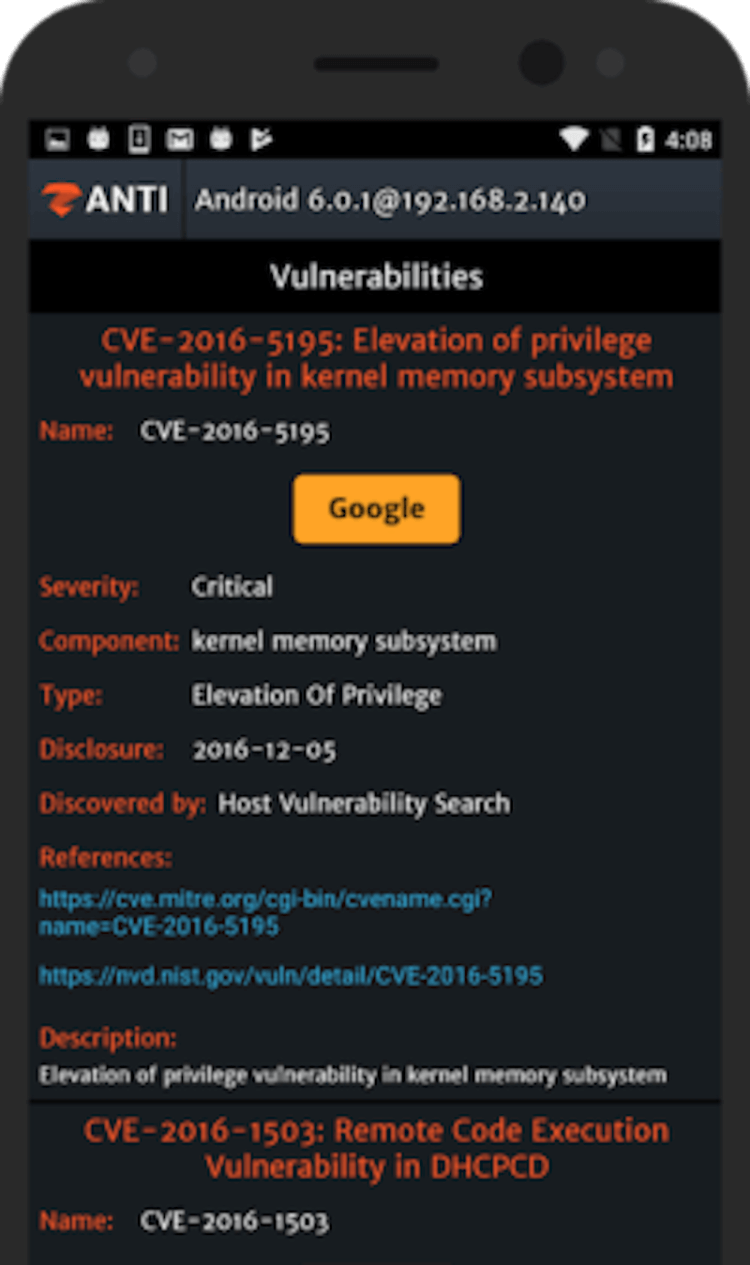
Zanti — Контроль доступа и не только
Этот простой в использовании мобильный инструментарий может быть использован для оценки безопасности сети WiFi, поиска уязвимостей и, конечно же, для проникновения в сети. Встроенный сканер WiFi показывает точки доступа, отмечая те из них, доступ к которым можно получить довольно легко. Вы также можете использовать приложение, чтобы «отрезать» входящий или исходящий трафик и оставить тем самым сеть без доступа в интернет.
Скачать: Zanti
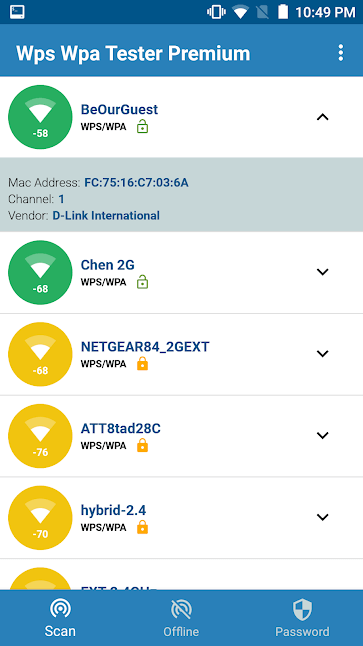
Reaver — Как узнать пароль от сети Wi-Fi
Reaver — это приложение для взлома паролей сетей WiFi, которое при этом довольно несложно использовать. Reaver обнаруживает беспроводные маршрутизаторы с поддержкой протоколов WPS и WPA/WPA2. Всю информацию вы получаете на довольно информативном графическом интерфейсе. Если вдруг вы забыли пароль от своей домашней сети, а сбрасывать настройки роутера не хочется, то попробуйте Reaver
Скачать: Reaver
WPA WPS Tester — Не только взлом, но и защита
WPA WPS Tester в противовес предыдущей программе представляет собой инструмент для поиска уязвимостей в протоколах WPS и WPA/WPA2. Оно может не только «подобрать пароль» к сети, но и позволяет узнать, насколько сеть защищена от взлома, сканируя как входящие и исходящие пакеты, так и сами беспроводные устройства на предмет наличия уязвимостей вроде бэкдоров.
Скачать: WPA WPS Tester
Reaver — консольная утилита для подбора PIN-кода WPS методом перебора (brute force attack).
PIN-код WPS — личный опознавательный номер, состоящий из восьми цифр код написанный на корпусе роутера (включен «по умолчанию» в многих роутерах), если его правильно ввести (используя специальную сессию WPS) то можно получить доступ к имеющиеся настройкам роутера. При проводном подключении не нужна никакая аутентификация, что делает PIN-код потенциально подверженным атаке методом перебора.
Reaver (reaver-wps) создана для надёжной и практичной атаки на WPS (Wifi Protected Setup) и прошла тестирование на большом количестве точек доступа (с различными реализациями WPS). В среднем для раскрытия PIN-кода WPA/WPA2 целевой точки доступа необходимо от четырёх до десяти часов, но на практике обычно требуется около половины этого времени (на предложение пина), пароль выводится в виде простого текста.
Оригинальная версия Reaver не обновлялась с января 2012 года (версия 1.4) и был сделан форк (reaver-wps-fork) прекративший развитие в начале 2014 года, а в апреле 2015 года вышла очередная модификация (reaver-wps-fork-t6x), главным отличием которой добавление возможности использования применимой к многим точкам доступа атаки Pixie Dust, служащей для нахождения верного пина WPS (атака позволяет найти верный пин WPS буквально за минуты).
Модифицированная версия Reaver требует установки Pixiewps (Wiire’s Pixiewps), которая используется для оффлайн брутфороса (bruteforce offline) PIN-кода WPS посредством эксплуатирования низкой или несуществующей энтропии некоторых точек доступа. В состав модификации входит утилита Wash, осуществляющая пассивное исследование и идентификацию точек доступа с включенным WPS.
Лицензия: GNU General Public License version 2 (GNU GPL v2)
Домашняя страница
Страница актуальной (на 06.06.16) модификации